Ever tried to paste a password into a log-in field, only to be told to type it in manually?
I really hate it when websites do this.
Some websites still don’t accept pasted passwords, even though the reasoning behind such a policy is pretty weak. In fact, because it stops password management tools from working properly, a restriction on password pasting can actually make users less secure.
This annoyance bit me recently, which prompted me to write this article. I had to open a business account with a European bank. When asked to create a password I generated a random 45 character password, one with symbols, numbers, upper and lowercase characters etc. The usual to make brute forcing it hard. Of course I come to login on the website and the app and try to paste the password from my password manager. NO. Not allowed, the site and the app have disabled pasting!! Which means I have to type in my 45-character random password every time I log in!!!! OR find a way around it.
Here’s a closer look at the issue, and how you can get around it.
Why do companies have a stop password pasting (SPP) restriction?
Occasionally, you’ll still come across websites that stop you from pasting passwords into the log-in box. Usually when this restriction exists, it’s there by design: i.e. the HTML code used on the website specifically prevents a pasted fragment from being entered into the field.
So why do companies deliberately include this block? It’s not exactly clear. As the UK’s National Cyber Security Centre (NCSC) points out, there’s no rule, technical standard or best practice point that recommends it.
There are a number of possible justifications for it. Although once these reasons are scrutinised, they don’t really stand up:
It prevents brute-force attacks. The argument is that it stops malicious software from repeatedly pasting password guesses into the box to crack it. But this ignores the fact that the website should, in any event, have controls in place to identify and block a high number of log-in attempts relating to a single account.
Avoiding sensitive data in the clipboard. The idea is that you shouldn’t have sensitive information such as passwords hanging around on your clipboard. This is because malware apps have the ability to scrape your clipboard. The trouble is, the majority of malware apps with clipboard-scraping capabilities are able to read your keystrokes, too. So being required to type in your password does nothing for malware protection.
Pasting prevents you from remembering. In theory, the ability to paste your password provides less of an incentive to remember it. But in reality, the average person has 70-80 active passwords. Even if you wanted to, you are never going to memorize all of them.
Password manager tools and pasting
- As this year’s Verizon Data Breach Investigations Report revealed, the majority of hacking-related breaches involve the use of lost or stolen credentials.
- Poor password hygiene is behind a lot of these breaches. People still reuse passwords, often across both personal and work accounts, even though they know they shouldn’t.
- Best practice says you need a unique password for each account. Ideally, these passwords should be unique, long, and consisting of a combination of letters, numbers and symbols.
- It’s a practical impossibility to memorise a string of such passwords. That’s why a password manager tool can be so useful.
- Your password manager can generate a secure, random password for each account. Later, when you need to log into a site, you type your master password into the password manager. The tool will then automatically paste the login information into the website.
- But if the website doesn’t allow pasting, it interrupts this process. For the user, it means having to manually input a long, randomly generated and unfamiliar password. It’s a needless hassle. In fact, for some users, it’s going to cause them to revert back to using a weak, easily-remembered password.
Chrome Workaround
We’ve seen a couple of fixes that allow you to bypass the ‘no password pasting’ restriction: one for Chrome and one for Firefox. Here they are…
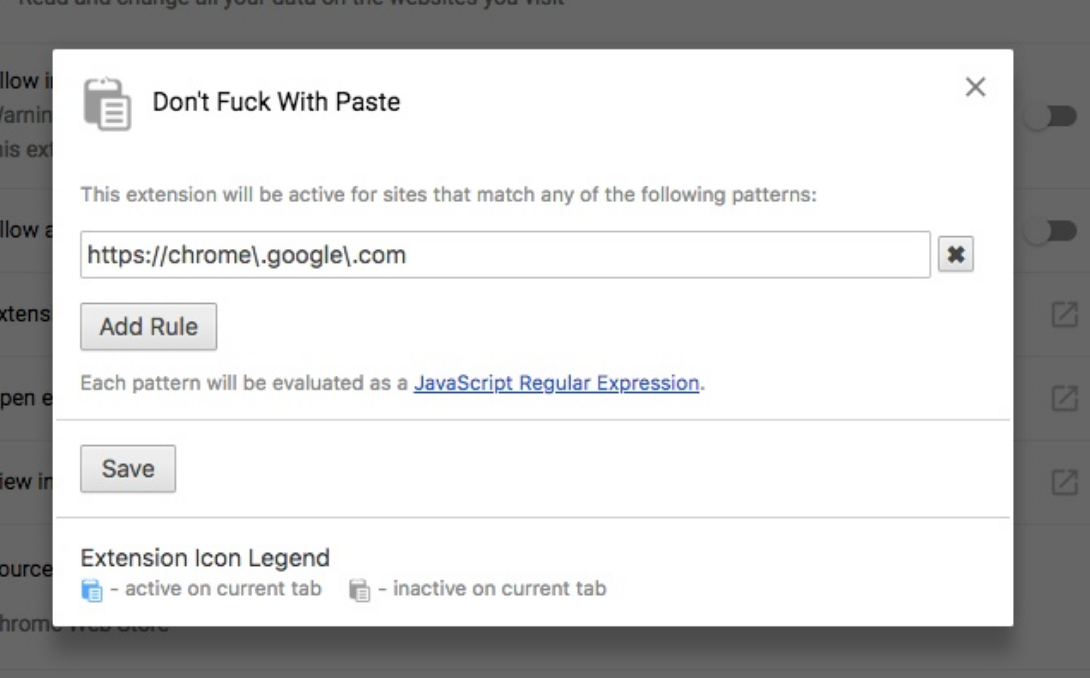
Get the Don’t F*ck with Paste extension here. Created by developer, Vivek Gite, the extension instructs your browser to bypass any paste restrictions on the page.
Firefox Workaround
You can fix the problem by changing the browser’s behaviour in the settings.
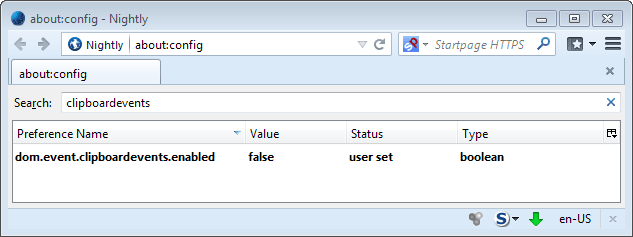
Go to about:config in Firefox. Click the “I’ll be careful, I promise!” disclaimer to carry on.
Now, in the search box, search for dom.event.clipboardevents. A single entry should come up in the list of preferences.
Double-click on the setting. This should change the value from “true” to “false”. Now, you should be able to copy and paste without any website-specific restrictions stopping you.
There is a downside to doing this that I found. It stopped me being able to paste into Google sheets and docs. So I use Chrome and Firefox interchangeable as needed.





I must say I have to completely agree with this. I have had to use passwords far less secure than my usual because of it. On a side note, it is also frustrating when passwords are limited to something like twelve to fifteen characters or so – same result: far more open to brute force than if I were allowed to use the stronger passwords from my password manager. Great blog post btw :)
Yes that is also annoying.
great tip thanks.
My pleasure.
Came across this issue myself the other week. Not a big fan of it.
Yep.
“Prevents brute force attacks” : the guys behind this stupid idea have poor knowledge of what a script is and how to use tools like curl to automate it.
I also hate this. Great tips btw. Thanks.
So true!
Appreciate this so much!
You are welcome.
Awesome tip, and it couldn’t have come sooner. I logged into one of my Credit Card accounts today to make a payment, and WHAM there it was NOTHING when I attempted to paste my extremely long, meaningless password. I used you quick work around and it worked like a charm in less than 60 seconds !! Thanks
Brilliant.
We really need to get rid of passwords, not making their use easier.
We will not get rid of passwords in my lifetime. Even if something like SQRL replaces them, passwords will remain for some systems as people know how to use passwords.
Fantastic!!! thanks!!! next talk about passwords managers…it is a must!!! and very related with this article.
Thanks Nathan! Would the use of a 2FA hardware token such as a Yubikey bypass any headaches such as paste blocking or the dreaded captcha every 20 minutes? BTW Loved your CCS course.
Thank you. 2FA usually uses passwords as the first factor. So it wont stop paste blocking being an issue with passwords.
A brilliant post and solution to a really irritating problem. Thanks Nathan, this problem has been getting worse lately, just used the firefox solution and it worked within seconds. Now does anyone know a work around for android, where apps prevent you from screengrabs? That’s another irritant for me………?
Thank you. Take a picture with another phone :)
Great tip and I’ll be using it and passing it on.
Do you have any way around sites that don’t allow you to autofill from Lastpass? St George Bank (in Australia) is a case in point. It apparently changes the info when it’s pasted in so it fails
Changes the info! why!?
This really makes users frustrating, thanks for the solution, Nathan!
turning this too false makes it so I cant paste text in facebook chat… FYI…. when I choose paste on my mac, the facebook chat window would disappear and the message would not be sent. works now that I changed it back to “true”.
I’ve made a simple open source tool to help pasting passwords in such fields (at least on the desktops). It is browser independent and you don’t have to mess with any settings. https://github.com/pqsec/passkb