Open source cyber security tools are as numerous as they are unique. With an abundance of open source tools on the market, it’s difficult to know which one you should be investing your time and energy into learning.
In this article, we’ll explore 20 of the most powerful and most used open source cyber security tools. Tools will be categorized based on what they do so you can quickly find the best open source tool that will help you specialize in the cyber security field that interests you most.
We’ll detail each tool, tell you why we like it, and show you where to get it.

What Is Open Source?
Open source software is software that allows users to view and modify the source code. In this way, open source programs are highly collaborative, peer-reviewed, and flexible. While most open source programs are free, not all are.
FOSS stands for Free and Open Source Software. These programs have the same characteristics as open source software but are also free of charge.
The opposite of open source is closed source. In this case, the program’s code can only be viewed and altered by its owner. In most cases, users must pay for closed source software.
There are numerous benefits to using open source, such as:
- Oftentimes open source programs are free
- Highly transparent, as the source code can be viewed by users
- Flexible as developers have the ability to amend code and customize it
- Arguably more secure as more developers are fixing the code and addressing vulnerabilities
Now let’s dive into the 20 of the best cyber security open source tools you can get your hands on.
Penetration Testing Tools
Find vulnerabilities and simulate real attacks with the help of these open source penetration testing tools.
ZED Attack Proxy (ZAP)
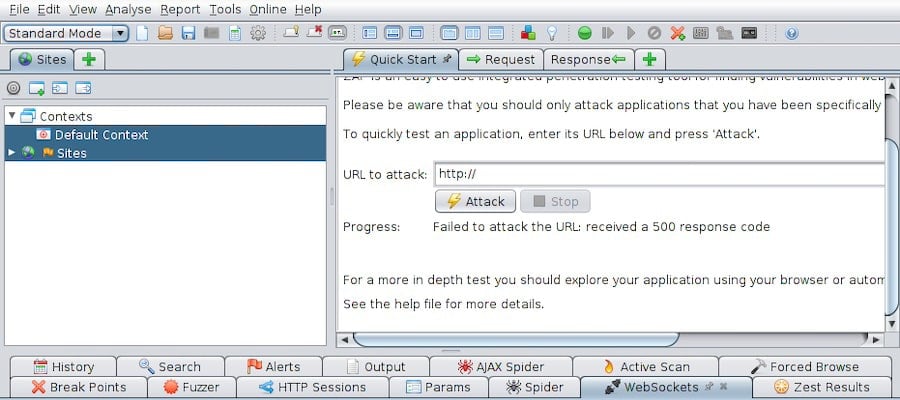
ZAP is an all-in-one web-app scanner tool. It’s 100% free, open source, and is updated and maintained by a team of hard working volunteers. Released in 2010 ZAP is used to scan web apps for vulneratilities. It’s also used as a proxy server that can alter HPTTS requests.
Why we like ZAP:
- It’s a comprehensive web-app security testing tool.
- Automatically scans web applications for vulnerabilities and cyber threats.
- Can go on the offensive and exploit found vulnerabilities via SQL injection or XSS.
- It’s the open source penetration testing alternative to Burp Suite
- Features include a passive scanner, web crawler, brute force attack capability, directory search, fuzzer and more.
You can download and learn more about ZAP here.
Metasploit
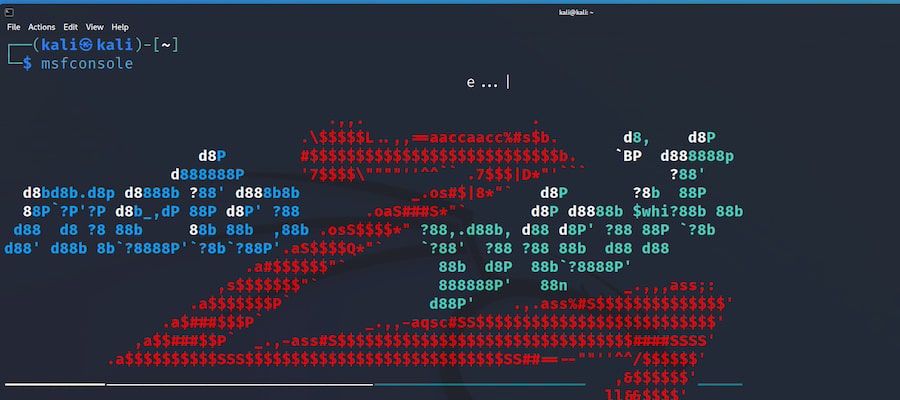
Metasploit is one of the first tools penetration testers learn to use. Everyone, from white hat to black hat hackers, uses this powerful penetration tool. Metasploit is easy to use, has a range of exploits already built in, and allows hackers to create easily deployed payloads.
Why we like Metasploit:
- Easy to test out and develop exploits against target machines and find security vulnerabilities.
- Can be used to automate the vulnerability scanning process.
- Allows even beginners to create and deploy payloads.
- After you perform an attack, Metasploit can be used to gather further information about a system of network via post-exploit techniques.
- Evasion techniques are included that allow the pentester to evade IDS.
- Used to test patch installations, for regression testing, and for vulnerability scanning.
Download and get started with Metasploit here.
John the Ripper

John the Ripper is an open source password-cracking tool. This CLI tool allows you to crack passwords using various approaches such as dictionary, brute force, and rainbow table attacks. The program runs in various modes, such as String and Wordlist mode, to crack passwords.
Why we like John the Ripper:
- Uses a variety of modes designed to crack passwords of varying complexities.
- Supports optimized and customized versions created by the community.
- Recognizes multiple hash types to crack a range of passwords.
- Leverages third-party plug-ins for increased customization.
- Has a plugin ecosystem that is supported by a growing community.
- Even beginners with little pentesting experience can use it.
Learn how to install John the Ripper as well as wordlists at Openwall.
Network Defense Tools
Detect unwanted or abnormal activity and troubleshoot your network by using the following open source tools.
Wireshark
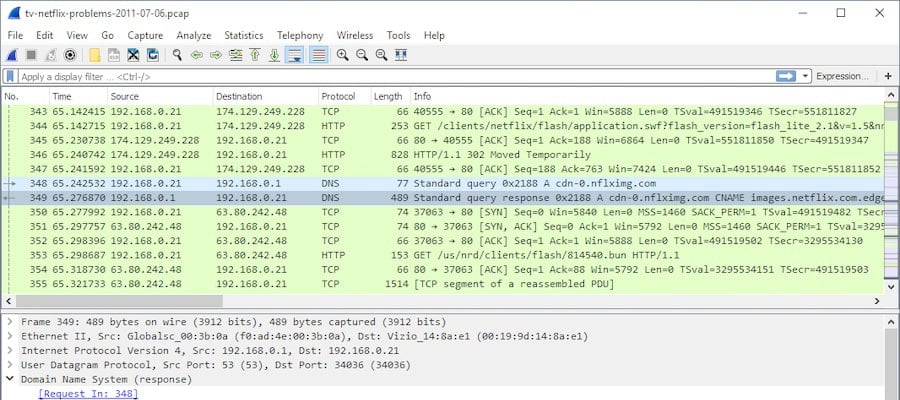
Wireshark is a popular network protocol analyzer used for network analysis, troubleshooting, forensics, and protocol development. It is a must-learn open source tool for SOC Analysts who want to learn how to capture, filter, and visualize network traffic, and quickly paint a precise picture of what is happening on their network.
Why we like Wireshark:
- Wireshark is 100% free.
- Powerful and easy to use.
- Used to identify complex network issues.
- Easy and quick to install.
- Widley used by security teams to analyze network traffic.
- Compatible with various OS such as: Linux, macOS, BSD, Solaris, and Windows.
- Plugins and scripts can be leveraged to customize Wireshark.
Download and learn how to use Wireshark here.
Nmap

Nmap stands for Network Mapper and is an open source command line (CLI) tool used to scan IP addresses and ports in your network. With a quick Nmap search, you can find open ports, detect what services are running, find vulnerabilities, and more.
Why we like Nmap:
- Beginner friendly; even simple commands can return valuable information.
- If you don’t feel comfortable with the CLI, Nmap has a GUI called Zenmap.
- Can quickly map out entire networks.
- Provides detailed information regarding OS and versions.
- Scrips found in the Nmap Scripting Engine can be used for penetration testing.
You can download this open source program via the Nmap website.
Snort
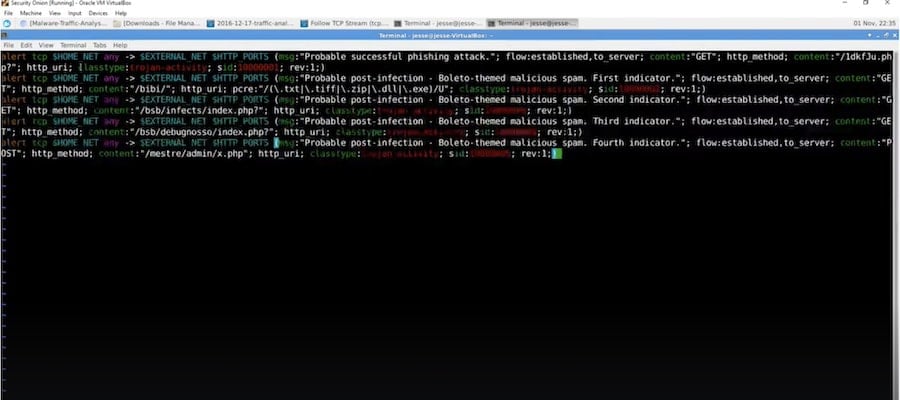
Snort functions as both an intrusion detection and intrusion prevention system (IDS/IPS). Snort can also be used as a packet sniffer and logger. By using rules offered by Snort as well as custom rules, Snort can use anomaly, protocol, and signature inspection methods to identify potentially malicious activity on your network.
Why we like Snort:
- Unique rules can be created to identify potentially harmful traffic.
- Complex rules can be created in the free version. However, you can upgrade to the paid version should you wish to create even more precise rules.
- Is available on all operating systems.
- Its rule language is flexible and easy to learn.
- Versatile capabilities that enable users to log, sniff packets, and use Snort as an IDS or IPS.
Learn how to download and learn the basics of this program via the Snort website.
Incident Response and Forensics Tools
These are our favorite open source incident response and forensics tools.
EnCase
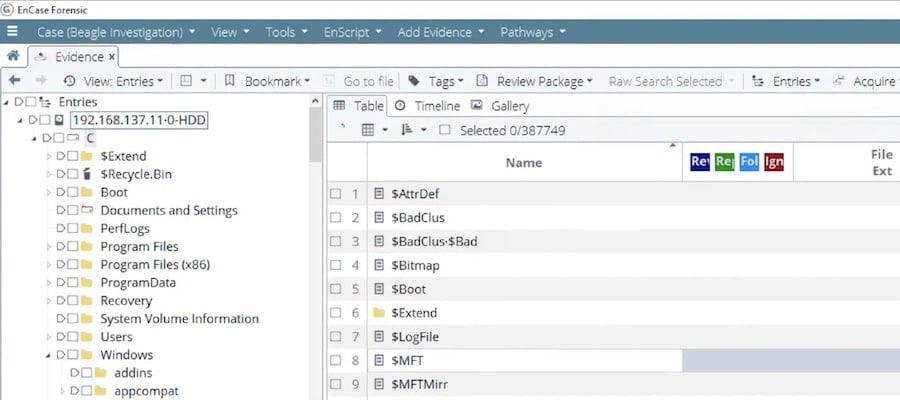
EnCase is a digital forensics case management software that walks users through the digital forensics process with built-in pathways and workflow templates. Workflow templates ensure that every step of the forensics process is being adhered to.
Why we like EnCase:
- Provides a written process of steps, making it beginner-friendly.
- GUI interface that runs on Windows.
- Can be used for both data acquisition and analysis.
- Reads bit-by-bit copies of hard drive and analyzes within slack space to retrieve deleted files.
- Automatically creates an easy-to-read timeline of all crucial events.
Learn more and download EnCase at Opentext.
CompTIA Voucher Hub
Planning your next CompTIA exam? Save up to 30% with our CompTIA Voucher Hub — official partner discounts for all CompTIA certifications, including Security+, Network+, A+, and more.
OSForensics

OSForensics is a comprehensive digital forensics tool enabling cyber security professionals to find valuable forensics data to solve crimes or understand how criminals hacked into a system. OSForensics offers free, paid, and perpetual license versions.
Why we like OSForensics:
- Arguably the most popular digital forensics tool on the market.
- Enables forensics teams to recover data from RAM.
- Can recover passwords, emails, and files that users attempted to delete.
- Creates a detailed picture of what was happening on the computer by examining recently accessed websites, interactions with USB drives, recent downloads, website logins, and more.
- Easily generates reports and images of computer systems to analyze at a later time.
- Offers a variety of powerful and free tools such as OSFMount, OSFClone, Volatility Workbench, and ImageUSB.
You can download and learn more about OSForensics at PassMark.
MISP (Malware Information Sharing Platform & Threat Sharing)
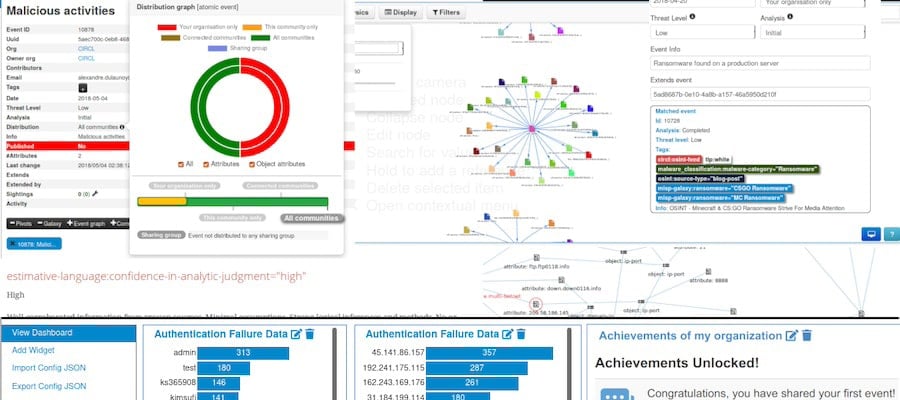
MISP is used for collecting and sharing indicators of compromise. MISP is helpful for quickly identifying threats and responding to incidents. It’s a vital tool when creating a threat intelligence strategy.
Why we like MISP:
- Allows organizations to share threat intelligence information through a standard format quickly.
- Intuitive end-user interface.
- Adjustable taxonomy is used to classify and tag events.
- STIX supported, using a standardized way to send, format, and secure data.
- Real time alerts about the latest threats and vulnerabilities.
MISP is available to download for free on its website.
Security Information and Event Management
Security information and event management systems, or SIEMs, are crucial for logging events and understanding what’s happening within your network.
AlienVault OSSIM
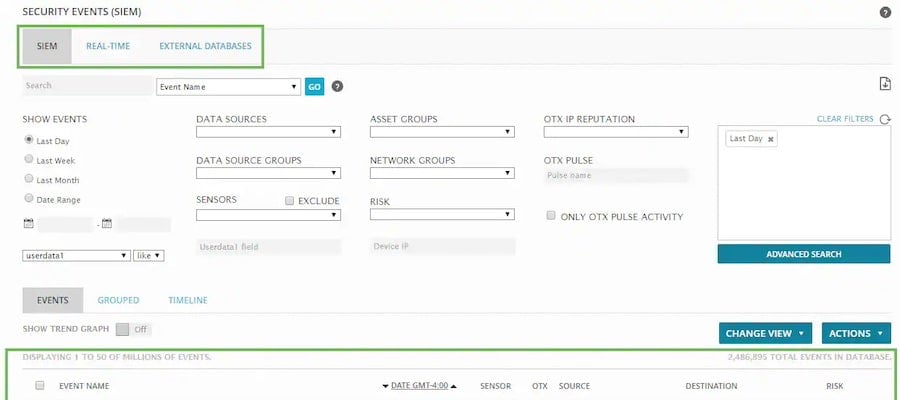
Purchased in 2019 by AT&T, AlienVault OSSIM is an open-source SIEM with a wealth of features. AlienValut OSSIM was originally created by developers after noting the lack of availability of high-quality open source SIEMs. AlienVault OSSIM interacts with other AT&T products to provide real-time information about malicious machines.
Why we like AlienVault OSSIM:
- Can easily integrate with a variety of other open source tools.
- Automated asset discovery to easily identity devices on the network.
- Can create events based on anomalous behavior.
- Doubles as a vulnerability assessment tool by scanning the network and creating reports.
- AlienVault can be configured to work as an IDS or HIDS
AilenVault OSSIM can be found on AT&T’s website.
ELK Stack
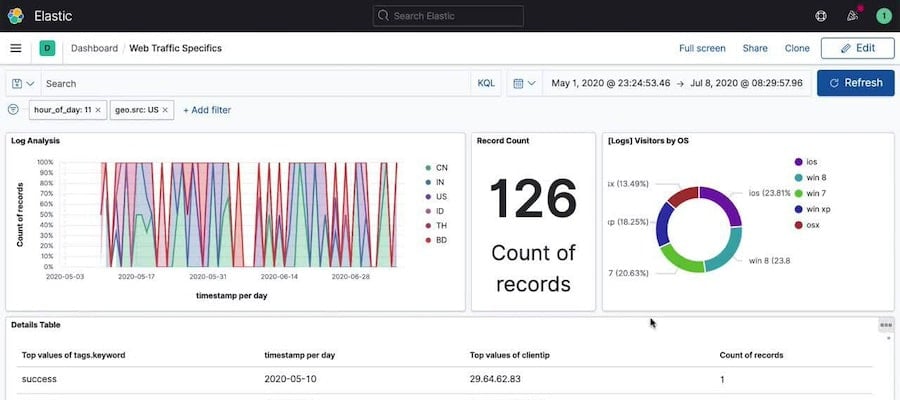
ELK Stack combines three tools: Elasticsearch, Logstash, and Kibana. Combined, these features make up ELK Stack, an agile and powerful open source SIEM. Elasticsearch functions as a SIEM search engine, Logstash is a server-side data processor, and Kibana is the GUI used to interact with the SIEM and visualize findings.
Why we like ELK Stack:
- Automatic scaling that grows with your usage.
- Easy to take snapshots of entire clusters or individual nodes.
- Various CLI tools that allow you to customize and easily configure SIEM security.
- Built-in integrations that allow alerts to be sent to a variety of third party systems.
- Allows for full and multi-stack monitoring.
Download and learn more about ELK Stack here.
SIEMonster

SIEMonster is a highly customizable FOSS SIEM that has a range of capabilities, such as machine learning, virtualization, and human-based behavior correlation. Third-party tools can also be seamlessly integrated to address cyber security needs.
Why we like SIEMonster:
- Designed for massive projects, offering users an ingestion rate of 2 million events per second.
- Apache NiFi is built in, allowing for easy scaling and performance maintenance.
- Easy to use unified dashboard that makes all events easy to understand.
- Machine learning cyber security software tool allowing for cyber threats to be identified efficiently.
- Used in the enterprise security monitoring setup of major companies such as UMass, RMIT, and BlueScope.
SIEMonster is available to download for free on its website.
Identity and Access Management (IAM) Tools
Open source Identify and Access Management (IAM) tools authenticate and authorize the access of users trying to log into company devices.
FreeIPA
FreeIPA is an identity and authentication software built for the Linux/UNIX environment. FreeIPA offers centralized authentication, authorization, account information, and other security capabilities pertaining to IAM.
Why we like FreeIPA:
- Built on top of reputable open source products.
- SSO is offered via the MIT Kerberos feature.
- Offers a GUI as well as a CLI
- Concentrated authentication, authorization, and account information capabilities.
FreeIPA is available to download for free on its website.
OpenIAM
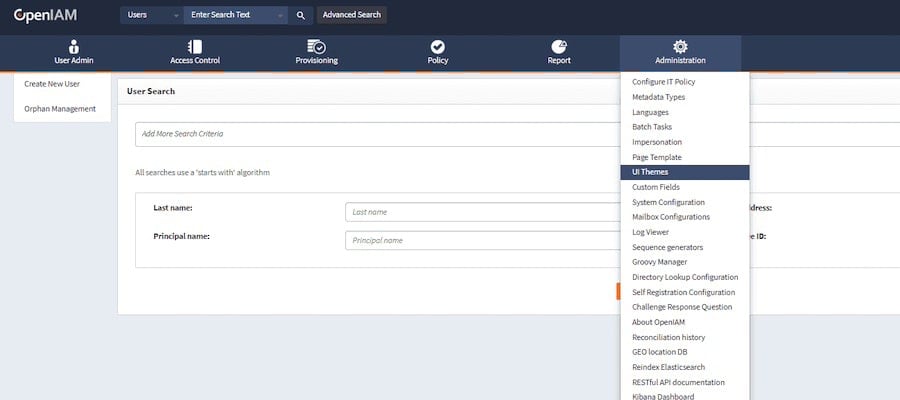
OpenIAM is an identity and access management platform providing users with a range of capabilities. OpenIAM allows cyber security analysts to obtain a unified understanding of who has access to certain information and tools.
Why we like OpenIAM:
- Offers flexible RBAC permissions.
- Enables single sign-on, simplifying access for users.
- Provides user authentication via MFA, adaptive authentication, and social login.
- Provides users with a self service portal allowing them to manage their own profiles and passwords.
- Workflow engine that automates business processes pertaining to identify management.
Access OpenIAm here.
The Complete Cyber Security Course Bundle
Build a rock-solid cyber security foundation with The Complete Cyber Security Course Bundle — four bestselling courses covering network security, anonymity, privacy, and advanced defense techniques.
Keycloak
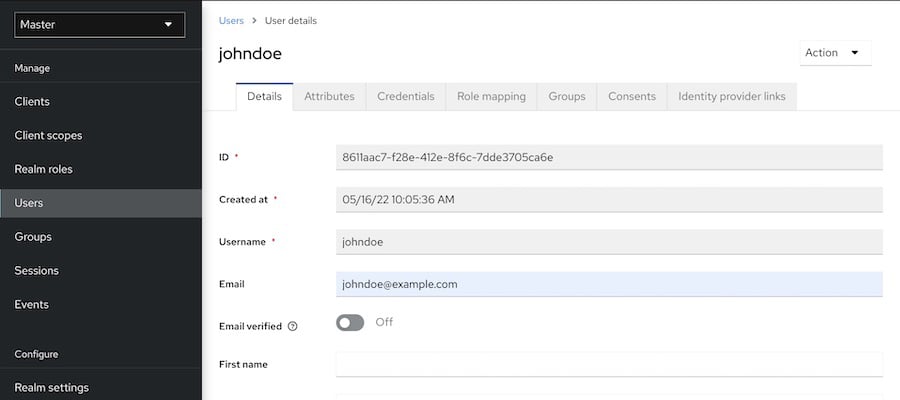
Keycloak is a beloved IAM tool because of its ability to easily integrate into your IT ecosystem. It also comes with a comprehensive list of features like SSO and user management. As a widely used IAM, its community is always creating helpful documentation and building out the product.
Why we like Keycloak:
- Single sign-on authentication via Keycloak.
- Users can also sign on via social network accounts.
- Built-in user federation connecting to LDAP and Active Directory servers.
- Easy to use admin and account management consoles.
- Offers role-based authentication in addition to more granular and customized forms of authorization.
Keycloak is available to download for free on here.
Encryption and Cryptography Tools
Use one of these FOSS cyber security tools to ensure your data is encrypted and secured.
GnuPG (GPG)

GnuPG is an open source software allowing users to encrypt data and create and sign certificates. It offers a flexible key management system and access modules for various public key directories.
Why we like GnuPG:
- Secure files and communication with encryption and decryption capabilities.
- Verifies and authenticates the integrity of data with digital signatures.
- Is capable of creating and managing cryptographic keys.
- Widely used among email clients.
- Compatible with PGP software.
GnuPG is available to download for free on its website.
OpenSSL
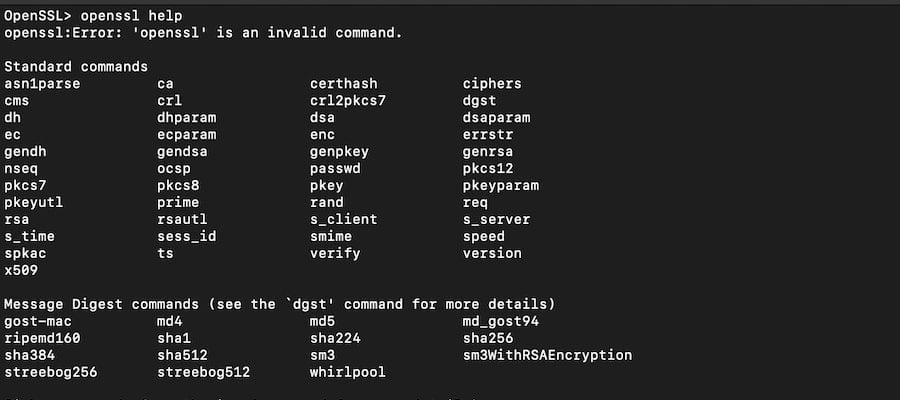
OpenSSL is an open source command line tool that is used to generate private keys, create CSRs, install SSL/TLS certificates, and identify certificate information.
Why we like OpenSSL:
- Easy to use CLI.
- Can choose from a variety of key algorithms and key sizes.
- It’s a simple program but has powerful capabilities.
- Widely used and battle-tested.
- Comes preinstalled in MacOS as well as certain versions of Linux.
OpenSSL is available to download for free on its website.
Endpoint Protection Tools
Secure individual systems with the help of these free endpoint protection tools.
ClamAV

ClamAV is a free antivirus engine that detects trojans, viruses, malware, and other nefarious threats. It works across platforms and primarily uses signatures to detect malware.
Why we like ClamAV:
- CLI that scans file systems and filters emails.
- Is used by Internet gateways and mail servers.
- Offers real-time protection on Linux OS.
- Cross-platform support for Windows, Linux, and macOS.
- The signature database is updated multiple times a day with newly discovered signatures.
- Integrates with version control systems like Git to manage changes and share analysis.
ClamAV is available to download for free on its website.
OSSEC
OSSEC is an open source endpoint protection tool that can be tailored to your security needs. It offers extensive configuration, allows for custom alert rules, and the ability to write scripts that address security alerts.
Why we like OSSEC:
- Works across multiple platforms, including macOS, Windows, Linux, and Solaris.
- Helps organizations comply with NIST and PCI DSS regulations.
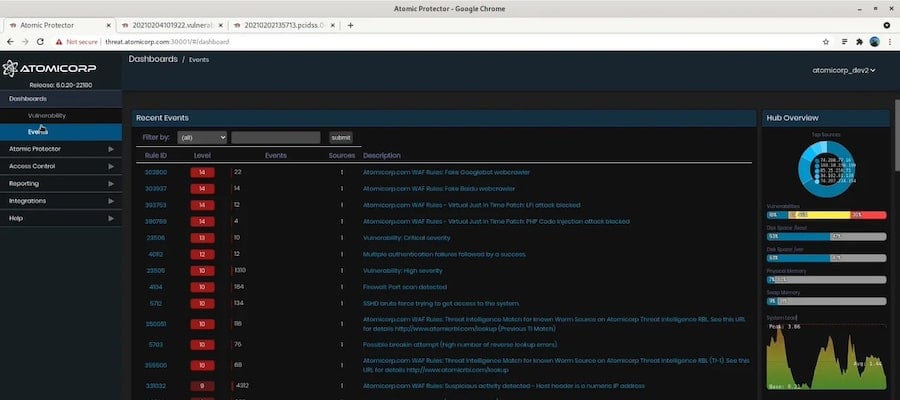
- You can upgrade to Atomic OSSEC, which provides users with access to thousands more rules, among other features.
- Easy to scale, making it optimal for growing businesses.
- Has log analysis, file integrity monitoring, and rootkit detention.
OSSEC is available to download for free on here.
Wazuh
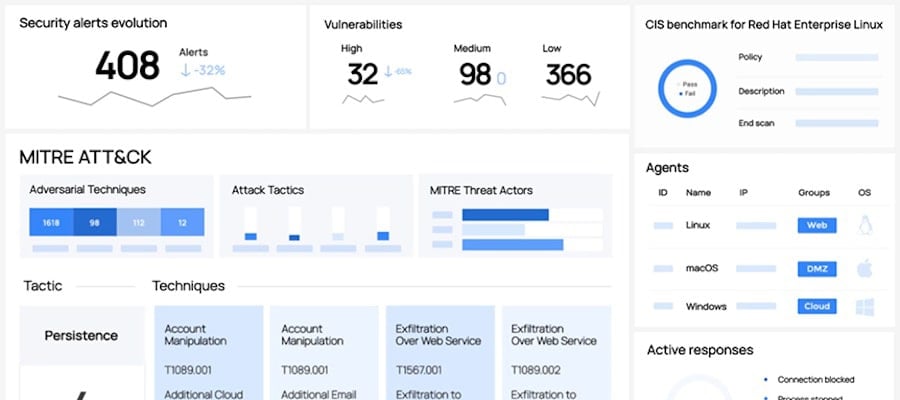
Wazuh marries its XDR and SIEM capabilities to create a robust endpoint security program. Wazuh automatically collects a wealth of data and responds to malicious activity like an IPS would.
Why we like Wazuh:
- Can be used to collect data and respond in real-time.
- Its database is constantly updated with the latest CVEs to identify the latest attack signatures.
- System and application configuration monitoring to ensure you’re up to date with the latest security policies and standards.
- Comes with out-of-the-box IPS protection.
- It is optimized to protect your cloud environment.
- It can be used to harden Docker security.
Wazuh is available to download for free on its website.
Conclusion
These are 20 of the most used open source cyber security tools on the market. As they are open source and free, we encourage you to download them and get your hands dirty.
Learning some of the aforementioned tools would be a great way to protect your system and become more appealing to potential employers. Whether you’re learning about penetration testing, network security monitoring, network traffic analysis, digital forensics, or SIEMs, learning as much as possible will serve to make you a better cyber security professional.
If you want to start learning how to use these free and open source cyber security tools become a StationX Member. You’ll receive access to over 30,000 courses and labs and join a community of cyber security professionals and enthusiasts.
You can also see our Information Security Training Bundles, granting lifetime access to top courses for a one-time purchase. Learn ethical hacking, cyber security, and prepare for top certifications.
We have bundles on:
- Pentesting, red teaming, and web app hacking
- Certification prep, including CompTIA, ISC2, AWS, Cisco, and Azure
- DevSecOps and Coding
- Linux
- AI
- And much more!




