We’ve been reminded that when it comes to malware delivery, threat actors tend to prefer tried and tested methods.
A recent roundup from Cofense Intelligence included a breakdown of malware loaders analysed by volume for the month of August 2018. It found that Microsoft Office documents containing malicious macros accounted for 45% of all deliveries. The second most popular method (accounting for 37% of cases), involved exploitation of CVE-2017-11882, a Microsoft Office Memory Corruption Vulnerability.
Individuals and businesses need to focus on practical fixes that reduce their attack surface...
Malware delivery via macros: the basics
From Excel data entry through to filling in fields on Word-based forms, macros are meant to take the donkeywork out of routine processes.
Written in Visual Basic for Applications (VBA), a macro is a program that can automate a set of multiple operations so that they can be performed with a single keystroke. It’s a simple idea: you basically ‘record’ your procedure - and then ‘play back’ the macro each time you need to repeat the process.
Macro capabilities have been part of the Microsoft Office suite for decades. At first, these macro scripts were enabled by default. But the trouble was that any macros embedded into a Word or Excel document would essentially be automatically executed as soon as the document was opened.
Malware distributors soon caught on to this. The setup meant that hackers could embed malware as macros in Office documents. In the classic ‘phishing scenario, these documents are emailed as attachments to targets, along with a convincing invitation to open them. Simply even by opening that file - or by hitting a common keyboard shortcut - the malware could be executed.
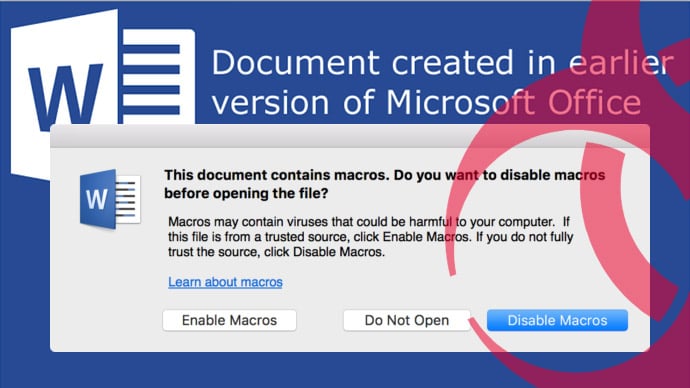
Microsoft has of course wisely ditched the whole ‘automatic execution’ approach. That’s why, when a user receives an incoming document that has macros embedded, they get a message at the top of the page stating that macros have been disabled. The only flaw with this very basic safeguard (and it’s a big one!) is that it takes just one click from the user to cancel out the blocker and enable the script.
Who’s distributing malware via macros?
The answer is, pretty much everyone. Ease of set-up and distribution means that macros can easily be put to work by unsophisticated novices. But the big boys rely heavily on this form of delivery, too.
Notable examples over recent years include Locky ransomware, which has been distributed in large part by a combination of phishing emails and Office attachments featuring malicious macros.
The Cofense report shows how some of the most damaging packets on the current threat landscape are being delivered in this way. This includes ‘next gen’ ransomware such as GrandCrab as well as the latest incarnations of Geodo/Emotet, a prominent banking trojan.
Essential protection against macro/Office vulnerabilities…
Given that macros still top the list of favourite malware delivery methods, the takeaway is clear: good hygiene (including informing and educating end users) remains your best first defence. Pay particular attention to the following…
A blanket ban on macros. In other words, if your people don’t need them, then disable them on all incoming documents across your entire organisation.
Take a tailored approach to macro enablement. Truth is, of course, that from analytics through to payroll, use of macros is a fact of life for most organisations. Where ‘going nuclear’ on them isn’t an option, a mix and match stance is the next best thing. Office 2016 gives you a few handy options for this…
- “Disable all macros with notification”. Accessible via File menu, Trust Centre and then Macro Settings, this lets an administrator decide which macros to enable on a case by case basis.
- “Disable all macros except digitally signed macros”. Again, this is accessible via Macro Settings. Only those macros that originate from a certified publisher will trigger a security notification for you to decide whether to enable them (the rest are automatically disabled).
- Group policies. From the Trust Centre tab, open “Block macros from running in Office files from the internet”. Using this, you can opt to disable macros from any or all of email attachments/ documents from file-sharing sites and files from cloud service providers (e.g. G Suite and OneDrive).
Patch management. Hot on the heels of macros, the exploitation of CVE-2017-11882 came second in the Cosense list of malware distribution methods. This refers to a specific vulnerability in the Microsoft Office Equation Editor Component which basically allows users to insert and edit mathematical equations within documents.
Bear in mind that the report was for August 2018 - and the patch for this vulnerability was rolled out way back in November. Betting on unpatched machines for packet delivery still pays huge dividends for cybercriminals - so make sure you don’t get caught out.




Hi Nathan
Took a break off work to read this article. Very interesting and I will surely read it again!. Please keep these great articles coming :)
Hi Nathan, Thank you for making this article.
Appreciate the article Nathan
Very interesting and I will surely read it again!. Please keep it up!
Great article!
Macro malware is delivered as email attachments or inside ZIP files and these files have names that force or scare people to open them- for example, invoices, receipts, legal documents, etc.