It’s the Holy Grail for any money-minded hacker: the discovery of a previously undetected flaw in a major software system, giving you the opportunity to cash in on your find for a tidy reward.
Exploit vendor, Zerodium has just hiked its bounties for zero-days in certain types of virtualization software. Across the board, rewards seem to be on the increase (we’re talking six or seven-sum figures for the most significant finds) - with no end to the ‘bounty bonanza’ in sight.
Here, we take a closer look at what’s on offer from the likes of Zerodium, and at what’s driving the demand for bug bounty hunters…
Add a header to begin generating the table of contents
Zero-Day Vulnerabilities, Exploits & Bug Bounty Hunters: What You Need to know…
A zero-day vulnerability is the name given to a newly-identified software security flaw. If left unfixed, it offers hackers the opportunity to create a package designed to specifically target that bug in order to compromise user systems. This type of package is known as a zero-day exploit.
The vulnerability gets its “zero day” label because the clock is ticking. Once it’s discovered, the developer has zero days to plug the hole by way of a bug patch roll-out before its existence becomes more widely exposed - and before hackers have the chance to create an exploit. (As a side note, it’s the reason why it’s never a good idea to ignore a patch update alert).
Bugs are a fact of life - and keeping on top of them all is an endless task. Two decades ago, Netscape first developed the bug bounty idea - i.e. paying independent developers for discovering flaws.
The idea caught on. Practically all major tech players - Google, Microsoft, Apple and Facebook included - now have a vulnerability reward program (VRP) in place. There’s even a ‘Hack the Pentagon’ program in play.
There’s now also a strong crowdsourcing element to the bug bounty market. Platforms such as HackerOne, Bugcrowd and Zero Day Initiative (ZDI) help businesses to coordinate their vulnerability detection efforts and connect businesses with independent researchers.
Who is Zerodium?
Established in 2015 and based in Washington DC, Zerodium specialises in acquiring “high quality exploits”.But unlike platforms such as HackerOne and Bugcrowd, the discoveries made by bug hunters are not sold back to the developers. Instead, Zerodium sells on its research to a very select client base, consisting mostly of governmental bodies who are concerned with cybersecurity and zero-day defences.
Zerodium’s latest announcement
Earlier this month, Zerodium sent out a Tweet…
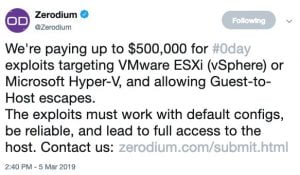
This latest bounty from Zerodium is focused on the following cloud technologies:
- Hyper-V, the technology at the core of Microsoft’s Azure public cloud computing platform,
- VSphere by VMWare (a subsidiary of Dell), which is used on Amazon’s secure cloud services platform for businesses, (Amazon Web Services).
These are both types of virtualization software (aka hypervisors), which essentially enable users to run multiple ‘virtual’ machines using a single piece of computer hardware.
Before this tweet, Zerodium was offering $200,000 for vulnerabilities relating to Hyper-V and VMWare exploits. With this move, Zerodium has more than doubled its reward for VMWare ESXi exploits. It’s also the first time that Hyper-V has been included as part of the company’s bounty program. It’s worth noting that the amount on offer for Hyper-V exploits is double the maximum amount that Microsoft itself is currently offering through its bug bounty program.
Zerodium states that whereas previously, there was little or no interest in this type of exploit from its customers, there is now a clear demand for it. Presumably this is in response to the steady growth in the take-up of cloud services – especially for website and IT infrastructure hosting.
What other rewards are on offer?
Highlights on Zerodium’s current payouts menu include a reward of up to $1 million for a Windows remote code execution – and similar amounts for significant exploits relating to WhatsApp, SMS and iMessage.
For the most significant exploits, it seems that the rewards on offer are on the increase. For instance, earlier this year, Zerodium hiked its maximum reward for a zero-click Apple iOS jailbreak from $1.5 million to $2 million.
The bigger picture on bug bounty hunting
In January, Tesla declared that there’s a free Model 3 on offer to any cybersecurity researcher who can hack the car’s system. But beyond the headline-grabbing rewards for the most significant exploits, there’s a much wider market for uncovering more routine security flaws.
As an example, the ‘Hacktivity’ roundup on the Hackerone site provides a snapshot of the type of activity the platform’s army of independent researchers are involved with. Open redirects, broken authentications, missing access controls and cross-site scripting all feature heavily.
The bounties paid for these bounties tend to range from a couple of hundred dollars up to around $20,000.
Last year’s State of the Bug Bounty report from Bugcrowd suggested that the average payout was $781, up 73% on the year before. Meanwhile, Gartner predicts that the proportion of enterprises using crowdsourced security testing platforms is set to explode from its current level of 5% up to more than 50% in 2022.
Here’s the upshot: businesses need bounty hunters. At current levels, there will be a global shortfall of cybersecurity pros of close to 2 million by 2022. If companies do not have the in-house resources to keep on top of vulnerabilities, then outsourcing the job is the only answer. And while a million dollars or a new Tesla might be a little unrealistic, getting involved in bug bounty hunting can help you develop a highly attractive side-hustle!
How to become a bug bounty hunter
First register on platforms such as HackerOne, Bugcrowd and Zero Day Initiative (ZDI). Then improve your hacking skills so you can find more bugs! These are my recommended resources.
The Complete Ethical Hacking Course Bundle (90% off Coupon)
https://www.stationx.net/hack90
The Complete Python for Hacking and Cyber Security Bundle (87% off Coupon) https://www.stationx.net/python
The Complete Nmap Ethical Hacking Course (85% off Coupon)
https://www.stationx.net/nmap
Ethical Hacking with Kali Linux, Snort and Wireshark (87% off Coupon)
https://www.stationx.net/kali
Network Hacking Continued - Intermediate to Advanced (87% off Coupon) https://www.stationx.net/advanced-network-hacking
A Bug Hunter's Diary
USA: http://amzn.to/2yGL0jn
UK: http://amzn.to/2zHjIqB
The Web Application Hacker's Handbook: Finding and Exploiting Security Flaws 2nd Edition
USA: http://amzn.to/2yHGO16
UK: http://amzn.to/2zGJHhK
The Hacker Playbook 2: Practical Guide To Penetration Testing
USA: http://amzn.to/2xYABAz
UK: http://amzn.to/2yVdmXD
Rtfm: Red Team Field Manual
USA: http://amzn.to/2xeSGGg
UK: http://amzn.to/2xrAEAJ
Penetration Testing: A Hands-On Introduction to Hacking: Georgia Weidman
USA: http://amzn.to/2gvNgji
UK: http://amzn.to/2z9C3Am
Hacking: The Art of Exploitation 2nd Edition
USA: http://amzn.to/2ztGlyF
UK: http://amzn.to/2xqX3xU
The Database Hacker's Handbook
USA: http://amzn.to/2xXICRj
UK: http://amzn.to/2yTcxym
The Oracle Hacker's Handbook: Hacking and Defending Oracle
USA: http://amzn.to/2gAmMAX
UK: http://amzn.to/2xpi1gJ
Underground: Tales of Hacking, Madness, and Obsession on the Electronic Frontier
USA: http://amzn.to/2xexfVQ
UK: http://amzn.to/2zP8uBj
TCP/IP Illustrated
USA: http://amzn.to/2yKTVk3
UK: http://amzn.to/2zGbRti




“up to”…. I will give you “up to” $1 million dollars to drive over and wash my car for me.
keep your up to 1 mil. I’ll keep the car
Sorry, it has a private key not a public key. You just get to wash it…. ;-)
Thanks for the info Nathan! Love your articles.
As more people are getting into bug bounty hunting, it is necessary to focus more on how things work instead of running tools.