Mozilla is going ahead with its plans to enable DNS-over-HTTPS (DoH) by default in its Firefox browser.
The roll-out will start with a small cohort of users in the U.S. – and barring any problems with deployment, it looks set to be extended gradually to Mozilla’s wider user base. Mozilla claims that the change is all about making internet connections more secure and protecting user privacy – but not everyone is happy about it. In the UK especially, there is concern that DoH will stymie the ability of ISPs to filter and track user activity.
Here’s a closer look at how DoH works, the controversy surrounding its deployment and the pros and cons of enabling it.
Add a header to begin generating the table of contents
What is DoH?
The existing Domain Name System (DNS) is the framework in which easy-to-remember website addresses (e.g. www.stationx.net) are translated into code that devices can read. Type an address in the browser and a request is sent to your local DNS server (most often provided by your Internet Service Provider). The DNS server then searches for and retrieves the numerical IP address of the web server that hosts that specific site.
With standard DNS systems, DNS requests are unencrypted. This makes it vulnerable to various forms of eavesdropping and ‘man-in-the-middle’ hacking attempts. Examples include tunnelling through DNS queries and responses to pass on malware, as well as DNS hijacking, where queries are redirected to a spoof domain server.
Developed by Mozilla, the new system, DNS over HTTPS (DoH) is designed to combat these vulnerabilities. Under it, DNS requests are sent via HTTPS and secured by a Transport Layer Security (TLS) cryptographic protocol. It means that requests are effectively hidden in the huge general stream of HTTPS internet traffic, thereby stopping snoopers from isolating and exploiting those requests.
What’s happening with Firefox and DoH?
Users have been able to explicitly enable DoH on Firefox since the release of v62 in 2018.
In a blog post earlier this month, Mozilla’s Selena Deckelmann confirmed that the company is now ready to start enabling DoH by default. The roll out will start in late September for a small percentage of U.S. users. There will be further announcements when the company is ready for 100% deployment.
Who’s complaining about DoH by default?
Especially in the UK, it’s fair to say that ISPs haven’t welcomed the arrival of DoH with open arms. In fact, Mozilla’s initial announcement of plans for a general roll-out led to a nomination for ‘Internet villain of the year’ by the UK’s ISP Association.
The concern for ISPs is that the new protocol will stop them deploying certain key features such as parental controls and anti-malware filters. With DoH, your DNS queries effectively bypass your ISP’s nameservers. And of course, just as hackers would struggle to isolate individual requests from the general stream of HTTPS traffic, the same goes for ISP providers. DNS-based Internet filtering requires ISPs to be able to see browsing requests at a household level. If ISPs don’t have this visibility, they cannot deliver the function.
It is also claimed that DoH will make life more difficult for governments: something that could be seen as good or bad news, depending on where you stand on the censorship debate! In the UK for instance, the government’s online harms reduction proposals lists ISP blocking of non-compliant sites as a potentially useful enforcement mechanism. The new protocol could effectively blow that out of the water.
For its part, Mozilla rejects the argument that DoH by default will prevent Firefox users from deploying filters. Under its plans, DoH will be automatically disabled on the browser whenever the presence of parental controls is detected. More generally, it will also be disabled if lookup failures occur.
Other issues with DoH
Enterprise security
The key feature of DoH is that it bypasses your internal DNS structure completely, as user requests – as requests are fired straight off to Mozilla’s servers of choice (currently Cloudfare). This also means that any security mechanisms you may have in place that also work through the DNS will also be bypassed.
Indeed, for enterprise configurations on Firefox, DoH will not be configured by default (you have to specifically enable it).
Performance
Under standard DNS, the server the server that handles a request typically operates inside the ISP’s own network. Under DoH, the request has that little bit further to travel – i.e. to Cloudfare’s servers. The suggestion is that performance will suffer.
In reality, early indications are positive. Sam Knows looked at this recently and found no tangible performance differences between DNS and DNS-over-HTTPS.
How to enable DoH in Firefox
When it comes to Firefox, DoH by default on promises a potentially useful privacy boost, with the added bonus of not having to lift a finger to enable it. That said, once it’s in place on your browser, it’s worth checking any parental controls and other filters you rely on to make sure they are still working.
And of course, if you can’t wait for it to be installed on Firefox by default, you can manually enable it. Here’s how:
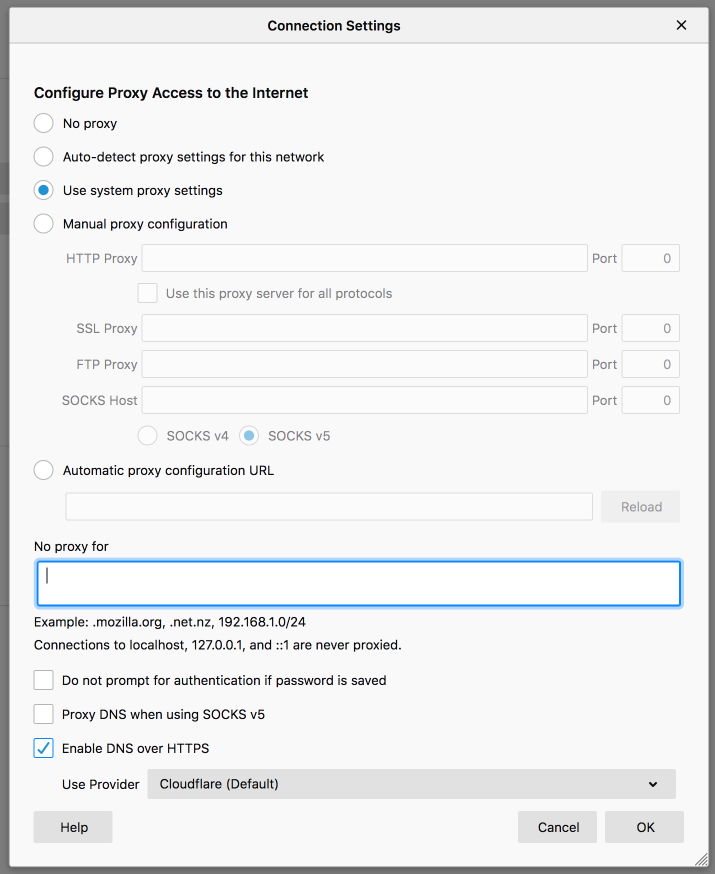
- On the Firefox menu, go to Tools and then Preferences.
- In the General section, go to Network Settings and then press Settings.
- Tick the box ‘Enable DNS over HTTPS’.
How to enable DoH in Chrome
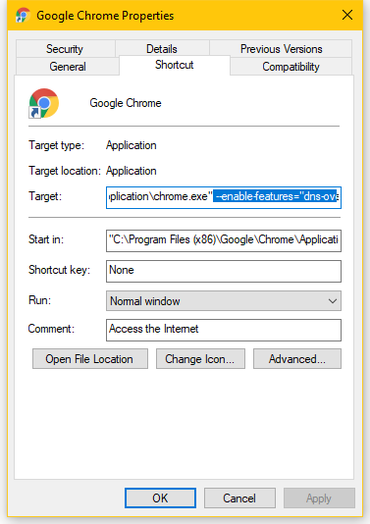
In case you are interested in enabling DOH in Chrome it will not be as easy as in Firefox, there is no menu option to enable or disable DOH. Users have to pass a command-line argument to Chrome executable to make it work. This is how to do it in Windows:
- Find the Chrome shortcut you use to start Chrome on your system, it can be on your task bar, desktop, start menu or elsewhere.
- Right click the shortcut and select Properties.
- In the Target field add the following text:
--enable-features="dns-over-https<DoHTrial" --force-fieldtrials="DoHTrial/Group1" --force-fieldtrial-params="DoHTrial.Group1:server/https%3A%2F%2F1.1.1.1%2Fdns-query/method/POST
- click Save.




Interesting, how we can block it in Enterprise environment..
It’s not really blocking anything. DoH enables encrytped DNS. You would need to implement DoH on your business DNS server.
Nice information, appreciate it.Cheers.
Thank you for that, I now feel a little more secure and trusting of my DNS
Nice one, and it’s helpful in getting secure from cyber attacks.
Hello Nathan! DoH protocol was one of the hot topics of last year, this protocol encrypts DNS traffic and helps in improving the user’s privacy on the internet.
That it does!