Become the cyber security expert the AI era demands.
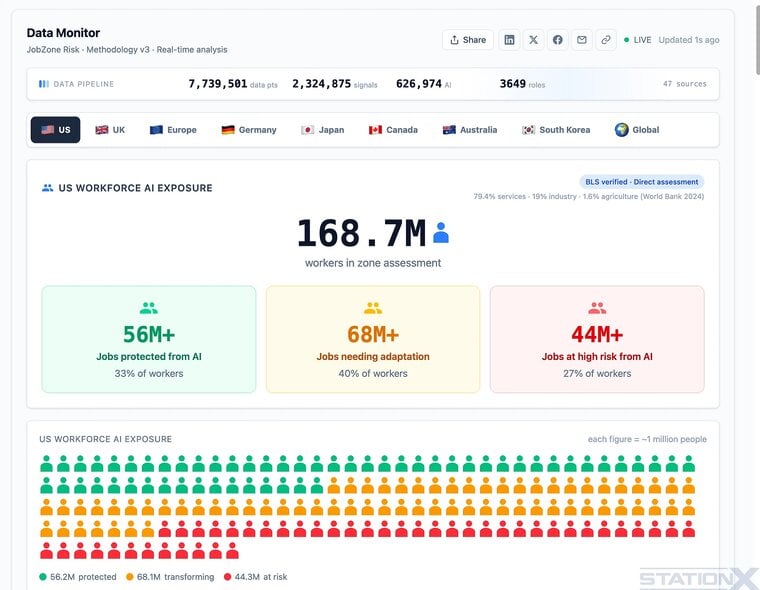
Learn to direct AI to build real security solutions, not just run tools. Every cyber role is becoming its AI-driven version — the AI-Driven pen tester, the AI-Driven security engineer, the AI-Driven SOC analyst — the people teams fight to hire. You graduate a solution creator with your own compounding AI infrastructure, ready to get hired in a senior role, consult for your own clients, or build your own business. The skill the market will pay for in 2027, 2028 and beyond.