Do you want to learn how to use Nmap for OS detection, or are you curious about how Nmap can detect operating systems in the first place?
Whether you need it for a penetration test, network mapping, or just for your own education, understanding Nmap's OS detection capabilities is valuable for any cyber security professional.
In this article, we will provide an overview of Nmap and then dive into the specific syntax for the commands used in OS fingerprinting.
You'll learn how the detection works under the hood and understand what you can reasonably expect from Nmap OS detection.
So, if you're eager to unlock the full potential of Nmap, let's get started!
What Is Nmap?
Nmap, short for Network Mapper, is an open-source tool commonly used in network discovery and security auditing.
Often referred to as the "Swiss Army Knife" of networking tools, Nmap is a staple in penetration testing.
It is employed to identify live hosts, detect operating systems, discover open ports, and enumerate running services on a network.
Nmap Command Generator
Say goodbye to the hassle of trying to remember the exact syntax for your Nmap commands! With our Nmap Command Generator, you can simply say what you need Nmap to do, and we will generate the command for you.
Nmap Commands to Detect Operating Systems
Let's start and show you how to use Nmap for OS detection. We will run our scans from a Windows system for demonstrations, but the commands are the same across different platforms.
The easiest way to perform an OS detection scan is by using the following command:
nmap -O <target>
Please note that running an OS detection scan with Nmap requires root privileges to send specialized network packets. You will need to precede the command with “sudo” to grant root access for this operation in Linux temporarily.
Information Security Courses Bundles
Want lifetime access to expert-led cyber security training? Explore our Information Security Course Bundles — one-time purchase packages covering top topics like Ethical Hacking, Cloud, Linux, DevSecOps, and CompTIA certifications.
Let’s scan an IP at 10.0.0.29 and see if Nmap can detect the OS running.

As you can see from the screenshot, Nmap identified Windows 10 as the operating system correctly. This information can be invaluable as a penetration tester as it will allow you to plan your exploits more effectively.
There may be instances where Nmap will not be able to identify the OS, such as in the screenshot below.

If this is the case, we can try and run the OS detection with the --osscan-guess flag. With this flag, Nmap will make an educated guess about the target's operating system. Nmap will provide a probability score in percentage form along with the guess. This increases the chance of getting some OS information but may be less accurate.
Let's try it with our previous example and see if Nmap can guess the operating system.
We can use the following command:
nmap -O --osscan-guess <target>
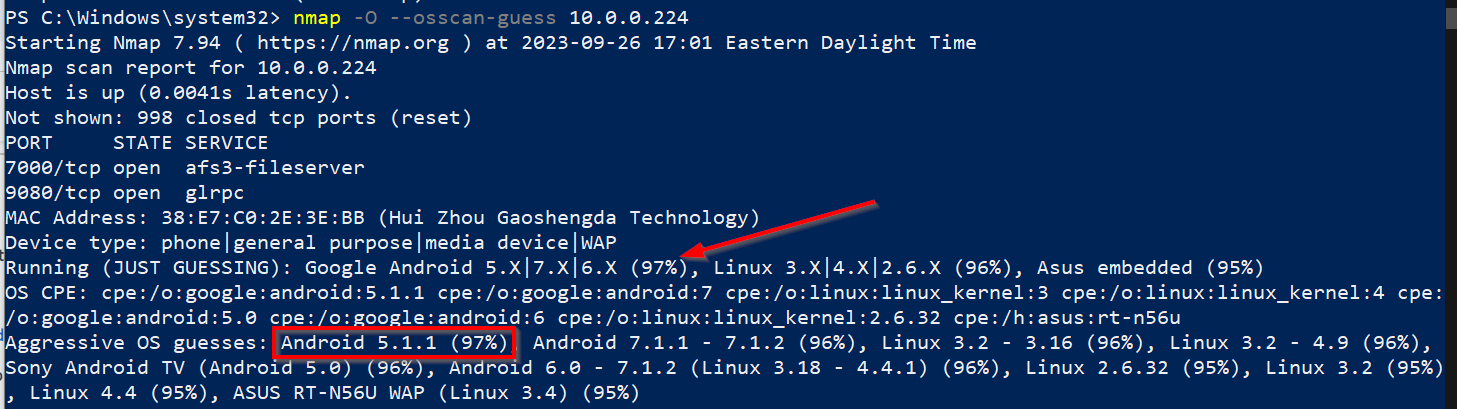
Using this command, Nmap accurately identified the operating system as Android and pinpointed the correct version. Such precise OS detection can be critical information for network administrators, security analysts, and penetration testers.
We can also execute an aggressive scan, which performs OS detection, service scanning, script scanning, and traceroute to help accurately identify the target's operating system.
Be cautious, though; this type of scan is even “noisier'” than a regular OS detection scan and is likely to be detected. Use it only when appropriate for your specific circumstances.
Let’s run the following command and see if it will help us detect the operating system.
nmap -A -T4 <target>

As you can see, Nmap figured out that the operating system is Windows 11. This information is crucial for further network analysis, vulnerability assessment, or compliance auditing.
How Does Nmap Detect Operating Systems
Nmap identifies the operating system of a target through either passive or active fingerprinting. We will take a closer look at both methods below.
Active Fingerprinting
In active fingerprinting, Nmap sends a series of specially crafted packets to the target host. It then observes how the host responds to these packets.
The response, such as TCP (Transmission Control Protocol) options, window sizes, and initial TTL (Time to Live) values, are compared against a database to determine the operating system.
Passive Fingerprinting
In passive fingerprinting, Nmap doesn't send any packets to the target. Instead, it observes the packets that the target sends during regular communication. By analyzing the attributes of these packets, such as the order of flags and options, Nmap can make an educated guess about the operating system.
Active fingerprinting is generally more accurate but can be detected by intrusion detection systems. Passive fingerprinting is stealthier but often less precise.
Fingerprinting Techniques
Nmap uses the following fingerprinting techniques to figure out the unique characteristics of a target's operating system. These include TCP/IP fingerprinting, service version detection, timing, and response.
TCP/IP Stack Fingerprinting
This is often the main way that Nmap does its OS detection. It involves sending various types of TCP and sometimes UDP packets to the target. How the target responds can indicate its operating system, as different OS’ have unique TCP/IP traffic settings.
Service Version Detection
While this is generally used to identify software running on specific ports, it can also give clues about the operating system. For example, certain software versions may only run on specific operating systems.
Timing and Response
The time intervals at which packets are processed and responded to can also provide hints about the OS. Some operating systems handle packet queues or prioritize certain types of traffic in a way that is characteristic of that OS.
CompTIA Voucher Hub
Planning your next CompTIA exam? Save up to 30% with our CompTIA Voucher Hub — official partner discounts for all CompTIA certifications, including Security+, Network+, A+, and more.
Accuracy
When Nmap performs OS detection, it lists possible operating system matches and probability percentages. These percentages reflect how closely the target system's responses align with known OS fingerprints in Nmap's database.
Higher probability scores indicate Nmap has high confidence in that OS guess. If you see a 97% score for a particular OS, it's highly likely that's the correct match.
Sometimes, Nmap will show multiple potential OS matches with varying confidence levels. This happens when the target system's responses partially match multiple known OS signatures.
Lower scores under 80% mean Nmap has less certainty about the OS guess. Such results can stem from unusual network conditions, the presence of a firewall, or highly customized operating systems.
Since Nmap isn't foolproof, it's wise to validate uncertain OS guesses with other checks:
- Run a version scan to fingerprint active services and link it to probable OS’.
- Manually grab banners from open ports to decipher OS or version details.
- Inspect traffic with Wireshark for behavioral clues about the OS.
Why Is This Useful
Having precise and reliable operating system detection provides immense value for a wide range of security and IT operations. In penetration tests, known OS details make you more effective in preparing exploits and payloads.
For network reconnaissance, accurate OS intelligence enables red teams to model environments and tailor attacks more successfully.
Precise OS detection is invaluable not just for penetration testers but also for network and system administrators.
For network admins, real-time data from Nmap adds a layer of verification that's especially useful during audits to ensure compliance with regulations like GDPR. System administrators benefit as accurate OS information aids in efficient troubleshooting.
DevOps and cloud engineers find this data crucial for performance tuning and automated deployments in their environments.
Again, real-time information from Nmap complements existing knowledge, enabling these professionals to make informed decisions.
See Some Of Our Other Nmap Articles
How to Use Nmap to Scan a Network: A Step-by-Step Guide
The Top 10 Nmap Scripts to Unlock Network Security
How to Install Nmap on Ubuntu: A Comprehensive Guide
Conclusion
As you can see, Nmap's OS detection features are incredibly useful in various scenarios. You should now have a clearer understanding of Nmap's capabilities for identifying operating systems.
We've introduced you to various commands for performing these detections and provided a thorough overview of how Nmap determines the OS of a target.
Armed with this knowledge, you're now well-equipped to use Nmap for OS detection in different contexts—penetration testing, maintaining a network inventory, or troubleshooting issues. This will enable you to interpret better and apply Nmap's OS detection features to suit your specific needs.
Ready to master the ins and outs of Nmap? Purchase our Nmap Course Bundle below, on sale now. And if you're looking to propel your cyber security career forward, join the StationX Master's Program today.
This Nmap Course Bundle includes:
- The Complete Nmap Ethical Hacking Course
- What is Nmap: How to Use Nmap for Penetration Testing
- Penetration Testing Training for Beginners




