The one downside to a tool as robust and powerful as Nmap is remembering so many commands. Even many seasoned industry professionals fail to make the most of Nmap simply because keeping track of all its flags can prove such a challenge.
We have compiled and organized this Nmap cheat sheet to help you master what is arguably the most useful tool in any penetration tester’s arsenal. Whether you use it to memorize Nmap’s options, as a quick reference to keep nearby, or as a study sheet for your CEH/Pentest+ exam, we’re certain it will help you become a Nmap pro.
Download your own copy of this cheat sheet here. Now, let’s get to the Nmap commands.
Nmap Cheat Sheet Search
Search our Nmap cheat sheet to find the right cheat for the term you're looking for. Simply enter the term in the search bar and you'll receive the matching cheats available.
- Nmap Cheat Sheet Search
- Quick Start
- Target Specification
- Nmap Scan Techniques
- Host Discovery
- Nmap Command Generator
- Port Specification
- Service and Version Detection
- OS Detection
- Timing and Performance
- Timing and Performance Switches
- NSE Scripts
- Useful NSE Script Examples
- Firewall / IDS Evasion and Spoofing
- Output
- Helpful Nmap Output examples
- Miscellaneous Nmap Flags
- Other Useful Nmap Commands
- When to Use Which Scan Type
- Reading Nmap Output
- Conclusion
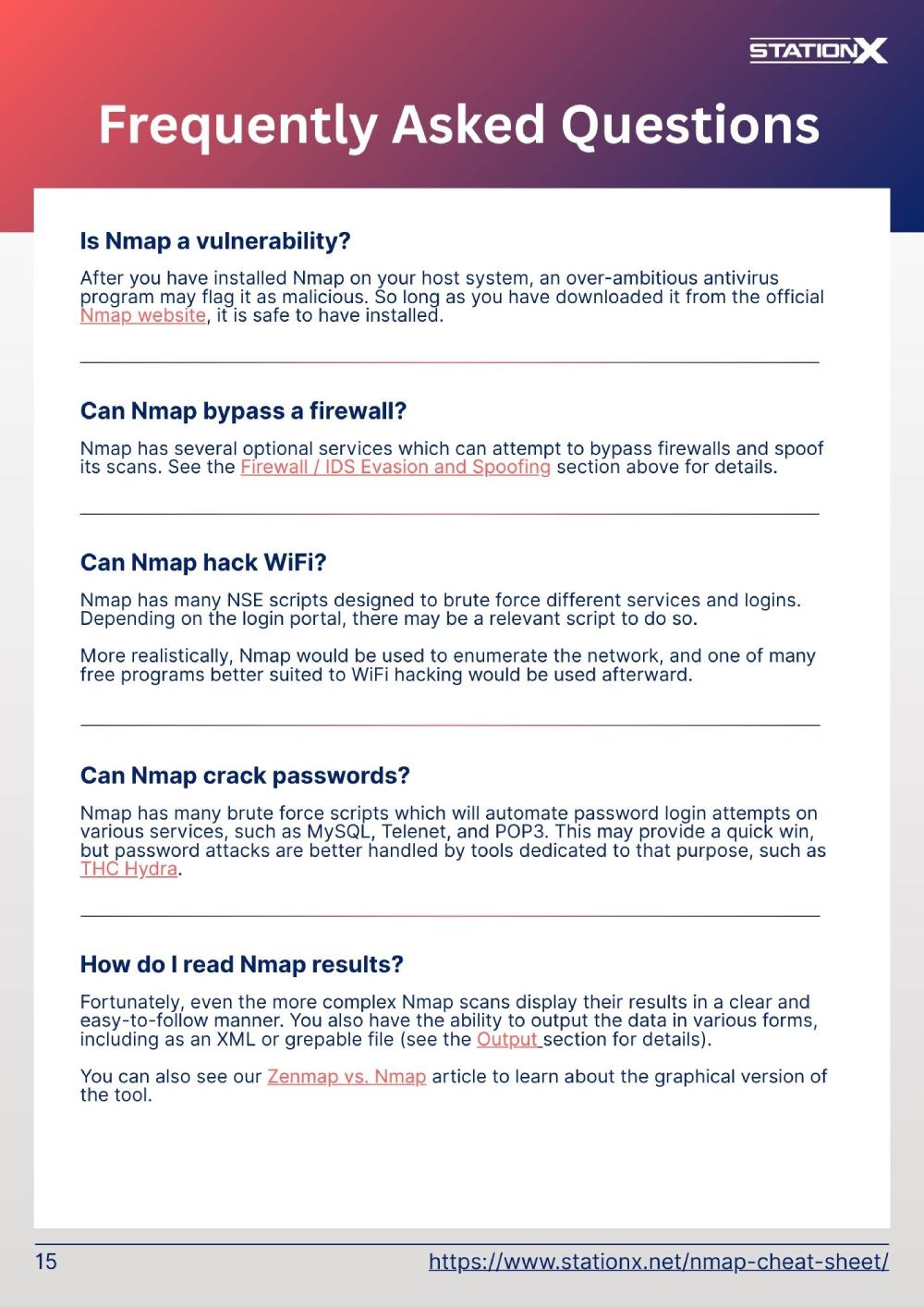
- Frequently Asked Questions
Quick Start
New to Nmap? Start with these three commands to get comfortable with the basics.
| Switch | Example | Description |
| -sn | nmap -sn 192.168.1.0/24 | Discover what's alive on your network |
| -F | nmap -F 192.168.1.10 | Scan the most common 100 ports on a single target |
| -sV -sC | nmap -sV -sC 192.168.1.10 | Runs service detection (-sV) and default scripts (-sC) to identify what's actually running on open ports |
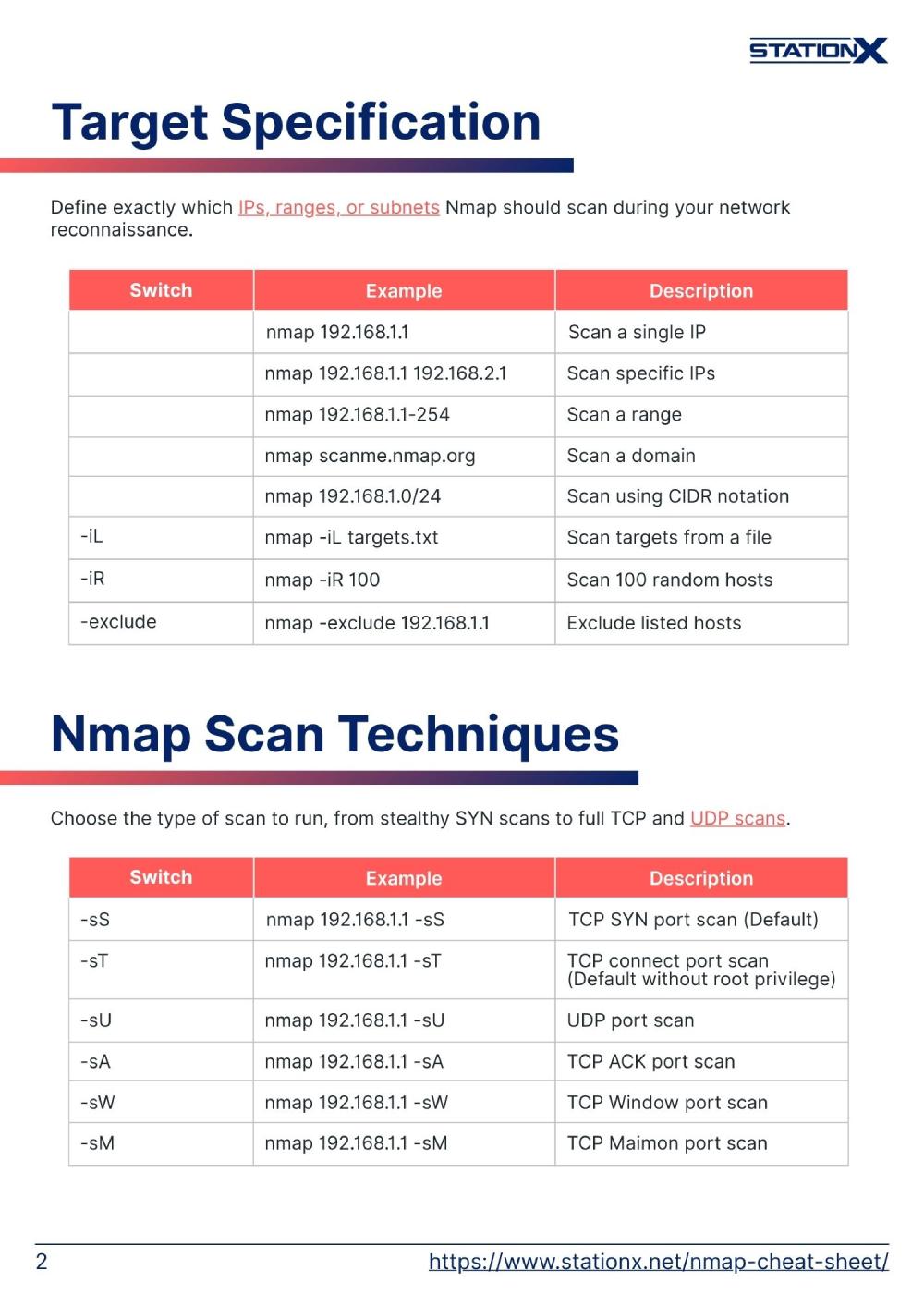
Target Specification
Define exactly which IPs, ranges, or subnets Nmap should scan during your network reconnaissance.
| SWITCH | EXAMPLE | DESCRIPTION |
| nmap 192.168.1.1 | Scan a single IP | |
| nmap 192.168.1.1 192.168.2.1 | Scan specific IPs | |
| nmap 192.168.1.1-254 | Scan a range | |
| nmap scanme.nmap.org | Scan a domain | |
| nmap 192.168.1.0/24 | Scan using CIDR notation | |
| -iL | nmap -iL targets.txt | Scan targets from a file |
| -iR | nmap -iR 100 | Scan 100 random hosts |
| -exclude | nmap -exclude 192.168.1.1 | Exclude listed hosts |
Nmap Scan Techniques
Choose the type of scan to run, from stealthy SYN scans to full TCP and UDP scans.
| SWITCH | EXAMPLE | DESCRIPTION |
| -sS | nmap 192.168.1.1 -sS | TCP SYN port scan (Default) |
| -sT | nmap 192.168.1.1 -sT | TCP connect port scan (Default without root privilege) |
| -sU | nmap 192.168.1.1 -sU | UDP port scan |
| -sA | nmap 192.168.1.1 -sA | TCP ACK port scan |
| -sW | nmap 192.168.1.1 -sW | TCP Window port scan |
| -sM | nmap 192.168.1.1 -sM | TCP Maimon port scan |
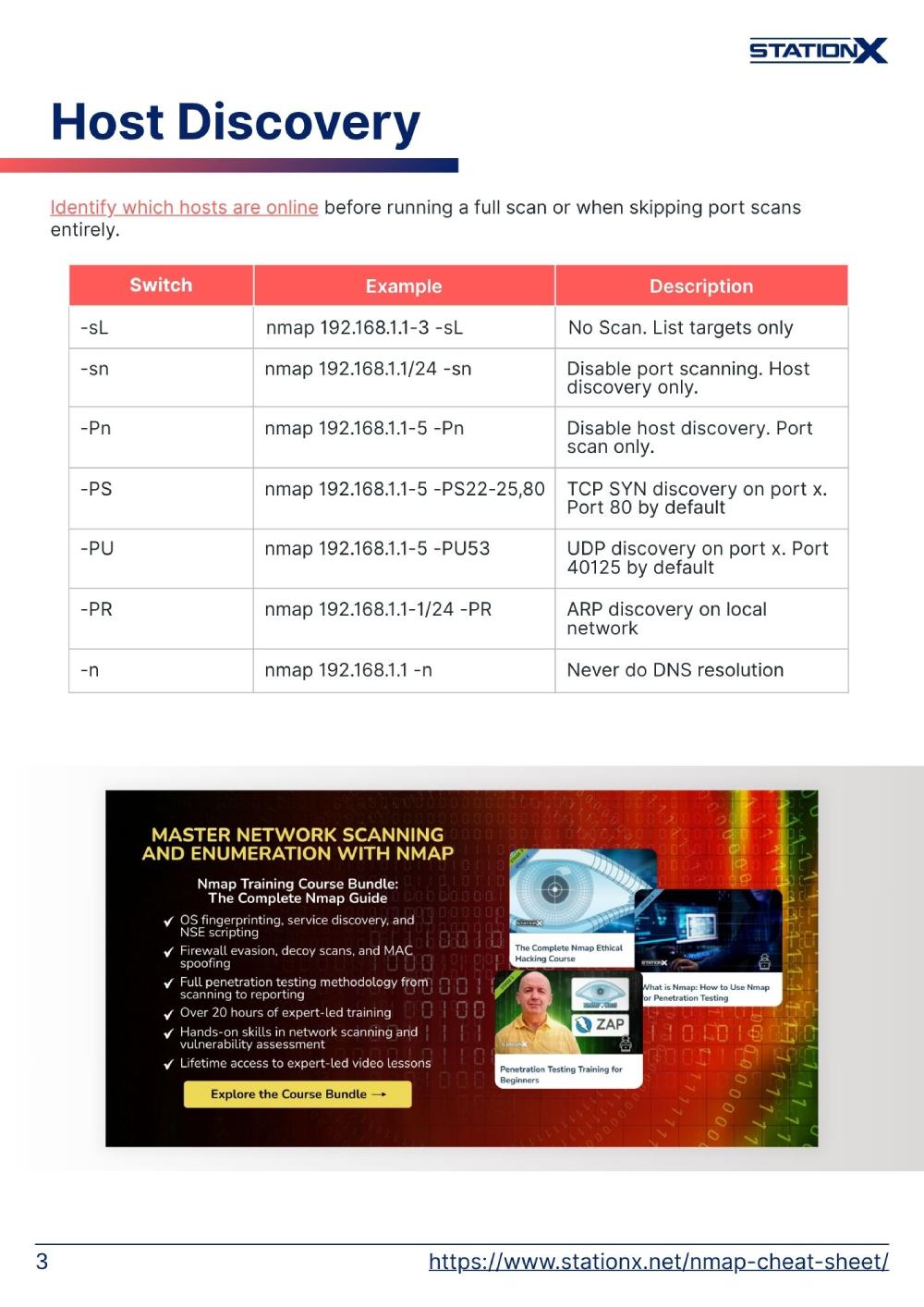
Host Discovery
Identify which hosts are online before running a full scan or when skipping port scans entirely.
| SWITCH | EXAMPLE | DESCRIPTION |
| -sL | nmap 192.168.1.1-3 -sL | No Scan. List targets only |
| -sn | nmap 192.168.1.1/24 -sn | Disable port scanning. Host discovery only. |
| -Pn | nmap 192.168.1.1-5 -Pn | Disable host discovery. Port scan only. |
| -PS | nmap 192.168.1.1-5 -PS22-25,80 | TCP SYN discovery on port x. Port 80 by default |
| -PA | nmap 192.168.1.1-5 -PA22-25,80 | TCP ACK discovery on port x. Port 80 by default |
| -PU | nmap 192.168.1.1-5 -PU53 | UDP discovery on port x. Port 40125 by default |
| -PR | nmap 192.168.1.1-1/24 -PR | ARP discovery on local network |
| -n | nmap 192.168.1.1 -n | Never do DNS resolution |
Nmap Command Generator
Say goodbye to the hassle of trying to remember the exact syntax for your Nmap commands! With our Nmap Command Generator, you can simply say what you need Nmap to do and we will generate the command for you.
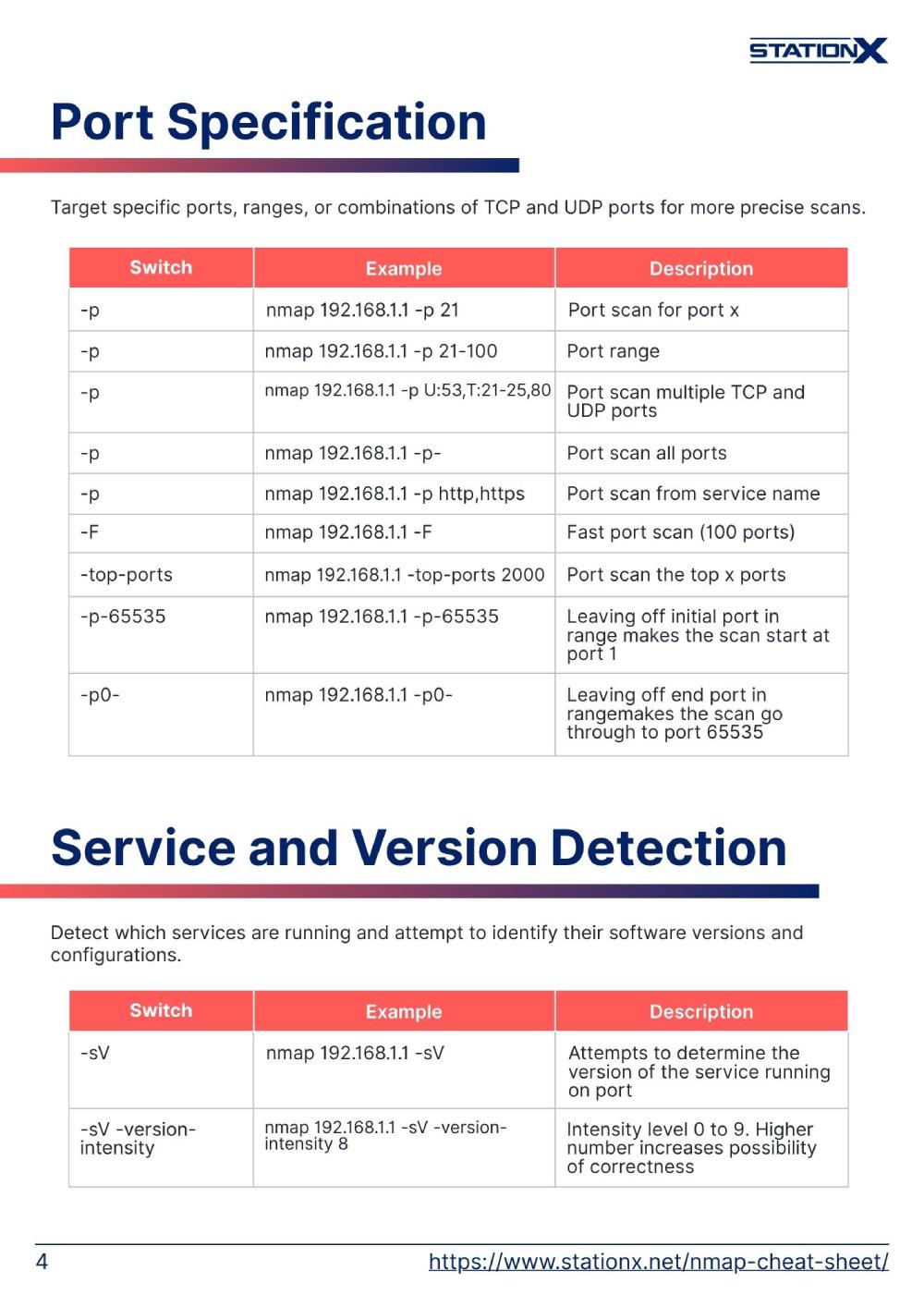
Port Specification
Target specific ports, ranges, or combinations of TCP and UDP ports for more precise scans.
| SWITCH | EXAMPLE | DESCRIPTION |
| -p | nmap 192.168.1.1 -p 21 | Port scan for port x |
| -p | nmap 192.168.1.1 -p 21-100 | Port range |
| -p | nmap 192.168.1.1 -p U:53,T:21-25,80 | Port scan multiple TCP and UDP ports |
| -p | nmap 192.168.1.1 -p- | Port scan all ports |
| -p | nmap 192.168.1.1 -p http,https | Port scan from service name |
| -F | nmap 192.168.1.1 -F | Fast port scan (100 ports) |
| -top-ports | nmap 192.168.1.1 -top-ports 2000 | Port scan the top x ports |
| -p-65535 | nmap 192.168.1.1 -p-65535 | Leaving off initial port in range makes the scan start at port 1 |
| -p0- | nmap 192.168.1.1 -p0- | Leaving off end port in range makes the scan go through to port 65535 |
Service and Version Detection
Detect which services are running and attempt to identify their software versions and configurations.
| SWITCH | EXAMPLE | DESCRIPTION |
| -sV | nmap 192.168.1.1 -sV | Attempts to determine the version of the service running on port |
| -sV -version-intensity | nmap 192.168.1.1 -sV -version-intensity 8 | Intensity level 0 to 9. Higher number increases possibility of correctness |
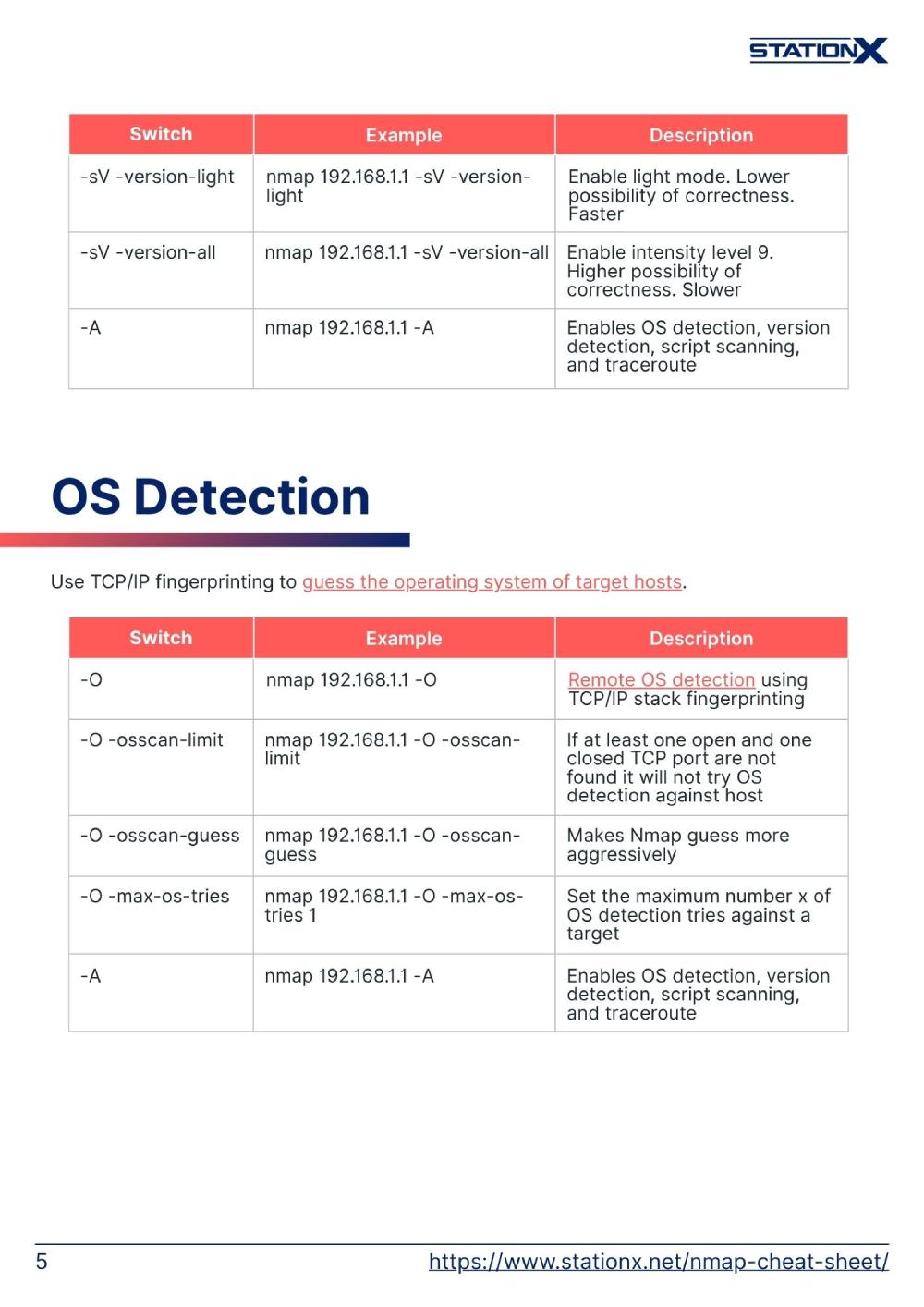
| -sV -version-light | nmap 192.168.1.1 -sV -version-light | Enable light mode. Lower possibility of correctness. Faster |
| -sV -version-all | nmap 192.168.1.1 -sV -version-all | Enable intensity level 9. Higher possibility of correctness. Slower |
| -A | nmap 192.168.1.1 -A | Enables OS detection, version detection, script scanning, and traceroute |
OS Detection
Use TCP/IP fingerprinting to guess the operating system of target hosts.
| SWITCH | EXAMPLE | DESCRIPTION |
| -O | nmap 192.168.1.1 -O | Remote OS detection using TCP/IP stack fingerprinting |
| -O -osscan-limit | nmap 192.168.1.1 -O -osscan-limit | If at least one open and one closed TCP port are not found it will not try OS detection against host |
| -O -osscan-guess | nmap 192.168.1.1 -O -osscan-guess | Makes Nmap guess more aggressively |
| -O -max-os-tries | nmap 192.168.1.1 -O -max-os-tries 1 | Set the maximum number x of OS detection tries against a target |
| -A | nmap 192.168.1.1 -A | Enables OS detection, version detection, script scanning, and traceroute |
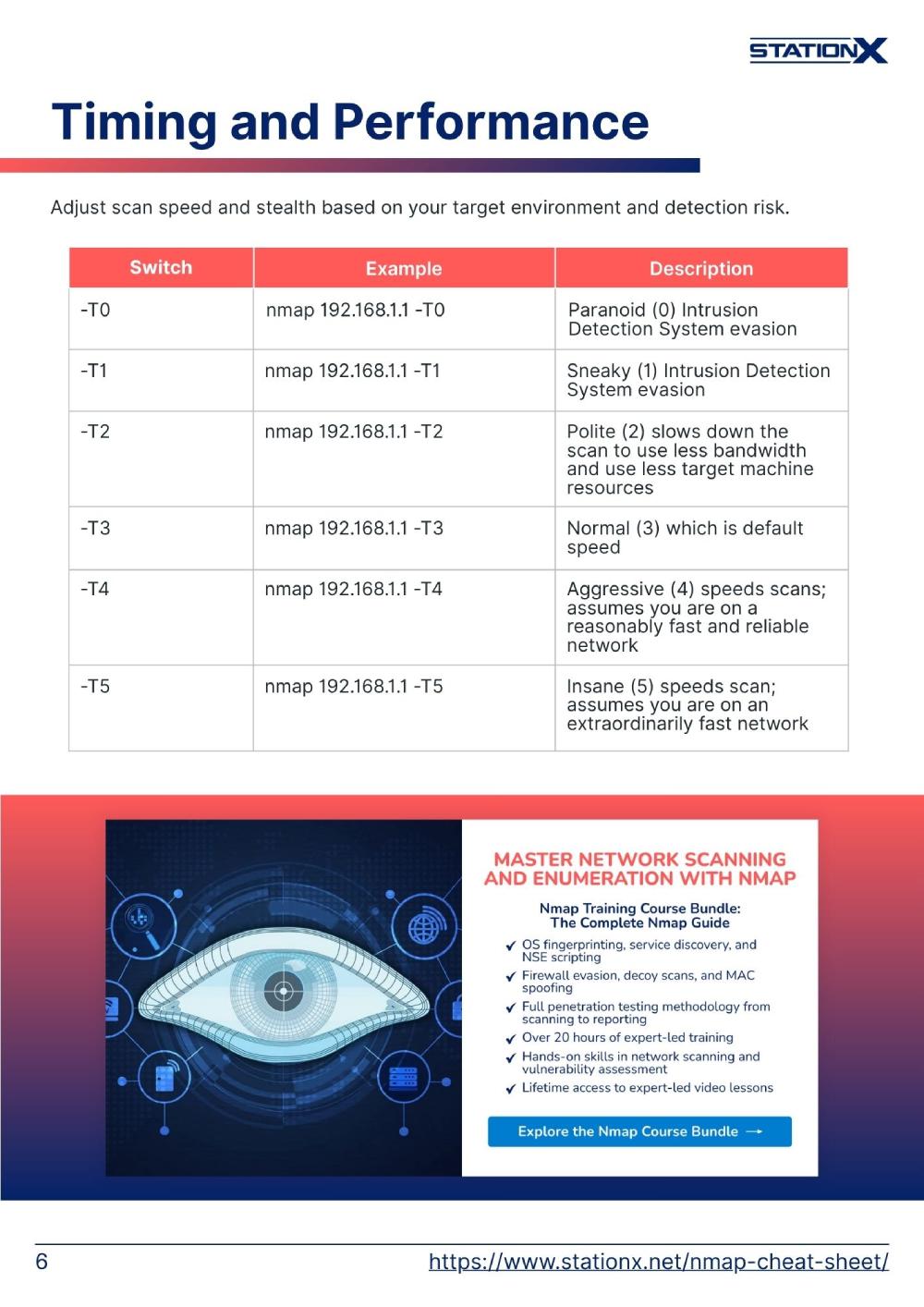
Timing and Performance
Adjust scan speed and stealth based on your target environment and detection risk.
| SWITCH | EXAMPLE | DESCRIPTION |
| -T0 | nmap 192.168.1.1 -T0 | Paranoid (0) Intrusion Detection System evasion |
| -T1 | nmap 192.168.1.1 -T1 | Sneaky (1) Intrusion Detection System evasion |
| -T2 | nmap 192.168.1.1 -T2 | Polite (2) slows down the scan to use less bandwidth and use less target machine resources |
| -T3 | nmap 192.168.1.1 -T3 | Normal (3) which is default speed |
| -T4 | nmap 192.168.1.1 -T4 | Aggressive (4) speeds scans; assumes you are on a reasonably fast and reliable network |
| -T5 | nmap 192.168.1.1 -T5 | Insane (5) speeds scan; assumes you are on an extraordinarily fast network |
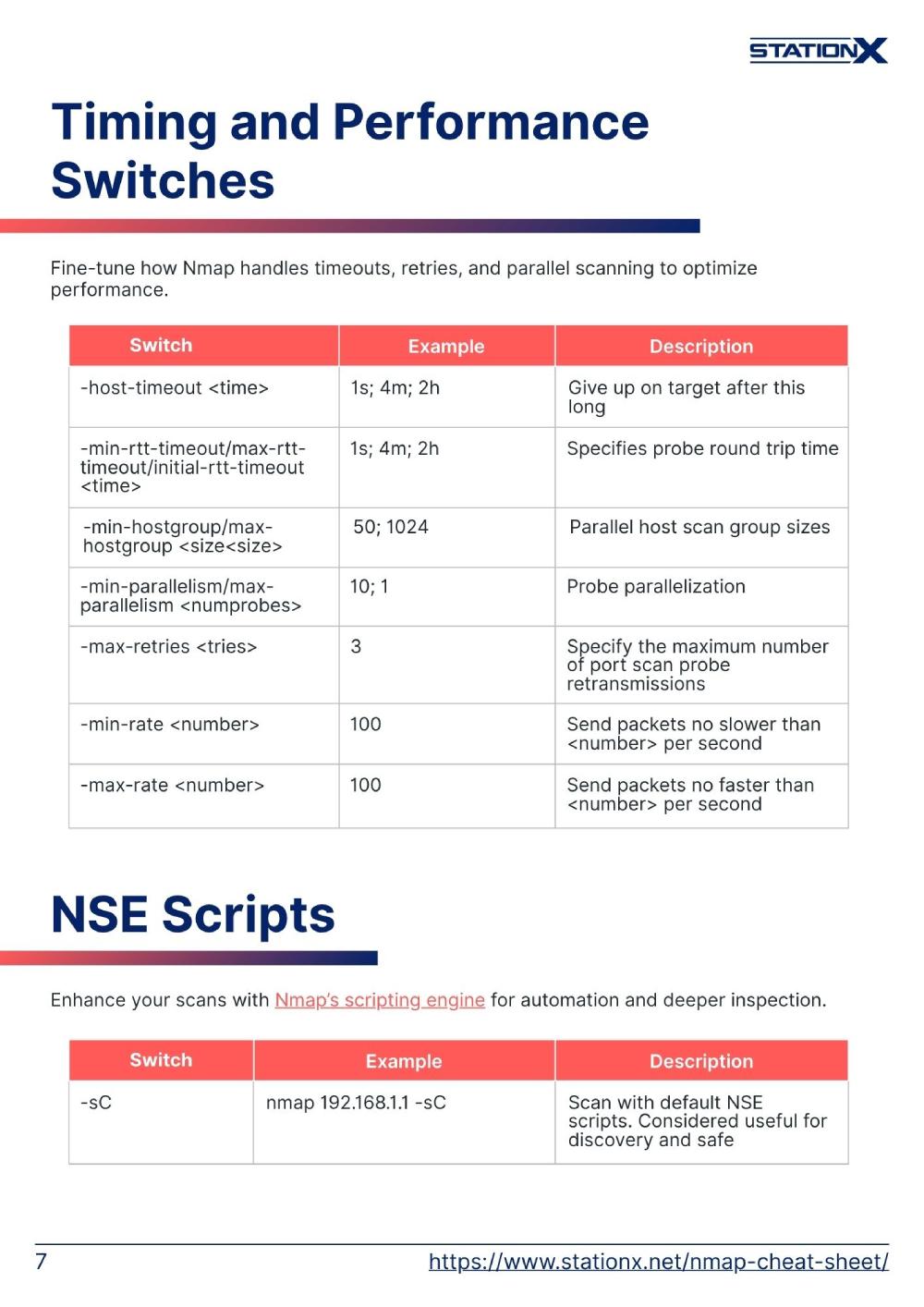
Timing and Performance Switches
Fine-tune how Nmap handles timeouts, retries, and parallel scanning to optimize performance.
| SWITCH | EXAMPLE INPUT | DESCRIPTION |
| -host-timeout <time> | 1s; 4m; 2h | Give up on target after this long |
| -min-rtt-timeout/max-rtt-timeout/initial-rtt-timeout <time> | 1s; 4m; 2h | Specifies probe round trip time |
| -min-hostgroup/max-hostgroup <size<size> | 50; 1024 | Parallel host scan group sizes |
| -min-parallelism/max-parallelism <numprobes> | 10; 1 | Probe parallelization |
| -max-retries <tries> | 3 | Specify the maximum number of port scan probe retransmissions |
| -min-rate <number> | 100 | Send packets no slower than <number> per second |
| -max-rate <number> | 100 | Send packets no faster than <number> per second |
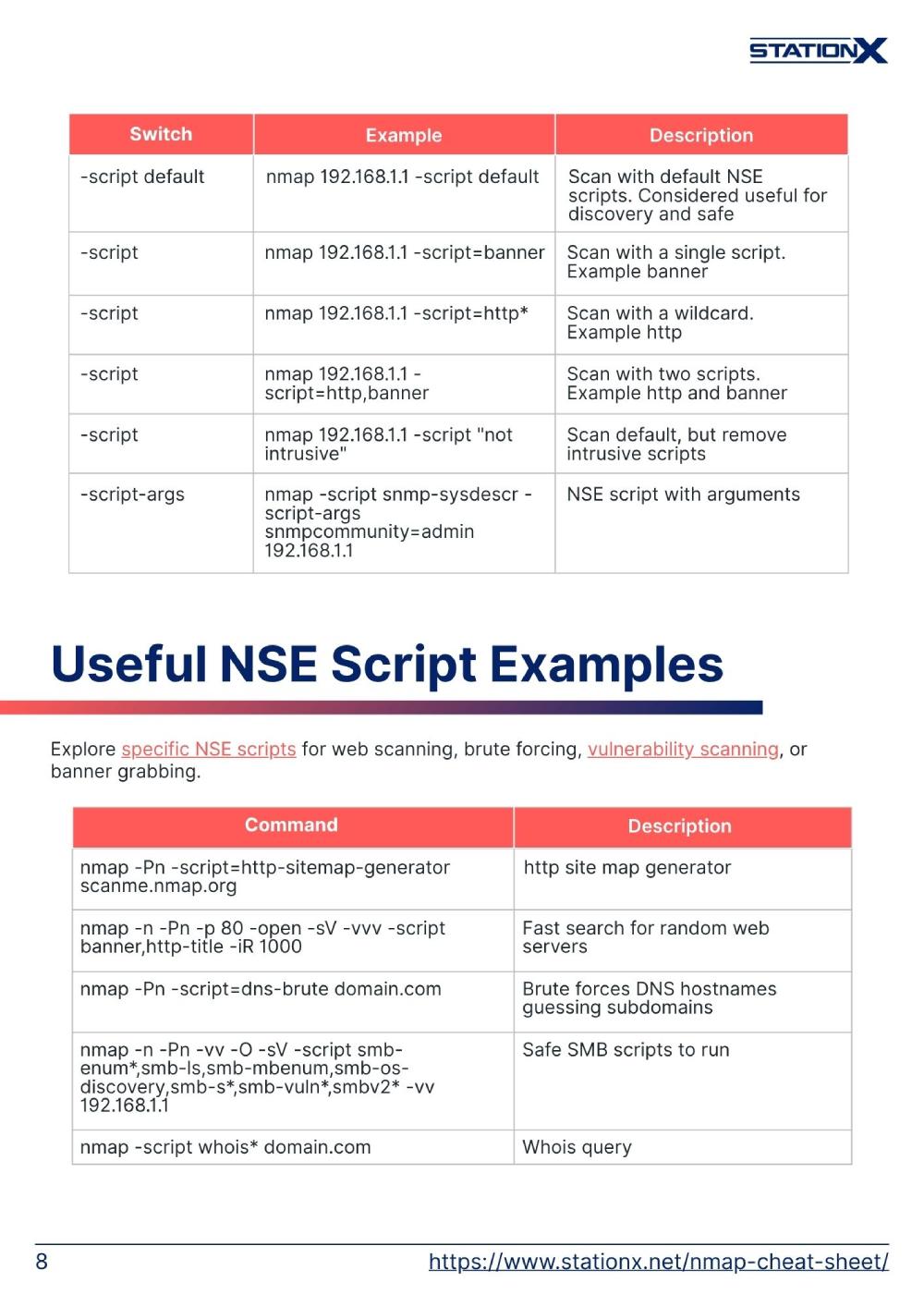
NSE Scripts
Enhance your scans with Nmap’s scripting engine for automation and deeper inspection.
| SWITCH | EXAMPLE | DESCRIPTION |
| -sC | nmap 192.168.1.1 -sC | Scan with default NSE scripts. Considered useful for discovery and safe |
| -script default | nmap 192.168.1.1 -script default | Scan with default NSE scripts. Considered useful for discovery and safe |
| -script | nmap 192.168.1.1 -script=banner | Scan with a single script. Example banner |
| -script | nmap 192.168.1.1 -script=http* | Scan with a wildcard. Example http |
| -script | nmap 192.168.1.1 -script=http,banner | Scan with two scripts. Example http and banner |
| -script | nmap 192.168.1.1 -script "not intrusive" | Scan default, but remove intrusive scripts |
| -script-args | nmap -script snmp-sysdescr -script-args snmpcommunity=admin 192.168.1.1 | NSE script with arguments |
Useful NSE Script Examples
Explore specific NSE scripts for web scanning, brute forcing, vulnerability scanning, or banner grabbing.
| COMMAND | DESCRIPTION |
| nmap -Pn -script=http-sitemap-generator scanme.nmap.org | http site map generator |
| nmap -n -Pn -p 80 -open -sV -vvv -script banner,http-title -iR 1000 | Fast search for random web servers |
| nmap -Pn -script=dns-brute domain.com | Brute forces DNS hostnames guessing subdomains |
| nmap -n -Pn -vv -O -sV -script smb-enum*,smb-ls,smb-mbenum,smb-os-discovery,smb-s*,smb-vuln*,smbv2* -vv 192.168.1.1 | Safe SMB scripts to run |
| nmap -script whois* domain.com | Whois query |
| nmap -p80 -script http-unsafe-output-escaping scanme.nmap.org | Detect cross site scripting vulnerabilities |
| nmap -p80 -script http-sql-injection scanme.nmap.org | Check for SQL injections |
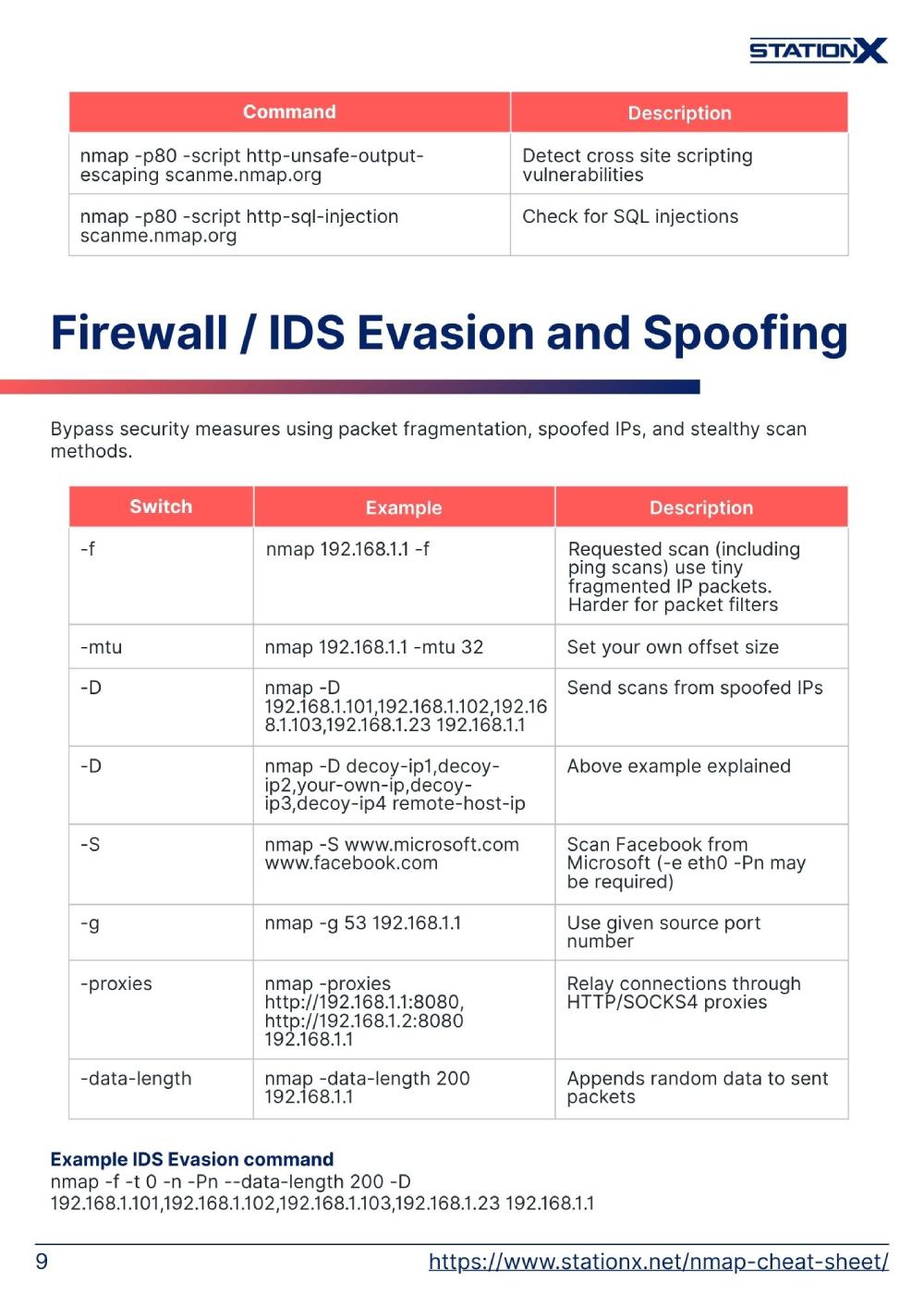
Firewall / IDS Evasion and Spoofing
Bypass security measures using packet fragmentation, spoofed IPs, and stealthy scan methods.
| SWITCH | EXAMPLE | DESCRIPTION |
| -f | nmap 192.168.1.1 -f | Requested scan (including ping scans) use tiny fragmented IP packets. Harder for packet filters |
| -mtu | nmap 192.168.1.1 -mtu 32 | Set your own offset size |
| -D | nmap -D 192.168.1.101,192.168.1.102,192.168.1.103,192.168.1.23 192.168.1.1 | Send scans from spoofed IPs |
| -D | nmap -D decoy-ip1,decoy-ip2,your-own-ip,decoy-ip3,decoy-ip4 remote-host-ip | Above example explained |
| -S | nmap -S www.microsoft.com www.facebook.com | Scan Facebook from Microsoft (-e eth0 -Pn may be required) |
| -g | nmap -g 53 192.168.1.1 | Use given source port number |
| -proxies | nmap -proxies http://192.168.1.1:8080, http://192.168.1.2:8080 192.168.1.1 | Relay connections through HTTP/SOCKS4 proxies |
| -data-length | nmap -data-length 200 192.168.1.1 | Appends random data to sent packets |
Example IDS Evasion command
nmap -f -t 0 -n -Pn --data-length 200 -D
192.168.1.101,192.168.1.102,192.168.1.103,192.168.1.23 192.168.1.1
Information Security Courses Bundles
Want lifetime access to expert-led cyber security training? Explore our Information Security Course Bundles — one-time purchase packages covering top topics like Ethical Hacking, Cloud, Linux, DevSecOps, and CompTIA certifications.
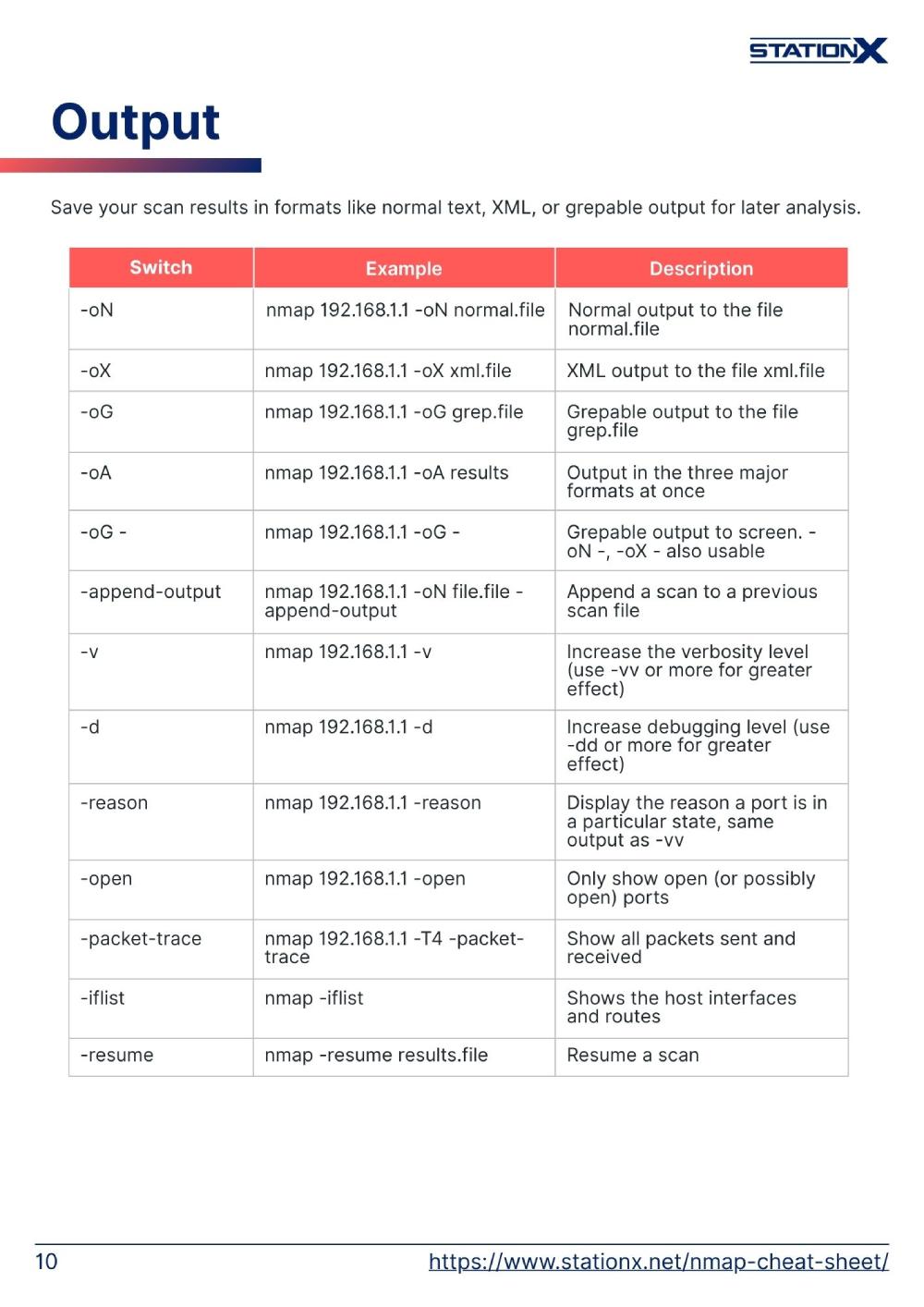
Output
Save your scan results in formats like normal text, XML, or grepable output for later analysis.
| SWITCH | EXAMPLE | DESCRIPTION |
| -oN | nmap 192.168.1.1 -oN normal.file | Normal output to the file normal.file |
| -oX | nmap 192.168.1.1 -oX xml.file | XML output to the file xml.file |
| -oG | nmap 192.168.1.1 -oG grep.file | Grepable output to the file grep.file |
| -oA | nmap 192.168.1.1 -oA results | Output in the three major formats at once |
| -oG - | nmap 192.168.1.1 -oG - | Grepable output to screen. -oN -, -oX - also usable |
| -append-output | nmap 192.168.1.1 -oN file.file -append-output | Append a scan to a previous scan file |
| -v | nmap 192.168.1.1 -v | Increase the verbosity level (use -vv or more for greater effect) |
| -d | nmap 192.168.1.1 -d | Increase debugging level (use -dd or more for greater effect) |
| -reason | nmap 192.168.1.1 -reason | Display the reason a port is in a particular state, same output as -vv |
| -open | nmap 192.168.1.1 -open | Only show open (or possibly open) ports |
| -packet-trace | nmap 192.168.1.1 -T4 -packet-trace | Show all packets sent and received |
| -iflist | nmap -iflist | Shows the host interfaces and routes |
| -resume | nmap -resume results.file | Resume a scan |
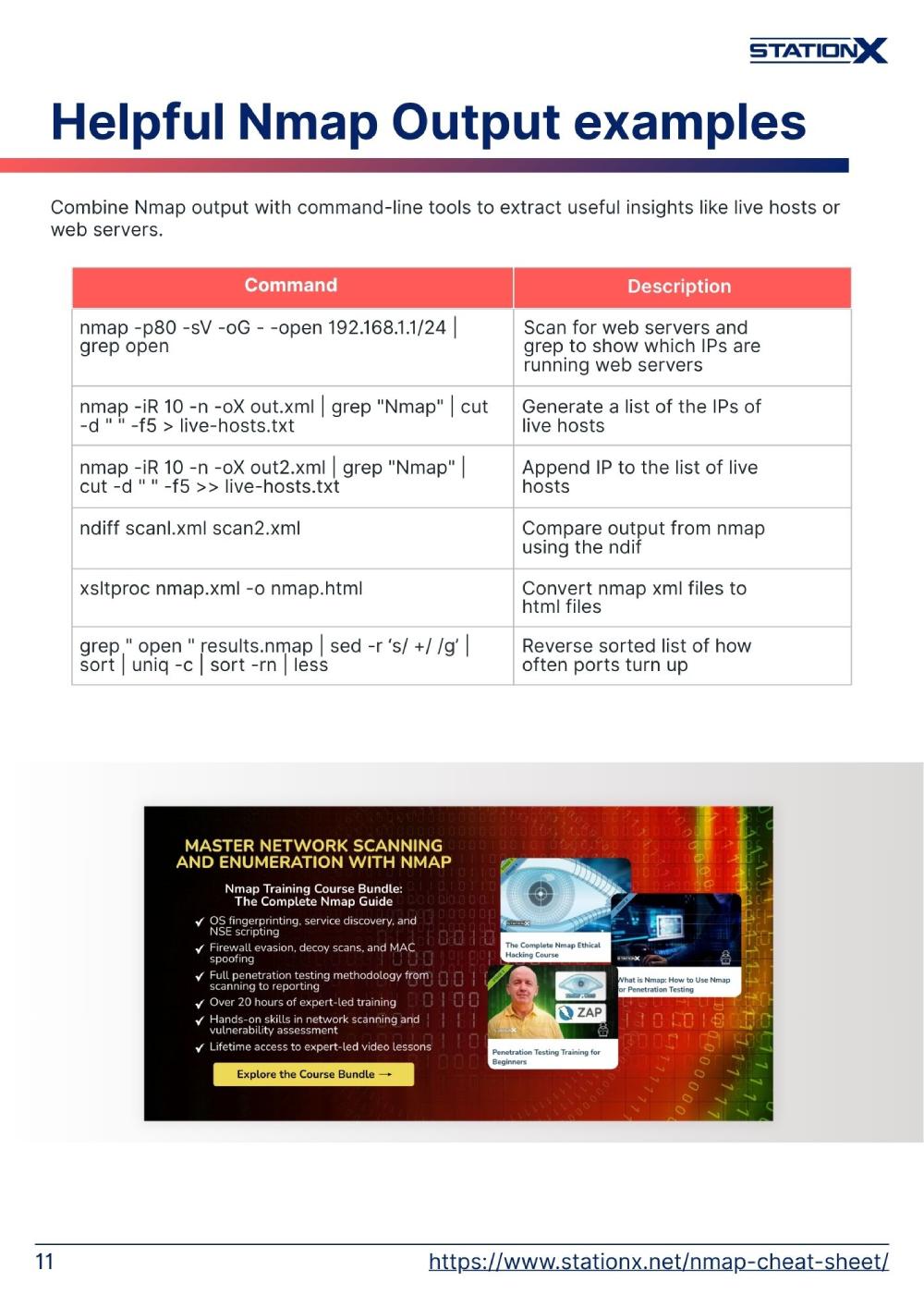
Helpful Nmap Output examples
Combine Nmap output with command-line tools to extract useful insights like live hosts or web servers.
| COMMAND | DESCRIPTION |
| nmap -p80 -sV -oG - -open 192.168.1.1/24 | grep open | Scan for web servers and grep to show which IPs are running web servers |
| nmap -iR 10 -n -oX out.xml | grep "Nmap" | cut -d " " -f5 > live-hosts.txt | Generate a list of the IPs of live hosts |
| nmap -iR 10 -n -oX out2.xml | grep "Nmap" | cut -d " " -f5 >> live-hosts.txt | Append IP to the list of live hosts |
| ndiff scanl.xml scan2.xml | Compare output from nmap using the ndif |
| xsltproc nmap.xml -o nmap.html | Convert nmap xml files to html files |
| grep " open " results.nmap | sed -r ‘s/ +/ /g’ | sort | uniq -c | sort -rn | less | Reverse sorted list of how often ports turn up |
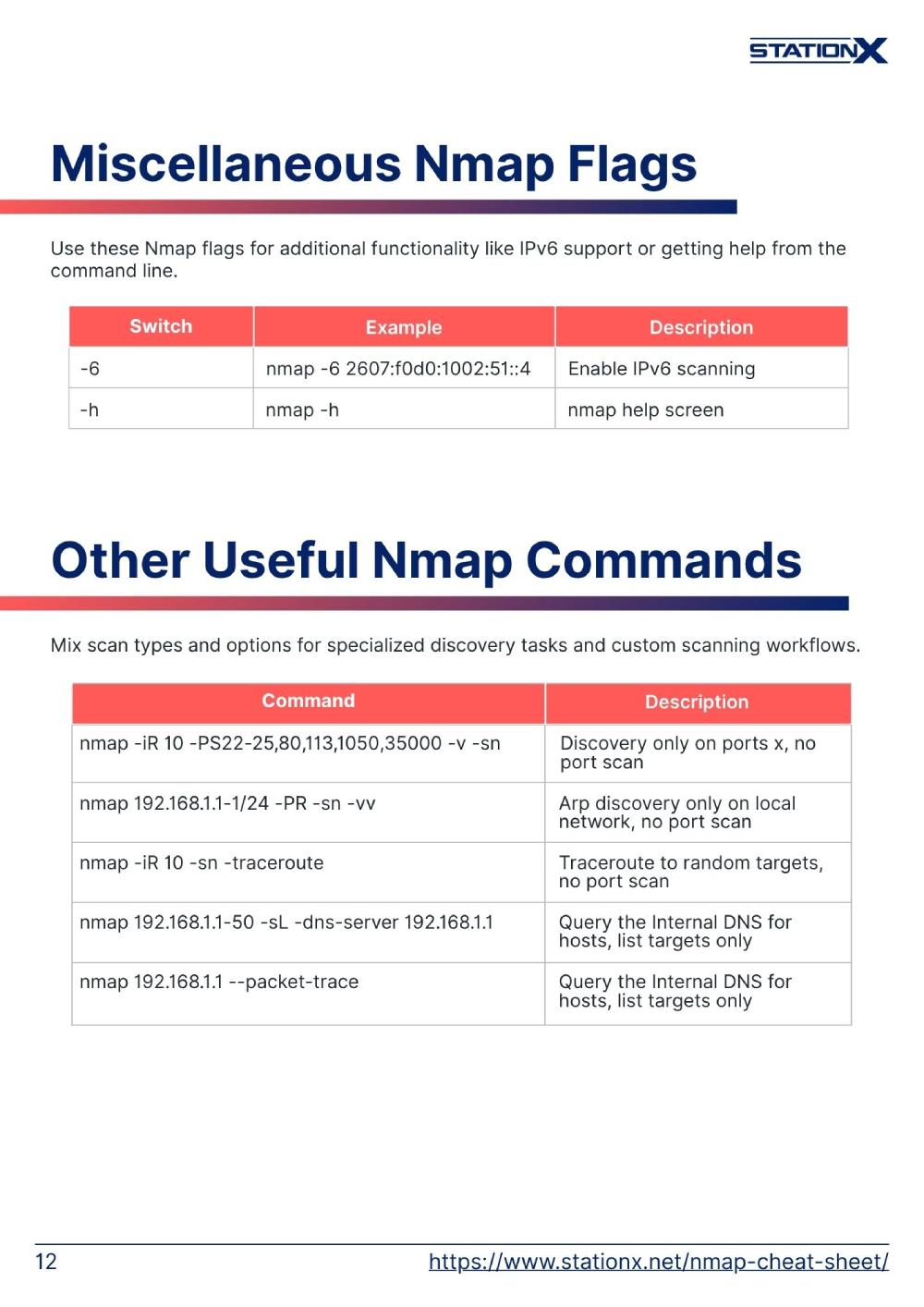
Miscellaneous Nmap Flags
Use these Nmap flags for additional functionality like IPv6 support or getting help from the command line.
| SWITCH | EXAMPLE | DESCRIPTION |
| -6 | nmap -6 2607:f0d0:1002:51::4 | Enable IPv6 scanning |
| -h | nmap -h | nmap help screen |
Other Useful Nmap Commands
Mix scan types and options for specialized discovery tasks and custom scanning workflows.
| COMMAND | DESCRIPTION |
| nmap -iR 10 -PS22-25,80,113,1050,35000 -v -sn | Discovery only on ports x, no port scan |
| nmap 192.168.1.1-1/24 -PR -sn -vv | Arp discovery only on local network, no port scan |
| nmap -iR 10 -sn -traceroute | Traceroute to random targets, no port scan |
| nmap 192.168.1.1-50 -sL -dns-server 192.168.1.1 | Query the Internal DNS for hosts, list targets only |
| nmap 192.168.1.1 --packet-trace | Show the details of the packets that are sent and received during a scan and capture the traffic. |
When to Use Which Scan Type
Choosing the right scan type depends on your goals, network position, and how much noise you can afford to make.
| Switch | Example | Description |
| -sS -T2 | nmap -sS -T2 192.168.1.10 | Standard scan, but slower - reduces detection likelihood |
| -sT | nmap -sT 192.168.1.10 | If you do not have root privs on your machine (logged, so not stealthy) |
| -sA | nmap -sA 192.168.1.10 | Tell you whether a firewall is statefully inspecting traffic |
| -sU -sV --top-ports 20 | nmap -sU -sV --top-ports 20 192.168.1.10 | Checks important UDP ports - needed for comprehensive enumeration |
Red Team Considerations
When conducting red team engagements, your scan strategy needs to prioritize operational security
| Command | Description |
| nmap -sS -T0 -f --data-length 64 --scan-delay 10s 192.168.1.10 | 5 minutes between probes, fragment packets to evade simple packet filters, append random data to avoid signature detection, add additional delay between probes |
| nmap -sS --randomize-hosts -iL targets.txt -T2 --max-retries 1 | Don't scan sequentially, don't retry aggressively, look more like organic network traffic. |
| nmap -g 53 192.168.1.10 | Some firewalls allow traffic from DNS (53) or HTTP (80) without inspection |
Reading Nmap Output
Understanding what Nmap tells you is just as important as running the scan. Here's how to interpret the results.
Port States
Nmap classifies ports into six states
| State | Meaning |
| Open | A service is actively accepting connections on this port. This is your target—something is listening. |
| Closed | The port is accessible (no firewall blocking), but no service is listening. |
| Filtered | Nmap can't determine if the port is open because packet filtering (firewall, IPS, router ACL) is preventing probes from reaching it. You're not getting responses—you're getting silence. |
| Unfiltered | The port is accessible, but Nmap can't determine if it's open or closed. |
| Open|Filtered | Nmap can't tell if the port is open or filtered. |
| closed|filtered | Rare state, usually seen with IP ID idle scans. The port is either closed or filtered. |
What to Do
How do you proceed with each state?
| State | Next Steps |
| Open | Potential attack vector - enumerate service |
| Closed | Nothing useful is running here. |
| Filtered | Try different scan types or evasion techniques to bypass the filter. |
| Unfiltered | You need a different scan type to determine if a service is running. |
| Open|Filtered | Run service detection (`-sV`) or NSE scripts to probe deeper. |
| Closed|Filtered | You can try a different scan type, but may not be helpful |
Conclusion
You are only doing yourself a disservice by failing to learn and utilize all of Nmap’s features. It is the first go-to tool you will use in the scanning and enumeration stage of many assessments, setting the foundation for the rest of your pentest.
Keep a copy of this Nmap cheat sheet to refer back to, and consider our StationX Master's Program for complete cyber security training.
You can also purchase our Nmap Course Bundle below to get started with Nmap today.
The Nmap Course Bundle includes:
- The Complete Nmap Ethical Hacking Course
- What is Nmap: How to Use Nmap for Penetration Testing
- Penetration Testing Training for Beginners







THANK YOU!!! I used to use Legion but for some reason the frontend is proving unreliable, so I need to put on my big boy pants and use Nmap the proper way.
Thanks
Thank you! It’s content like this that helps make the membership cost worth it. Don’t get me wrong, the sheer content on the website makes it worth the cost but this stuff is just icing on the cake!
nmap –A –T3 –S 192.168.1.2 –p- 192.168.1.6
Thanks a ton. It is very useful.
Solved problem
jsjs
Very good informations, Thanks a lot.
Thanks you