So you’re looking to become an ethical hacker? That is definitely an excellent choice! The realm of ethical hacking presents an intriguing career path, delving into the world of cyber security through an offensive, yet ethical, lens.
However, quantifying the timeline to become an ethical hacker or a junior-level penetration tester is not a cakewalk. In order to plan for your professional ethical hacking career, you must know, "How long does it take to become an ethical hacker?"
This article specifically answers this question by providing a comprehensive roadmap that details the significance and complexity of estimating timelines. It also extensively details other considerations, including foundational knowledge assumptions, certification preparation, technical and soft skills, and practical experience requirements.
So, without further ado, let's dive in and discover how long it takes to become an ethical hacker!
Foundational Knowledge Assumptions
If you want to start learning ethical hacking, you are expected to have a solid foundational knowledge of fundamental concepts of information technology (IT), operating systems, networking, and cyber security. Having prior foundational knowledge plays a crucial role in enhancing your ethical hacking capabilities and making your ethical hacking journey seamless.
Following are some of the foundational skills you must master before beginning a career as an ethical hacker.
- Basic IT Concepts:
- Understanding of fundamental IT concepts, including hardware, software, networking, and data storage.
- Operating Systems:
- Proficiency in operating systems such as Windows, Linux, and macOS.
- Command-line interface (CLI) familiarity, especially in Linux distributions like Ubuntu, Kali Linux, or CentOS.
- Networking Fundamentals:
- Knowledge of networking protocols (TCP/IP, SSH, DNS, DHCP, HTTP/HTTPS, etc.).
- Understanding of network devices (routers, switches, firewalls) and their functionalities.
- Ability to configure and troubleshoot network settings.
- Cyber Security Basics:
- Awareness of cyber security concepts, including confidentiality, integrity, and availability (CIA triad).
- Awareness of security principles such as authentication, authorization, encryption, and hashing.
- Knowledge of common security mechanisms like firewalls, VPNs, and intrusion detection/prevention systems.
- Understanding of common cyber threats and attack vectors.
- Continuous Learning Attitude:
- Ethical hacking is a dynamic field; readiness to learn continuously and stay updated with the latest tools, techniques, and threats is crucial.
Time Estimate for Gaining Foundational Knowledge:
Note that the journey toward becoming an ethical hacker is inherently unique for each individual, and the duration required to achieve proficiency significantly relies on the existing background in technology and cyber security.
This personalized trajectory is shaped by diverse factors, including prior education, professional experience, technical acumen, and familiarity with IT, networking, ethical hacking, and cyber security concepts. We do break this down in the article, “How Long Does It Take To Learn Cyber Security,” which we strongly recommend reading if you’re still at this stage of your career.
The following courses can help you gain the foundational knowledge and practical skills that you require to begin becoming an ethical hacker:
Learning Ethical Hacking Skills in Certification Preparation
Once you’ve mastered the foundational knowledge, you can proceed to prepare for the actual ethical hacking concepts. Remember that certifications hold immense value in the realm of ethical hacking, especially for aspiring penetration testers. They serve as tangible proof of an individual's expertise, validating their skills and knowledge in various cyber security domains.
Certifications not only enhance your credibility but also provide structured learning paths, ensuring a comprehensive understanding of ethical hacking methodologies, tools, and practices. Employers often prioritize candidates with relevant certifications, considering them reliable indicators of proficiency and dedication to the field. OSCP is one such certification that employers typically look for from candidates for ethical hacker and penetration tester roles.
OffSec Certified Professional (OSCP):
Among the plethora of certifications available, the OffSec Certified Professional (OSCP) stands out as one of the most esteemed and practical certifications for ethical hackers. Offered by OffSec, the OSCP emphasizes hands-on experience and practical skillsets crucial for penetration testers and is in high demand.
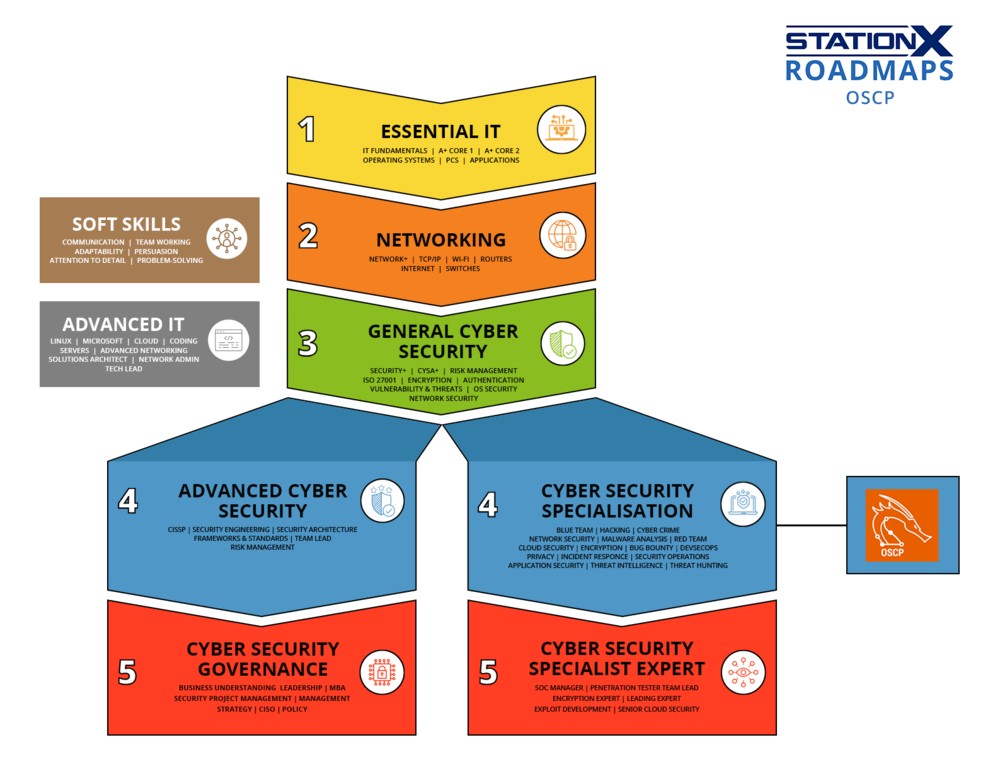
The roadmap below shows us where the OSCP certification falls in terms of skills and abilities. OSCP falls into stage four of StationX’s cyber security roadmap, which is “cyber security specialization.” Depending on the company, this can be viewed as anywhere from entry-level to intermediate roles.
Skills Required for OSCP:
OSCP is a penetration testing certification designed by the creators of Kali Linux to test your real-world penetration testing knowledge and skill set. Some of these skills, as outlined in the OSCP syllabus, include:
- Penetration Testing Methodologies:
- Understanding and application of penetration testing methodologies like reconnaissance, vulnerability scanning, exploitation, and post-exploitation techniques.
- Network Scanning and Enumeration:
- Nmap: A versatile tool for network discovery, scanning, and reconnaissance.
- The Harvester: Gathers information from various sources, facilitating reconnaissance and information gathering.
- Network Hacking: Proficiency in network hacking concepts, including network scanning, firewall evasion, and network sniffing.
- Exploitation Frameworks:
- Metasploit: An essential penetration testing framework aiding in exploitation, post-exploitation, and vulnerability validation.
- Web Application Testing:
- Burp Suite: A comprehensive tool for web application security testing, including scanning for vulnerabilities and web application proxy.
- SQL Injection: Writing SQL scripts and understanding SQL injection in addition to utilizing tools like SQLMap for database exploitation.
- Password Cracking and Hash Analysis:
- John the Ripper: A widely-used password cracking tool for dictionary attacks and brute forcing.
- System hacking: Proficiency in endpoint or system hacking methodologies, including account takeover, privilege escalation, password attacks, etc.
- Basic Scripting/Programming Skills for Tool Usage:
- Scripting languages (e.g., basics of Bash and Python) for using basic ethical hacking tools for reconnaissance, scanning, exploitation, and privilege escalation.
- Report Writing:
- Capability to effectively document and communicate findings through detailed penetration testing reports.
- Problem-Solving and Persistence:
- A strong problem-solving mindset and persistence to tackle complex challenges inherent in penetration testing scenarios.
OSCP Preparation and Time Estimate:
Preparation for the OSCP demands a substantial investment of time and effort. Aspiring candidates typically dedicate anywhere between 200 to 400 hours to adequately prepare for the OSCP exam. This duration includes in-depth study, practical exercises, and hands-on labs to master the requisite skills.
Additional Technical Skills
In addition to certifications like OSCP, proficiency in various tools, concepts, and programming/scripting languages is paramount for ethical hackers and penetration testers. Mastering these technical skills enhances your ability to become an expert ethical hacker.
Overview of Additional Technical Skills
In addition to the skills that we discussed in the beginning, you may need additional technical and practical hands-on knowledge and skills to excel in ethical hacking. Some of the additional technical skills are:
- Packet Analysis and Network Traffic Inspection:
- Wireshark: A powerful packet analyzer used for network troubleshooting, analysis, and protocol examination.
- Advanced Programming and Scripting:
- Bash Scripting: Writing complex commands for various purposes in Linux environments.
- Python: Writing advanced scripts with the versatile scripting language that is used in the majority of ethical hacking tools.
- PowerShell: Useful for Windows exploitation and writing proof of concept malware files in certain scenarios. Effective in achieving system and account takeover, privilege escalation, lateral movement, etc.
- Active Directory (AD) Understanding:
- Mastery of Active Directory is essential for comprehending and exploiting Windows network environments.
- Databases:
- Basic understanding of databases and how they function.
- Knowledge of SQL (Structured Query Language) and database management systems.
Estimated Additional Study Hours:
Achieving proficiency in these technical skills typically demands an additional 100 to 200 hours of dedicated study, practice, and hands-on experimentation. You need to allocate substantial time to familiarize yourself with these tools, explore their functionalities, and gain practical experience by simulating real-world scenarios.
Gaining Real-World Experience
Real-world experience is a pivotal aspect of an ethical hacker or penetration tester's journey, offering invaluable insights and practical skills that certifications and theoretical knowledge might not provide. It bridges the gap between theoretical understanding and the actual challenges encountered in securing systems and networks.
Employers typically seek candidates with real-world experience, but it's not uncommon for entry-level candidates to lack this experience until they land a job. However, there are ways for a candidate to gain real-world experience. Let's see some of the ways that you can gain real-time experience that will help you land your dream job as a professional ethical hacker.
Capture The Flag (CTF) Challenges:
- Hands-on Application: CTF challenges simulate real-world scenarios, allowing ethical hackers to apply their knowledge in solving security-related puzzles and scenarios.
- Diverse Skill Development: Ethical hackers can encounter a wide array of challenges with the CTFs, enhancing their skills in various areas of cyber security, including (but not limited to) cryptography, reverse engineering, web exploitation, and network analysis.
- Collaborative Learning: CTFs often encourage teamwork, fostering collaboration and knowledge-sharing among participants.
Bug Bounties:
- Live Testing Ground: Bug bounty programs offer ethical hackers a platform to test their skills on real systems and applications, identifying and reporting vulnerabilities to organizations.
- Incentivized Learning: Monetary rewards or recognition incentivize ethical hackers to actively hunt for vulnerabilities, enhancing their problem-solving and reconnaissance skills.
Practical Scenarios:
In addition, to the aforementioned, here are some of the ways that StationX can help you build the practical experience:
- Moderating Focus Groups
- Leading Mastermind Groups
- Networking with Industry Experts
- Practical Exercises and Virtual Labs
- Contributing code on Github and within the StationX community
- Taking up Internship, teaching assistant, or co-op opportunities
Additional Hours for Real-World Practice:
Gaining substantial real-world experience through CTF challenges, bug bounties, and practical scenarios typically requires an additional 100 to 200 hours of dedicated practice. The experience gained in such real-world scenarios contributes significantly to an ethical hacker's skill set and readiness to tackle security challenges in diverse environments.
Meeting Job-Specific Requirements
Employers often have distinct requirements tailored to their industry, the complexity of their systems, and the nature of potential threats they face. These demands can vary significantly based on the type of position you are targeting within the cyber security landscape.
As you advance through your career journey, you must consider the job-specific requirements. It is imperative that you learn specialized tailored skills regardless of whether you're looking for jobs you're interested in or applying for a job that expects specific skills.
Tailored Requirements:
- Industry Focused Knowledge: Industries such as finance, healthcare, government, or technology might have specific compliance standards (e.g., PCI DSS, HIPAA, GDPR) that necessitate specialized knowledge and certifications.
- Specialized Skills: Certain job roles might require expertise in niche areas such as industrial control systems (ICS), IoT security, or cloud security, demanding additional specialized training and knowledge.
- Regulatory Knowledge: Understanding regional or industry-specific regulations and compliance frameworks becomes crucial in certain roles, influencing security strategies and risk mitigation approaches.
- Tool and Technology Preferences: Some employers might emphasize proficiency in specific security tools or technologies relevant to their infrastructure, necessitating additional training to meet their preferences.
- Threat Landscape Awareness: Awareness of the prevalent threats and attack vectors within a particular industry or sector is essential for developing tailored security strategies.
Time Estimation for Fulfilling These Requirements:
The time estimation for fulfilling these job-specific requirements typically ranges from 50 to 100 hours. This time is dedicated to acquiring specialized knowledge, training, or certifications tailored to the demands of the targeted job role. Candidates aiming for roles in specialized areas within ethical hacking often invest this time to ensure they meet the job-specific prerequisites and stand out as qualified candidates in their desired field.
Soft Skills Development
While technical expertise is fundamental, soft skills play an equally crucial role in the success of an ethical hacker or penetration tester. These skills enable effective communication, collaboration, and the ability to convey complex technical findings in a comprehensible manner.
Communication Skills:
Clear and effective communication is essential to convey technical vulnerabilities, risks, and recommendations to non-technical stakeholders. Collaboration with teams, explaining technical concepts, and articulating findings succinctly are critical aspects of an ethical hacker's role.
Report Writing:
The ability to document findings in comprehensive and articulate reports is crucial. This skill aids in conveying technical details, risks, and mitigation strategies to clients or stakeholders.
Problem-Solving and Analytical Thinking:
Strong problem-solving abilities and analytical thinking are indispensable in identifying and resolving complex security issues.
Adaptability and Creativity:
The ever-evolving nature of cyber security demands adaptability and creativity in devising innovative solutions to emerging threats.
Personal Branding and Interview Skills:
- Personal Branding: Establishing a personal brand through networking, online presence, and contributions to the cyber security community can significantly enhance visibility and credibility in the field.
- Interview Skills: Effective communication during interviews, showcasing technical expertise, and articulating one's experiences and skills are pivotal in securing a job in the cyber security domain.
Time Allocation for Developing These Skills:
Devoting approximately 50 hours to developing soft skills is crucial for aspiring ethical hackers. These 50 hours allocated to honing soft skills complement technical expertise, making an individual a well-rounded professional capable of not only identifying security flaws but also effectively communicating and collaborating to address them.
This time can be dedicated to various soft skill activities such as:
- Communication Improvement: Engaging in public speaking, attending workshops, or joining Toastmasters to enhance presentation and communication skills.
- Report Writing Workshops: Participating in courses or workshops focusing on technical writing and report creation.
- Networking and Personal Branding: Dedication to networking events, building an online presence through social media or blogs, and contributing to cyber security forums or discussions.
- Interview Preparation: Practice interview scenarios, mock interviews, and refining one's ability to convey technical knowledge effectively during interviews.
Note that the combination of technical prowess and strong soft skills elevates an ethical hacker's overall impact and value within the cyber security landscape.
Conclusion: How Long Does It Take To Become an Ethical Hacker?
The journey to becoming a proficient ethical hacker or a junior penetration tester demands a dedicated investment of time and effort, estimated to range from 500 to 950 hours.
While the estimated time to become an ethical hacker or a junior penetration tester varies, leveraging resources like the Master's Program by StationX can significantly optimize your learning curve, enhance skill development, and provide the support needed to thrive in the dynamic field of ethical hacking.
Accelerate your journey within the cyber security realm and unlock your potential to become an ethical hacker with StationX's tailored learning experience and vibrant community connections through our Master's Program.