The CompTIA Security+ exam tests your cyber security knowledge across a wide range of topics to ensure you are ready for an entry-level role. The best way to prepare for this exam is by studying and answering CompTIA Security+ practice questions.
Practice questions help you assess your current knowledge, allow you to identify areas that need improving, and let you accurately determine if you are ready to take the real exam. They are an essential piece of preparing for your Security+ exam.
This article gives you a taste of what to expect on the real exam by providing multiple-choice and performance-based (PBQ) practice questions. You can interactively test your knowledge using these questions across all five of the Security+ domains. This is not an exhaustive list of everything you will be tested on in the Security+ exam. Just a glimpse of what to expect.
CompTIA Security+ Exam Domains
The Security+ exam consists of five domains. These domains are designed to assess your cyber security knowledge and readiness to enter the industry. They include:
- General Security Concepts (12%)
- Threats, Vulnerabilities, and Mitigations (22%)
- Security Architecture (18%)
- Security Operations (28%)
- Security Program Management and Oversight (20%)

To assess your knowledge, the Security+ exam comprises no more than 90 questions that must be completed in 90 minutes. These questions are a mixture of multiple-choice and performance-based questions (PBQs). Let’s take a look at the kinds of questions you can expect to see on the exam.
CompTIA Security+ Practice Questions
It is key that you prepare for the CompTIA Security+ exam by testing yourself using mock exam questions. Practice exams allow you to test your current knowledge, identify areas where you need to improve, and assess if you are ready to take the real exam.
Below are some CompTIA Security+ practice questions you can expect to see on the exam. This includes a mixture of multiple-choice and performance-based questions split into each Security+ domain.
To learn more ways to prepare for the Security+ exam, check out The Ultimate CompTIA Security+ Study Guide for Exam Prep.
General Security Concepts (12%)
The first domain you will be tested on focuses on foundational aspects of cyber security, such as the CIA triad, key terminology (e.g., gap analysis, honeytoken, zero trust), and security controls. This domain ensures you understand the fundamentals and know the common language cyber security professionals use.
Things you must remember:
Sample Question 1:
What does CVE stand for?
a) Common Vulnerability Expectation
b) Common Vulnerabilities and Exposure
c) Causal Vulnerability and Exposure
d) Correct Vulnerability in Essence
Click for answer
b) Common Vulnerabilities and Exposure
Sample Question 2:
What is an Advanced Persistent Threat (APT)?
a) An advanced monitoring tool that tracks persistent threats
b) A script kiddie that won’t go away
c) A persistent vulnerability that is not getting patched
d) A sophisticated, persistent, and targeted cyber attack
Click for answer
d) A sophisticated, persistent, and targeted cyber attack
Sample PBQ:

Threats, Vulnerabilities, and Mitigations (22%)
A key area of cyber security is understanding threats and how to defend against them. This domain focuses on how to identify threat actors, understand their motivations, and mitigations you can use to defend against them.
Things you must remember:
Sample Question 1:
Which of the following are NOT recognized as threat actors?
a) State actor
b) Criminal syndicate (organized crime)
c) Script Kiddie
d) Office Worker
Click for answer
d) Office Worker
Sample Question 2:
Which of the following are ways to defend against SQL injection?
a) Using a modern database
b) Not using web forms
c) Input validation and sanitization
d) Using a secure programming language
Click for answer
c) Input validation and sanitization
Sample PBQ:

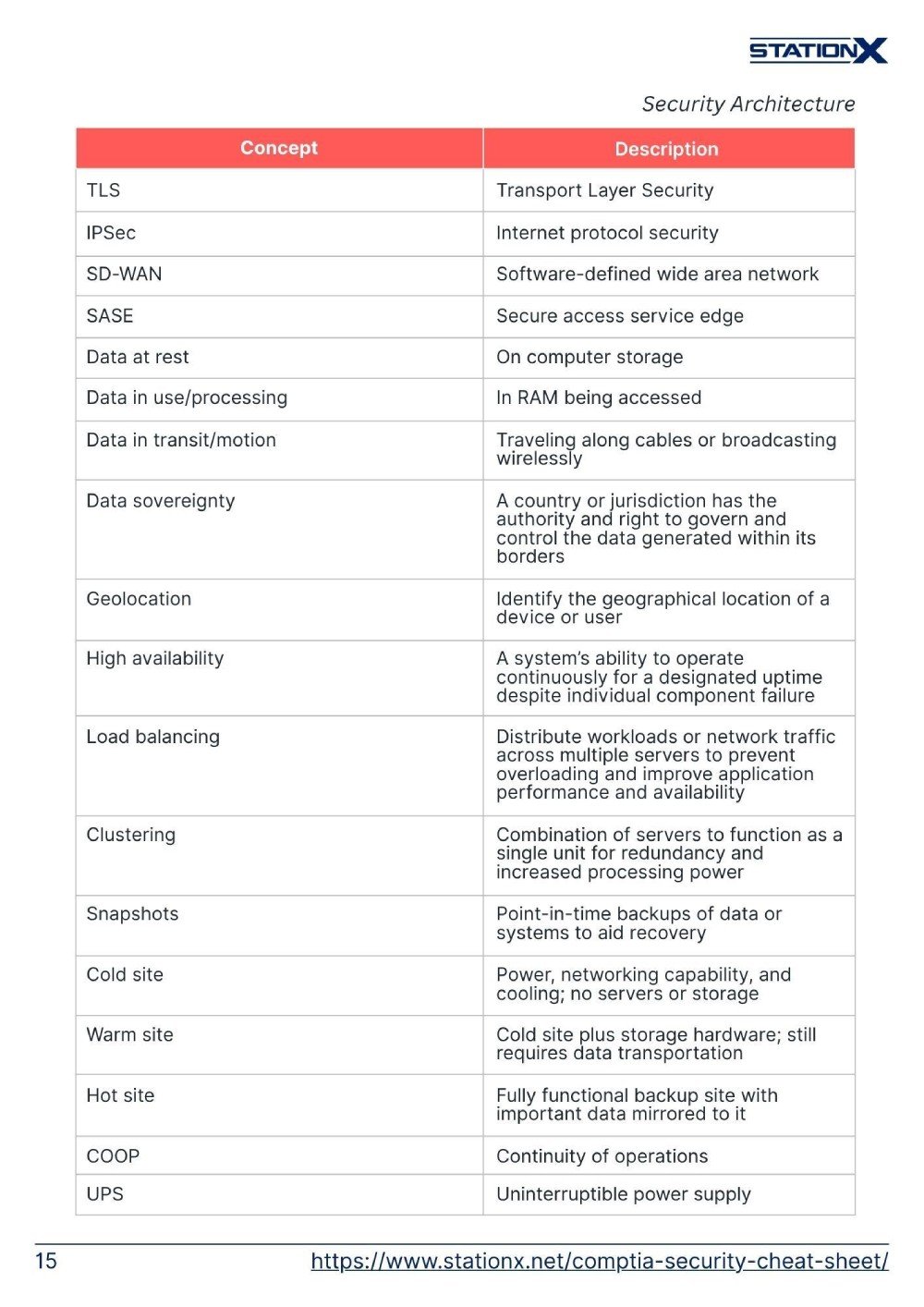
Security Architecture (18%)
Systems need to have a secure architecture to be resilient to attacks. This domain delves into what secure system architecture looks like by discussing data types, classifications, and methods to secure data. It also focuses on how data is made available using things like load balancing and site considerations.
Things you must remember:
Sample Question 1:
What does it mean to air gap a system?
a) Physically isolate a secure computer network from unsecured networks.
b) Set up a demilitarized zone (DMZ) that traffic has to pass through before reaching a secure computer network.
c) Create a subnet for different computer networks to secure them.
d) Use only wireless network connections.
Click for answer
a) Physically isolate a secure computer network from unsecured networks.
Sample Question 2:
Which of the following are key considerations when choosing a secure symmetric cipher?
a) Key length, age, and block size.
b) Popularity, speed, and key length.
c) Key length, block size, and number of rounds.
d) Key exchange, hashing, and salting.
Click for answer
c) Key length, block size, and number of rounds.
Sample PBQ:

Security Operations (28%)
This is the most heavily weighted domain. It covers the practical day-to-day work you will likely be doing as a security professional, including incident triage and response, security investigations, the importance of automation and orchestration, using data sources effectively (e.g., log management), and performing vulnerability scans.
Things you must remember:
Sample Question 1:
Why is Security Orchestration, Automation, and Response (SOAR) important?
a) Helps automate response and reduce overall response time.
b) Allows you to see more incidents.
c) Adds another layer of security to a system.
d) Gives pretty graphics for SOC analysts to visualize attacks.
Click for answer
a) Helps automate response and reduce overall response time.
Sample Question 2:
Which of the following is NOT a method for implementing identity and access management?
a) Attribute-based access control (ABAC)
b) Multi-factor authentication
c) Role-based access control (RBAC)
d) Using a password manager
Click for answer
d) Using a password manager
Sample PBQ:

Security Program Management and Oversight (20%)
The final domain in the Security+ exam looks at the role governance plays in cyber security. It focuses on policies and standards, risk management processes and strategies, and effective security awareness training to mitigate threats like phishing.
Things you must remember:
Sample Question 1:
What is business impact analysis?
a) Process for assessing and quantifying the potential impact of cyber security incidents on business operations.
b) Analysis of how a business would benefit from a cyber security program.
c) Process of assessing how a vulnerability may impact a business.
d) Assessing the damage a threat actor could cause to business operations.
Click for answer
a) Process for assessing and quantifying the potential impact of cyber security incidents on business operations.
Sample Question 2:
What is the formula for calculating Single Loss Expectancy (SLE)?
a) Single Loss Expectancy = Annualized Rate of Occurance / Business Impact
b) Single Loss Expectancy = Asset Value / Exposure Factor
c) Single Loss Expectancy = Annualized Rate of Occurrence x Business Impact
d) Single Loss Expectancy = Asset Value x Exposure Factor
Click for answer
d) Single Loss Expectancy = Asset Value x Exposure Factor
Sample PBQ:

CompTIA Security+ Exam Advice
The Security+ can be a daunting exam. You have 90 minutes to answer a maximum of 90 questions assessing your general knowledge and performance across various cyber security topics. It is important to remember this is an entry-level certificate that many people have been able to pass before you. By dedicating adequate time to studying and exam preparation, you can pass this exam.
To help you be successful, here are some strategies that will help you maximize your exam score:
- Ensure you understand each item on CompTIA’s objectives list before taking the exam. It helps to write out a detailed roadmap, so you ensure you cover all the material. Read How Long to Study for Security+? A Comprehensive Roadmap to find out how to do this.
- Give yourself ample time on exam day to reach the exam location, be adequately rested and fed, and have the materials you need. You want to minimize stress as much as possible on exam day. It is stressful enough already.
- Try to memorize important acronyms and their meanings. These can be found at the bottom of CompTIA’s objective page. They will help you remember keywords, phrases, and pieces of information when answering questions. CompTIA will only supply the acronyms on the exams.
- Regularly take practice exams throughout your studying to track your progress and identify domains you need to spend more time studying.
- Schedule your exam before you start studying. This gives you a goal to work towards and will keep you motivated.
Conclusion
Your preparation for your exam will be the difference between passing and failing. The CompTIA Security+ practice questions listed in this article give you a taste of what to expect on your exam. You must familiarize yourself with this format, learn to identify the correct answer on multiple choice questions quickly, and fully understand what performance-based questions are asking you to do.
We have a range of resources you can use to help best prepare for your Security+ exam. There is our Security+ cheatsheet, ultimate exam preparation guide, and a detailed breakdown of the new SY0-701 Security+ exam.
If you want to take your exam preparation and career to the next level, check out StationX’s Master's Program. You will get access to certification advice, mentorship, over 30,000 classes and labs, and a tailored blueprint for obtaining your desired career.
Click the banner below to see our CompTIA Security+ Training Bundle. For a one-time purchase, get lifetime access to multiple Security+ exam prep courses, practice tests, flashcards, and more. And don't forget you can save up to 30% on your Security+ exam voucher by purchasing through our store.
The CompTIA Security+ Course & SY0-701 Practice Test Bundle includes:
- CompTIA Security+ Study Guide: SY0-701 Total Course
- CompTIA Security+ Training: Self-Paced Course
- CompTIA Security+ SY0-701 Exam Questions and Answers
- CompTIA Security+ Practice Test Series: Ace the SY0-701
- CompTIA Security+ Exam Objectives Flash Cards: SY0-701 Prep