To have a long and successful career in IT and cyber security you need to know at least the basics of computer networking.
Knowing how data gets from point A to B will give you a better understanding of your IT surroundings regardless of your profession. This introduction to networking primer will equip you with the foundational knowledge you need to move on to more advanced topics.
Over the next few minutes, you’ll learn about the many types of networks, network topologies, network hardware, IP addressing and subnetting, network protocols, security, and more.
If you’re ready, we are too! Let’s go.
What Is Enterprise Networking?
Home networks are usually straightforward, with one device acting as an all-in-one router, modem, switch, and wireless access point.
This changes when you account for more devices, traffic, security, speed, and other factors, such as when dealing with enterprise networking.
Networking for an enterprise becomes more complex as you now have to network other devices, offer more security, and meet a range of unique needs and requirements, all while having the capacity to scale your network securely.
Types of Networks
When it comes to networking, there is no one-size-fits-all policy. Familiarizing yourself with each network will give you a better ability to choose, troubleshoot, and protect your network.
1. Local Arena Network (LAN)
A LAN, or local area network, is a network where all the devices used to connect with one another and the internet are housed under one roof. Networks within a home or office, for example, are a LAN.

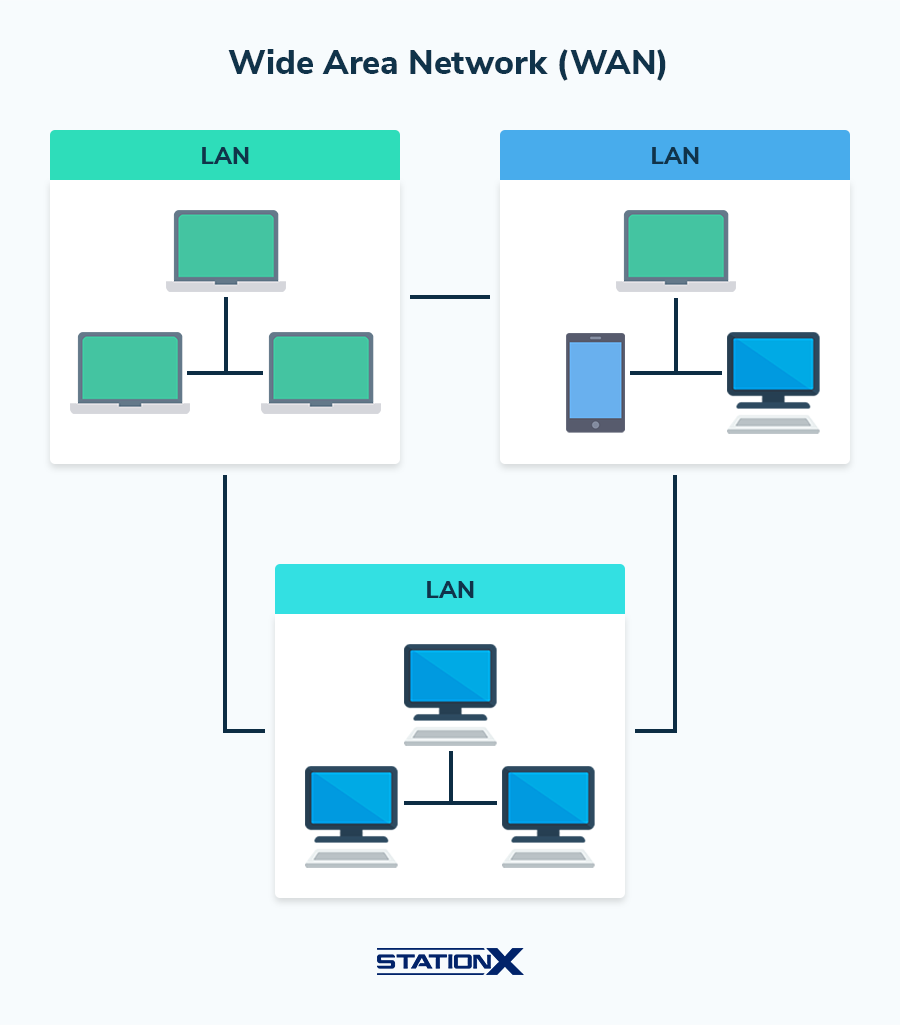
2. Wide Area Network (WAN)
A WAN extends beyond a single building and connects multiple LANs regardless of location.
WANs are popular among companies with branches strewn across the country or the world needing fast and secure networking capabilities. In essence, a WAN is a constellation of LANs or a network of networks.
In fact, the Internet itself is considered a WAN as it connects all devices regardless of location.
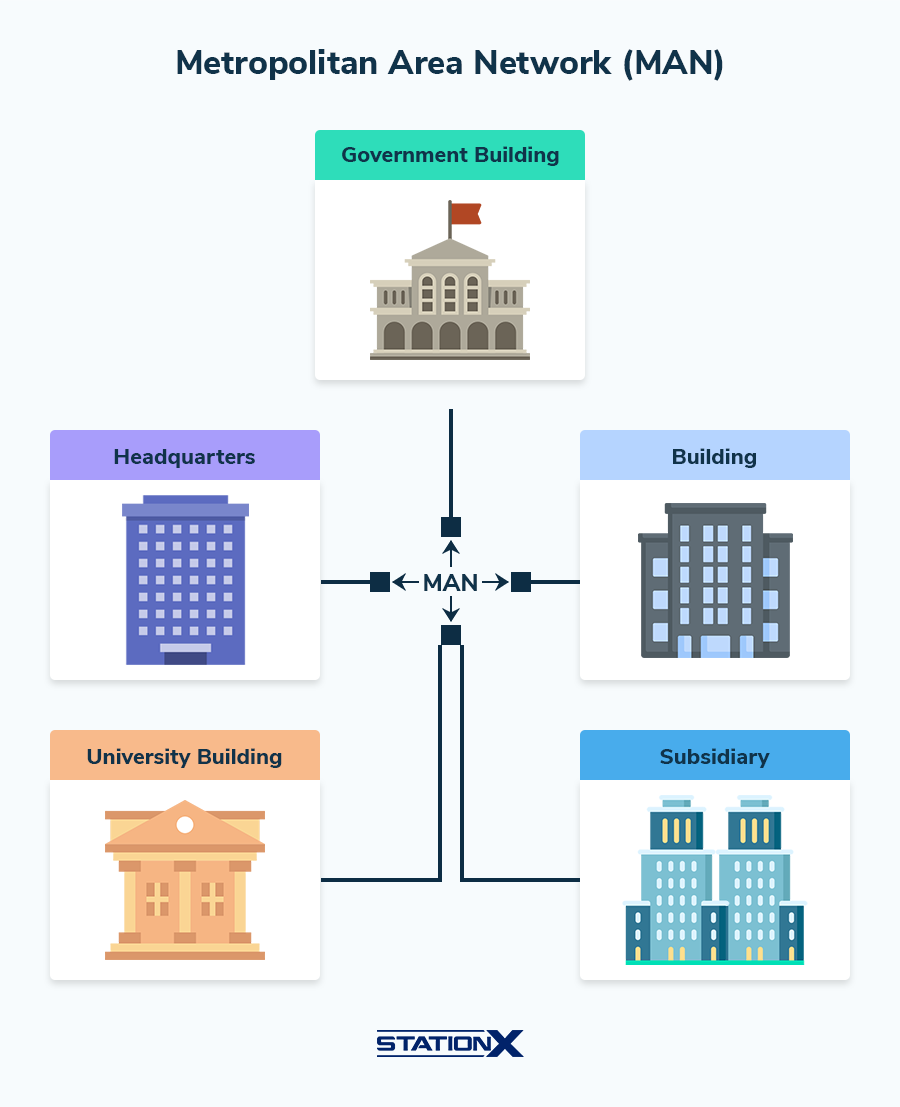
3. Metropolitan Area Network (MAN)
A Metropolitan Area Network (MAN) is an extensive computer network that spans a metropolitan area or campus. Its size and scope fall between a LAN and a WAN.
MANs are often used to connect multiple offices of a single organization within a city, provide connectivity for city-wide services, or link educational campuses.
Due to their proximity, they will likely share a physical infrastructure, such as high-capacity fiber optics.
WANs, by contrast, may need to rely on different technologies, backbones, and internet providers to facilitate connections.
4. Personal Area Network (PAN)
If you’ve ever airdropped files to a friend or connected your earbuds to your computer via Bluetooth, you’ve used a personal area network.
A PAN connects devices close to one another—within a few feet—via wired and non-wired connections such as Bluetooth.
Typically, PANs do not connect to the Internet but are device-to-device connections within the same room.

Introduction to Networking Topologies
Network topologies are different from network types in that topologies are node arrangements that facilitate data sharing. Here are some common—and not-so-common—network topologies.
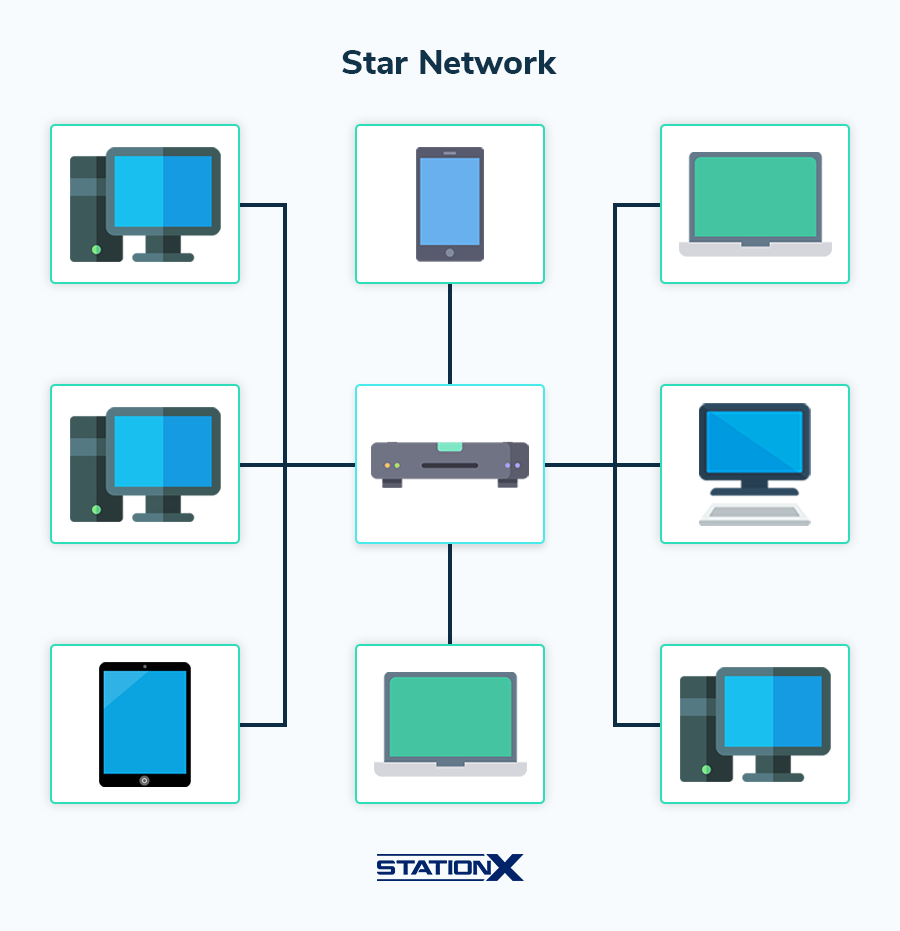
1. Star
The most common topology, the star topology, requires every node on the network to connect to a central device such as a hub, switch, or router.
Most LANs use the star topology. Should the network devices wish to communicate with one another, data must be sent to the central hub first and then routed to its ultimate destination.
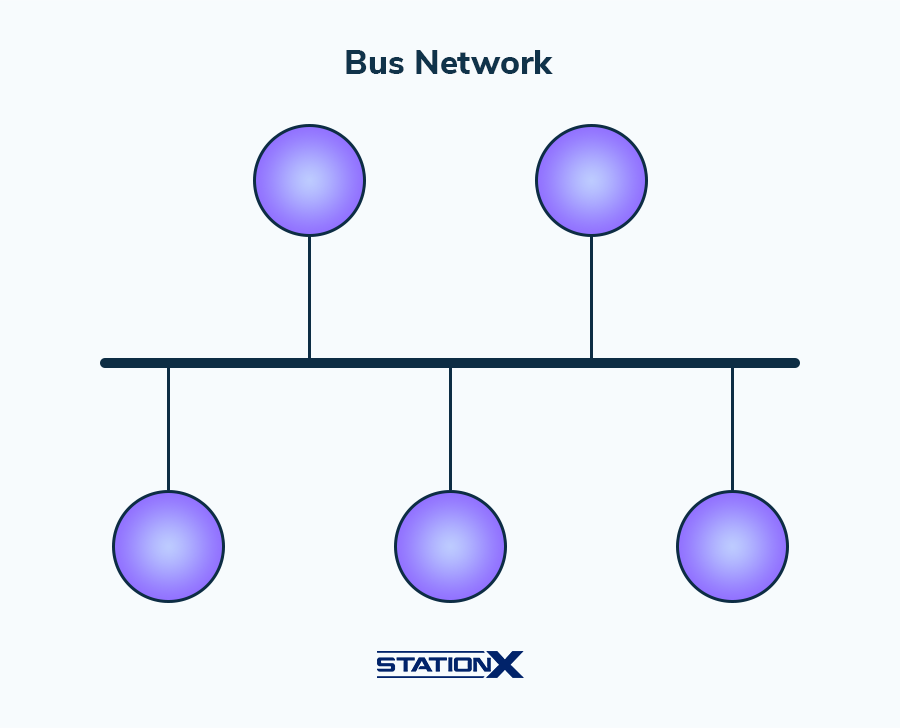
2. Bus
In a bus network topology, every node is connected to the same cable called the “bus.”
Sharing the same cable means that every time a message comes into the bus topology, every node connected to the cable will receive that message. A disadvantage of this setup is that having one cable connect to every device on a network creates a single point of failure.
But bus topologies aren’t all negative. Some positives include being simple and easy to deploy and scale, and reliable as long as the cable does not fail.
3. Ring
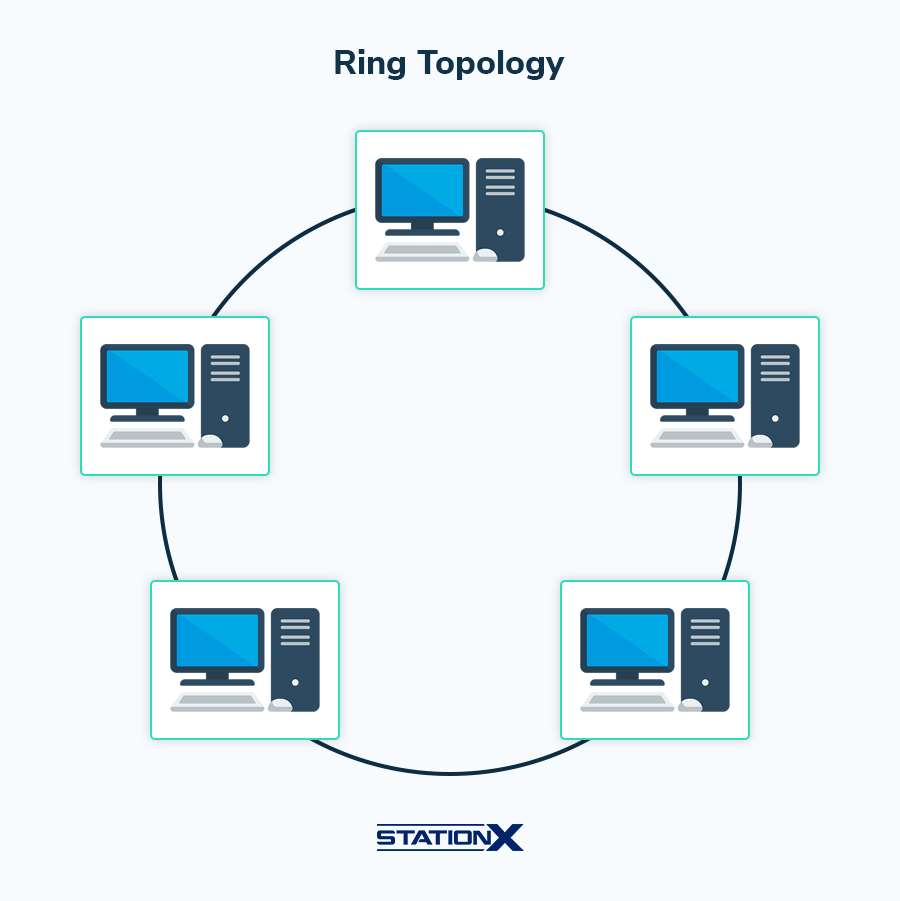
Every node on a ring topology relies on other nodes on the network to pass along information.
Every device on a ring network is connected to two nodes. Ring topologies can pass information one way meaning every node must cooperate to pass that information along to ensure it reaches its destination on the network, while other rings are bidirectional.
Some advantages of this topology include minimal collisions, cost, ease of implementation, and a high data transmission speed.
The crucial disadvantage is obvious: if one node fails to do its job, all communication breaks down.
4. Mesh
A mesh network is a highly interconnected topology where every node is connected to another.
This means every node can take multiple routes when communicating with one another. There is also a partial mesh network where only some nodes can directly connect.
Some benefits of a mesh network include increased stability, range, and direct communication. The negatives of a mesh networks may be the cost, scalability, and complexity of setting up and managing them.

5. Hybrid
Sometimes, organizations can’t rely on one topology for all their networking needs, opting to implement a hybrid topology strategy.
This hybrid strategy uses multiple topologies for their networking needs.
Perhaps an organization near you uses a star topology for most of their everyday networking needs but also needs to configure a wireless mesh network should a network cable fail to connect to an access point.
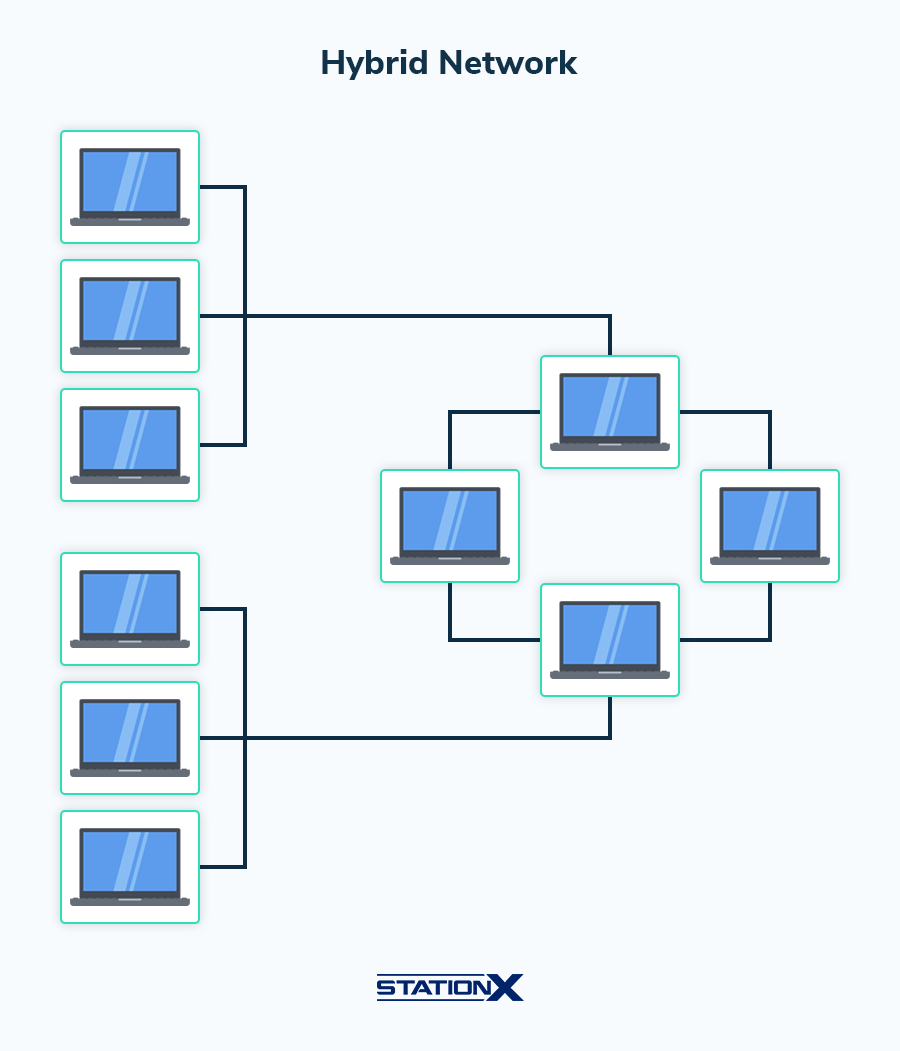
Bus and ring topologies aren’t nearly as popular as they once were. The main topologies we use are star, mesh, and hybrid topologies.
Introduction to Network Hardware
To create network types and topologies, you’ll have to use some of the following hardware.
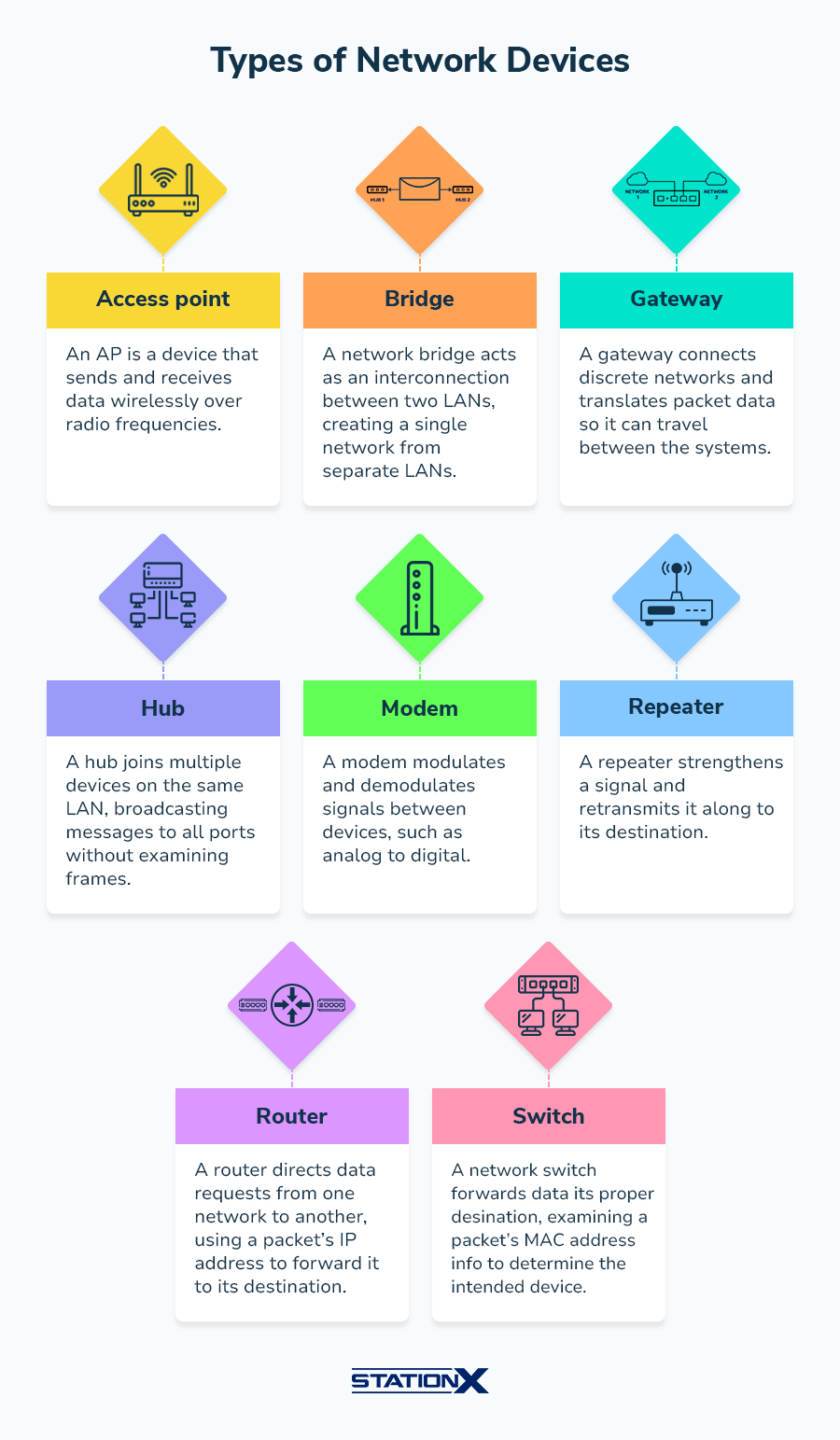
Router
A router allows you to connect with networks on the internet using an IP address to forward packets.
Switches
Switches use a MAC address to forward packets within a LAN. Switches need to connect with a router to access the Internet.
Hub
Similar, though not as intelligent as a switch, a hub connects internal devices by broadcasting messages to all connected devices and ports. For the most part, hubs can be replaced by switches.
Bridge
A bridge connects two LANS, creating one network in turn.
Modem
While most modern modems are built into routers, modems modulate signals to and from the Internet that otherwise would be unintelligible to a router. Think of a modem as a translator for networking devices.
WAP
A WAP or wireless access point is a switch for wireless devices, allowing them to connect to and communicate within a network.
Firewall
A firewall uses rules to filter traffic coming in and out of your internal network. A firewall is built into most home routers. However, most enterprises will use firewall-specific hardware.
Other common pieces of network hardware include:
- Hosts: A network host is any network device communicating on a network (computer, printer, etc.).
- Servers: Network servers are powerful machines designed to handle various networking tasks such as identity and access management, and data storage.
Introduction to IP Addressing and Subnetting
If you want to connect to the Internet or communicate within a network, you’ll need an IP address. Here’s a quick primer on everything related to IP addresses.
What Are IP Addresses?
An IP address is a unique string of numbers (IPv4) or numbers and letters (IPv6) used to identify a device connected to the Internet.
IP stands for Internet Protocol, a set of rules to format data efficiently to send through the Internet.
Every time you connect to a router, you’re provided a new private IP address that the router will use to identify you. Your private IP address is known only within your local network.
Your router also has a public IP address, which it then used to connect to the Internet. Your public IP address does not change as it's assigned by your ISP (Internet Service Provider).
Subnetting
Subnetting is a way to make a network smaller. Imagine if you had hundreds or thousands of devices in a network.
Making sure that all the data generated by these devices is quickly routed would be difficult. So, to make routing easier, devices are grouped via subnetting.
The process of subnetting involves creating a subnet mask. A subnet mask is akin to an IP address, but it’s only used for internal routing purposes.
NAT
NAT stands for network address translation.
Due to the finite amount of public IP addresses, not every device can have its own public IP address.
NAT translates a private IP address to a public one to access the internet—and vice versa. Slowly, we are transitioning to using IPv6 addresses, which are plentiful and would allow every device to have its own public IP address.
But until then, we’ll be stuck using IPv4 and relying on our router to use NAT to translate our private IP address so that we may connect to the internet.
All devices within a LAN have their private IP address but share a single public IP address thanks to NAT.
IPv4 Address Classes
There are three main private IPv4 address classes. The type of address class you’ll use depends on the size of the network you’re on.
Class A Private Range: 10.0.0.0 to 10.255.255.255
This range is used by large businesses that have many devices that want to connect to the internet.
Class B Private Range: 172.16.0.0 to 172.31.255.255
Medium-sized businesses use the Class B range of IP addresses.
Class C Private Range: 192.168.0.0 to 192.168.255.255
The class C range is the range you use when on your home network or in a small business.
Network admins need to choose their network class wisely to ensure each device they want to connect to their network can do so.
Introduction to Networking Protocols
Without rules for networking, data could never be transferred correctly. There are protocols for each type of interaction.
Some of the most common networking protocols include:
- HTTP: Unencrypted hypertext transfer protocol used to access web servers
- HTTPS: Encrypted hypertext transfer protocol
- FTP: File transfer protocol used to transfer data
- SMTP: Simple mail transfer protocol, is used for sending email between mail servers
- SSH: Secure shell is used for sending commands to a computer over an unsecured network
- DNS: Domain name translation is used to translate IP addresses of websites to human readable names and vice versa
Each protocol has its own logical port number. Ports allow computers to understand one another as they help differentiate traffic. Ports aren’t physical locations but virtual destinations where protocols take place.

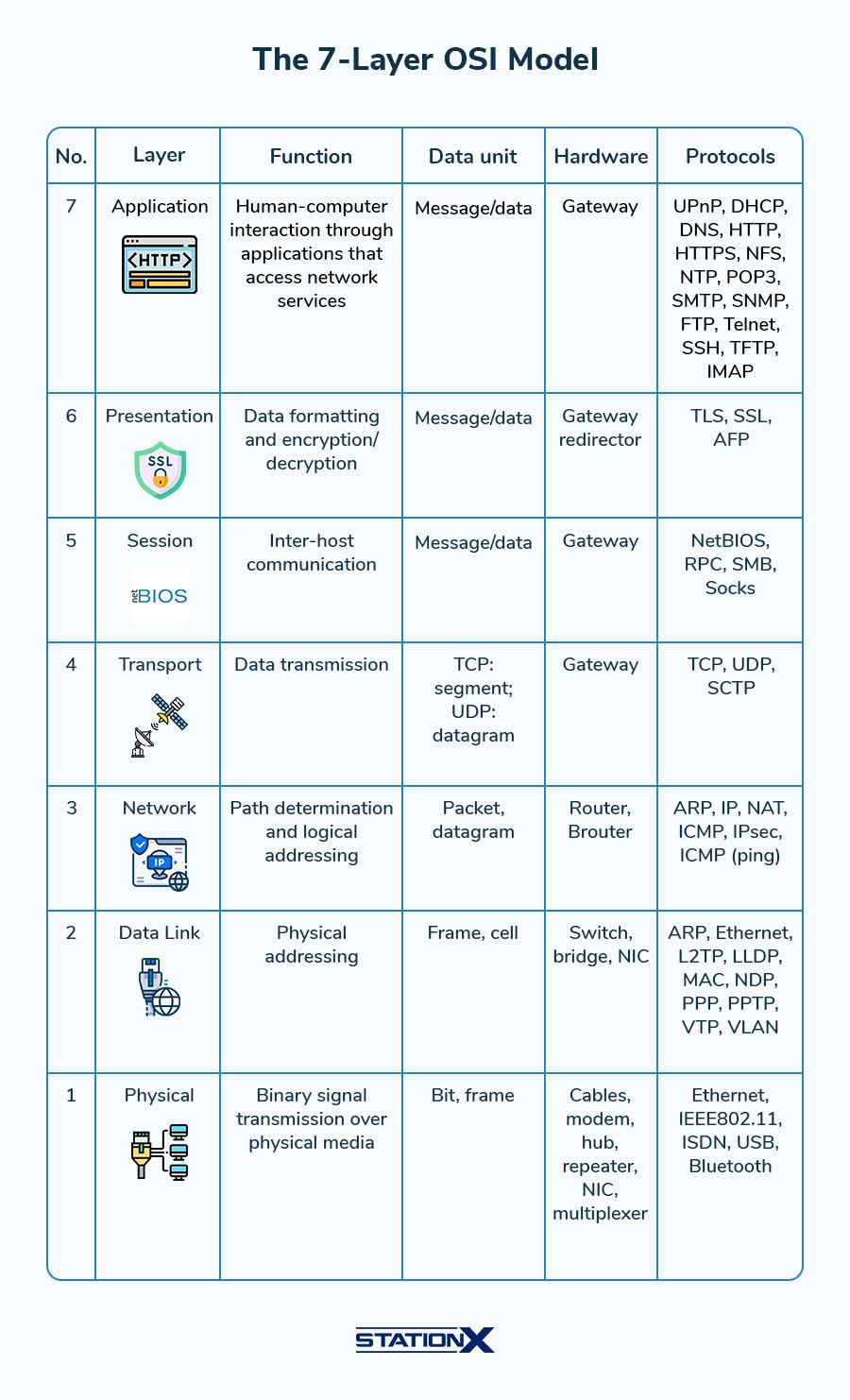
OSI Reference Model
The OSI model is the standardized language computers use to talk to one another. While the current OSI model is a little dated, it’s still widely used to understand how the internet works and to help with network troubleshooting.
There are seven layers to the OSI model:
- Physical Layer
- Data Link Layer
- Network Layer
- Transport Layer
- Session Layer
- Presentation Layer
- Application Layer
Data being received to your host device must move through all of the OSI layers, starting with the Physical (data travelling through a modem) to the Application (what you use to access the data).
Likewise, sending information through a network or the internet requires the data to move from the Application layer to the Physical before heading to its final destination.
Each layer is explained in the infographic below.
Introduction to Network Security
The Internet isn’t inherently secure.
To harden systems and ensure that your data isn’t compromised, cyber security professionals use the following network security tools:
- Firewalls, which use rules to filter traffic in and out of a network;
- IDS, or intrusion detection systems, which monitor network traffic and issue notifications when identifying suspicious traffic;
- IPS, or intrusion prevention system, which works similarly to an IDS but can take automatic action to block suspicious traffic;
- SIEM, or security information and event management system, used to collect logs from all devices connected to your network to monitor your network traffic;
- VPN, or virtual private network, that connects you from your network to a remote network;
- VLAN, or virtual local area networks, used to group devices together and create a network within a network (e.g., creating networks for each company department)
Bringing a Network Together
Understanding how each network component interacts with the others can be challenging. To better understand how networks function, even professionals use network diagrams to create easy-to-understand visuals.
This is a diagram of the network architecture we might see in the home or a small business.
When visualized, it’s easier to understand what devices we have on our network and how they communicate.

Conclusion
This networking introduction article is just the tip of the iceberg.
For anyone looking to obtain a deeper understanding of computer networks, learning the nuances of computer networking will only help you become a more competent cyber security professional.
Your next logical step might be to start studying with a networking course or for networking certifications such as CompTIA Network+ or CCNA.
Network+ is broader and vendor-neutral, while CCNA is a Cisco-specific networking certification that requires test takers to familiarize themselves with Cisco-specific networking infrastructure.
Obtaining either certification demonstrates your networking prowess to employers.
If you’re wondering which one to choose, we recommend CCNA if you want a more network-specific technical role, such as a network administrator or network engineer.
Network+ is best for those who need a more superficial understanding of networking, such as cyber security or other IT professionals.
If you want to learn more about cyber security, IT, or networking online, or prepare for the aforementioned exams, join the StationX Master's Program.
In this program, you’ll have access to over 30,000 courses and labs, one-on-one mentorship, our supportive and informative community, and our mastermind program.
You can also see our CompTIA Network+ Training Bundle and CCNA Certification Training Course Bundle below.