In this tutorial, we’ll show you how to get from zero to hero and easily learn the features of Flipper Zero. You’ll see some great walk-through examples detailing exactly how you can master it with no prior knowledge.
Flipper Zero has become very popular with cyber security professionals, but what is it all about? According to the device’s creators, Flipper Zero is your “cyber buddy,” but that doesn’t say much about what you’d want to use it for.
With this Flipper Zero tutorial, you’ll learn that it’s a tool that will aid greatly in the art of physical penetration testing tasks. It’s also a fun tool to get you started in the world of software-defined radio.
So get your Flipper ready because we’re going to walk you through some Flipper Zero hacking projects.
Flipper Zero Tutorial for Beginners
Let’s begin the guide. First we’ll get your Flipper Zero set up and ready to go. Next we’ll walk through the basic functions and interface. Then we’ll tackle three projects step by step: Cloning RFID access cards, creating a BadUSB and DuckyScripts, and end with cloning a garage door opener.
Getting Started With Flipper Zero Tutorial
Now that you have your Flipper Zero in your hand, let’s walk you through getting started.
Initial Setup
Before you even start, you’ll need to ensure that you have a high-quality microSD card. It needs to be a minimum of 4GB in size and formatted to the FAT filesystem. Insert it with the chip side upwards.
It’s probably best to charge your Flipper first by sticking it into your USB power bank or your computer’s USB port to give it some juice. You can power it on by holding the back button for three seconds.
Firmware Update
After powering up your Flipper Zero for the first time, you’ll probably need to get your device’s firmware up to date. When we unboxed ours, it mandated that we do so.
There are two ways to update the firmware: using the mobile app or through the desktop app (qFlipper).

It’s important to note that there are three firmware versions you can choose from:
- The stable release
- The release candidate
- The development release
The stable release is tested extensively and therefore recommended for most individuals. If you want something a bit more up-to-date than the stable release, you could try the release candidate. However, it may have bugs present before it becomes the final stable release.
Finally, the development release represents the bleeding edge, often released multiple times daily, so don’t expect this firmware version to be stable on every download.
Regardless of whether you use the mobile app or the desktop app to perform the update process, the task is similar for either option. For this example, we’re going to show the qFlipper desktop app, so ensure that you have plugged your Flipper Zero into your computer or mobile device via a USB-C cable.
You can download qFlipper from the Flipper website for your appropriate platform:
The update is a straightforward three-step process:
- Once you have downloaded the tool, start it up and click on the button that looks like a spanner, which is entitled “Advanced controls.”
- Next, choose the “Firmware update channel” from the drop-down menu, select the appropriate release that you want to deploy onto your Flipper Zero, and finally, click on the button that says “Update.”
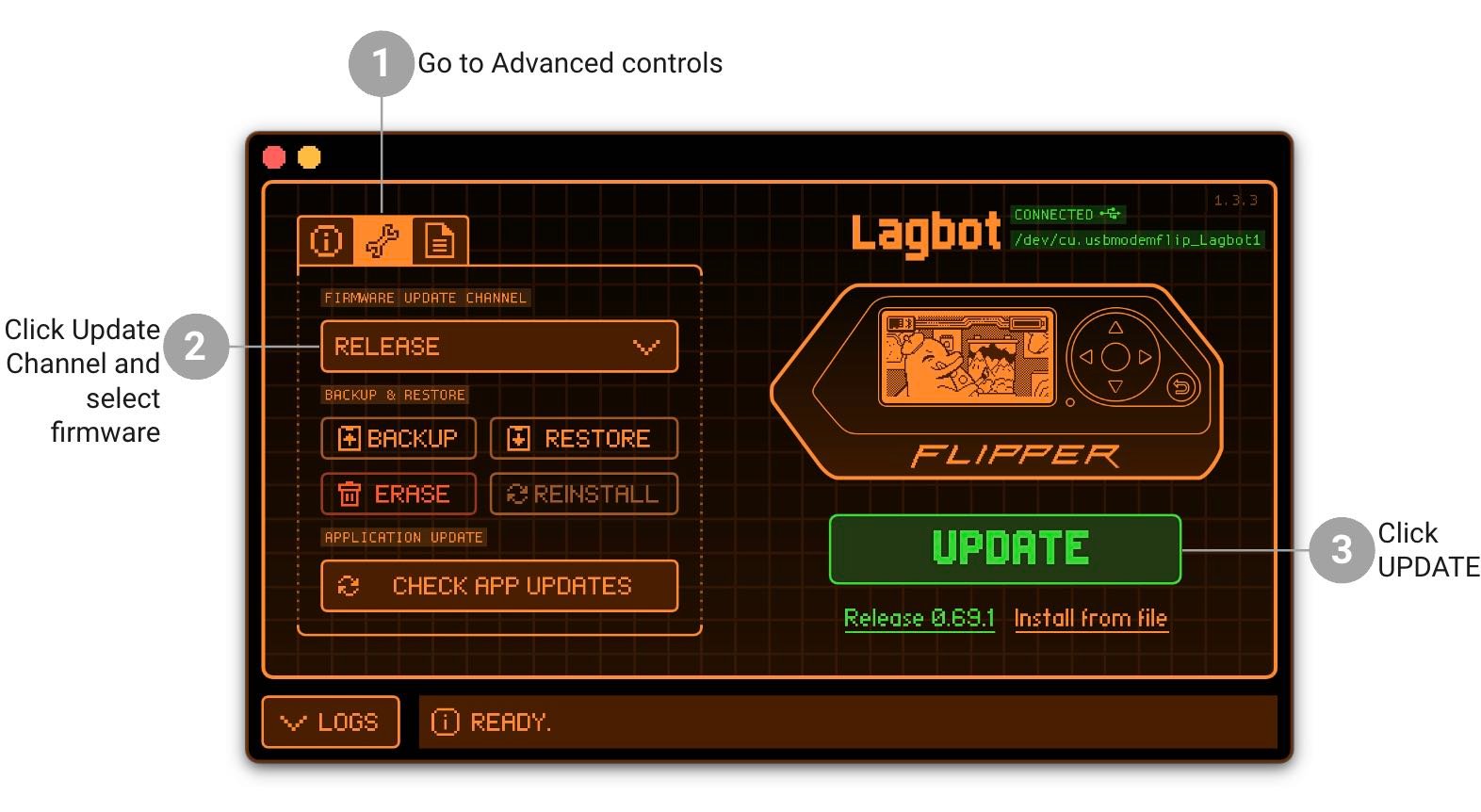
Source: https://docs.flipper.net/basics/firmware-update
- Once you click on the update button, the device should go through a series of restarts before eventually providing you with an update success screen on the device and in the qFlipper or mobile app.

Custom Firmware
The Flipper Zero has several add-on expansions, and it can also be adapted to work in ways the original manufacturers, Flipper Devices, didn’t conceive of.
Due to these aspects, Flipper has been good enough to make the device open to allow third parties to write custom firmware. This means that you can download firmware from other vendors to expand the capabilities of the Flipper in many ways.
For example, the Xtreme firmware is a popular expansion firmware that allows customization of the interface, protocols, and other aspects.
A word of caution regarding third-party firmware, however: anything but the stable release firmware should be considered as non-stable, and whilst unlikely, could damage your Flipper irreversibly or have unintended consequences.
How to Use a Flipper Zero: Basic Operations and Features
Let’s take a minute to discuss how we can move around within the Flipper Zero’s interface.
Flipper's Keys and Menus
Whilst the Flipper is a powerful device with many different applications, navigating the various menus is relatively trivial. There are two main buttons and a direction pad.
Button one, which is located inside the middle of the direction pad, is mainly used for affirmative action, such as executing a function like entering a new menu.
The second button has a backward arrow on it and is used to reject an action or return from a menu, with the direction pad providing the appropriate navigational aid.
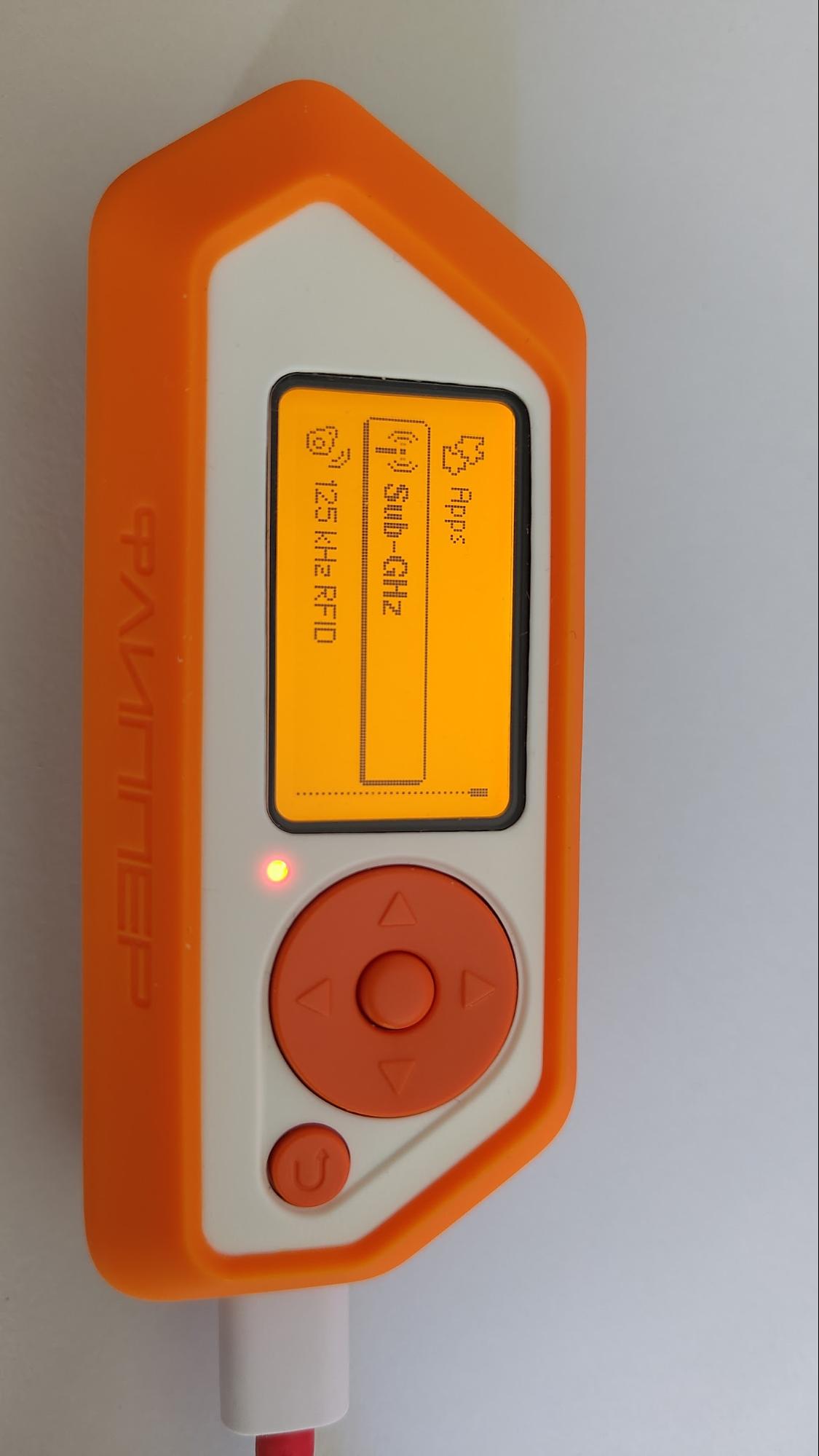
For example, to use Flipper’s RFID functionality, simply press the main button (the button in the middle of the D-pad), and use the up/down buttons until you scroll to the “125 kHz RFID” option.
Press the main button once more, and you’ll see a sub-menu (our menu has four options), specifically related to the use of the RFID functionality (Read, Saved, Add Manually, and Extra Actions).
Finally, if your Flipper Zero crashes for whatever reason, you can reboot it by holding down the left and back buttons for five seconds.
Key Functionalities
Flipper Zero can be used to gain a true appreciation for how many software-defined radio and proximity-based technologies work and put them to use for many tasks in emulating or reproducing these technologies.
The technologies that the Flipper operates on include:
- Radio Frequency Identification: RFID, which is used often in proximity cards for access control systems.
- Sub 1-GHz Range wireless device control: Used across multiple end devices, including garage doors, IoT sensors, and doorbells, as well as smart devices like lightbulbs. Whilst car remotes often operate in this frequency range, most modern cars use rolling-code encryption technology, making it impossible to use the Flipper One to lock or unlock cars.
- Near Field Communication (NFC): Works similarly to the RFID technology, providing access to higher-frequency proximity cards—for example, a prepay bus pass and contactless credit card using PayWave uses NFC.
- Bluetooth: A well-known low-distance radio technology is supported to allow you to connect your Flipper Zero to third-party devices and smartphones.
- Infrared: Flipper Zero has a built-in library of signals to control common devices such as TV remotes, air conditioners, and stereos. Otherwise, you can program the Flipper to understand other Infrared sequences using another remote control.
- iButton: Also known as 1-Wire keys, these are commonly seen on door access controls. It’s quite an old technology, however, it’s still used across the world. As the 1-Wire protocol doesn’t have any authentication, Flipper Zero can easily read and store the keys in its memory.
- USB Type-C: Although the primary purpose of the USB port is to charge or flash the device, it can also be used to provide USB signals to other devices in a method called BadUSB.
- Expandability: Flipper Zero can be expanded in many ways—similarly to a Raspberry Pi or Arduino—using general-purpose IO (GPIO). Flipper Zero already has some expansion boards, including the official Flipper Zero WiFi dev board, SubGHz range expander boards, and SAM Expansion boards with HID Seos and iCLASS. These can greatly enhance the use of the Flipper Zero for red teaming purposes.
Red Team Hacker Bundle: Learn Hacking Online Red Team Style
Train like a professional adversary with the Red Team Hacker Bundle. Learn offensive security tactics, privilege escalation, and post-exploitation techniques used by real red teams.
Flipper Zero Hacking Projects
What can you do with a Flipper Zero? Now that we’re good to go, let’s walk through some Flipper Zero hacking projects.
Disclaimer: Flipper Zero for Hacking
Please note that Flipper Zero is intended for educational and experimental purposes only. Users are responsible for ensuring their activities comply with local laws and are conducted ethically.
Cloning RFID Access Cards
In this example, we’ll be copying—or “cloning” an RFID access card. RFID access cards are in widespread use worldwide, mainly to replace physical keys. Note that some of the RFID cards are in a circular “keyfob” format, however work in generally the same way as their card counterparts.
What Is RFID Technology?
Radio Frequency Identification is a technology that uses magnetic fields to automatically identify and track tags attached to physical objects.
These tags contain electronically stored information and can be passive—powered by the electromagnetic field generated by the reader—or active—having their own power source. RFID is used in a variety of applications, including access control, inventory management, and even in passports and contactless payment systems.
Key Information
Once we have cloned an RFID card, we can replay the RFID information from our Flipper Zero—negating the need for an RFID card—or clone it onto another RFID card of the same type rather than from the original card. This means that we no longer need the original key card to open a target door.
How to Clone an RFID Access Card
First of all, enter the main menu by pressing the main button, which is located in the middle of the D-pad. Scroll down until you can see the “125 kHz RFID” and press the main button again. You’ll see “Read” at the top of the submenu.
With the access card, you want to clone at the ready, so place it underneath your Flipper Zero. Press the main button to read the card. Within a few seconds, you should hear a chirp and some information showing what type of card has been read.
Next, press the right D-pad direction key, and you’ll be presented with three options: “Save,” “Emulate,” and “Write.” If you want to save the RFID key values for use later, press the main button on “Save.”

If you want to use the newly stored RFID values straight away, select “Emulate.” If you want to clone the RFID card that you just read onto another RFID card or fob, simply use the D-pad to select “Write” and press the main key.
Move the Flipper Zero over the new card or fob, and in a few seconds, you should see “Successfully written” appear on the screen. You have now cloned a key.
If you have written the key values to the Flipper Zero, rather than an RFID key fob, you can go back into the “Saved” menu at any time, select the card you saved, press the main button, and press “Emulate” to replay the RFID data to a target receiver.
BadUSB and DuckyScripts
In this example, we’ll be using the demo BadUSB script which is provided on the Flipper Zero to demonstrate the capabilities of a BadUSB attack. You can create your own BadUSB “DuckyScripts,” or obtain pre-made scripts online to deploy payloads that achieve a multitude of attacks.
What Is BadUSB/KBUSB?
Most of the functions of the Flipper Zero are based on radio technology. However, BadUSB is a security exploit that leverages USB to execute malicious code on a computer without the user's knowledge.
It exploits the trust that computers inherently have in USB devices—specifically the keyboard, which doesn’t need setting up before it’s used. This makes BadUSB a potent tool for cyberattacks, such as spreading malware or hijacking user inputs.
BadUSB was first revealed in 2014, but later popularised by Hak5 when they released the USB Rubber Ducky, a simple USB stick that pretended it was a keyboard by using USB enumeration techniques.
The RubberDucky provided a simple programming language called “DuckyScript” which allowed the user to perform automation payloads such as credential exfiltration, remote code execution, access shells and much more.
Key Information
The DuckyScript language is a simple yet flexible language that allows you to deploy payloads to a target computer via a “RubberDucky” USB stick or, in this case, via the FlipperZero.
Payloads available on the official Rubber Ducky github include code for remote access, command execution, exfiltration and even mobile phone-based exploits amongst many others.

How to Perform the Action
If you want to create your own DuckyScript for the BadUSB attack or download one that someone else has made, you’ll need to copy it onto the SD Micro card.
Eject your card carefully from the Flipper Zero and insert it into your computer. In our case, we had to use a microSD card adapter.
In your computer’s file browser, you should see the SD card appear—ours is simply called NONAME. Inside the card’s folders, you’ll find a folder called badusb.
Simply copy your DuckyScript payload to that folder. You may wish to rename it to something helpful to remember it by.

Once you have copied your payloads to the MicroSD card, ensure you eject it safely from your PC’s operating system, then re-insert it into your Flipper Zero carefully. They can snap easily!

Once the card has been inserted, insert the USB cable into your Flipper Zero and the other end into your target computer. Press the main button and use the up/down keys on the main menu until you find “Bad USB.”
Press the main button and you’ll see the various payload files that are in the “badusb” folder on your microSD card, including any that you just copied. Move up/down to select the payload you wish to execute.
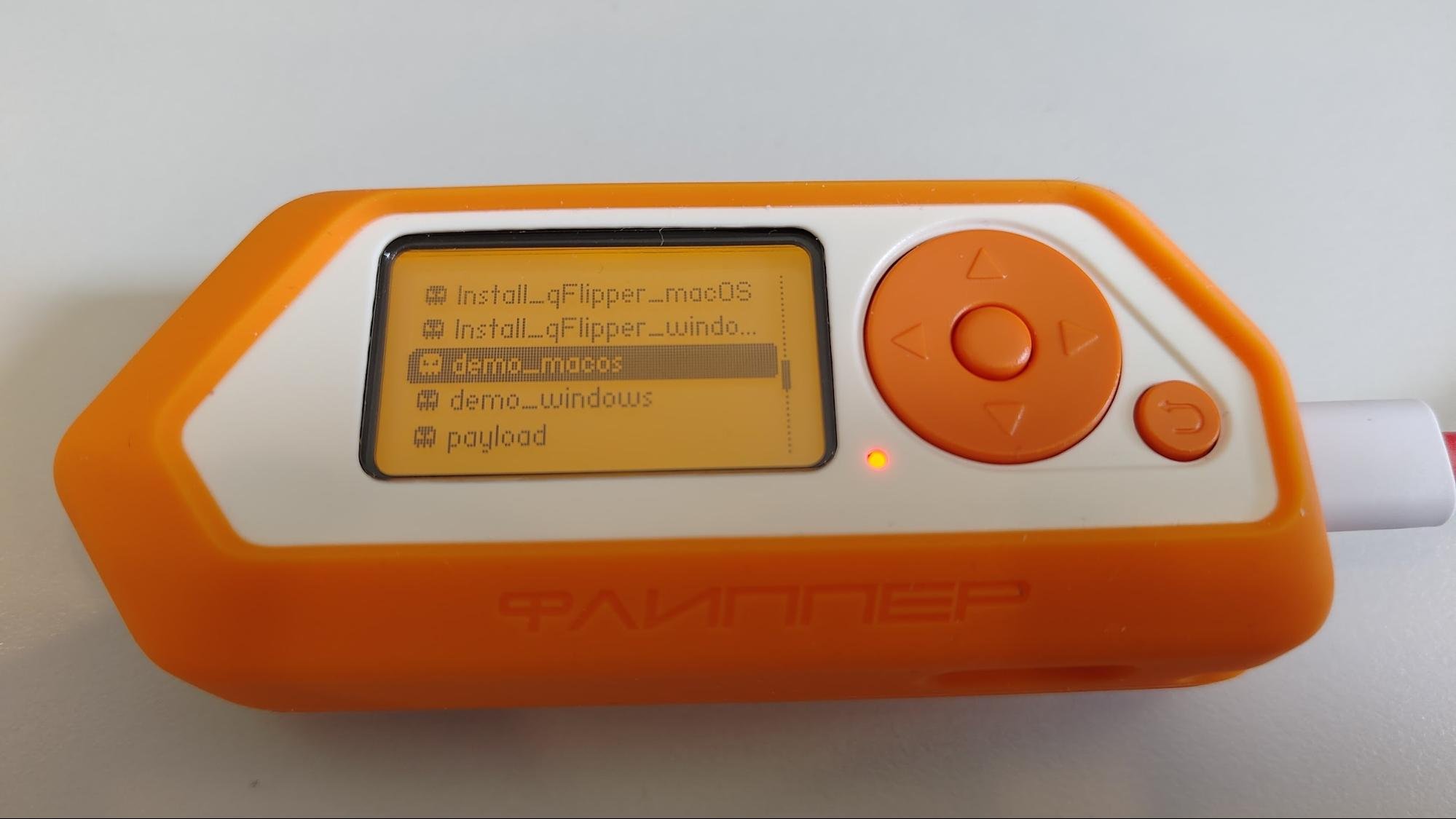
In this example, we’re using the demo_macos payload which is provided with Flipper Zero. Press the main button on the payload that you’ve selected.

When you’ve connected the USB cable to both the Flipper Zero and the target computer, you’ll see an image similar to the one above. Now, simply press the main button to execute the payload.
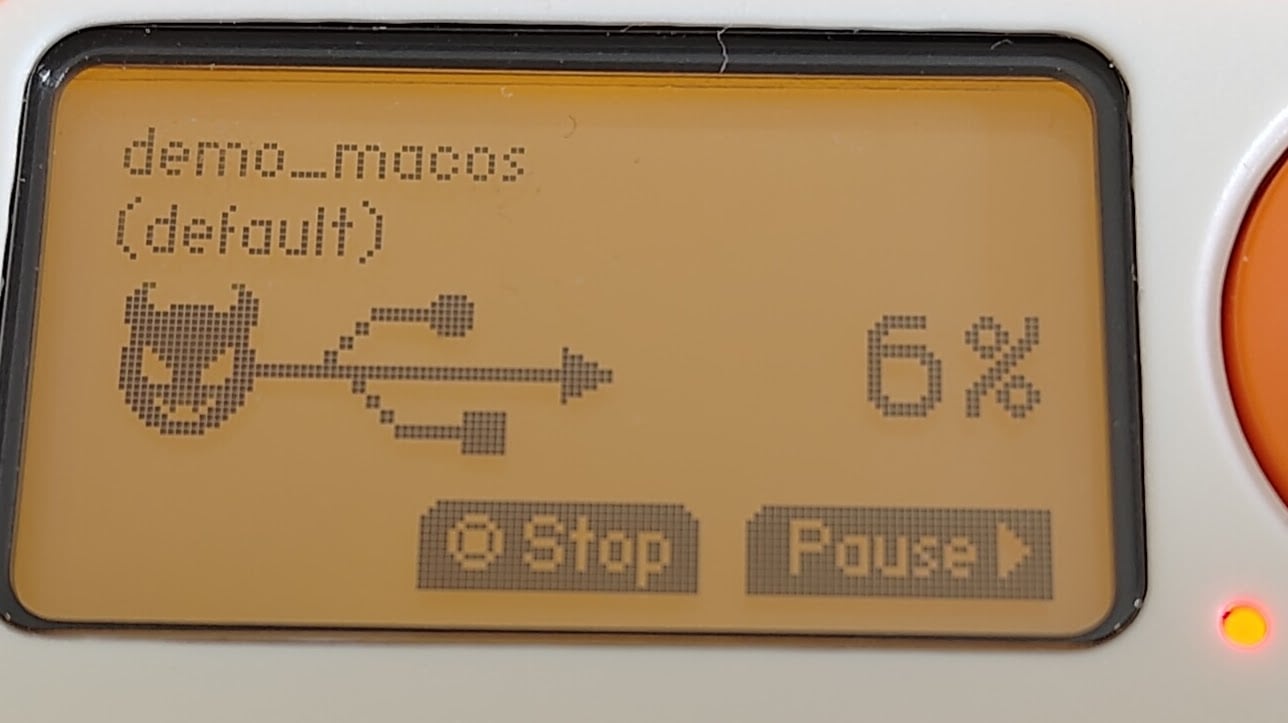
If the payload script is working correctly, you should see a progress indicator as above.

As you can imagine, with physical access to a computer, in just a short amount of time you can compromise it easily and make it perform any sort of action that would take a significant amount of time without the BadUSB compromise.
Cloning a Garage Door Opener With Sub-GHz Wireless
In this exercise, we’ll be cloning a garage door opener from a distance of up to 35 meters. Flipper Devices says it can work at up to 50 meters, but your mileage may vary.
What Is Sub-GHz?
Sub-GHz refers to wireless communication frequencies that are below 1 GHz.
These frequencies are commonly used for long-range communication due to their ability to penetrate obstacles and cover greater distances with less power compared to higher-frequency signals.
Sub-GHz communication is widely utilized in applications like remote control systems, IoT sensors, doorbells, smart bulbs and metering.
Ethical Hacking Courses Bundle: Learn Hacking for Beginners
Just starting out? The Ethical Hacking Courses Bundle teaches you how to think like a hacker, exploit common weaknesses, and build the foundational skills for penetration testing.
Key Information
To perform this clone, we’ll need to have access to the original garage door opener, or at least be present at the same time as the garage door is opened.
Garage door openers tend to be less encrypted than modern car remotes, so it’s more likely to be successful, especially on older ones.
That said, newer garage door openers use something called “rolling code encryption.” If your garage door uses this technology, then it won’t work with your Flipper Zero.
How to Perform the Action
Firstly, enter the main menu by pressing the main button in the middle of the D-pad and move up or down until you see “Sub-GHz.”
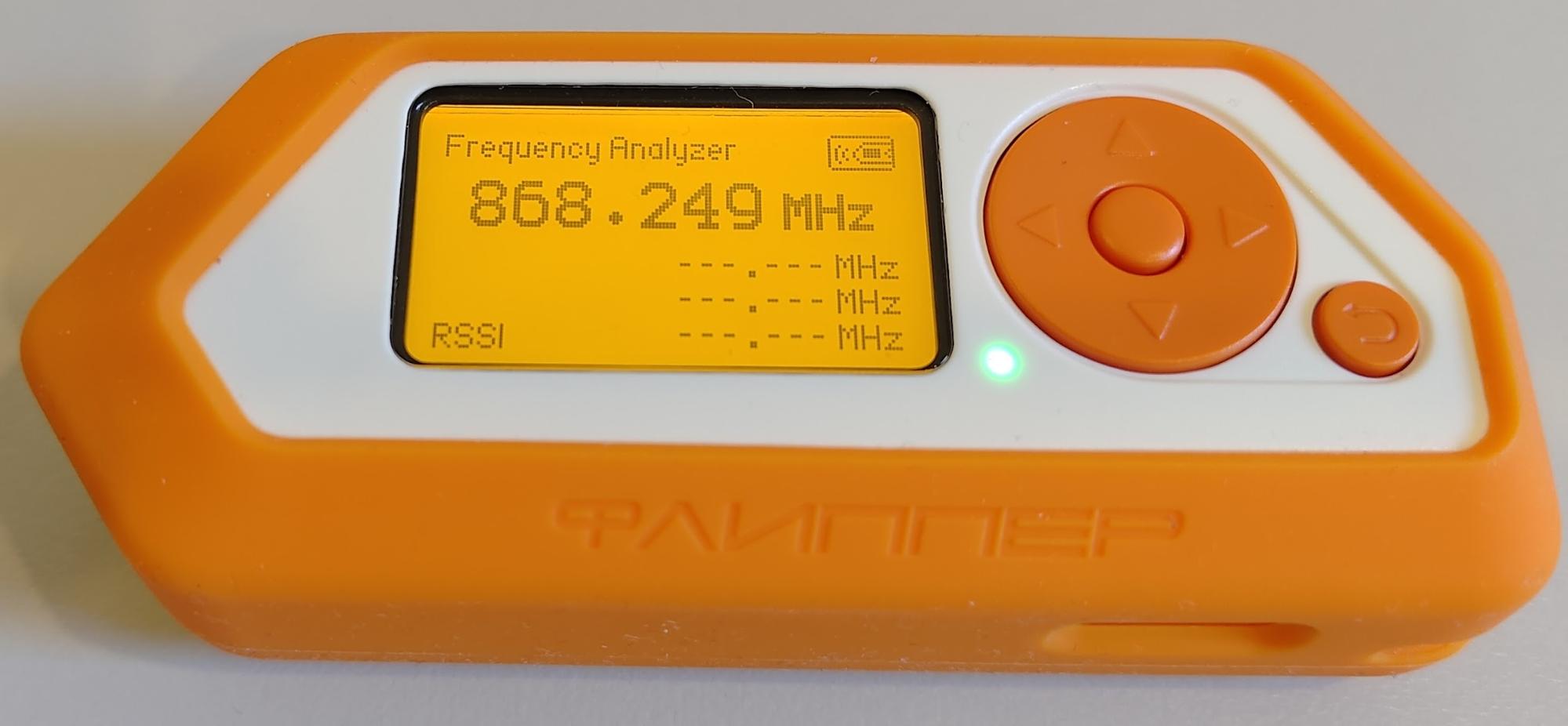
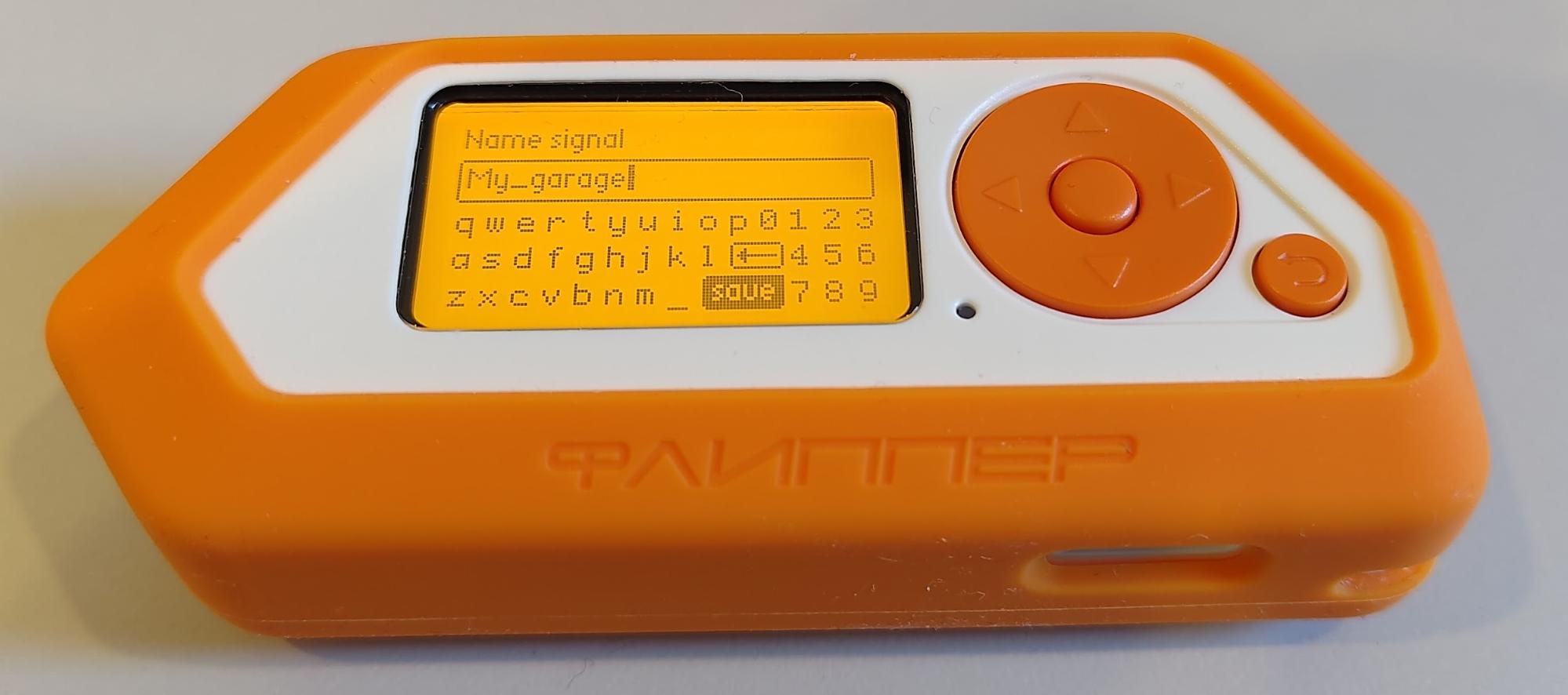
Next, move the D-pad down to “Frequency Analyzer” and press the main button. Press the button on the garage door and note the frequency that the remote emitted. If you have a two-button remote, press the second button also, so you can take note of it, too.
Now, we press the back button and select “Read RAW.” You’ll see a frequency recorder image.
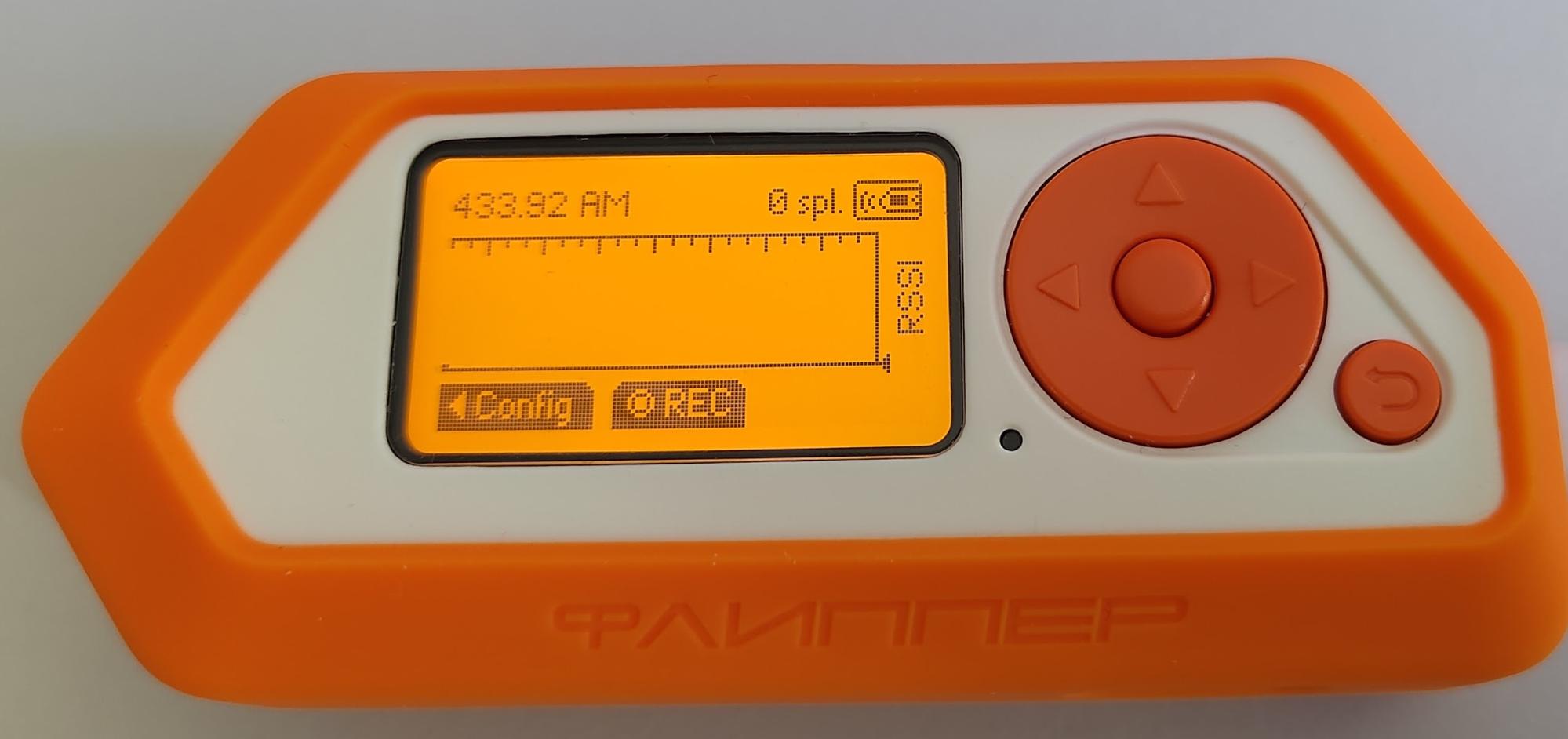
Press the left arrow on the D-pad to select “Config” and configure the frequency you noted down earlier. If you have more than one button with a separate frequency, you’ll need to repeat this process.

You can change the frequency values to match the ones you found on the frequency analyzer by using the left and right keys.
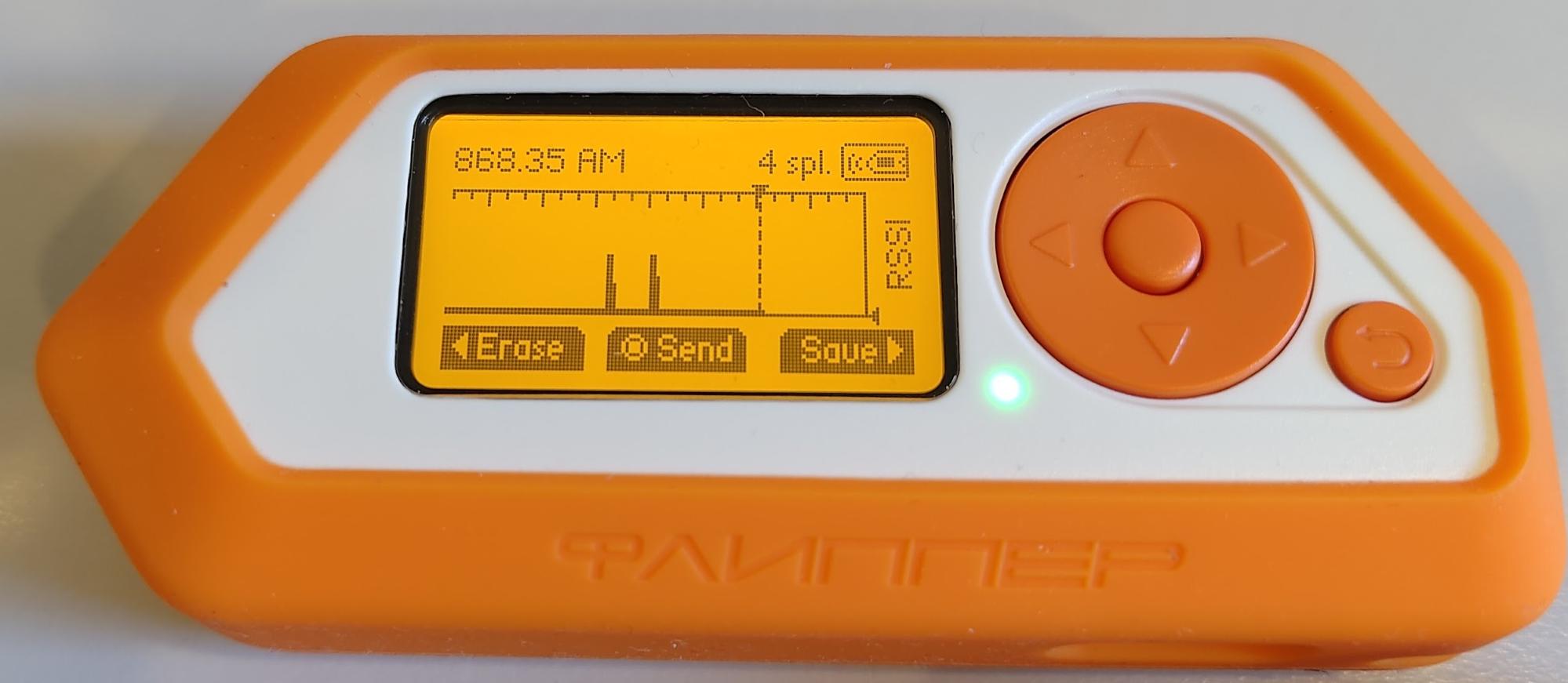
Next, press the back key and the Flipper Zero will return you to the frequency recorder you saw when you entered “Read RAW.” Press the main button and it will start Recording.
Press the garage door button once again and you’ll notice the display shows the frequency being read by a “spike” in the image.
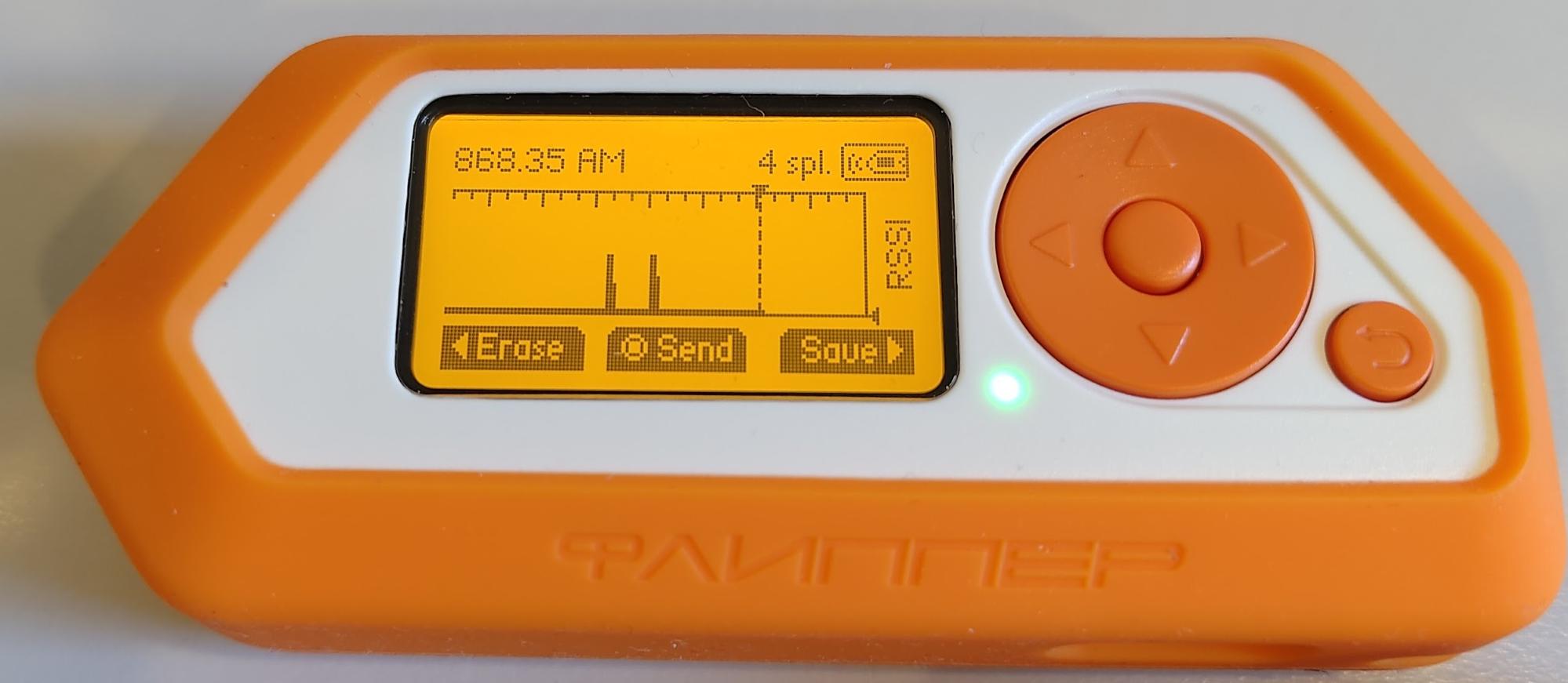
Now that you have captured the signal, you can either press the “Save” feature by pressing the right button to save this signal to use at a later time or, if you want to send it immediately to the receiver, you can use the “Send” feature by pressing the middle button.
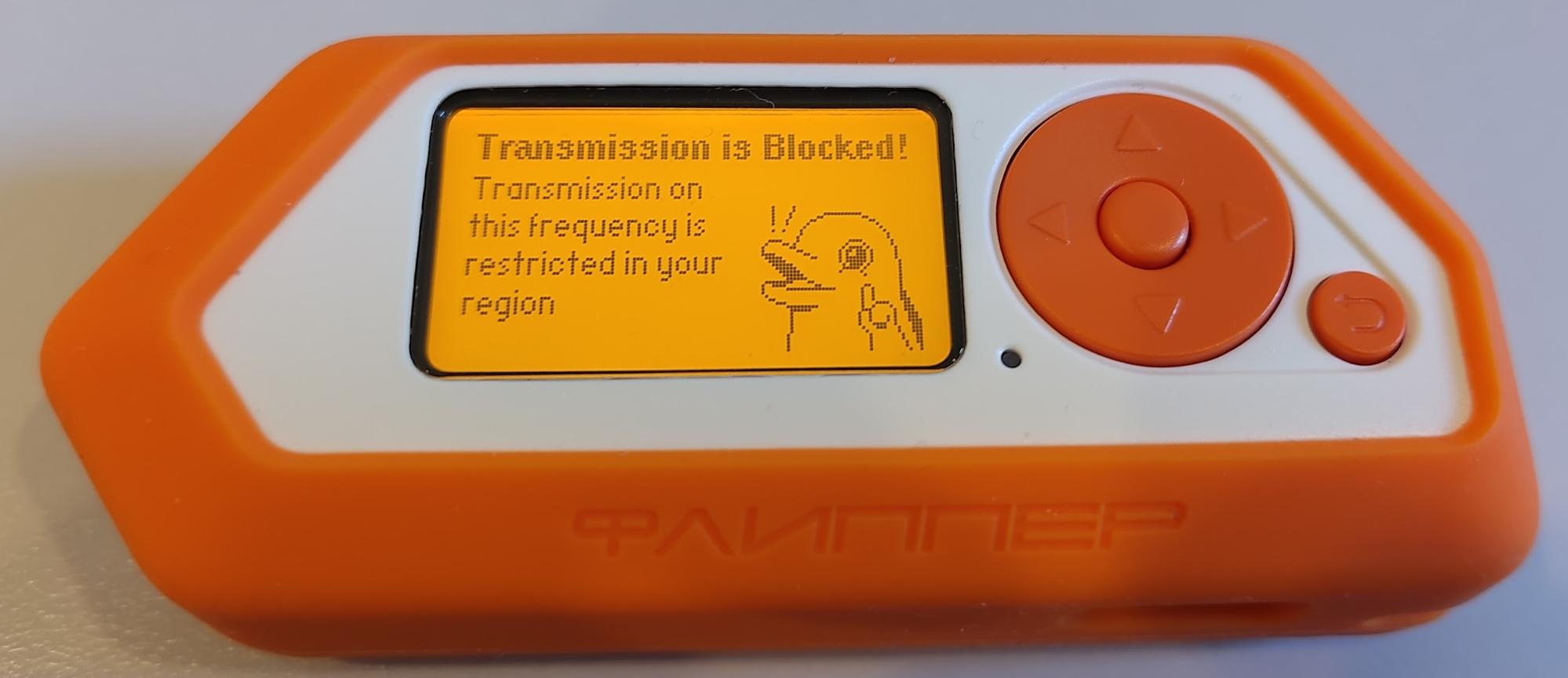
Note that some frequencies may not be allowed to be transmitted in your location using the authentic Flipper Zero firmware.
Conclusion
The Flipper Zero is a wonderful tool that brings to light the world of Software Defined Radio (SDR), a world seldom understood by those who aren’t manufacturers or part of the SDR hacking world.
With Flipper Zero, however, this realm is now more accessible and exciting for hobbyists and hackers alike.
Many individuals have misunderstood Flipper Zero as a device designed for nefarious purposes. However, it can be seen as an educational, multi-purpose tool that brings SDR and experimentation together in a fun way.
Like most tools, if people want to use them illegally, they’ll often find a way.
If you’re interested in understanding the world of Software Defined Radio in a multi-tool form, then the Flipper Zero is a great, user-friendly introduction to this world. Plus, it makes for a great conversation topic with friends at the dinner table.
If you want to get hands-on with more hacking projects, consider joining the StationX Master's Program. With access to over 30,000 courses and labs, as well as mentors, custom certification roadmaps, study groups, and more, StationX can take your hacking skills to the next level.
Master cyber security from beginner to advanced with our Complete Cyber Security Course Bundle covering network security, ethical hacking, endpoint protection, and online anonymity. Click the banner below.
The Complete Cyber Security Course Bundle includes:
- The Complete Cyber Security Course! Volume 1: Hackers Exposed
- The Complete Cyber Security Course! Volume 2: Network Security
- The Complete Cyber Security Course! Volume 3: Anonymous Browsing
- The Complete Cyber Security Course! Volume 4: End Point Protection
- The Complete Cyber Security Course Practice Test - Volume 1




