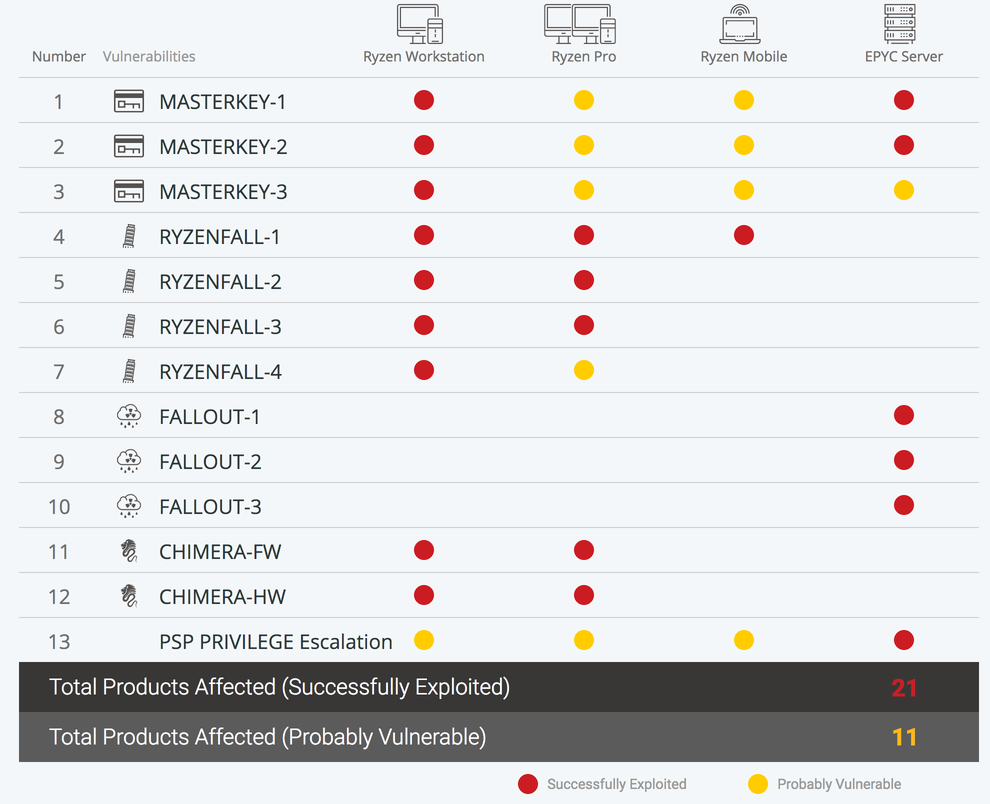
Heads up about 13 vulnerabilities within AMD’s RYZEN and EPYC processors that could make some data breaches even worse. Note requires attackers to first gain administrative rights on a targeted network or computer.
CTS Labs, a Tel Aviv-based security company announced the vulnerabilities on AMDFLAW website and in videos published Tuesday (Above). The company also published a white paper that explains what the vulnerabilities are without including their full technical details.
So lets keep an eye on what happens as we don't know all the details yet. Could be overblown.
Some other useful reading material; Theregister and Dan Guido's Twitter.
Update from Alexandru Lepsa:
If you look at the "vulnerabilities", the "worst" one requires you to manually flash your bios with basically a virus and some of the other claimed vulnerabilities require you to willingly exploit your system while in administrator mode, also one of the vulnerabilities is with a motherboard manufacturer and not AMD.
Their website was just registered, as was the whitepaper domain, and they only gave AMD 24 hours notice, which is very unusual, and then they don't link any of their exploits to a CVE (https://cve.mitre.org/) which is even more unusual - basically unheard of.
Finally, their domain is WHOIS protected and they have this disclaimer on their site - "you are advised that we may have, either directly or indirectly, an economic interest in the performance of the securities of the companies whose products are the subject of our reports".
Not to mention this: https://imgur.com/OkWlIxA
Basically this looks like some sort of stock manipulation scheme or some other sort of sketchy attempt to confuse the public, kind of like all those bogus ICO whitepapers that look mostly legit but really aren't and you only find out once you've already lost all your money.
No one is denying that these vulnerabilities may exist but it's a bit akin to saying "doctors have discovered that if one shoots themselves in the foot, one will bleed" or that "news flash, if you give a robber keys to your home they will rob you".
Thanks
Nathan




https://plus.google.com/+LinusTorvalds/posts/PeFp4zYWY46
Linus Torvalds said this whole thing is just made and is just a big bullshit.
Yes just read that.
Thanks for the heads up on both the potential of there being vunerablities, and the potential of it being a sham. Also congratulations this is the first email ive recieved from a Udemy course that contained something of value. Thank you good sir
Thank you good. It would be a waste of my time if they were not of value!
According to theregister,” The flaws do not open AMD-powered PCs and servers to remote hijacking over the internet, nor allow malicious apps to commandeer systems. Instead, they can be leveraged to ensure that once malware is present, it’s more difficult to find and remove”.