Have you ever wondered “what is a C2 framework” or “C2 server”?
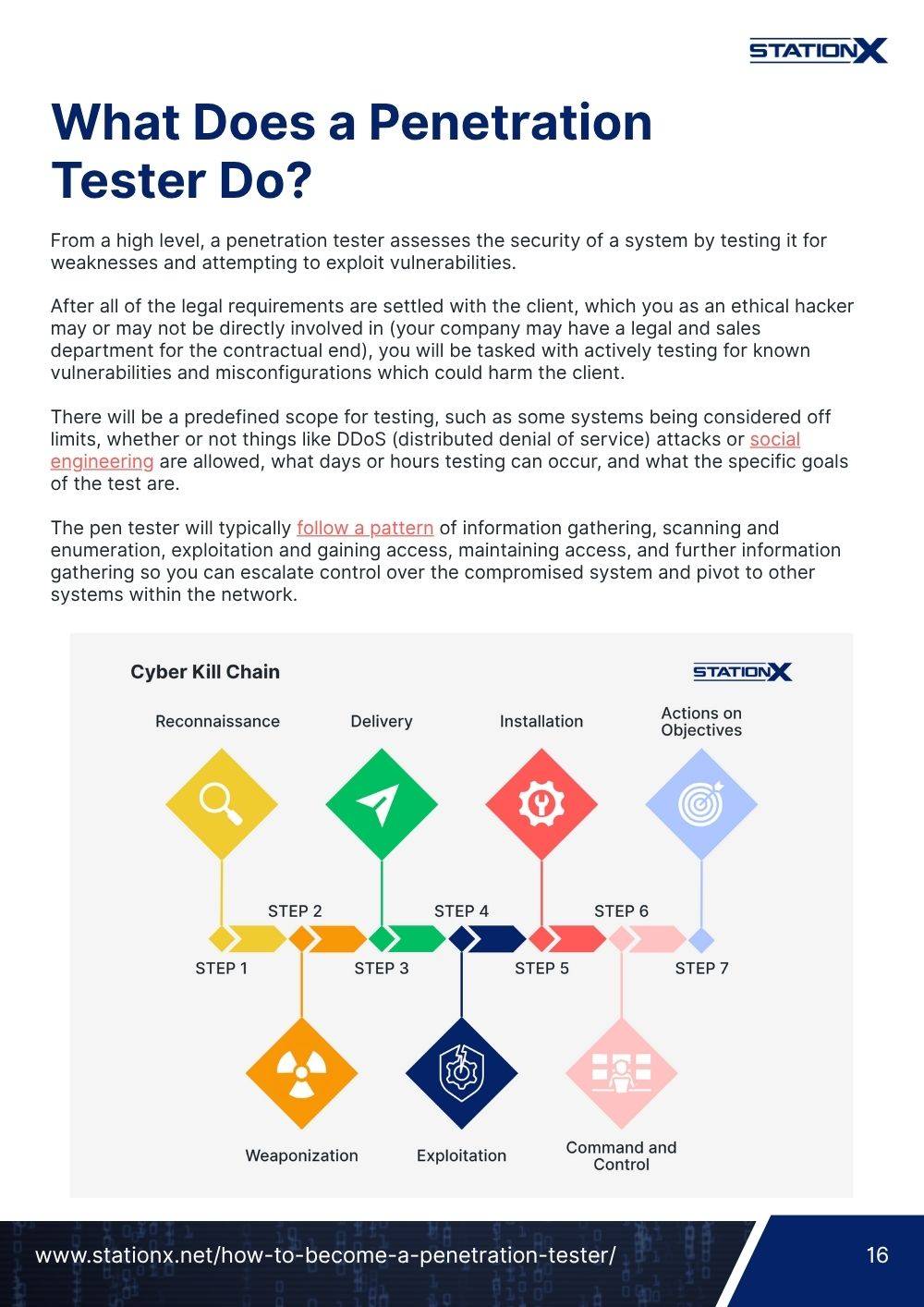
If you’ve been in the hacking game for long enough, you’ve likely come across these terms, heard advanced penetration testers or red teamers talk about them, and may even know that C2 stands for Command and Control.
Now is the time to unmask C2 frameworks and learn everything about them.
In this guide, you’ll learn what is a C2 server and framework, why you’d want to use one, and the key benefits they can provide you and your team.
You’ll discover some of the most popular C2 frameworks available today and get hands-on experience using the popular open-source C2 framework Havoc.
Let’s dive in and explore the fascinating world of C2 frameworks!
What Is a C2 Framework?
If you’ve ever performed hacking or penetration testing before, you’ll know about malware and shells.
You execute a piece of malware on a target machine, which creates a terminal session or shell that connects back to you (reverse shell), or you connect to (bind shell). You can then remotely control the target machine.
Every hacker wants to get a shell on a target system to perform post-exploitation tasks like gathering credentials, exfiltrating data, or pivoting to new targets using techniques like kerberoasting.
A C2 framework takes the idea of shells to the next level. They provide a centralized platform for controlling hundreds of compromised systems within a target network and are used in nearly every real-world cyber attack.
Moreover, the C2 Framework has advanced automation capabilities and incorporates various top-tier tools and assets effortlessly. This aids in lateral movement, post exploitation enumeration, privilege escalation, persistence, and more.
Usually, C2 frameworks have three parts: a C2 server, a C2 client, and a C2 agent.
- C2 Server: The central command center for managing compromised systems, C2 communication, and data.
- C2 Client: Software installed on a C2 operator’s machine that allows them to connect to the C2 server and interact with compromised machines.
- C2 Agent: Malware installed on a compromised target machine that connects back to a C2 server and allows an operator to control the infected machine remotely. This is also known as a C2 implant or bot, depending on the C2 framework you are using.

You execute the C2 agent on a target machine, and the agent connects back to your public-facing C2 server.
An operator logs into the C2 server to interact with the compromised machine through the server.
The operator can interact with the C2 server and compromised systems using a command-line or graphical interface (GUI). Many advanced C2 frameworks include both so an operator can visualize the systems they are attacking.

But why do you need a C2 framework? Why not just use a reverse shell? Let’s learn more.
What Is the Purpose of a C2 Framework?
C2 frameworks are platforms designed to provide you with the capabilities to perform post-exploitation tasks, maintain access to systems, and work collaboratively with others to achieve your objectives.
C2 infrastructure is designed to use a client-server model where multiple C2 clients can connect to a centralized C2 server through an intuitive user interface, from which they can attack systems.
This allows multiple operators to work simultaneously, provides a central point for data exfiltration, and only takes a single public-facing IP/domain, making setting up new C2 infrastructure easier.
Typically, C2 infrastructure will be created using C2 redirectors (machines that redirect C2 traffic to the C2 server). If one of these machine’s IPs or domains gets blocked, you can just spin up another C2 redirector to take its place and point this to the C2 server.
The architectural design of C2 frameworks also makes them considerably more stable than reverse or bind shells. The public-facing C2 server means you don’t need your own system in a DMZ to get callbacks—that’s the server’s job.
This, along with a well-engineered C2 agent, means there’s less chance of interruption or disconnection when you’re hacking. You could shut down your client machine and connect back to the server at a later time without losing any shells.
If you’re still not convinced, another powerful feature of C2 frameworks is their support for external post-exploitation hacking tools and hiding the execution of these tools in memory: tools like Mimikatz, BloodHound, and Nmap.
This capability means you can tailor a framework to your needs using tools you’re comfortable with. You can even use different C2 agents or frameworks together. For instance, connecting a Metasploit agent to a Cobalt Strike C2 server.
To explore more hacking tools that C2 frameworks can work with, try reading Top 20 Network Penetration Testing Tools.
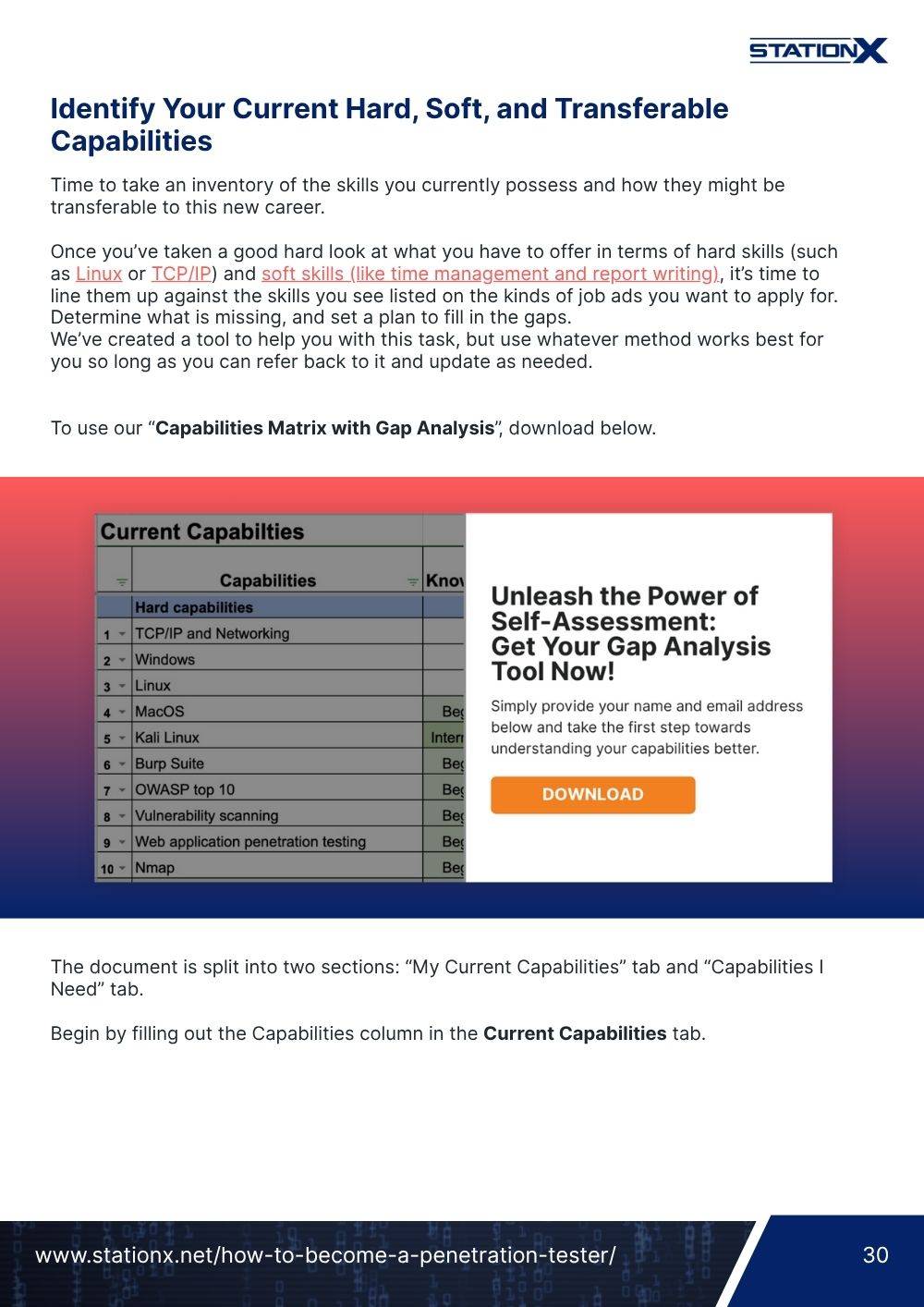
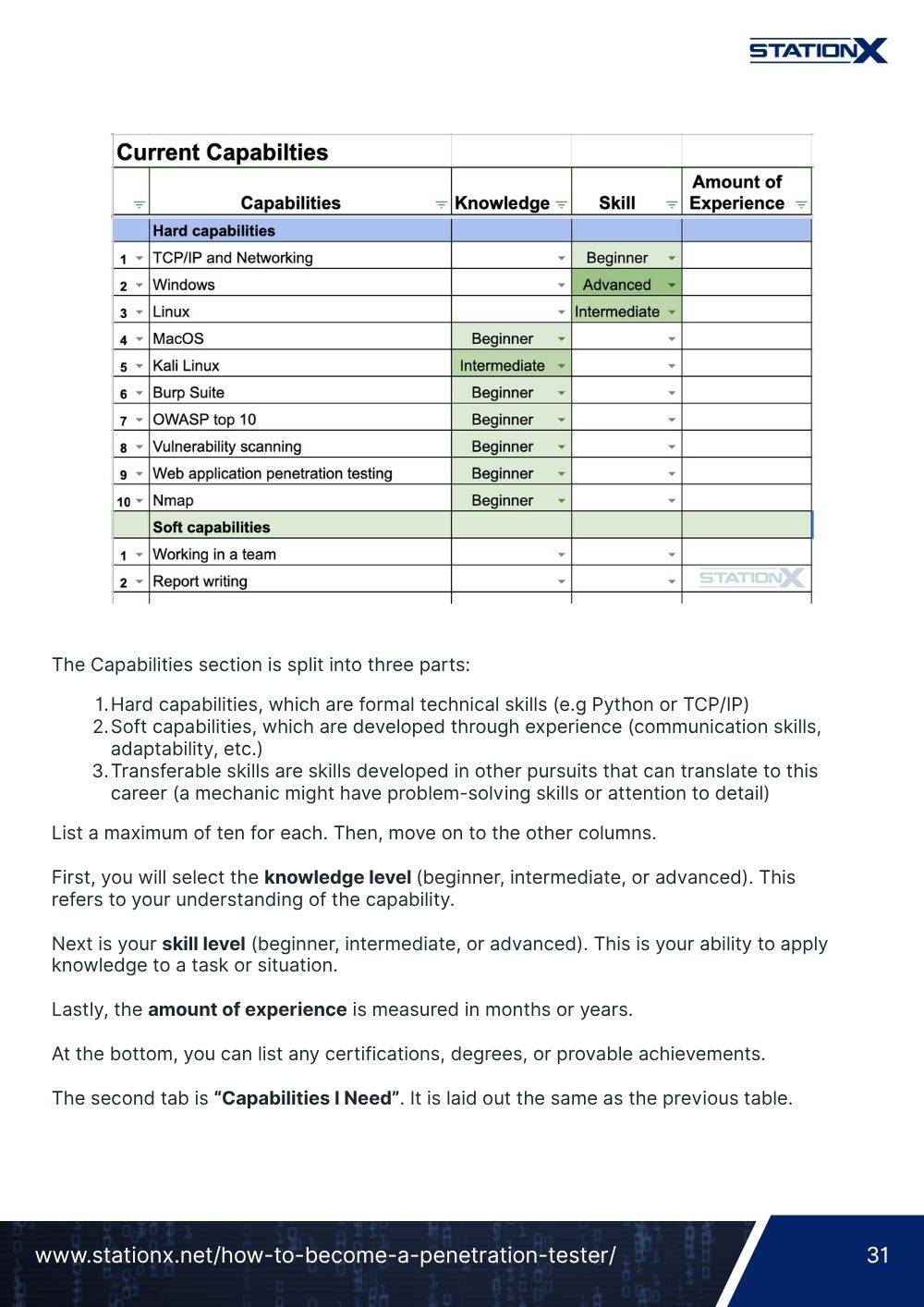
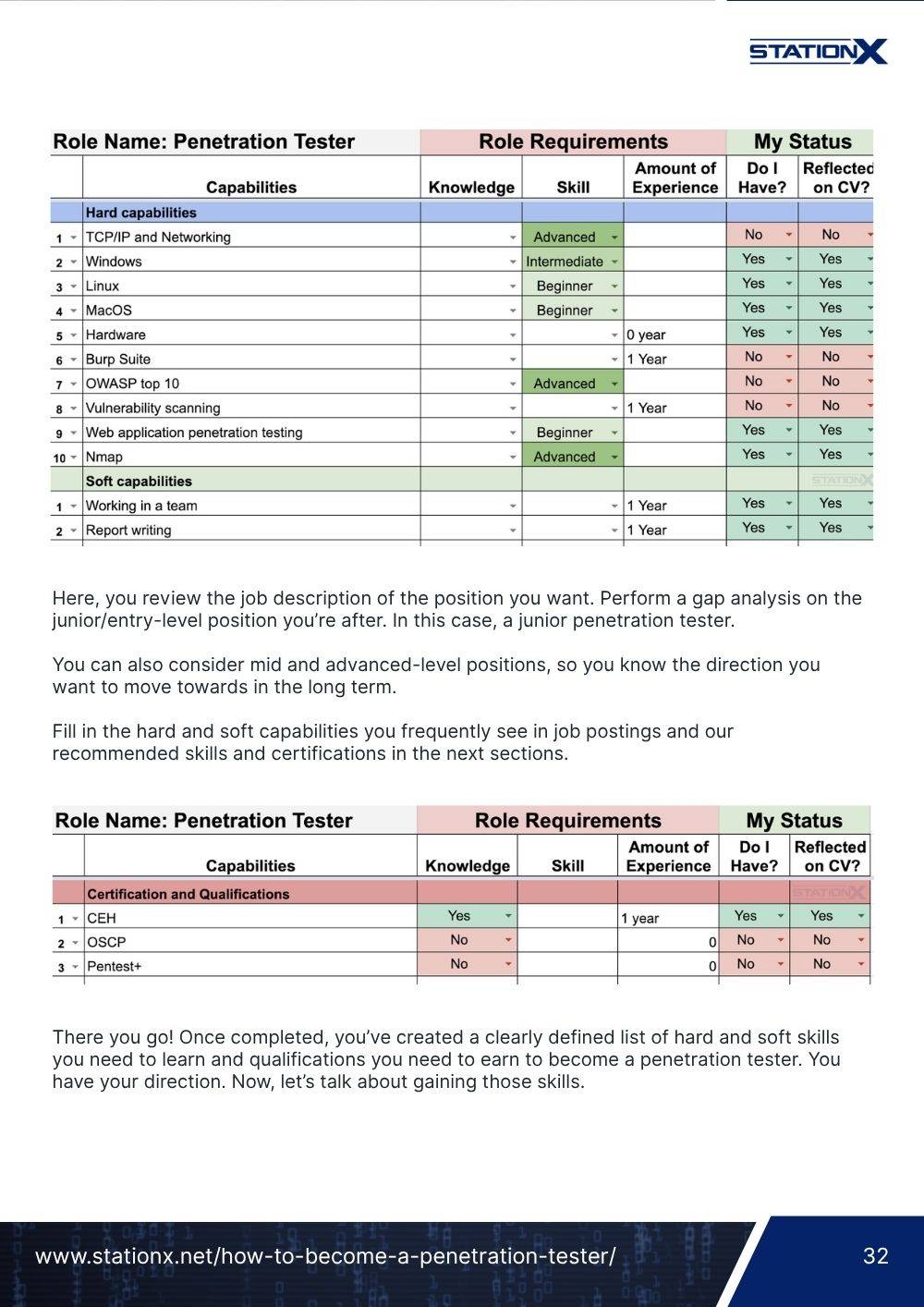
These qualities make C2 frameworks ideal for red teaming or purple teaming exercises where security professionals need to mimic real-world attacks to test their defensive capabilities.
What Are the Benefits of a C2 Framework?
Now you know what frameworks are and why attackers use them, so let’s explore some of the key benefits of these platforms.
Benefits of C2 Frameworks
CompTIA PenTest+ Voucher
Launch your pentesting career with a discounted CompTIA PenTest+ Voucher. Save up to 30% and earn your certification with an authorized CompTIA partner.
What Are Some Popular C2 Frameworks?
So now you want to get your hands dirty and start using a C2 framework. Great! But which one should you use? Let’s look at some of the most popular C2 frameworks to help you decide.
Cobalt Strike
Cobalt Strike is a commercial adversary simulation and red team operations platform widely used in the security industry by penetration testers, red teamers, and purple team exercises. It is one of the industry leading tools for C2 frameworks, but its advantages come with a premium price tag.
Use case: A powerful and versatile C2 framework suitable for advanced security testing. It is ideal for commercial red team operations.
PowerShell Empire
PowerShell Empire is an open-source post-exploitation framework that extensively uses the PowerShell scripting language, typically found on Windows systems. You can learn more about PowerShell Empire in this comprehensive guide.
Use case: Perfect for Windows environments that use PowerShell scripts, C#, or Python.
Slither
Slither is an open-source, cross-platform adversary emulation and red team framework designed for security testing on Windows, MacOS, and Linux machines.
Use case: Ideal for encrypted communications and advanced evasion techniques. It is a C2 framework at the cutting edge of adversary emulation.
Havoc
Havoc is free, open-source, and easy to set up. It provides a client interface for interacting with the C2 server in real-time through API calls, similar in look and feel to Cobalt Strike.
Use case: Great alternative to Cobalt Strike.
Brute Ratel C4
Brute Ratel C4 is a commercial red team and adversary simulation platform that can automate the execution of adversary tactics, techniques, and procedures (TTPs), will map attacks to the MITRE ATT&CK matrix for reporting, and supports multiple command and control channels.
Use case: Focuses heavily on evading modern EDR solutions and bypassing defenses.
Setting Up a C2 Framework With Havoc
This demonstration will show you how to set up and use the Havoc C2 framework. Havoc is an excellent choice for those starting with C2 frameworks. It’s open-source, easy to set up, and provides an intuitive GUI for interacting with your C2 agents.
Havoc Lab Setup
This demonstration consists of a Kali Linux machine where you will install Havoc and a Windows 10 workstation, which will be the target machine for your attacks. To learn how to install Kali Linux as a virtual machine and create your own hacking lab, read the following guides:
- How to Install Kali Linux on VMware: The Ultimate Guide
- How to Install Kali Linux on VirtualBox & Start Hacking Now
- How to Create a Virtual Hacking Lab: The Ultimate Hacker Setup
Once you have a Kali Linux and Windows 10 virtual machine setup, you can install Havoc.
Havoc Installation
To install Havoc, clone the GitHub repository with the command git clone https://github.com/HavocFramework/Havoc.git.

Next, move into this cloned directory and install the required dependencies by executing the following two commands:
cd Havoc
sudo apt install -y git build-essential apt-utils cmake libfontconfig1 libglu1-mesa-dev libgtest-dev libspdlog-dev libboost-all-dev libncurses5-dev libgdbm-dev libssl-dev libreadline-dev libffi-dev libsqlite3-dev libbz2-dev mesa-common-dev qtbase5-dev qtchooser qt5-qmake qtbase5-dev-tools libqt5websockets5 libqt5websockets5-dev qtdeclarative5-dev golang-go qtbase5-dev libqt5websockets5-dev python3-dev libboost-all-dev mingw-w64 nasm

Now build the Havoc C2 server (called “Teamserver” in the documentation) by running the following commands:
cd teamserver
go mod download golang.org/x/sys
go mod download github.com/ugorji/go
cd ..
make ts-build

Then, build the Havoc C2 client with the make client-build command.

Next, edit the ./profiles/havoc.yaotl file to match the following configuration.

You can change the user and Password variables to whatever you like (1).
Importantly, the Teamserver is being run locally on the same Kali Linux machine on which you run the client. To run the server locally, you must change the Host variable to 127.0.0.1 (2).
Note that in a real-world environment, the server would not be run locally on your machine. Instead, it would be on a different public-facing machine to which multiple clients could connect. This would likely be hosted on the cloud or somewhere that is unlikely to face downtime.
Start the Havoc C2 server using the default profile by executing the command ./havoc server --profile ./profiles/havoc.yaotl.

Connect to the C2 server by starting the Havoc C2 client with the command ./havoc client (1).
Use the details you created in the ./profiles/havoc.yaotl file to connect to the C2 server. Click the New Profile button (2), insert the local IP address (3), and then add the username and password you set (4).
Finally, press Connect to connect to the Havoc server (5).

You will be greeted by the default Havoc dashboard.

With the C2 server and client running, you can move on to deploying agents on compromised systems.
Using the C2 Framework Havoc
Now that you’ve installed everything, let’s start using our first C2 framework.
Deploying an Agent With Havoc
There are three steps to perform when deploying a C2 agent on a compromised machine using Havoc.
Step 1: Create a Listener
First, you must create a Listener in the Havoc interface to listen for incoming connections from Havoc agents. To do this, select the Listeners option from the View dropdown menu.

This will bring up the Listeners tab. Click the Add button to bring up the Create Listener popup wizard.

Fill out the Name of the listener (1), leave the payload as Https (2), make sure the Host is set to the IP address of your Kali Linux machine (3), and then click Save (4).

Clicking Save will create your listener on the Havoc Teamserver.

You can now create a payload that executes the Havoc C2 agent and connects back to this listener.
FREE Cyber Security Career Guide
Thinking of a career in cyber security? Our Cyber Security Career Guide walks you through the industry landscape, skill-paths, certifications, and realistic timelines to become job-ready.
Step 2: Create a Payload
To create a payload in Havoc, select the Payload option from the Attack dropdown menu.

This will bring up the Payload wizard, which you can use to customize your options.
Select the Listener you want the payload to connect to (1), the Architecture you are targeting (2), and the Format you want the payload in (3).
For modern Windows operating systems, this will be x64 and Windows Exe. You can leave the rest of the configuration options as their default values and select Generate to create your payload (4).

Once generated, Havoc will ask you where you want to save your payload. Remember this location. You’ll need to use your payload later.

Step 3: Transfer and Execute the Payload
The next step is transferring your Havoc payload onto your target machine.
In the real world, uploading and executing a payload on a target machine is typically done through a phishing email.
For the purpose of our demo, you’ll simply transfer the file to the target machine and execute it manually.
First, navigate to the directory where you saved your Havoc payload, then create a Python HTTP server with the command python3 -m http.server.

Now, on your Windows 10 target machine, open a web browser and navigate to the IP address of your Kali Linux machine. Make sure you disable protections in the Windows Security application, such as Virus & Threat Protection and App & Browser Control. This will ensure the payload executes and is not blocked by Windows Defender.
In the real world, you’d use obfuscation techniques to hide the malicious nature of your payload. This would be done to avoid detection from any system protections and trick the victim into executing it.

Select the executable file. Once downloaded, click the Open file link and select the Run option.

Finally, jump back on your Kali Linux machine and confirm the payload ran, the C2 agent was deployed, and you have a connection from your target machine to the Havoc C2 server.

Once you have a C2 agent running on your target machine, you can start running commands and interacting with the compromised host.
Running Havoc C2 Commands
To execute remote commands on a compromised machine, you first need to connect to the C2 agent you want to run commands through. To do this, right-click on the agent and select Interact from the popup menu.

This will bring up the C2 agent’s tab at the bottom of the Havoc GUI. You can issue commands at the bottom command bar (1) and see the results populate in the output tab (2).

To discover what commands you can execute, run the help command.

Scrolling through the help menu will reveal a lot of commands you can run. Poplular ones include:
whoamito get information about the current user and their privileges.powershellto run Windows PowerShell commands.uploadanddownloadto put files onto the machine or take them off.shellto drop into a command shell.tokento manipulate and impersonate Windows tokens.screenshotto take a screenshot of the current user’s desktop.- And many more!
You can even generate a graphical map of the hosts you have infected and their connections back to your Havoc C2 server by selecting View > Session View > Graph.

This is very useful when you have pivoted deep inside an organization’s network and need to see the path traffic is taking on its way out.

Legal and Ethical Considerations When Using C2 Frameworks
Congratulations, you now know how to set up and work with a C2 framework!
However, with great power comes great responsibility, and for C2 frameworks, this means making legal and ethical considerations when using these powerful tools.
To help you quickly get up to speed on the legality and ethics of using C2 frameworks, here are some key things to consider before performing any hacking activity:
- Obtain written permission. The most important thing in any penetration test or red team engagement is having legal permission to perform the testing activity. Make sure you and the client sign a legal contract that stipulates what testing you will be performing and that you have permission to do it. There can be serious consequences if you fail to get legal consent.
- Clearly communicate with the client and set expectations. The client needs to know what type of testing you’ll perform and a high-level overview of how it’ll be done. They may not need to know specific tactics and techniques, but they need to be able to differentiate your testing from a real-world attack. You should have a point-of-contact (POC) on your team that the client can contact to confirm if testing activity is ongoing when they start seeing alerts.
You can learn more about the legal and ethical considerations of penetration testing, red teaming, and hacking in Is Hacking Illegal? The Law and Ethical Perspectives.
Conclusion
C2 frameworks are awesome tools. They allow you to evade detection, remain stealthy, and scale your penetration testing or red team operations to new levels with centralized management and robust mechanisms for interacting with compromised systems.
Many C2s even include advanced customization options that allow you to tailor your C2 infrastructure to a specific target or objective.
This article detailed the purpose of C2 frameworks, the benefits they offer, and some popular commercial and open-source ones you can use. You even got some hands-on experience using the Havoc C2 framework!
If you want to learn more about C2 frameworks and other advanced hacking techniques, check out one of the courses available to members of the StationX Master's Program.
Our membership provides access to over 30,000 courses and labs, career mentorship, study and mastermind groups, an active community of students and professionals, certification roadmaps, and much more to ensure you succeed in your cyber security career goals.
Master red team tactics, including reconnaissance, Active Directory attacks, firewall evasion, scripting and API hacking, post-exploitation techniques, and enterprise phishing. Think, operate, and report like a professional red team operator in live environments and emulate real attackers
This Red Team Hacker Bundle includes:
- Red Teamer Hacking Course: Learn Ethical Hacking Volume 1
- Red Teamer Hacking Course: Learn Ethical Hacking Volume 2
- Red Teamer Hacking Course: Learn Ethical Hacking Volume 3
- Windows API Hacking Course With Python
- Breaching The Perimeter With Enterprise Phishing Training
- Get a Red Team & Penetration Tester Job Course
- The Complete Nmap Ethical Hacking Course