Easily, the most frequently asked question we receive at StationX is, “How do I become a penetration tester?”
You may already know that it’s an exciting, well-paying, and in-demand career. Or, you may only have recently piqued an interest in hacking for a living. Either way, without some guidance, knowing where to start can be very difficult.
At StationX, we have trained over 500,000 students in cyber security. Now, we’ve assembled this epic guide on how to become a penetration tester to help you on your pentesting career journey.
This penetration tester roadmap will walk you through the hard and soft skills needed for this job, how to get training, what professional certifications to pursue, how to get a mentor and prepare you for interviews.
By the end, you will have all the tools and knowledge you need to start your journey toward an exciting and rewarding career as a penetration tester.
- What Is a Penetration Tester?
- What Does a Penetration Tester Do?
- Job and Salary Prospects for Penetration Testers
- Is Becoming a Penetration Tester Right for Me?
- Find a Penetration Tester Mentor and Connect With People
- Identify the Capability Gap Between You and a Penetration Tester
- Gain the Skills & Qualifications Needed to Be a Penetration Tester
- Gain Practical Hands-On Experience in Penetration Testing and Cyber Security
- Apply for Penetration Testing Jobs
- To Sum Up
- Frequently Asked Questions
What Is a Penetration Tester?
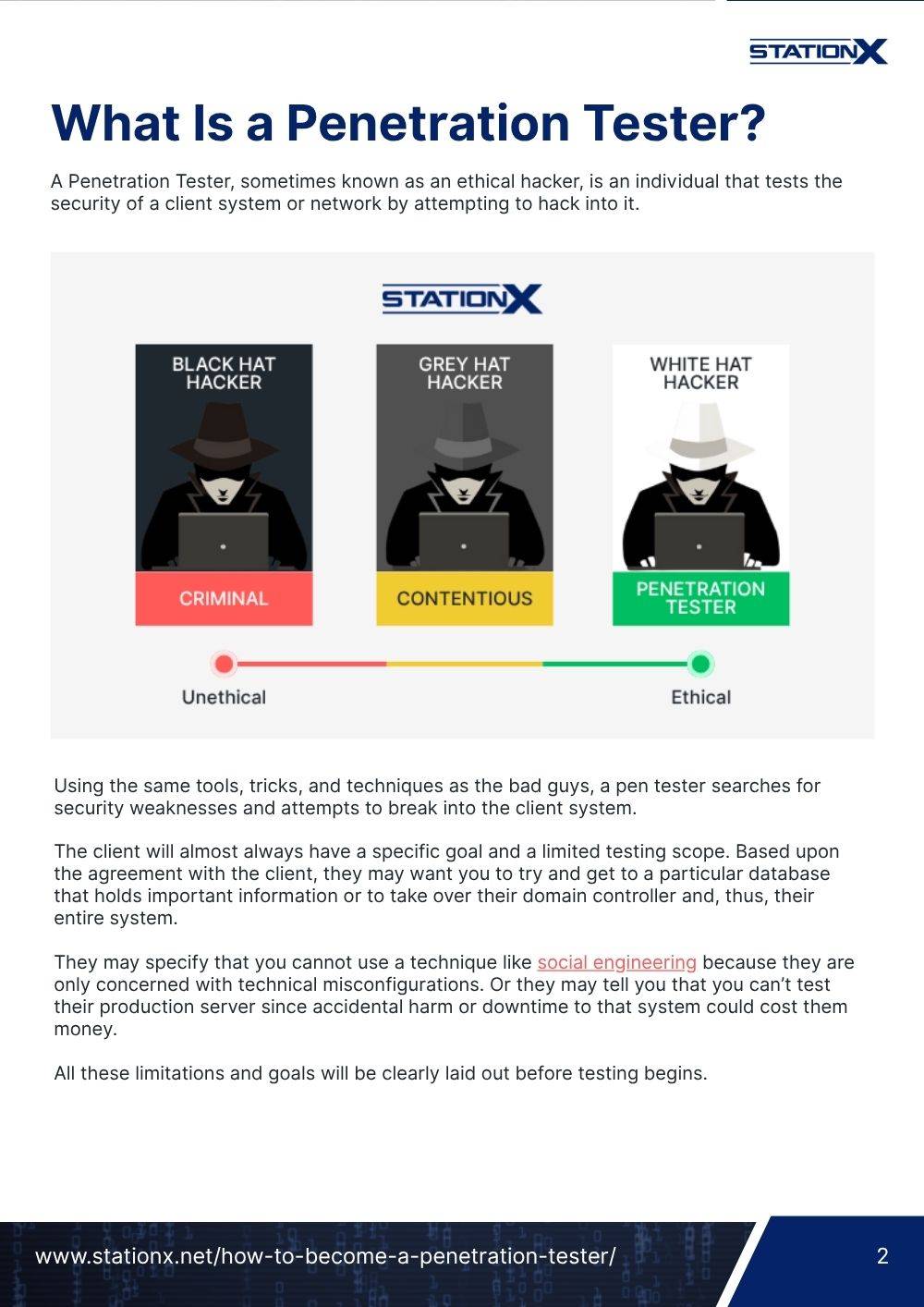
A Penetration Tester, sometimes known as an ethical hacker, is an individual that tests the security of a client system or network by attempting to hack into it.

Using the same tools, tricks, and techniques as the bad guys, a pen tester searches for security weaknesses and attempts to break into the client system.
The client will almost always have a specific goal and a limited testing scope. Based upon the agreement with the client, they may want you to try and get to a particular database that holds important information or to take over their domain controller and, thus, their entire system.
They may specify that you cannot use a technique like social engineering because they are only concerned with technical misconfigurations. Or they may tell you that you can’t test their production server since accidental harm or downtime to that system could cost them money.
All these limitations and goals will be clearly laid out before testing begins.
There are two major differences between an ethical hacker and a criminal hacker.
- Firstly, the ethical hacker has a client’s written permission to hack their network, often working within a permitted scope of testing (such as certain parts of a network being off-limits or banning certain types of attacks that may damage the company’s uptime).
- The second difference is a criminal hacker will often attempt something destructive, such as stealing valuable information like intellectual property or passwords, releasing malware or ransomware, or taking down the system and making it unusable. An ethical hacker stops before that point and assembles an audit report for the client.
- The differences between ethical and criminal hackers are addressed further in our "What Is a Red Hat Hacker?" article.
An audit report is what the client is after: A clear summary of the security weaknesses, how they can be exploited, and most importantly, how they can be remediated.
If you are already familiar with the roles, salaries, and specifics of the career, you can jump straight to Steps to Becoming a Penetration Tester.
Where Does a Penetration Tester Fit Into the Cyber Security Industry?
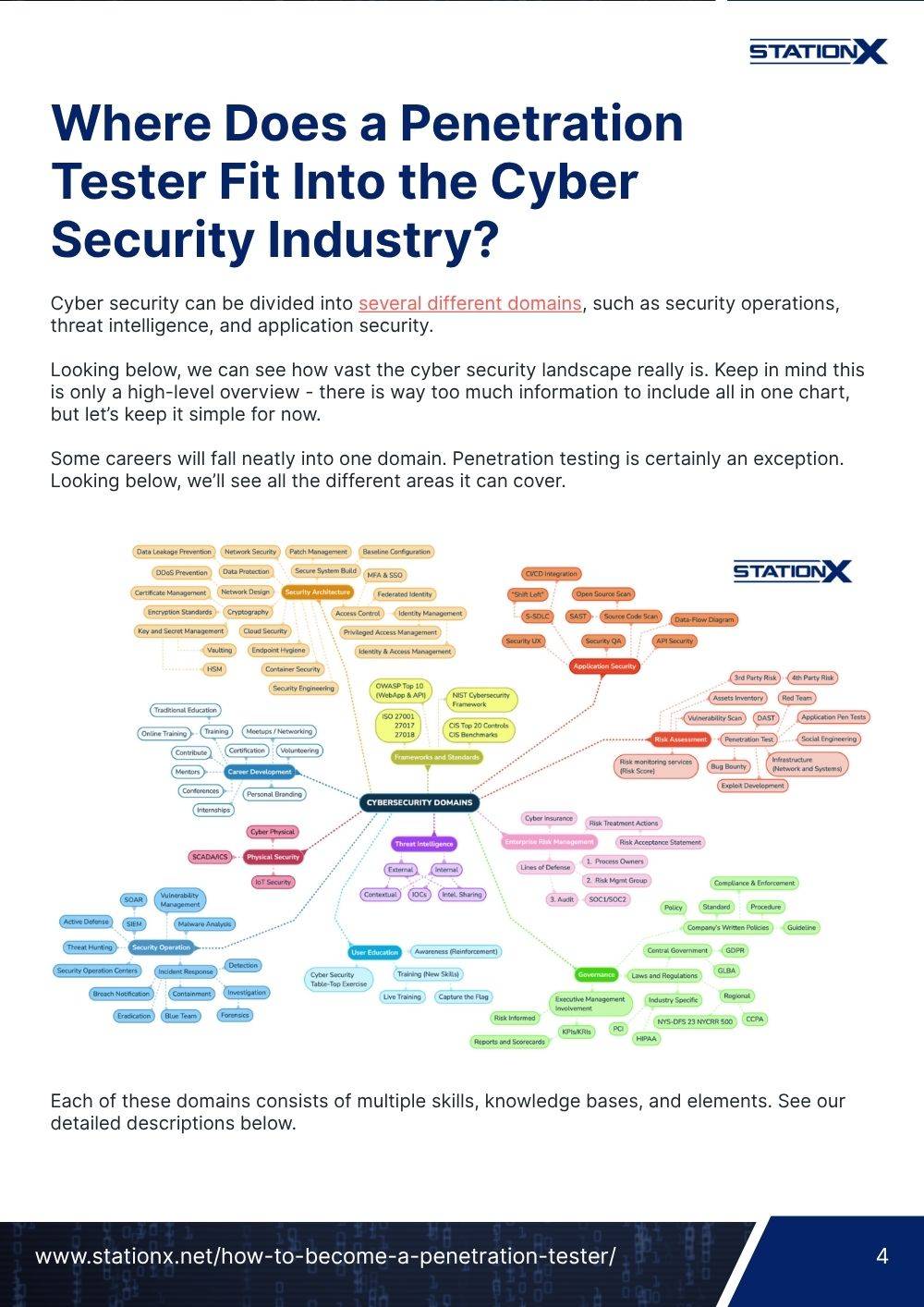
Cyber security can be divided into several different domains, such as security operations, threat intelligence, and application security.
Looking below, we can see how vast the cyber security landscape really is. Keep in mind this is only a high-level overview - there is way too much information to include all in one chart, but let’s keep it simple for now.
Some careers will fall neatly into one domain. Penetration testing is certainly an exception. Looking below, we’ll see all the different areas it can cover.

Each of these domains consists of multiple skills, knowledge bases, and elements. See our detailed descriptions below.
Security Architecture
Security architecture is a comprehensive security design that considers both the requirements and potential hazards present in a particular situation or environment. Additionally, it details where and when to implement security controls.
- Network Security: Assuring the confidentiality, integrity, and availability (referred to as the CIA Triad) of a network or system. Penetration testers will attempt to counterman the protections clients and vendors put into place to keep the CIA Triad in place.
- Patch Management: Ensuring all the latest updates and security fixes are in place on systems and programs. Penetration testers often look for out-of-date systems and missing security patches to attack and gain a foothold on a system.
- Baseline Configuration: “A set of specifications for a system, or Configuration Item (CI) within a system, that has been formally reviewed and agreed on at a given point in time, and which can be changed only through change control procedures. The baseline configuration is used as a basis for future builds, releases, and/or changes.” (NIST SP 800-128 under Baseline Configuration). Pentesters will test the security of baseline configurations and help create one that is more secure for the client.
- DDoS Protection: DDoS, or Distributed Denial of Service, is an attack where a system is flooded with malicious junk data, usually ping requests, to slow the service for legitimate users. The goal is to make the system unusable or crash due to its inability to manage the flood of requests. These attacks are often performed through botnets (a vast network of infected and enslaved computers managed by a single hacker). Pentesters may be asked to perform a controlled simulation to test a client’s ability to handle such an attack.
- Secure System Build: The design and implementation of a “hardened” network, software, machine instance, or other infrastructure. A penetration test's purpose is to audit a system's security and assist clients in closing holes in their security.
- Certificate Management: Monitoring, enabling, and executing digital SSL certificates are all parts of certificate administration. It is essential to the continued operation, encryption, and security of client-server connections.
- Cryptography: The use of complex math to obfuscate digital communication or documents and make them unreadable by anyone other than the intended recipients. The method is referred to as “encryption.” Any time you require a password to read a document or see the little padlock icon in your web browser's URL address bar, encryption is used to secure the information. Pen testers will use a variety of tools to try and brute force or bypass this encryption.
- Access Control: By validating various login credentials, such as usernames and passwords, PINs, biometric scans, and security tokens, “access control” identifies users. Pentesters will attempt to circumvent access controls to gain access to systems.
- Key and Secret Management: Key and secret management is the safe and easy storing of API keys, passwords, certificates, and other private information. Use it to manage, access, and audit information meant to be kept secret.
- Cloud Security: Cloud is currently the fastest-growing networking technology. Public cloud systems (such as Amazon Web Services (AWS), Microsoft Azure, and Google Cloud) and private cloud systems (such as those offered by Oracle and VMWare) are replacing traditional physical on-premises systems due to their low startup costs and ability to quickly expand and decrease resources as needed. The growing popularity of cloud-based systems has made them an attractive target for hackers and bad actors. Pen testers have unique methods to test and protect these systems.
- Identity and Access Management: “Identity management (IdM), also known as identity and access management (IAM), ensures that authorized people – and only authorized people – have access to the technology resources they need to perform their job functions.” (VMWare) Pen Testers see if they can beat identity management by forging/assuming the necessary identity, creating a new one with authorization, or bypassing it entirely.
Application Security
The process of developing and testing application security features to prevent vulnerabilities and defend against attacks.
- Source Code Scan: When performing a “white-box test,” penetration testers are given access to internal information not available to the public, including the source code of the systems and software they are testing. This allows them to review the code and more efficiently look for security vulnerabilities resulting from mistakes in the programming.
- API Security: Application Programming Interface (API) is the interface between software and a user. Most Software-as-a-Service (such as Google Maps and Twitter) are considered APIs. Some companies create public APIs that programmers can call back to and use in their software, such as facial or voice recognition systems. APIs have become a common part of web app pentesting.
Frameworks and Standards
A set of rules, recommendations, and best practices for controlling hazards in the digital sphere. Security goals, such as preventing unauthorized system access, are often matched with controls, such as proper password policies, etc.
- OWASP Top 10: A reference standard for the most critical web application security risks. Ethical hackers will use this standard as a reference guide to test a client’s system.
- NIST Cyber Security Framework: A set of best practices and recommendations for cyber security from the National Institute of Standards and Technology.
Physical Security
Physical Security limits access to areas where data and system controls are located. Fences, gates, security personnel, cameras, RFID badges, locks, etc., can keep out cyber criminals who wish to get on-premises and access data/devices directly.
- SCADA/ICS: Supervisory Control and Data Acquisition / Industrial Control Systems, such as those used in power plants, manufacturing, water treatment, etc. Attacks on these systems have become a terrifying favorite among nation-states and must be secured.
- IoT Security: The testing and security of Internet of Things (IoT) devices such as “smart home” systems. IoT devices are notoriously insecure, many lacking proper encryption and security controls or using very simple default passwords. Penetration testers will test the security of these systems and attempt to use them as a springboard into other client systems.
User Education
Educating end-users on cyber security practices and training individuals in any of the cyber security domains, such as ethical hacking, cyber forensics, and malware analysis.
- Cyber Security Table-Top Exercise: Meetings used to walk through security incidents, how to prepare for them, and how to respond when they occur. Usually the domain of the defensive security team, this can be done as part of the pentest debrief or as a stand-in for systems too sensitive to risk active testing.
Governance
Establishing a system for cybersecurity governance guarantees that a company's security programs align with its business goals, adhere to rules and regulations, and meet goals for managing security and risk.
- Compliance and Enforcement: Some countries require private companies to perform a penetration test as part of legal compliance for particular industries or systems, often when sensitive information is involved, such as credit cards and medical personal identifiable information (PII).
Common Job Titles for Penetration Testers
Some terms to look out for when seeking a pentesting position include
- Pentester/Penetration Tester
- Junior Penetration Tester
- Penetration Tester Trainee
- Senior Penetration Tester
- Penetration Tester Team Lead
- Ethical Hacker
- White Hat Hacker
- Red Teamer
- Vulnerability Tester
- Security Tester
- Vulnerability Assessor/Vulnerability Assessment Professional
- Application/Network Security Consultant
- Application Security Analyst
- Application Security Architect
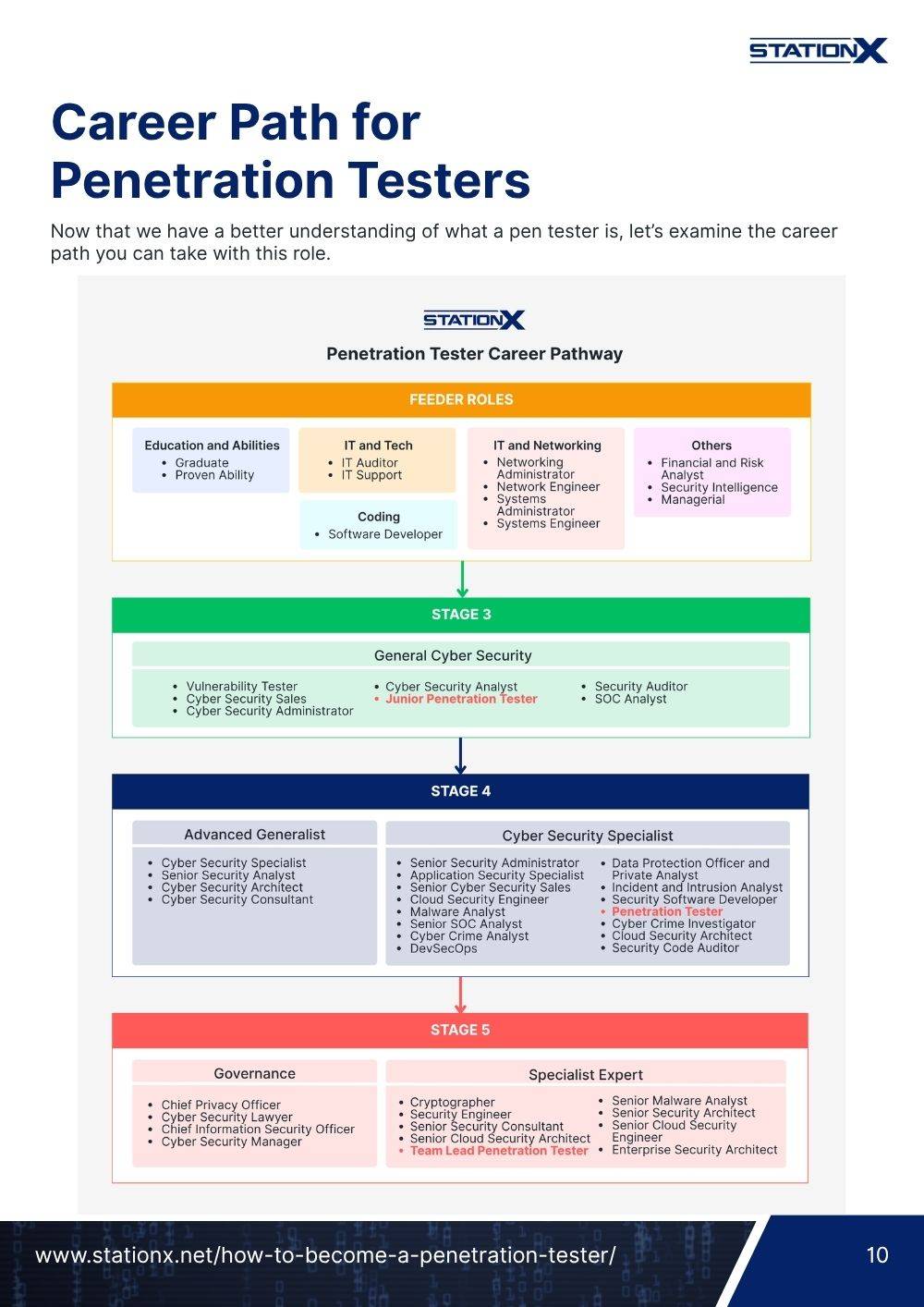
Career Path for Penetration Testers
Now that we have a better understanding of what a pen tester is, let’s examine the career path you can take with this role.

Feeder roles can be considered entry-level jobs that are easier to attain without previous experience but can still lead to a cyber security career. They provide enough industry experience and exposure to make upward mobility to more complex positions easier. Often, you can begin requesting security-related tasks or shadow someone working in the security department as a launching pad to your ideal career. A quick overview of the different feeder roles shown above:
- Support Desk is a common entry point for IT professionals who troubleshoot employee or customer desktops, phones, and other systems.
- IT Roles can include anything related to networking and systems administration. You might assist the network administrator, roll out new hardware to staff, set up switches and network devices, etc.
- Systems Administrator is a bit more technical than the IT roles, such as setting firewall rules, managing user accounts in Active Directory, etc. Several entry-level roles will provide this hands-on training.
- Graduates from college or university programs can get an entry-level position based on their degree.
- Internships can offer hands-on experience and training and may lead to a position within the organization.
- Proven Ability of your skillset through professional certifications, involvement in the infosec community (through blogs/GitHub/YouTube/etc.), competitive CTF (Capture The Flag) events, and more can get you noticed by employers.
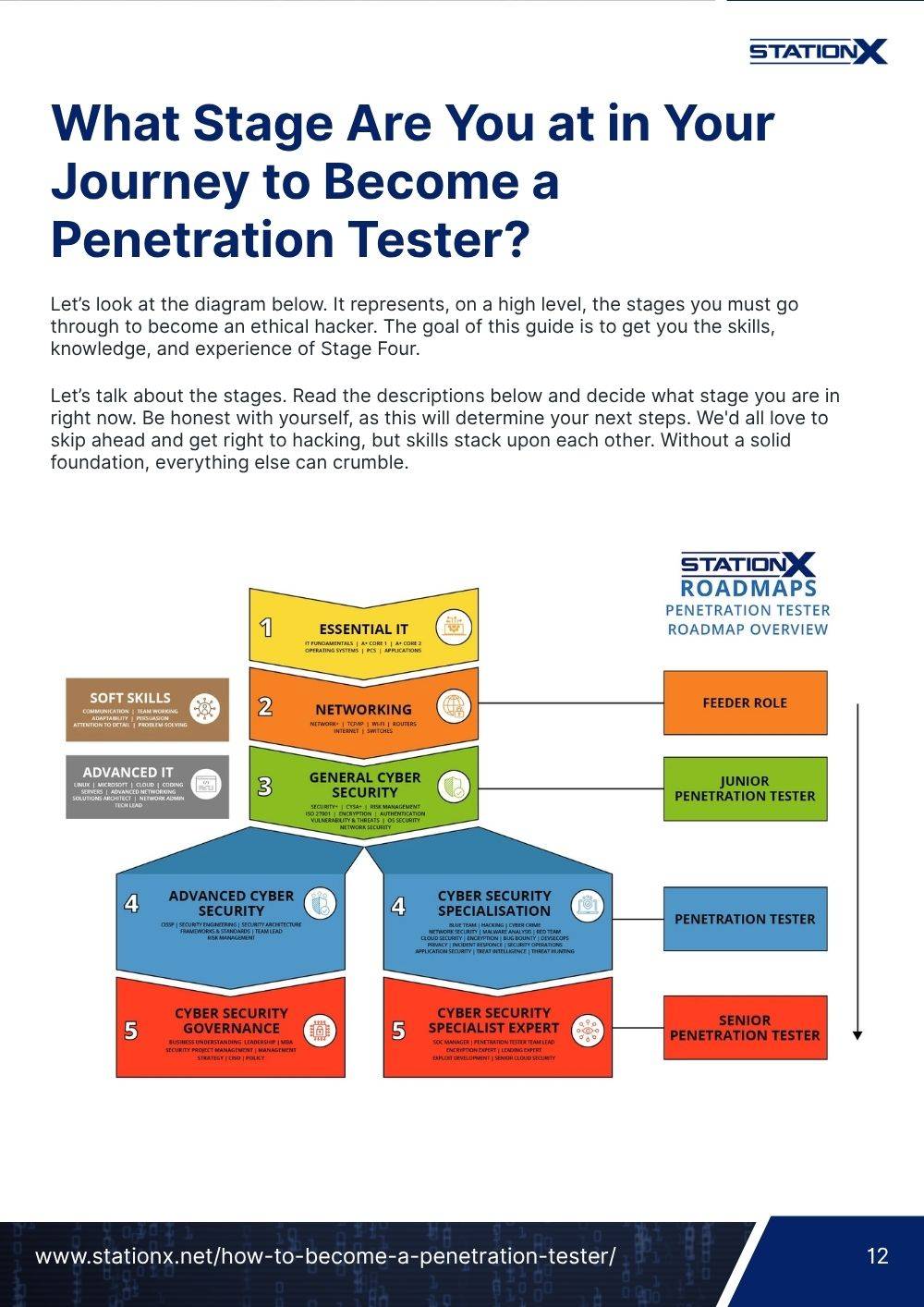
What Stage Are You at in Your Journey to Become a Penetration Tester?
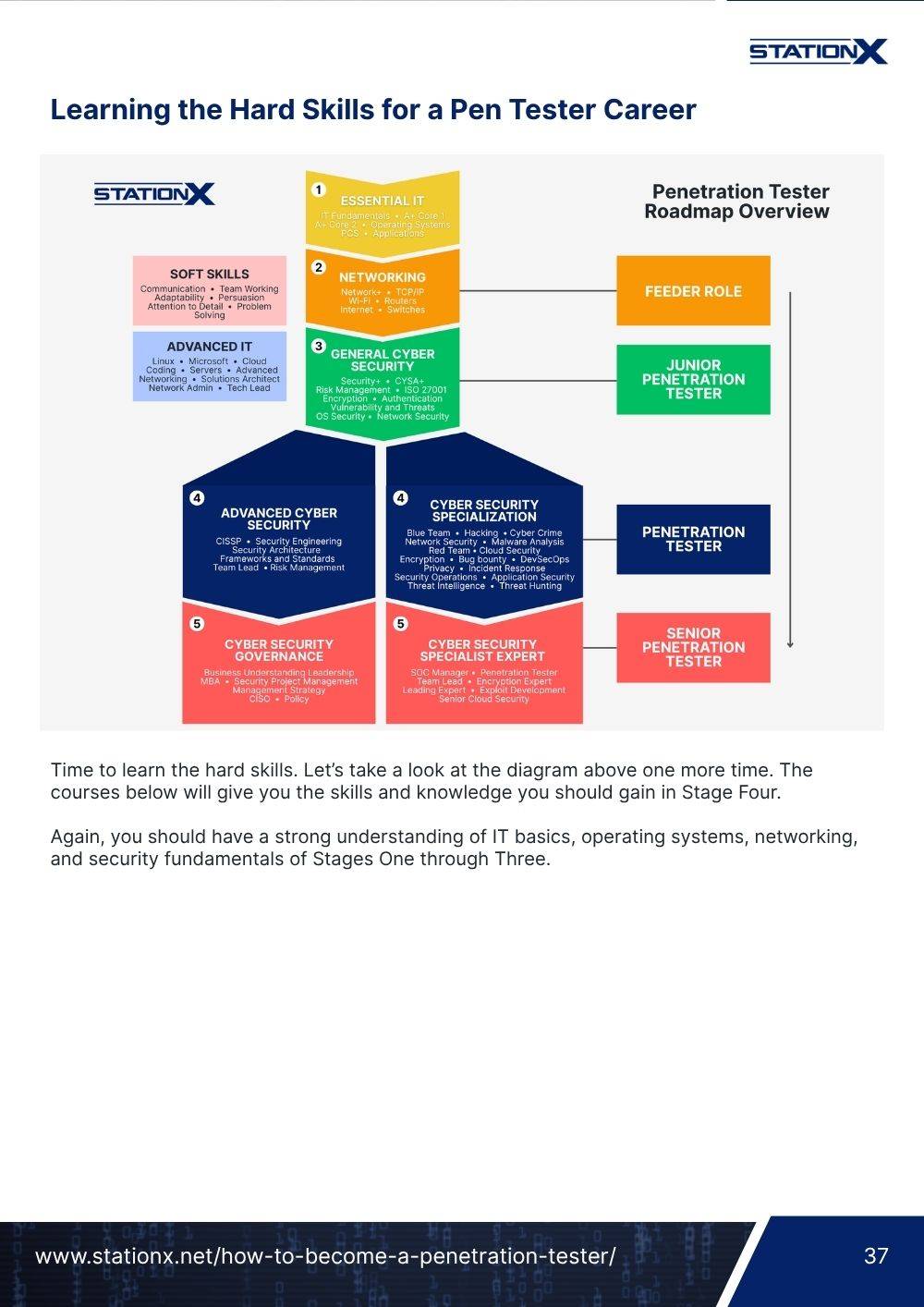
Let’s look at the diagram below. It represents, on a high level, the stages you must go through to become an ethical hacker. The goal of this guide is to get you the skills, knowledge, and experience of Stage Four.
Let’s talk about the stages. Read the descriptions below and decide what stage you are in right now. Be honest with yourself, as this will determine your next steps. We'd all love to skip ahead and get right to hacking, but skills stack upon each other. Without a solid foundation, everything else can crumble.

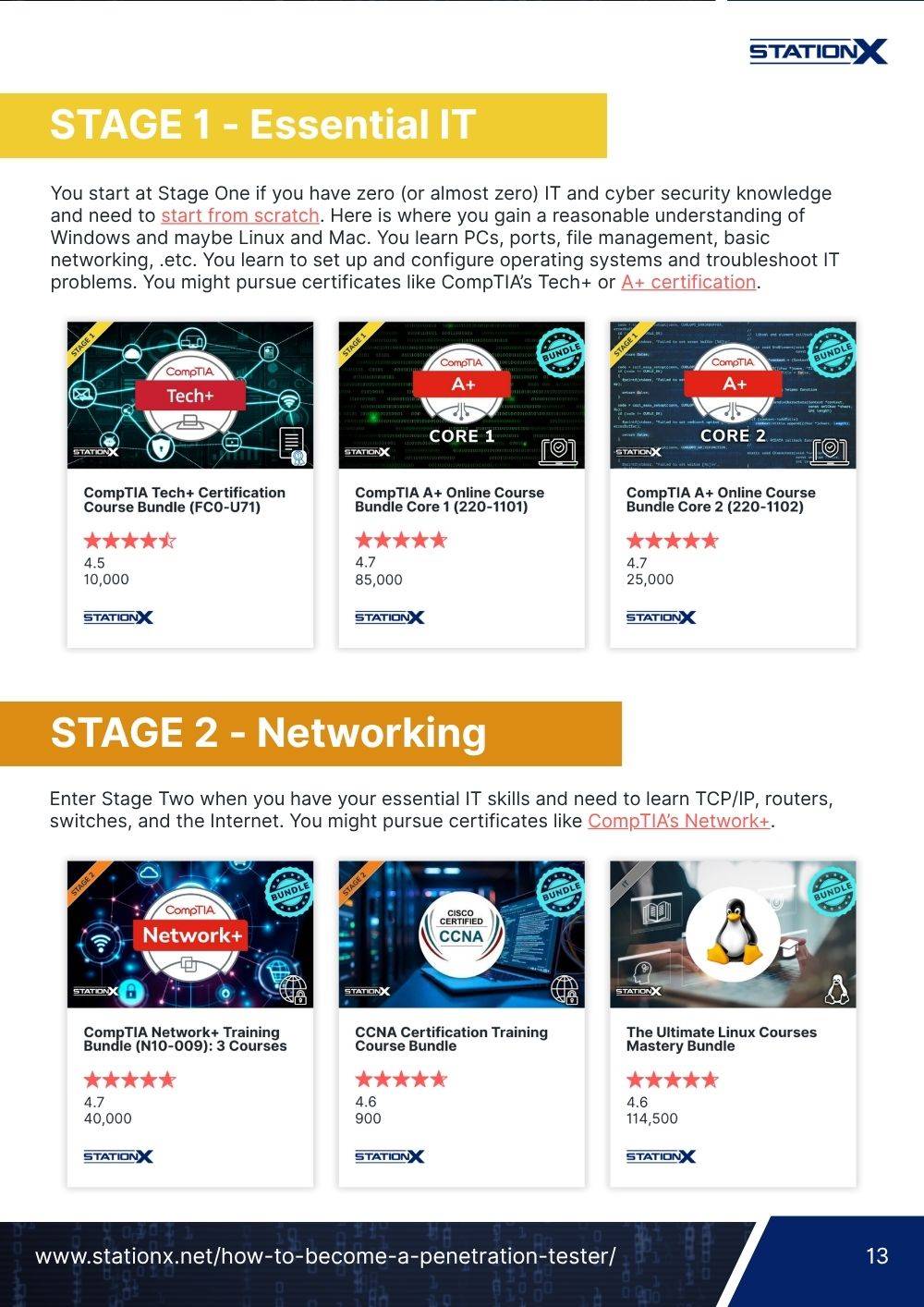
Stage 1 – Essential IT
You start at Stage One if you have zero (or almost zero) IT and cyber security knowledge and need to start from scratch. Here is where you gain a reasonable understanding of Windows and maybe Linux and Mac. You learn PCs, ports, file management, basic networking, .etc. You learn to set up and configure operating systems and troubleshoot IT problems. You might pursue certificates like CompTIA’s Tech+ or A+ certification.
Stage 2 - Networking
Enter Stage Two when you have your essential IT skills and need to learn TCP/IP, routers, switches, and the Internet. You might pursue certificates like CompTIA’s Network+.
Stage 3 - General Cyber Security
Enter Stage Three when you have experience working with all the previously mentioned topics and have good experience with IT, networking, and applications. You might hold Tech+, A+, or a technology degree, or have worked in IT support.
At the end of Stage Three, you will have knowledge/experience of topics like encryption, authentication, threats and vulnerabilities, basic hacking, OS security, .etc. You might have qualifications already, like CompTIA’s Security+, CEH, or ISC2’s SSCP.
Then you would be ready for a junior penetration tester role.
If you’re not at Stage Three yet, don’t worry. Consider some of our fundamental courses to get up to speed, such as CompTIA A+ Core 1 and Core 2, Network+, and Security+, all listed above. If you’re ready to start Stage Four, keep reading.
Stage 4 - Cyber Security Specialization - Penetration Tester
After completing Stage Three, you move towards gaining a deeper knowledge of penetration testing and hacking. Here you may choose to specialize in an area of penetration tesing, like web apps, mobile, red team, and so on. You might pursue certificates like
- OSCP – Offensive Security Certified Professional
- GPEN – GIAC Certified Penetration Tester
- GWAPT – GIAC Web Application Penetration Tester
Stage 5 - Cyber Security Specialization - Senior Penetration Tester
It’s time for Stage Five when you have five+ years of working as a pen tester and want to become an expert in a specialist area. For example, you are a penetration tester who wants to move into reverse engineering and create custom exploits. You might pursue certificates like
- CCSAS – CREST Certified Simulated Attack Specialist
- OSCE3 – Offensive Security Certified Expert 3
- OSWE – Offensive Security Web Expert
What Does a Penetration Tester Do?
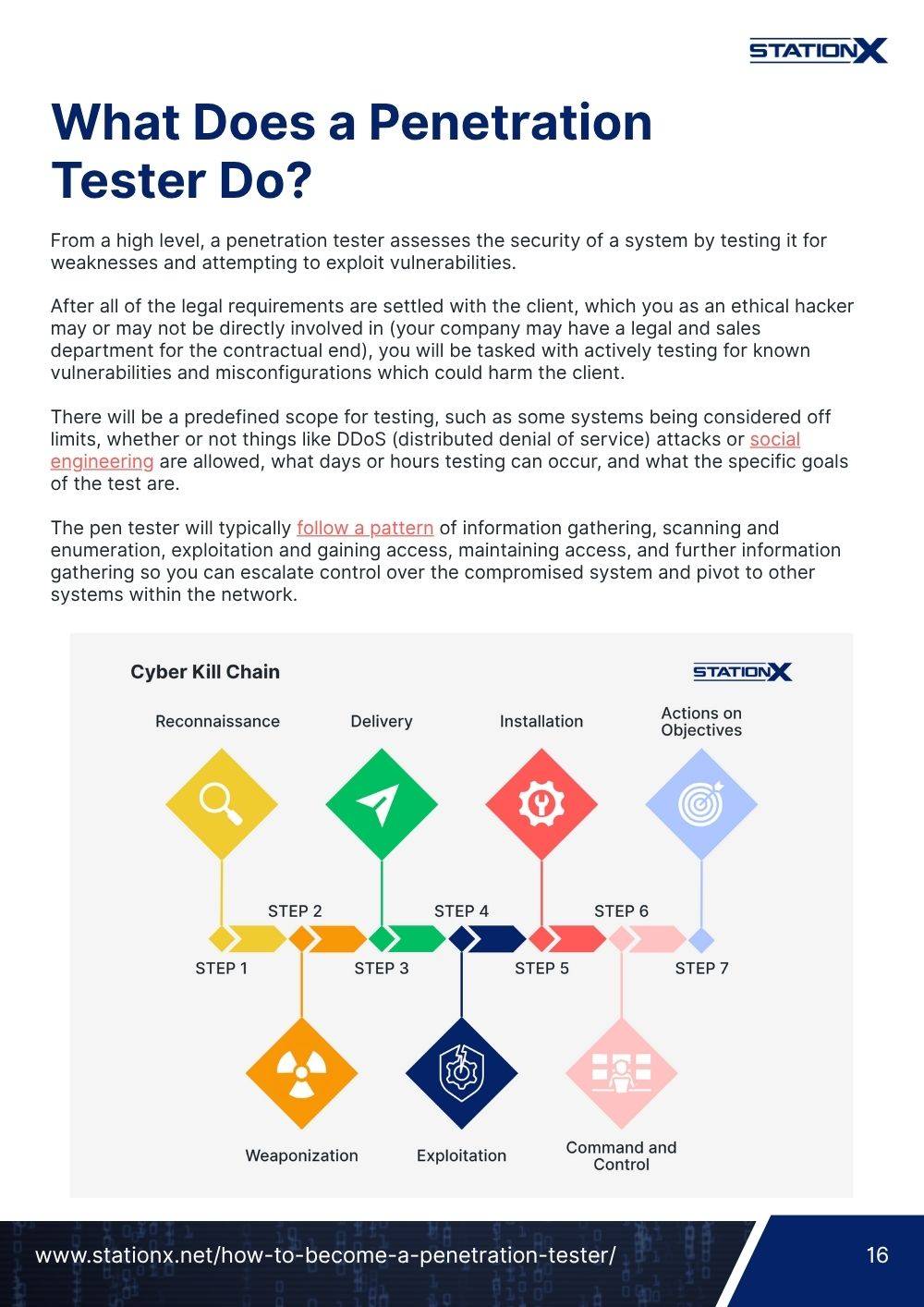
From a high level, a penetration tester assesses the security of a system by testing it for weaknesses and attempting to exploit vulnerabilities.
After all of the legal requirements are settled with the client, which you as an ethical hacker may or may not be directly involved in (your company may have a legal and sales department for the contractual end), you will be tasked with actively testing for known vulnerabilities and misconfigurations which could harm the client.
There will be a predefined scope for testing, such as some systems being considered off limits, whether or not things like DDoS (distributed denial of service) attacks or social engineering are allowed, what days or hours testing can occur, and what the specific goals of the test are.
The pen tester will typically follow a pattern of information gathering, scanning and enumeration, exploitation and gaining access, maintaining access, and further information gathering so you can escalate control over the compromised system and pivot to other systems within the network.

There are many types of penetration tests, including but not limited to external, internal, assumed breach, web app, physical, and wireless.
Once the testing phase is complete, the penetration tester will organize all of the documentation they’ve taken during the testing and assemble a report showing what the vulnerabilities were, how they were exploited, proof, the risk level to the client, and how their IT department can mitigate the threat.
Pen Tester Job Descriptions
Below, you will find some example job postings for junior and intermediate penetration tester positions from various countries. Consider common themes in the postings to see the skills and knowledge these employers are looking for. Click the listings to view the respective penetration tester job description.






Job and Salary Prospects for Penetration Testers
As with any career, the average salary can vary depending on the specifics of the role, the location you are working, and your individual experience. But let’s take some statistics from various sources to assemble a more complete picture.

According to ZipRecruiter, as of June 2025, the average annual salary of a penetration tester in the United States is $119,895 per year (averaging $58/hour).
“While ZipRecruiter is seeing annual salaries as high as $168,500 and as low as $22,500, the majority of Penetration Tester salaries currently range between $96,000 (25th percentile) to $141,000 (75th percentile) with top earners (90th percentile) making $158,500 annually across the United States.”
According to the book, “Hack the Cybersecurity Interview” by Ken Underhill, Christophe Foulon, and Tia Hopkins (Published July 2022):
“I’ve seen salaries as low as $76,000 and as high as $270,000+ for specialized public sector work. For a junior-level pentester, you can usually expect between $70,000 and $100,000…”
Payscale lists the average annual salary for a junior pentester at $70,000 USD.
Read "How Much Do Penetration Testers Make?" for a deep dive into this topic.
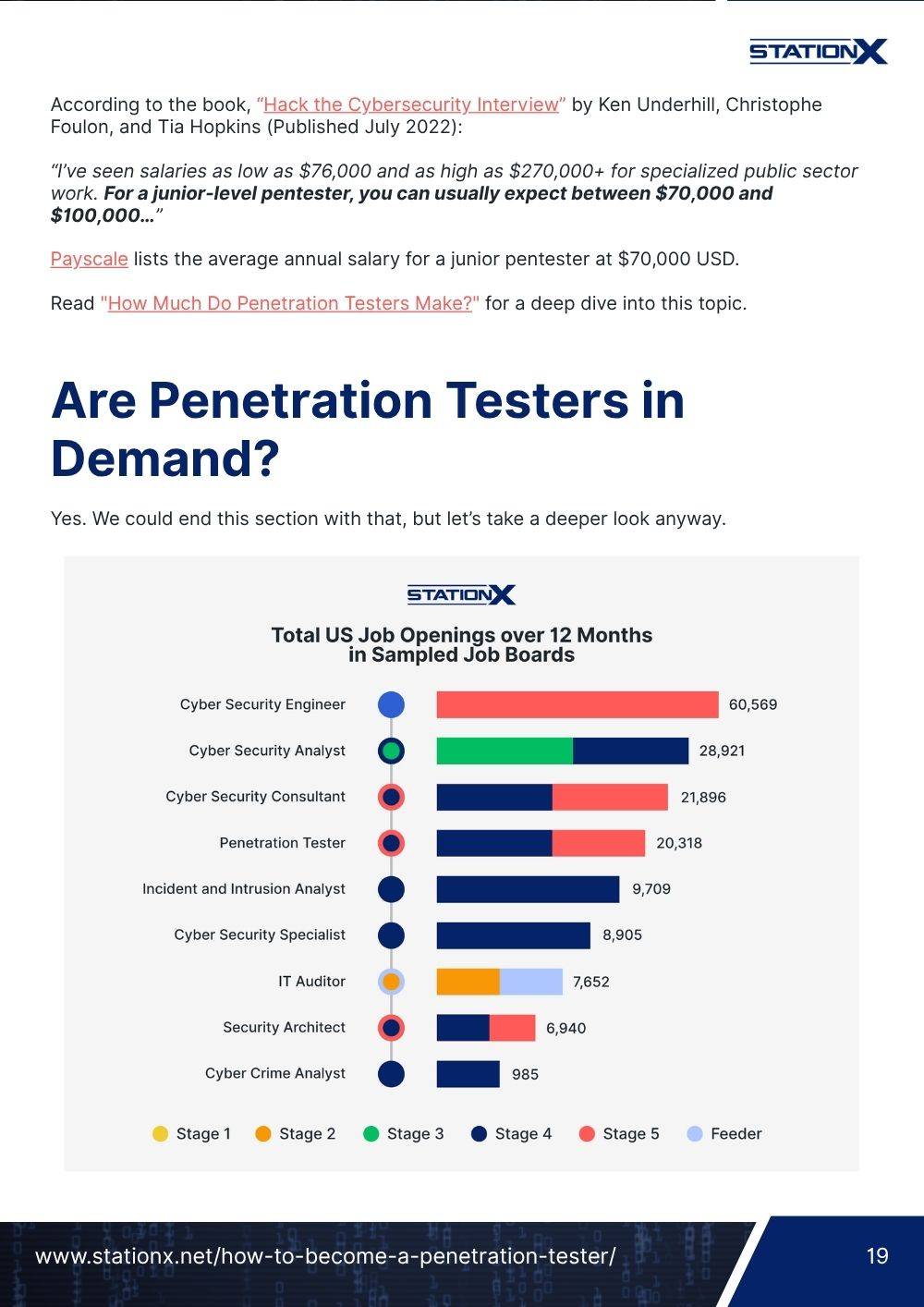
Are Penetration Testers in Demand?
Yes. We could end this section with that, but let’s take a deeper look anyway.

The phrase “junior penetration tester” on LinkedIn showed 29,453 positions available in the United States, 2,717 in the United Kingdom, and 868 in Canada.
According to Rob Sobers in his Varonis article, “157 Cybersecurity Statistics and Trends,” as of Sept 2024, there are nearly 470,000 job openings in the cyber security industry, and InfoSec positions like information security analysts are predicted to grow 35 percent by 2031.
A 2022 industry report projects that the global cyber security market is projected to grow to USD $345.4 billion by 2026.
Is There a Future in Penetration Testing?
Penetration testing is a field that will only grow in demand as companies and governments continue to face attacks from cyber criminals.
- The global cost of cybercrime reached over $9.5 trillion in 2024.
- Ransomware attacks in 2024 averaged $5.2 million to pay globally, with small businesses being extorted on average $50,000 to $250,000.
- Small businesses lose, on average, $500,000 - $2,000,000 per ransomware incident when considering downtime, recovery costs, and reputational damage.
- 51% of companies admit they are ill-equipped to respond to a cyber attack.
Similar studies, such as StationX's "Cybercrime Statistics (Shocking Trends You Must Know)," Forbes’ “Alarming Cyber Statistics for Mid-Year 2022 That You Need To Know,” and Comparitech’s “300+ Terrifying Cybercrime and Cyber security Statistics (2024 Edition),” show the need for cyber security auditors and pen testers is only growing.
All of us are part of a global economy completely reliant on the sustained functionality of our modern technology. Cybercriminals, terrorists, and enemy nations are aware of this.
A ransomware attack on a company could bankrupt it based on downtime alone. Attacking important infrastructure like a power plant could cripple a large part of a nation. Taking down a hospital’s network could quickly lead to fatalities. Thanks to global networking, breaches and infections aren’t isolated to one site.
In 2024, Change Healthcare, one of the largest healthcare payment processors in the U.S., was crippled by a ransomware attack that disrupted claims and billing services nationwide. The attack cost parent company UnitedHealth Group over $1 billion and exposed the data of up to 190 million individuals.
Becoming more reliant on this technology and moving more business to the digital realm creates a larger and more tempting attack surface for those threat actors with an agenda (financial, political, or otherwise).
The importance of penetration testing to secure these networks cannot be understated. That said, there is a factor we haven’t addressed yet. Technology is under constant development to assist and strengthen both the defender's and the attacker’s sides. As with any technology, the more the process can be automated, the easier it is to use and the more attractive it becomes.
We see the implementation of Artificial Intelligence in fields we’ve never considered in the past. We have seen A.I. generate artwork (much to the displeasure of artists and designers), write fiction, act as a knowledge resource, and be integrated into different security systems such as Microsoft Security Copilot.
From the defensive side, AI is actively used in malware analysis, threat hunting, and data loss prevention with tools like Kaspersky’s Endpoint Security, SentinelOne’s Singularity, and Zscaler Data Protection, respectively. See 10 Examples of AI in Cyber Security (Latest Research).
We cover how to utilize ChatGPT as an ethical hacker in our article "Unlock ChatGPT for Hacking: Jailbreaking Ethical Restrictions." It can be used to write malicious code, provide possible solutions when a pen tester is stuck, assist in writing social engineering campaigns, and more.
Morris II has been labeled the first worm designed to target GenAI systems through malicious self-replicating prompts. Instead of traditional code, the worm uses carefully crafted prompts to manipulate AI systems like Gemini Pro or ChatGPT.
The AI is tricked into including malicious instructions in its outputs, essentially "copying" the worm into new content. The result is both harmful output, like spamming and data theft, and propagation, as the content is sent to connected systems like email assistants.
We have also witnessed how worms like NotPetya and BadRabbit combined a common vulnerability with a penetration testing tool (EternalBlue and Mimikatz, for those interested) to fully automate their rampage to great effect. This did not require anything as complex as A.I.
With AI adoption by both attackers and defenders happening rapidly, the big frightening question is, "Will A.I. replace ethical hackers?"
We can’t dismiss the possibility completely. In our opinion, Artificial Intelligence will take a bigger role in cyber security, both for attackers and defenders, but the need for human pentesters will remain. Penetration testing and ethical hacking requires a certain level of creativity not yet met by A.I.
Much like the various vulnerability scanners available on the market, A.I. is likely to assist in basic enumeration and information gathering but will still require a knowledgeable human pen tester to prompt it and know what to do with the gathered information. We believe it will become an indispensable tool in a hacker's arsenal, but a tool nonetheless.
Is Becoming a Penetration Tester Right for Me?
We can’t tell you if being a penetration tester is a career you will enjoy. What we can do is discuss the personality traits that best suit the penetration tester job.
The key soft skills we discussed included analytical thinking, attention to detail, and problem-solving. Are you that type of person? If you enjoy puzzles, problem-solving, troubleshooting, and breaking down issues into smaller pieces to work through, this may be a career that inspires you.
We also discussed communication skills, collaboration, and honesty. It might seem odd that these are more emotional traits than analytical ones, yet they sit side-by-side with each other as important traits in this field. Why is that?
Holland Code Assessment for Ethical Hackers
This question was examined in the research paper “Exploring the Vocational Interests of Cybersecurity Competition Participants.” It’s an interesting read, but we’ll summarize a key finding.
The paper used “Holland’s RIASEC model” to determine personality types. It assumes six vocational personalities.
- Realistic
- Investigative
- Artistic
- Social
- Enterprising
- Conventional
After some research, the paper noted that,
“Cyber security competition participants score highest in the investigative, social, and artistic areas, which differs to some extent from other computer science-related groups. The social aspects of group competition and the creative aspects of cyber security problem solving may explain this difference.”
Cyber security's creative problem-solving aspects require more artistic traits than other computer science fields. This makes sense when you compare the role to that of a cloud architect or network administrator, which requires less “outside-the-box” style thinking.
A pen tester is also tasked with communicating their findings to individuals across a wide spectrum of technical knowledge, from executives who only know the basics of using the internet to IT administrators and network engineers who are expected to apply your suggested fixes. These are certainly social skills.
There are several sites online where you can take Holland’s RIASEC assessment to see your vocational code. Try a few and see if you return an ISA or IAS code.
Quick Self-Assessment: Are You Cut Out to Become a Pen Tester?
Take a look at your current job (if employed) or the courses you are taking (if still in school) and ask yourself, “What do I like and dislike about what I’m doing?” Now picture yourself in a penetration tester role. How many likes and dislikes overlap with this job as you imagine it?
This field is constantly changing, and you will need to keep up with it. It’s not difficult so much as it is a demand of dedication.
You must keep learning new technologies, techniques, systems, and vulnerabilities. There will be lots of very dull and sometimes poorly explained documentation you will need to read. And you may find yourself working odd hours if the client demands it.
If these notions scare you off, that’s perfectly fine. It just means that penetration tester may not be the field for you. If this all sounds up your alley, you may have found a calling.
Take our quiz below to see if penetration tester is the career path for you!

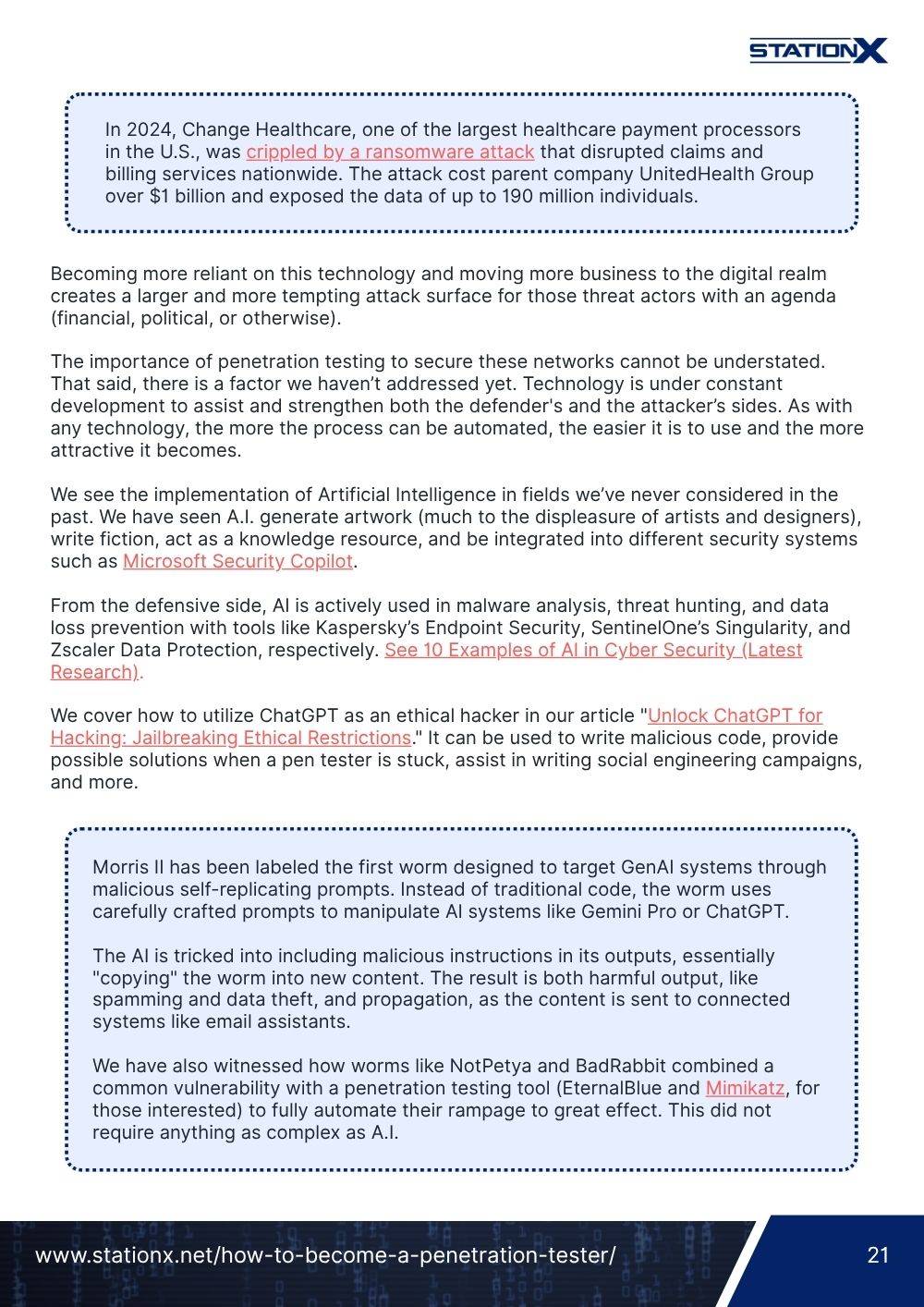
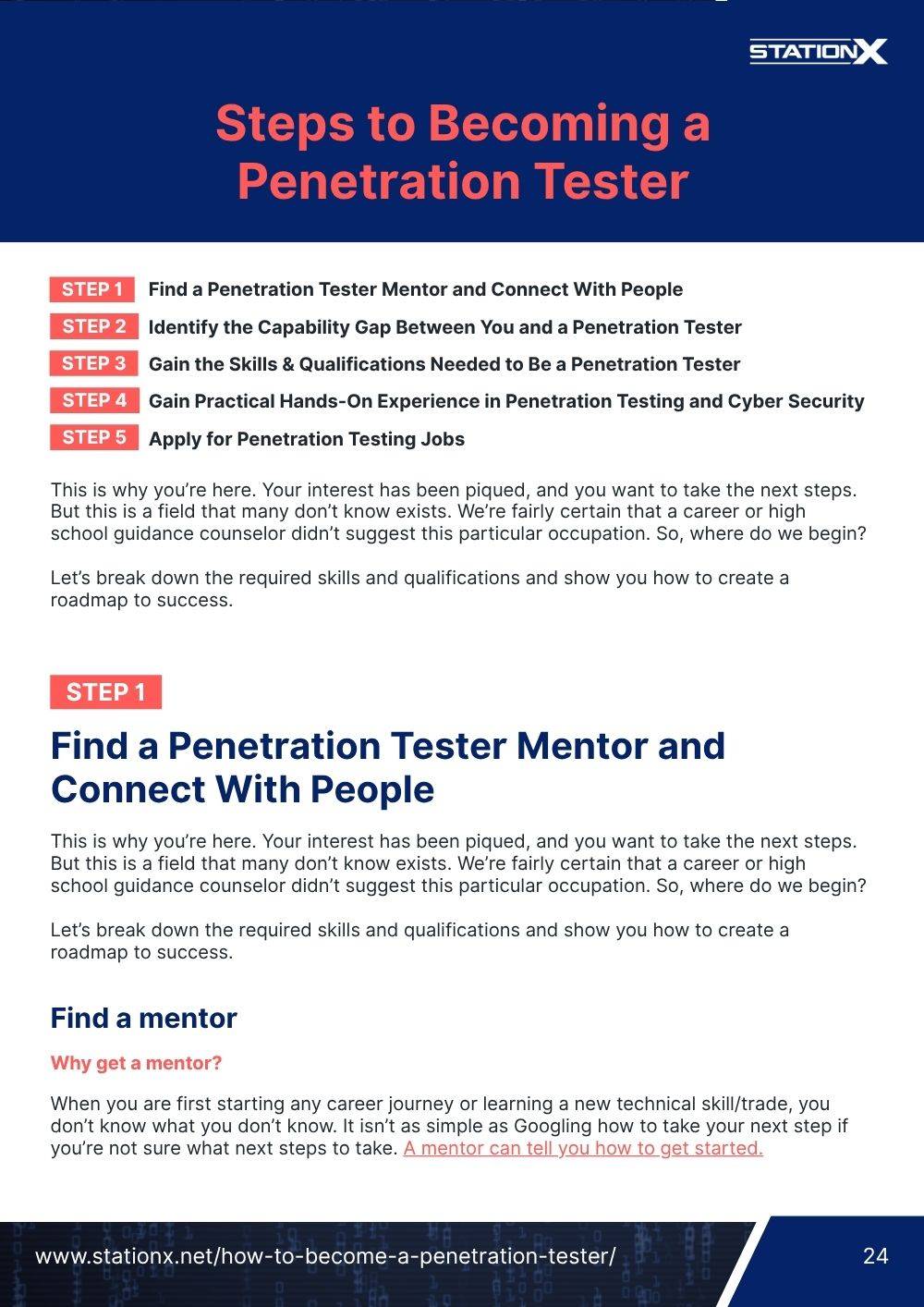
- Step 1 - Find a Penetration Tester Mentor and Connect With People
- Step 2 - Identify the Capability Gap Between You and a Penetration Tester
- Step 3 - Gain the Skills & Qualifications Needed to Be a Penetration Tester
- Step 4 - Gain Practical Hands-On Experience in Penetration Testing and Cyber Security
- Step 5 - Apply for Penetration Testing Jobs
This is why you’re here. Your interest has been piqued, and you want to take the next steps. But this is a field that many don’t know exists. We’re fairly certain that a career or high school guidance counselor didn’t suggest this particular occupation. So, where do we begin?
Let’s break down the required skills and qualifications and show you how to create a roadmap to success.

Find a Penetration Tester Mentor and Connect With People
Find a mentor
Why get a mentor?
When you are first starting any career journey or learning a new technical skill/trade, you don’t know what you don’t know. It isn’t as simple as Googling how to take your next step if you’re not sure what next steps to take. A mentor can tell you how to get started.
There are so many courses and certifications for penetration testing you can take, but some are not worth pursuing, while others are almost industry standards. A mentor can tell you which is which. They can tell you how to gain experience that you can show employers and how to make worthwhile connections in the industry.
A mentor isn’t just someone who will teach you the hard skills - though it’s great if you can find that person. A mentor can tell you what skills are in demand right now and offer advice on learning and studying these topics. They can tell you what worked for them and what didn’t, how they succeeded and why they failed, and what route they would take if they were starting over.
Joining the StationX Master’s Program gives you direct access to exactly the kind of mentorship you need to break into penetration testing. You won’t just get general advice—you’ll work one-on-one with experienced mentors who understand the industry and can guide you through your specific challenges and goals.
You’ll also gain access to private chat channels where you can speak directly with StationX experts, get personalized feedback, and ask for advice anytime you need it. Whether you’re trying to choose the right certification, build a study plan, or figure out how to land your first job, we’ve got your back.
The Master’s Program includes:
- Unlimited career mentorship via live chat
- A custom study roadmap reviewed by a StationX mentor
- Access to scheduled focus groups on topics like AI, defense, and hacking
- A supportive community of students, teaching assistants, and professionals
- Exclusive 1:1 sessions to tackle your career goals directly
If you’re serious about becoming a penetration tester, this is the kind of guidance that turns interest into a career.
Join a Mastermind Group
A Mastermind Group is a small, self-regulated group of like-minded people coming together to mutually help each other reach new levels of personal success.
The group will periodically meet to share ideas, create accountability, support each other, and grow to succeed. At StationX, you can join a mastermind group and meet as often as you want (though we recommend weekly) to assist each other in achieving your career and educational goals.
Why should you join a mastermind group?
They have been proven to help you establish good habits to achieve your goals and increase your learning retention rates.
Establishes systems of good habits to achieve goals
Increase your learning retention rates
Network With Other Penetration Testing Students in the StationX Community and Elsewhere
The benefits of networking cannot be overstated. Some people think of networking only as a way into a particular company, like having a friend on the inside to help you get hired. Networking is much more than that.
Building a network provides career support, advice, and new perspectives. It helps you reevaluate your skills and knowledge base. It also assists you in growing your personal brand and establishing a stronger professional name for yourself.
Everyone in your network is a resource library, and building one full of individuals who share a passion for cyber security means you gain access to a very niche source of information.
So how do you build a network?
You can join the StationX Community and connect with other students, experts, and junior professionals.
LinkedIn is an excellent platform to reach out to others, as some individuals clearly state that they want to connect with others in their field. Recruiters will almost always accept connection invitations. Many people post articles and blogs discussing their field of expertise; by responding to them on the subject, you can open a dialogue and build a connection.
You can connect with Nathan House, founder and CEO of StationX, and share his professional network. You can also follow StationX on LinkedIn.
Infosec Twitter is full of professionals who love to share insights, tips, and technologies. As an open platform, you can retweet and reply to these posts. Sharing your insights, struggles and successes can garner attention and help build your network. Be sure to follow Nathan House and StationX.
There are many industry events and meetups, both large and small, that happen all year round. See what is happening in your area. You can plan to travel to some of the larger conferences. Many of these also happen completely online (such as over Discord) due to Covid.
Our Member’s Section lists the top-recommended conferences to attend.

Identify the Capability Gap Between You and a Penetration Tester
Let’s talk about skills and capabilities. You are going to need to think about what skills and abilities you have that apply to this role and which need to be developed.
We’ll start by looking at possible specializations you may be interested in within pentesting, identifying your current skillset, and analyzing what you need to work on.
Find a Passion and Specialization
Pentesting is certainly a specialized role within cyber security, but you can still dive deeper and focus on particular areas if you choose. You will, of course, start as a generalist, and many continue to stay well-rounded in all areas of pentesting. Should you wish to specialize, you can consider:
You can also specialize in hacking Active Directory, WiFi, cloud infrastructures such as Azure and Amazon Web Services, SCADA/ICS systems, and more.
To see if something specific excites you as a specialty, look at
- The different courses available on StationX
- Job postings on CyberSecurityJobs.com
- The StationX blog
- The StationX YouTube Channel
- Any of the many great hacker and pentesting blogs/YouTube channels/podcasts out there (we recommend John Hammond’s YouTube, Darknet Diaries podcast, and TrustedSec blog)
- The areas highlighted on the domains map discussed earlier to see if something specific excites you
If you can’t decide yet, stay general for now.
You can also get to know the cyber security industry and what jobs are offered with this free career guide.
Identify Your Current Hard, Soft, and Transferable Capabilities
Time to take an inventory of the skills you currently possess and how they might be transferable to this new career.
Once you’ve taken a good hard look at what you have to offer in terms of hard skills (such as Linux or TCP/IP) and soft skills (like time management and report writing), it’s time to line them up against the skills you see listed on the kinds of job ads you want to apply for. Determine what is missing, and set a plan to fill in the gaps.
We’ve created a tool to help you with this task, but use whatever method works best for you so long as you can refer back to it and update as needed.
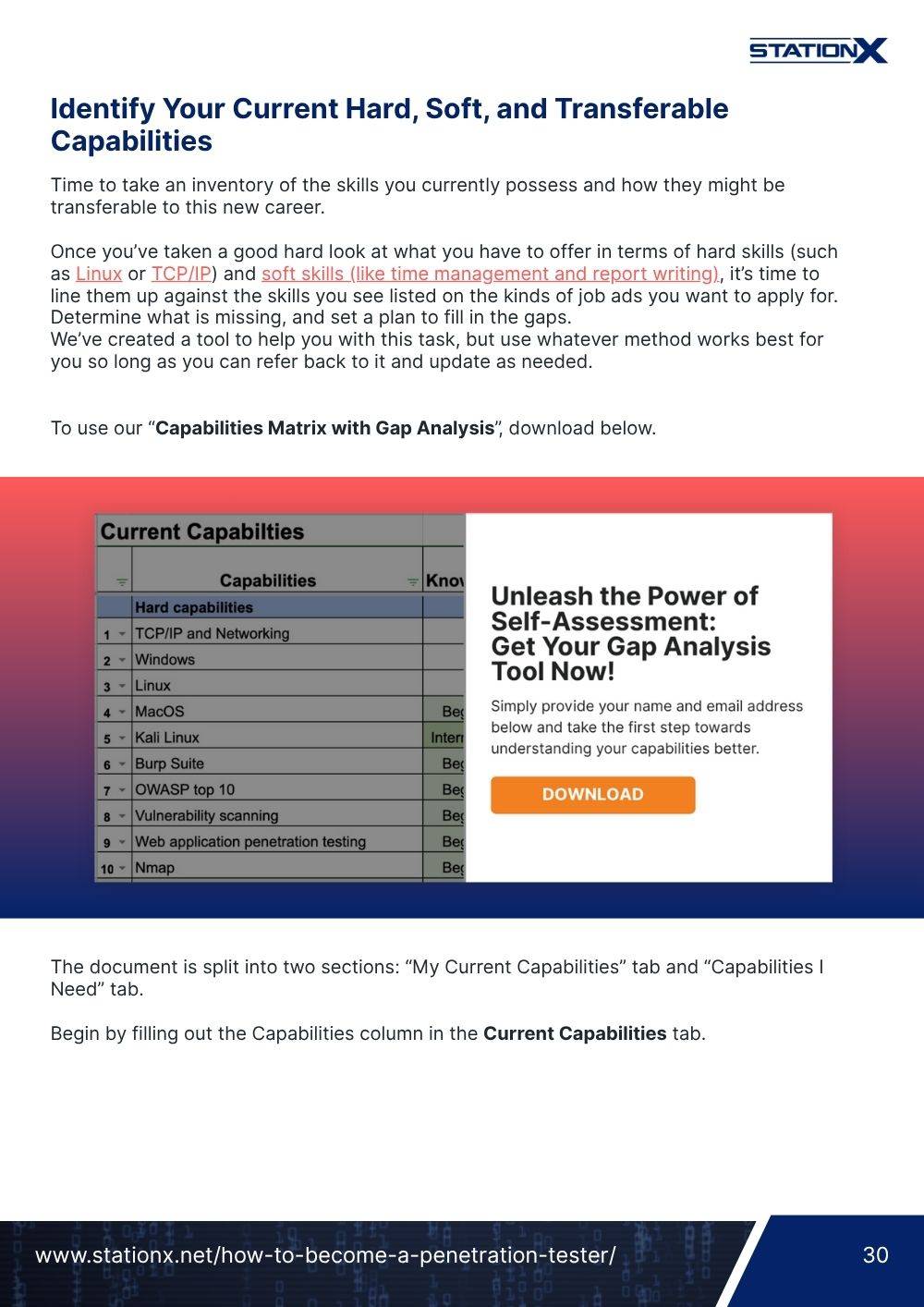
To use our “Capabilities Matrix with Gap Analysis”, provide your email and receive it free.
The document is split into two sections: “My Current Capabilities” tab and “Capabilities I Need” tab.
Begin by filling out the Capabilities column in the Current Capabilities tab.

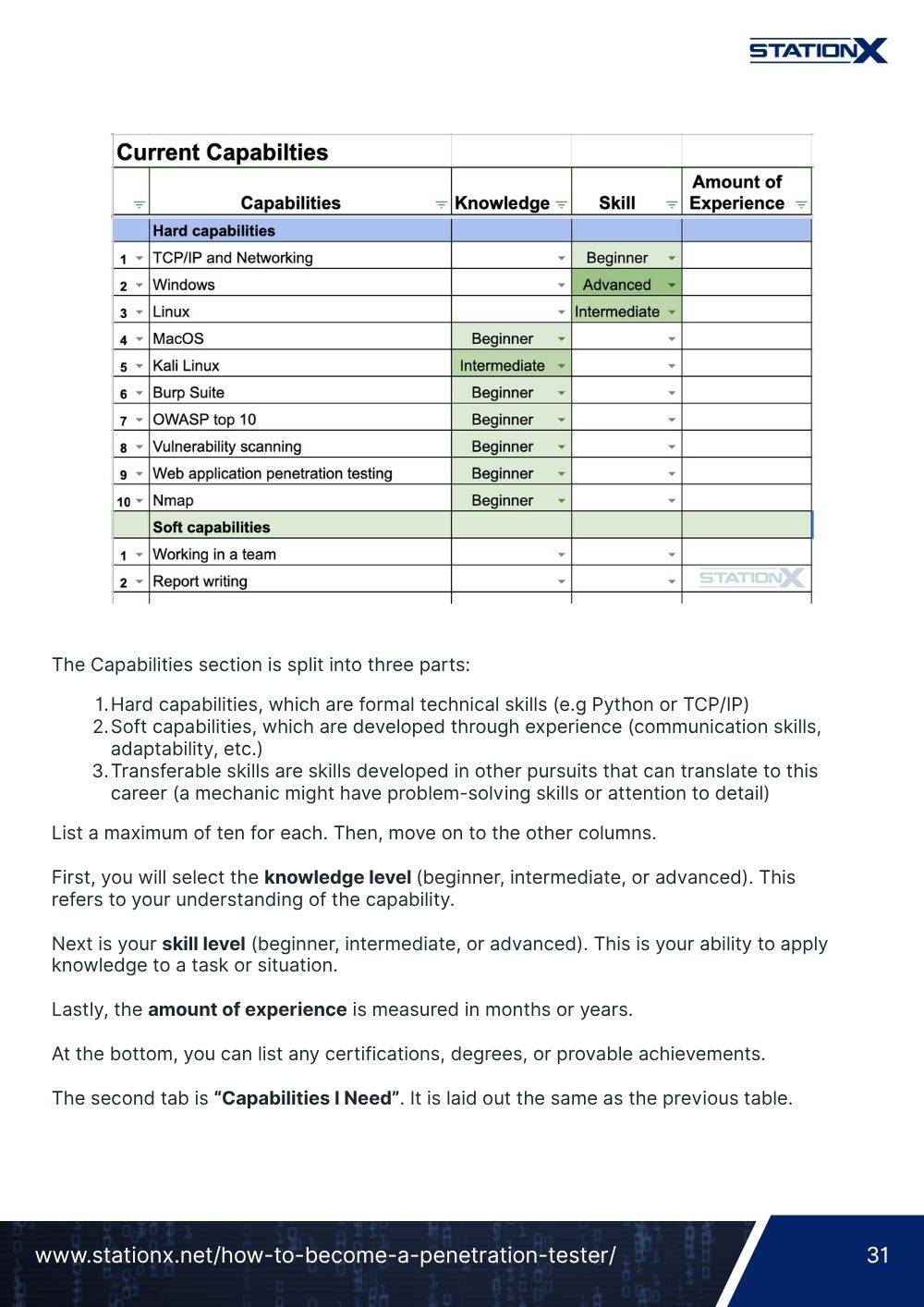
The Capabilities section is split into three parts:
- Hard capabilities, which are formal technical skills (e.g Python or TCP/IP)
- Soft capabilities, which are developed through experience (communication skills, adaptability, etc.)
- Transferable skills are skills developed in other pursuits that can translate to this career (a mechanic might have problem-solving skills or attention to detail)
List a maximum of ten for each. Then, move on to the other columns.
First, you will select the knowledge level (beginner, intermediate, or advanced). This refers to your understanding of the capability.
Next is your skill level (beginner, intermediate, or advanced). This is your ability to apply knowledge to a task or situation.
Lastly, the amount of experience is measured in months or years.
At the bottom, you can list any certifications, degrees, or provable achievements.
The second tab is “Capabilities I Need”. It is laid out the same as the previous table.

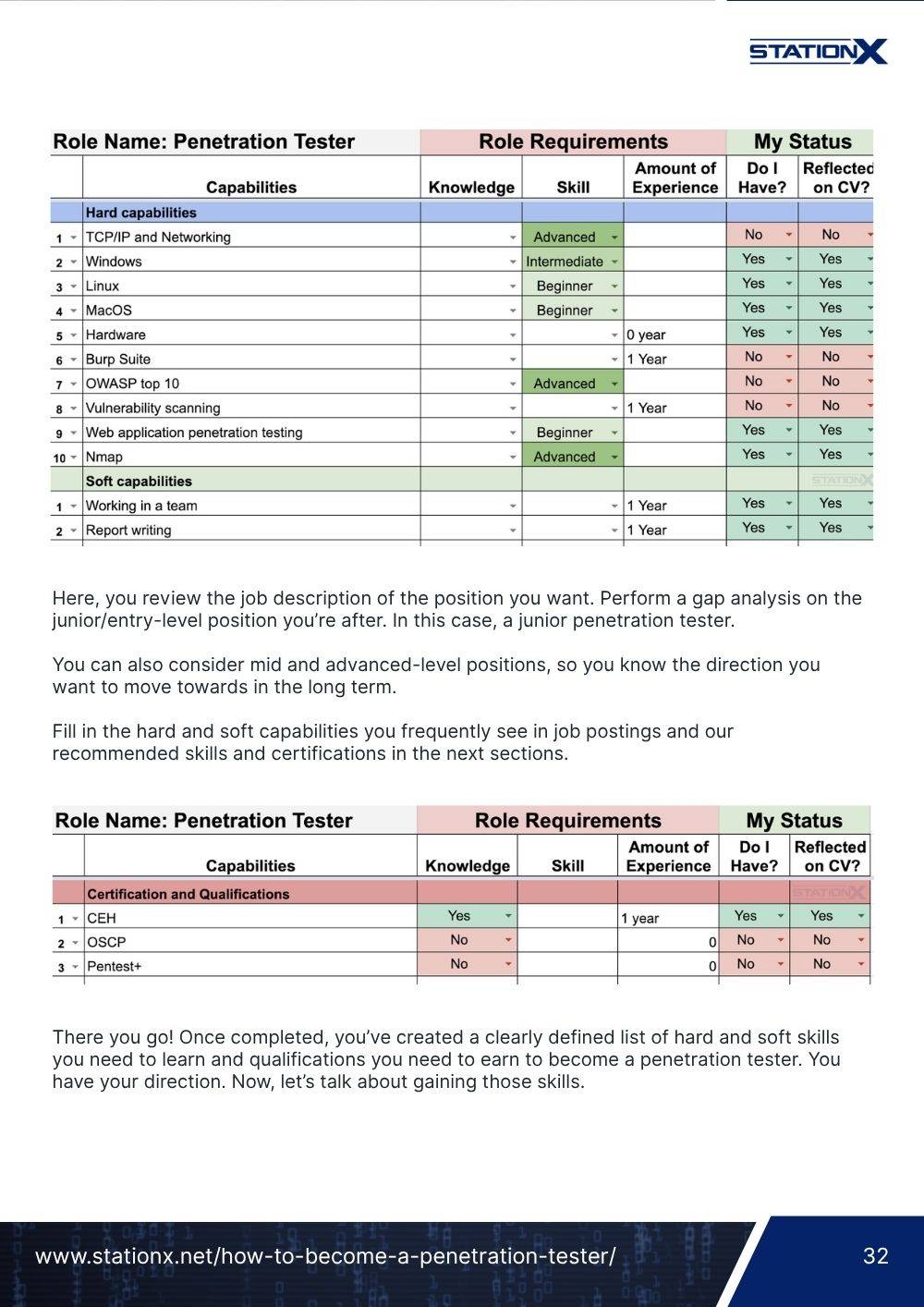
Here, you review the job description of the position you want. Perform a gap analysis on the junior/entry-level position you’re after. In this case, a junior penetration tester.
You can also consider mid and advanced-level positions, so you know the direction you want to move towards in the long term.
Fill in the hard and soft capabilities you frequently see in job postings and our recommended skills and certifications in the next sections.

There you go! Once completed, you’ve created a clearly defined list of hard and soft skills you need to learn and qualifications you need to earn to become a penetration tester. You have your direction. Now, let’s talk about gaining those skills.

Gain the Skills & Qualifications Needed to Be a Penetration Tester
Pen testers are expected to have a wide array of skills. Don’t be intimidated by this, but recognize that this job weighs hard technical skills with almost equal value as soft skills.
Remember, hacking gets you the information you need for your report, but your writing and presentation are what gets you paid.
The Hard Skills Needed for Ethical Hacking
Hard skills are the technical abilities you should possess. Remember, you will be required to test many different systems.
We’re not just referring to Windows and Linux desktop environments. Websites, VoIP phone systems, mobile devices, routers, Active Directory, Azure environments, SQL databases, and many other systems and infrastructures need testing.
It’s impossible to be an expert in everything, but developing enough surface-level knowledge to speak with an expert and keep up in some casual shop talk is necessary.
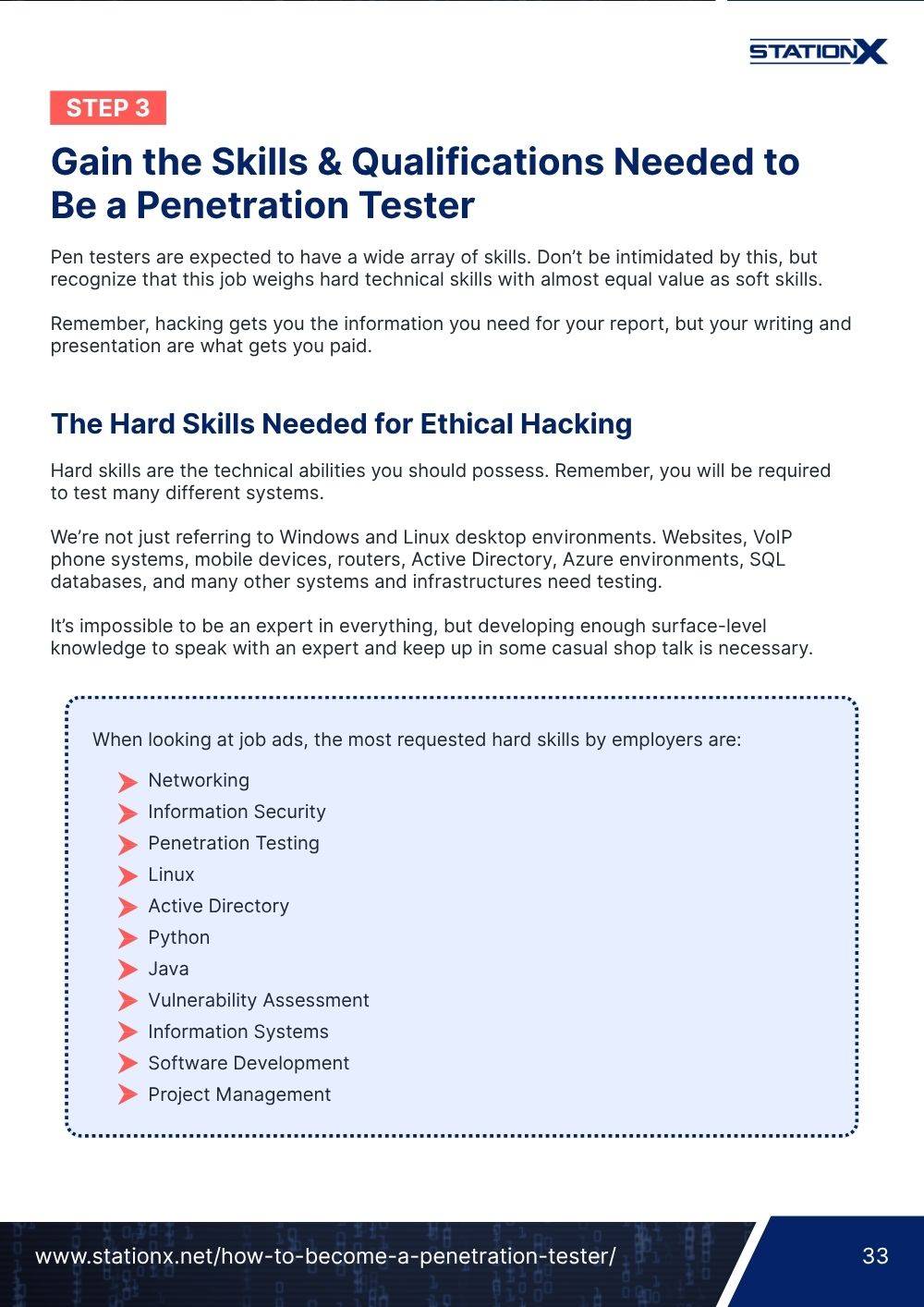
When looking at job ads, the most requested hard skills by employers are:
- Networking
- Information Security
- Penetration Testing
- Linux
- Active Directory
- Python
- Java
- Vulnerability Assessment
- Information Systems
- Software Development
- Project Management
Some of these required skills are very broad and general. “Networking,” for example, can mean many things. To illustrate this, Cisco has five levels of certification (Entry, Associate, Professional, Expert, and Architect) and nine different learning paths. All of those are “Networking,” but they are not equal.
There is a huge difference between a Cisco Certified Network Associate (CCNA) and a Cisco Certified Internetwork Expert (CCIE). Salary alone differs by roughly $50,000 per year between the two.
So, let’s break down these skills and define them into more concrete and actionable topics.
Some of the top skills that are growing in demand are
There are courses available on almost all of these topics in the StationX courses section.
Learning the Hard Skills for a Pen Tester Career

Time to learn the hard skills. Let’s take a look at the diagram above one more time. The courses below will give you the skills and knowledge you should gain in Stage Four.
Again, you should have a strong understanding of IT basics, operating systems, networking, and security fundamentals of Stages One through Three.
If you’re ready for the next steps, we recommend taking the following courses in this order:
More advanced hacking courses include:
All our hacking and penetration testing courses are here. You have full access to them when joining with a StationX membership. You can also purchase our Ethical Hacking Courses Bundle by clicking the banner below.
We have an article on our favorite ethical hacking books worth reading. Even if you don't build up a complete personal library, having some key choices as reference material is highly valuable.

Soft Skills Needed for Ethical Hacking
While job postings are usually low on soft skill requirements, they can be as, if not more, important than hard skills. These skills allow you to sell yourself to the client, organize a readable report worth paying for, and push yourself forward when you hit a wall.
These skills include
- Interpersonal and communication skills: The most important skill on this list. You are working with clients. They trust you with their network. They are looking to you and your expertise to protect themselves. In some cases, you are pitching the service. Learn this skill!
- Critical/analytical thinking: There is no straightforward path to take when trying to hack into a system. Sure, there are methodologies to follow, but situations are unique. You need to be able to look at the bigger picture, find what doesn’t belong, what’s misconfigured, and what can be abused or changed. It’s a puzzle that may or may not have an answer.
- Persuasion: This is more useful for higher-up roles, such as consulting and management. It also comes into play if you are doing social engineering.
- Adaptability: The famous motivational phrase and popular meme from Bear Grylls, “improvise, adapt, and overcome,” certainly applies to pentesting. As we said earlier, you will hit walls. You will encounter technology you’ve never seen before. You will be running short on time. Time to adapt.
- Collaboration/teamwork: Sometimes, you will be working on your own. Other times you may be part of a team on the same project. You will often have a technical contact, such as a network administrator, at the client in case of an issue. You need to be able to work smoothly with others.
- Attention to detail: You will be preparing reports that state what the vulnerabilities are, what tools were used, pictures as proof, and recommendations for remediation. These need to be high-level for the executives and very detailed for their IT admins. You also need to be sure not to do anything that will cause them downtime or damage their systems.
- Passion: This is not a job where you do the minimum while watching the clock. You need to love this. Hacking needs to excite you. If it doesn’t, look at another field within cyber security.
- Problem-solving: That’s what hacking is - problem-solving. The system is designed to keep you out. You want in. Solve the problem.
- Honesty and ethics: You’re being asked to play the criminal. Clients are putting a great amount of trust in you not to abuse your access by stealing information, extorting them, or lying to cover up a mistake.
Do I Need to Know Programming to Become a Penetration Tester?
The answer is somewhere in the middle. A junior penetration tester can get by without being able to code. Although, understanding the basics enough to look through and modify code slightly is necessary for pentesters of any level. As you move forward in your career, coding becomes much more important.
You will often use publicly available code referred to as “exploits”. These public exploits are often written in either Python or C (primarily Python). Without knowing what the exploit is actually doing, firing it on a client system is a huge risk.
- Is the exploit making permanent changes you will need to restore?
- Is it adding default credentials to a client system that attackers might be aware of?
- Is it malicious and calling back to another hacker?
If you aren’t confident enough in your ability to read the code, you can’t use it safely.
At higher levels, it becomes more important for a few reasons.
Web application penetration testing, as mentioned earlier, makes up a large percentage of the penetration testing landscape. Java and PHP are common in this discipline. Knowing these languages makes you a better pentester and allows you to tell a client what specifically needs to be fixed to secure their code.
Bash and PowerShell are scripting languages used by Linux and Windows systems respectively. Python, as we already mentioned, is a scripting language commonly used in pentesting and is used by network admins to roll out mass changes to a system, especially in cloud environments. You will be using these daily as a pentester.
Lastly, any public code that can be used by hackers has likely been cataloged by at least some of the major antivirus and security companies. Making changes to avoid detection, or at much more advanced levels, actually coding your own tools, will make you a much stronger ethical hacker.
We would also say that learning Python is one of the best ways to grow your skills and advance your career.
Getting the Necessary Qualifications to Become a Pen Tester
There are countless cyber security certifications available, and for many students, it becomes overwhelming to try and decide which have value and which don’t. This can be frustrating when you consider the amount of study required and the cost involved in writing the exams.
Let’s examine some of the most frequently asked-for certifications:
General cyber security certifications
- CompTIA Security+
- Certified Information Systems Auditor (CISA)
- Certified Information Systems Security Professional (CISSP)
- Various SANS/GIAC certifications
While these are some of the most common certifications seen in job postings, we want to be clear that our recommendations only partially align with this list.
Security+ is an excellent certification to get if you’re a beginner because it covers the fundamentals of information security. Having this certification tells employers you understand the terminology and are knowledgeable in a wide variety of security practices. Our Security+ Exam Cheat Sheet and 10 Tips to Pass the CompTIA Security+ Exam article can help you with this goal.
CISA and CISSP, by contrast, are NOT entry-level certifications. These are for individuals looking to move from an intermediate to an advanced career level.
You should pursue CISSP as a certification in your career. CISSP is the closest there is to an industry-wide standard certification and should be the goal of anyone wanting a career in information security. That said, it is not for those just starting in cyber security.
It is also worth noting that SANS certifications are very expensive, and it is common for those in the industry to request employers pay for the training and certification rather than the individual get it themselves.
If you're loofjking for a breakdown of the top beginner credentials to consider, read "10 Cyber Security Certifications for Beginners."
Penetration testing certifications
CEH and Pentest+ are very similar to each other. We compared the two in our Pentest+ vs CEH article. In summary, Certified Ethical Hacker appears more often on job postings, while Pentest+ is more affordable and covers a more complete and well-rounded curriculum. Both are DoD directive 8570 approved. Pick the one you feel is right for you.
While there are now several hands-on practical ethical hacking exams on the market (see our list of the very best certifications), OSCP offered by OffSec remains the most well-known and sought-after. It’s infamous for its 24-hour long exam requiring the hacking of a three-machine Active Directory network and three stand-alone boxes. It is as much a hazing ritual as an exam but a must-have for aspiring pentesters.
Recommended training courses for pen tester certifications
The previously listed courses in our "Learning the Hard Skills" section certainly cover the materials required to tackle CEH and PenTest+, and set the foundation for OffSec's PWK (Penetration Testing with Kali Linux) and OSCP.
Training for the other cyber security certifications discussed is also available through StationX.
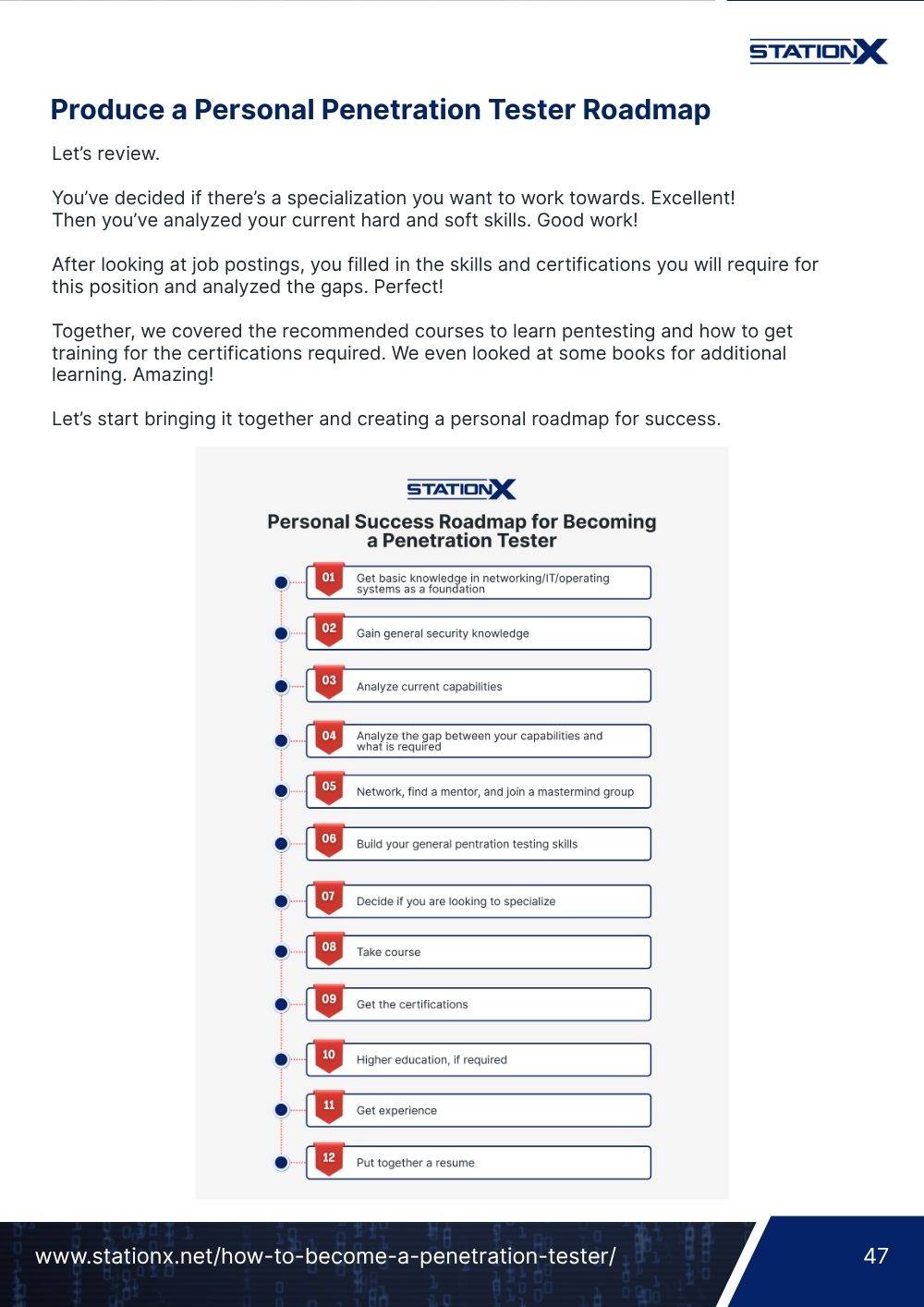
Produce a Personal Penetration Tester Roadmap
Let’s review.
You’ve decided if there’s a specialization you want to work towards. Excellent!
Then you’ve analyzed your current hard and soft skills. Good work!
After looking at job postings, you filled in the skills and certifications you will require for this position and analyzed the gaps. Perfect!
Together, we covered the recommended courses to learn pentesting and how to get training for the certifications required. We even looked at some books for additional learning. Amazing!
Let’s start bringing it together and creating a personal roadmap for success.

We will discuss the last few steps in the coming sections, but you can start working on your roadmap now. Also note that, as a member of the StationX Master's Program, a mentor will produce a custom roadmap for you.
Do You Need a Degree to Become a Penetration Tester?
There is a lot of debate surrounding this question, but rather than go into great detail quoting global analysis and polls, we’ll try to sum it up simply.
Can a degree help? Sometimes. More so if you intend to become something like a Chief Information Security Officer (CISO).
Do you need a degree? No.
Let’s look at it like this. The traditional attitude among companies for highly technical roles has always been to require a degree.
The gap between the number of cyber security positions and the available candidates is widening, and requiring a degree in computer science or a similar field limits the potential candidates a company can look at.
Next, while general computer science degrees are fairly common, specific cyber security degrees (let alone ones for pentesting) are more niche and harder to find.
Comparing certifications and degrees, it becomes clear why certifications are requested more. Certifications are standardized. If you have a certification from a reputable organization, the employer knows exactly what you know.
It doesn’t matter where you write your OSCP, CISSP, or Security+ exam. You can write it in any country and city worldwide, and it will be the same. The questions and tasks will vary for each participant, of course, but the expectations and grading are equivalent to each other no matter where you take them.
Degree programs vary from one college or university to another. The employer doesn’t know if the courses are practical and hands-on or glorified certification prep courses. Without being familiar with each program and its syllabus, the employer is just guessing if you have the required skills. Certifications are much more defined and regulated.
Having a bachelor's degree or a master’s degree or higher will never hold you back, and yes, some employers want to see it. A degree could tip the scales if all other things are equal between you and another candidate.
Generally, though, your experience and certifications will hold more weight than a degree. Read our in-depth analysis, "Can You Get a Cyber Security Job Without a Degree?"

Gain Practical Hands-On Experience in Penetration Testing and Cyber Security
Students often feel trapped in the cycle of “I can’t get a job without experience,” and “I can’t get experience without a job.” Fortunately, there are several ways to bulk up the experience section of your resume.
Here are some of our recommended actions to gain that experience:
See "How to Get Cyber Security Experience (Fast)" and "Cyber Security Projects for Resume Building" for more ideas.
Can I Get a Job Without Work Experience?
You might think, “All the above is great, but can I get hired without paid work experience?”
Feeder Roles: Yes. Generally, these involve a low level of technical understanding. The A+, Network+, or CCNA certifications will go a long way here. The experience gained from the previous section should be more than sufficient.
Entry Level: Generally, yes. That’s what an entry-level position is supposed to be, a job for those just entering the field without much experience. Certifications and the experience from the previous section will get you noticed here.
Intermediate and Advanced: No. For intermediate positions, you will have to earn your hours at an entry-level position before being trusted with more responsibilities. Advanced levels require not only technical experience but proven managerial skills.

Apply for Penetration Testing Jobs
Let’s recap. You’ve planned out your roadmap to success. You’ve developed your hard and soft skills. You’ve taken the courses, gotten the certifications, and want to get hired. What now?
As hiring practices are changing to match the demand for skilled professionals, we all must adapt in kind to properly promote ourselves.
Develop a Personal Brand for Your Pen Testing Career
You need to think of yourself as a product that you are trying to sell to an employer. What makes you appealing? Well, what makes any product appealing to a company?
A good product will save them time, lower their costs, and increase their revenue. Is that you? How do they know that you are the product they need?
This is where a personal brand comes into play. You are advertising yourself the same way paid software like Burp Suite Pro, Cobalt Strike, and PlexTrack advertise themselves. Show that you offer skills, knowledge, passion, and determination that could be theirs if they hire you.
Get on social media, particularly Twitter and LinkedIn. Consider a separate professional Twitter account from your regular one. Share your accomplishments. Thank influencers who inspire you. Complete a course? Tag the instructor. Pass a certification? Tag the organization and/or the instructor of any prep course you took.
Get yourself a blog. Sharing your experiences is a great way to get noticed. It doesn’t matter if the subject has been written on before by others because it’s never been written about by you. Write opinions, walkthroughs, and exam experiences (without breaking confidentiality agreements), journal your journey, and be sure to include struggles and victories.
Become a teaching assistant at StationX. This is a great opportunity to help others stuck at the same points you struggled with and eventually passed. It’s an amazing way to network, and saying you acted as a teaching assistant or mentor will go a long way on a resume.
Review the “Demonstrate your Abilities and Passion” section of our free Career Guide.
We have an excellent Cyber Security Personal Branding course by Ken Underhill.

Create a Great Resume for Pen Testing
There are three types of resumes you should consider creating—and each serves a different purpose in landing a job in penetration testing.
1. LinkedIn Profile
If you don’t have one already, get a LinkedIn account. It’s essential for professional networking, and many job sites use your LinkedIn to autofill applications. Recruiters actively scan LinkedIn to find candidates with the right skills.
Want help optimizing your LinkedIn profile? Check out our LinkedIn Job Search Complete Course by Ken Underhill.
2. Traditional Resume and Cover Letter
Many companies still require a PDF or Word resume with a tailored cover letter. You’ll need a clean, well-formatted resume that’s packed with the right keywords to pass Applicant Tracking Systems (ATS). That means you should be updating it for each job application based on the language in the posting.
Need help standing out? StationX Resume Services offer custom-built cybersecurity resumes created by hiring experts. You'll get:
- A one-on-one consultation
- A resume tailored specifically to your cybersecurity career goals
- Keyword-optimized formatting designed to beat ATS filters
- The option to upgrade with LinkedIn profile optimization
You’ll also find help in the Complete Career in IT Course and our Best Penetration Tester Resume (Templates & Examples) article.
3. Personal Website or Blog
A personal website gives you space to showcase your skills, write about your learning journey, and post project demos or CTF walk-throughs. This could be a GitHub page, a blog on Medium, or a custom site using your name or alias. Bonus points if you update it regularly—especially with technical posts. Recruiters and hiring managers notice.
How to Find Penetration Testing Jobs
There are several places to look for job postings.
- Cyber Security Jobs is designed specifically for our industry and organizes postings by specialization and certifications. We recommend you sign up here and register for penetration tester job alerts in your area.
- LinkedIn has a job search function. With a paid membership, it can provide information about how your skills line up with the job posting and how you compare with other applicants.
- Indeed is a popular job posting site. You can upload a resume and allow recruiters to reach out to you with potential job openings.
- If you are in the US see the Cyber Security Supply & Demand Heat Map
- Search for cyber security companies in your area and watch the job board on their website. Some will allow you to sign up for email notifications when a position is posted.
- Be sure to take the Complete IT Job Search Course in the member’s section.
- Read our Newbie’s Guide to Finding a Cyber Security Job article.
The Pen Tester Interview
Once you score the interview, you need to prepare. There will, of course, be the usual tell us about yourself, your previous experience, strengths and weaknesses, and other tried and true (and often tired) questions. We have a course on preparing for these interviews.
More common now are behavioral interview questions. These are best discussed in the article “41 Behavioural Interview Questions You Must Know” by Akshay Sachdeva on The Martec. He explains,
“The purpose of behavioral interview questions is to understand who you are, how you think, and how you approach real-world dilemmas. Your answers to these behavioral questions can help the interviewer gauge how you may (or may not) complement the current team.”
Some examples he includes in the article are
- Describe a time when you disagreed with a team member. How did you resolve the problem?
- Tell me about a time when you failed.
- Give me an example of when you had to assume leadership for a team.
- What is the most difficult/challenging situation you’ve ever had to resolve in the workplace?
- Tell me about a time when you disagreed with a supervisor.
- How do you approach problems? What’s your process?
We asked Joe Stimac from InterviewReady, “What piece of advice can you give early career Cyber job seekers?”
His response was,
“My best advice is to think like an employer and be prepared to demonstrate how you meet/exceed the job requirements. Offer specific examples of experiences for each duty/task posted in the job requirements by using P.A.R. (describe the problem, the actions you took, and the result).
“Employers hire people whose answers are credible and memorable. If you have limited or no employment history, talk about the transferable skills you learned at school or via StationX training.”
Want to practice how to present yourself with confidence in interviews?
Our StationX Interview Coaching Services include deep-dive mock interviews, personalized coaching, and feedback designed to help you land the job and negotiate the salary you deserve. These sessions are tailored specifically for cybersecurity roles and led by industry veterans who know exactly what hiring managers are looking for.
Also, be sure to read our article, "Top Penetration Tester Interview Questions."
Sample Interview Questions for a Penetration Tester
Cyber security interviews will have some questions very specific to the role. Here are some examples you should prepare for.
Introduction Questions
- Where do you go to research the latest vulnerabilities?
- What is the last script you wrote?
- What areas are you planning to improve on?
- How have you given back to the infosec community?
- What individuals or organizations do you follow on social media, or what blogs do you read that you recommend others follow and why?
Less Technical
- What is the purpose of a penetration test?
- Define the difference between red teams, blue teams, and purple teams.
- How is a black-box test different from a white-box test?
- What would you do if you saw signs of a previous breach during a pentest?
- What are some types of threat actors?
Moderate Technical
- Define golden and silver tickets.
- What are the most common network vulnerabilities?
- Define session hijacking and some methods.
- What Nmap command won’t ping the host?
- What is Kerberoasting?
Highly Technical
- Can SQL injection lead to remote code execution? How?
- What is the first thing you should do before testing begins?
- You have local credentials to a machine but not network credentials. What do you do next?
- On an Active Directory network, you have a valid username but no credentials. What would you do next?
- You get simple command injection on a web server through the address bar. What would you do to get a shell?
To Sum Up
If you seek an exciting, challenging, financially rewarding, and long-term secure career, penetration tester is a superb choice. For all the convenience and prosperity modern technology has brought us, the cyber landscape is still a battlefield. Companies and governments need ethical hackers to help them remain secure. That isn’t changing anytime soon.
If you are the person they’re looking for, a world of opportunities to work and excel in this field awaits you. These roles can be provided from the headquarters of the world’s largest companies to your home, from anywhere in the world. The only limits in this career are your own creativity and resourcefulness.
We hope this article helps you on your journey to becoming a penetration tester. If you have any questions, let us know in the comment section below.