The following article outlines some of the very best tools written in Python for people interested in cyber security, both on the offensive and defensive side of the industry.
We will show you the tools in action and describe why we like them so you can quickly determine if they’re right for you.
From open source intelligence gathering, network enumeration tools, database and Active Directory hacking to privilege escalation, password cracking, poisoning, and pivoting tools, we’ve dug out some of the best Python hacking tools.
But first, let’s figure out why Python has risen to the top for many developers and users.
Why Is Python Popular for Hacking Tools?
Python is a high-level programming language, first released in February of 1991 by Dutch programmer Guido van Rossum. Now in its third major iteration, Python is one of the world’s most popular programming languages today, with over 49% of developers choosing to use Python.
Python is open source, free of charge, and cross-platform, working on Linux, macOS and Windows. It has an extensive standard library that includes modules for many essential tasks right out of the box, and it’s relatively easy to learn and read.
Unlike languages such as C++, Python is an interpreted language. This is helpful because you don’t have to spend time compiling code, and you can use almost any development environment, from text editors to full-blown IDEs such as Visual Studio to write Python code. All of this versatility makes Python an ideal platform for cyber security professionals to create hacking tools.

Python Hacking Tools Categories
In this article, we will cover a number of important categories for Python hacking tools. These are as follows:
- OSINT Tools
- Enumeration Tools
- Web Application Hacking Tools
- Database Hacking Tools
- Active Directory Hacking Tools
- Privilege Escalation Tools
- Password Cracking Tools
- Poisoners
- Pivoting Tools
OSINT Tools
Open source intelligence, commonly referred to as OSINT, is the process of collecting and analyzing information from publicly available sources for intelligence purposes. Having good OSINT tools can make all the difference in discovering viable attack surfaces.
1. theHarvester

theHarvester is a one-stop-shop for OSINT reconnaissance. It has been around since approximately 2019 and scans many popular services and outputs them in a simple format, significantly automating the OSINT process and saving you from going to many different sources manually.
Why we like theHarvester:
- It’s simple to use.
- Modular, works with approximately 40 popular services with new ones being added all the time, including Bing, Cert Spotter, DNSdumpster, FullHunt, GitHub,Hhunter, OTS (AlienVault), Shodan, and pen test tools.
- It performs DNS brute forcing.
- It takes screenshots of subdomains that are found.
theHarvester is available at https://github.com/laramies/theHarvester and can be installed in Kali simply by typing sudo apt install theHarvester.
2. Recon-ng

Recon-ng is a reconnaissance framework designed with the goal of providing a powerful environment to conduct open-source web-based reconnaissance quickly and thoroughly. Recon-ng looks similar to the Metasploit Framework, so you will feel at home if you use Metasploit on a regular basis.
The product is split into three distinct tools: recon-ng (the main web reconnaissance framework, with an interactive shell ala Metasploit/msf), recon-web (which is a web interface to recon-ng), and recon-cli, (which is the command line version of the tool). Do note, however, that whilst the project has been going since at least 2012, it is not as up-to-date as some other tools.
Why we like Recon-ng:
- Allows for customization via modules.
- Very good at collecting threat intelligence.
- Has extensive coverage of data sources and APIs.
Recon-ng is available from https://github.com/lanmaster53/recon-ng and is installed in the default Kali linux installation.
3. SpiderFoot
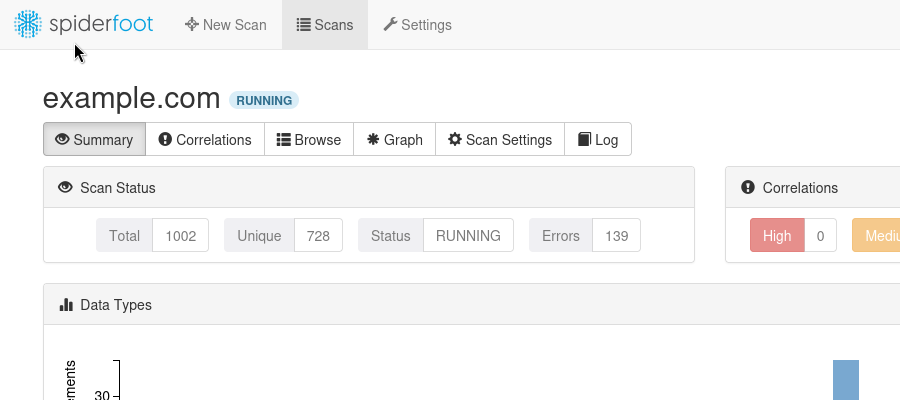
SpiderFoot integrates with masses of data sources and utilizes a range of methods for data analysis. It offers a graphical web-based user interface, as well as a CLI. The benefit of SpiderFoot, unlike other similar tools, is that it gathers intelligence related to different types of target, including people’s names, e-mail addresses, IP addresses, domain names, hostnames, network subnets or ASNs.
Not only can SpiderFoot be used offensively to gather information about the target, but it can also be used defensively to identify the sort of information your organization is providing attackers to use against you.
Why we like SpiderFoot
- The graphical web-based user interface makes Spiderfoot easy to use and makes the data that has been discovered easy to navigate, whilst the command line interface tool allows the power of CLI-based automation.
- SpiderFoot has over 200 modules that perform many helpful actions, including:
- Host/subdomain/TLD enumeration/extraction
- Email address, phone number, and human name extraction
- Bitcoin and Ethereum address extraction
- Check for susceptibility to subdomain hijacking
- DNS zone transfers
- Threat intelligence and Blacklist queries
- API integration with SHODAN, HaveIBeenPwned, GreyNoise, AlienVault, SecurityTrails, etc.
- Social media account enumeration
- S3/Azure/Digitalocean bucket enumeration/scraping
- IP geo-location
- Web scraping, web content analysis
- Image, document, and binary file metadata analysis
- Dark web searches
- Network scanning (port scan) and banner grabbing
- Data breach searches
Spiderfoot is available on GitHub at https://github.com/smicallef/spiderfoot and is installed in Kali Linux by default.
Ethical Hacking Courses Bundle: Learn Hacking for Beginners
Just starting out? The Ethical Hacking Courses Bundle teaches you how to think like a hacker, exploit common weaknesses, and build the foundational skills for penetration testing.
4. Sherlock

Sherlock is a tool to find usernames across most social networks including Twitter/X, Reddit, Blogger, Docker Hub, Gamespot, HackerNews, Pastebin and many more.
Why we like Sherlock
- Sherlock is a simple tool that does what it says on the tin. If you want to find usernames across social media, this is a very quick and simple tool to use.
Sherlock is available on GitHub at https://github.com/sherlock-project/sherlock. Sherlock isn’t installed in Kali by default; however, it is easily installed by typing sudo apt install sherlock.
Enumeration Tools
Enumeration tools are used during initial reconnaissance, they are designed to identify network topologies, devices, services (such as DNS and Directory Services), applications, banners and user details on a network by scanning and collecting related information.
5. pyWhat
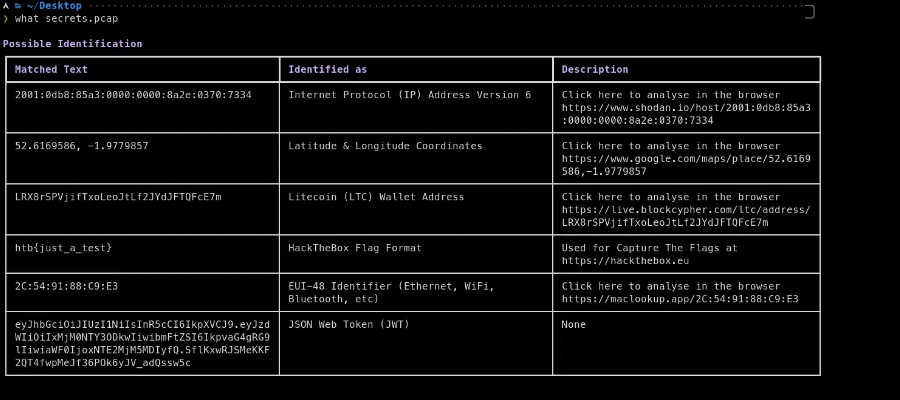
pyWhat is an analysis tool that lets you know what a file is or what it contains. It works on strings of text, too.
In the ‘old days’, we would use the unix command ‘strings’ to look up arbitrary text strings in a file or perhaps use a hex editor. Rather than use strings, a debugger, or a hex editor, we can use pyWhat to identify what is in a file, and it will give us a much more succinct description of what the information actually is.
Why we like pyWhat
- A random EXE file may contain malware or ransomware - pyWhat will help you identify the malware within the executable.
- pyWhat will also recursively analyze the contents of a file, such as a network capture .pcap file, identifying items such as IP addresses, but even more useful things such as URLs, email addresses, even phone numbers, and credit card numbers.
- Searches GitHub repositories for credentials or API keys.
Although pyWhat is not installed on Kali Linux by default, it is freely available on GitHub at https://github.com/bee-san/pyWhat. You can install it easily using pip: sudo pip pywhat.
Web Application Hacking Tools
Web application hacking tools are used to test, analyze, and exploit vulnerabilities in web applications to assess their security and identify potential weaknesses.
6. wfuzz
A fuzzing tool is an automated tool that involves brute-forcing invalid, unexpected, or random data as inputs to a target. In the case of wfuzz the target is a website. The most common use of wfuzz is to use wordlists to check for paths and files that are not advertised on a website but could be found by guessing their name.
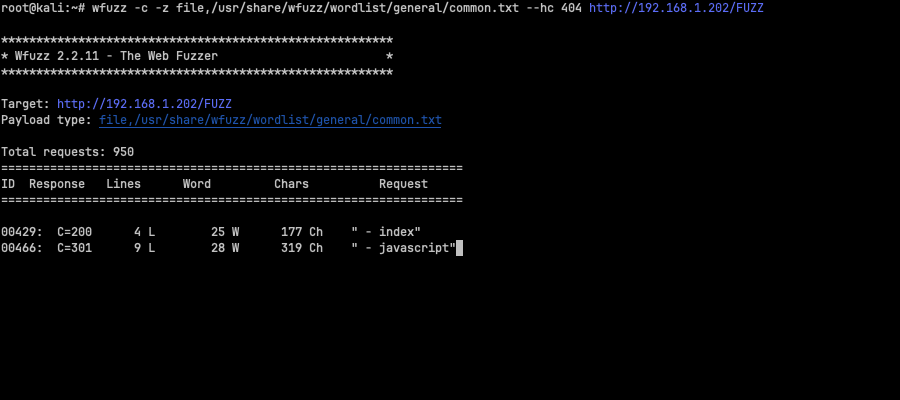
Why we like wfuzz
- Simple to use: place the word FUZZ wherever you want the given payload to exist.
- Works on authentication pages, forms, directories, files, headers, and parameters.
- Has a modular framework to allow Python developers to contribute easily.
- Can be used with other tools such as Burp Suite.
Wfuzz is provided in the default Kali Linux installation and can also be obtained via Github: https://github.com/xmendez/wfuzz
7. droopescan
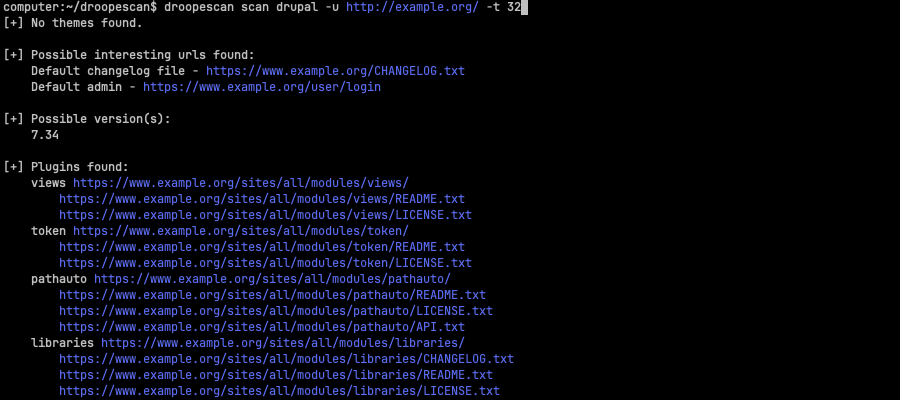
Droopescan is a multi-CMS vulnerability scanner. It scans for issues in some of the most popular content management systems, including WordPress, Drupal, and Silverstripe. It also has partial functionality for Joomla and Moodle.
Why we like droopescan
Establishes systems of good habits to achieve goals
- Most CMS vulnerability scanners don’t check all CMS engines. Having the ability to check many with one tool, especially when you don’t know what the target website uses, makes the job of the tester quicker.
- The scanning process is fast and stable.
Whilst droopescan is not provided in the default installation is available on GitHub at the following URL: https://github.com/SamJoan/droopescan.
Database Hacking Tools
Database hacking tools are applications that test for vulnerabilities in Database systems such as Microsoft’s SQL Server, MySQL, or PostgreSQL. They may often attempt to exploit those vulnerabilities to allow a way into a database that should otherwise not be possible.
8. sqlmap

sqlmap is the de-facto open-source database penetration testing tool. It automates the process of detecting and exploiting SQL injection flaws and taking over database servers, and has many features that are helpful to a penetration tester.
Why we like sqlmap
- Easily take over databases with injection flaws.
- Powerful detection engine.
- Many niche features.
- Lots of switches for database fingerprinting.
- Exploits techniques such as “over data fetching” and accessing underlying file systems as well as executing system commands on the underlying O/S.
- Provides an API client/server tool (sqlmapapi).
Sqlmap is available from Github: https://github.com/sqlmapproject/sqlmap and is installed by default in most Kali Linux installations.
Active Directory Hacking Tools
Active Directory is an LDAP (Lightweight Directory Access Protocol) service created by Microsoft. It maintains a directory of users, groups, and authorizations to allow a user to a particular system or file. The tools below show various ways of exfiltrating important information regarding AD servers, as well as potentially how to exploit weaknesses in them.
9. Impacket

Impacket provides a suite of tools for Active Directory enumeration and exploitation which provides low-level access to Microsoft services (NTLM and Kerberos authentication, file sharing using SMB1-3 protocols, SQL Server and MSRPC). Impacket also provides common service discovery using common protocols such as IP, TCP, UDP and ARP.
Why we like Impacket
- Sixty simple scripts make up the suite of tools in Impacket
- Tools include impacket-DumpNTLMInfo (provides information on your NTLM configuration), exchanger (that messes with MS exchange services), keylistattack (which performs an agentless attack to dump secrets from the remote machine), and Get-GPPPassword (which obtains and decrypts group policy preferences passwords)
- The software is frequently updated
- Packets can be constructed from scratch, as well as parsed from raw data.
Impacket can be obtained as source code from Github: https://github.com/fortra/impacket. It comes pre-installed by default on Kali Linux. All of the tools are available in the Kali metapackage ‘impacket-scripts’.
10. CrackMapExec (CME)

From its own description, CrackMapExec is a “Swiss army knife for pen testing networks”. It’s more than a password tool; it’s a versatile pen testing utility for network auditing and exploitation. It excels in enumeration, vulnerability exploitation, and post-exploitation activities. With capabilities for credential harvesting, automated workflows, and Active Directory interactions, it's highly modular and integrates well with other tools, making it essential for comprehensive network security assessments.
Why we like CrackMapExec
CrackMapExec performs a number of password exploitation services, particularly upon Windows targets:
- Easily enumerates logged-on users
- Rapidly spiders SMB shares
- Executes psexec style attacks
- Auto-injects Mimikatz/Shellcode/DLL’s into memory using Powershell
- Will dump the NTDS.dit and more
- Due to it being a concurrent threading script, it is quite fast
- Uses only native WinAPI calls for discovering sessions, users, dumping SAM hashes
- Opsec safe (no binaries are uploaded to dump clear-text credentials
- A database is used to store used/dumped credentials. It also automatically correlates Admin credentials to hosts and vice-versa allowing you to easily keep track of credential sets and gain additional situational awareness in large environments.
CrackMapExec is installed in the default installation of Kali, but may also be obtained from Github: https://gitlab.com/kalilinux/packages/crackmapexec
Privilege Escalation Tools
Privilege escalation tools are used to exploit vulnerabilities in systems, applications, or processes in order to gain elevated access or permissions beyond the permissions that were originally granted as a normal user.
11. BeRoot

Beroot is a post-exploitation tool that performs checks for common misconfigurations on Linux and Windows systems which might be exploitable to escalate privileges.
Why we like BeRoot
BeRoot attempts to cover a lot of local privilege escalation tactics, including the following Windows methods:
- DLL hijacking
- Unquoted paths
- Names pipes
- Registry
- Memory exploits ala Mimikittenz
- Enumeration of configuration files
- Cached SAM
As well as Linux methods including:
- Sudo
- Kernel & Daemon takeover
- Password mining
- NFS
- Cron
- SUID binaries and file permissions
BeRoot is not available within the standard Kali Linux repositories, but is available freely from Github: https://github.com/AlessandroZ/BeRoot/tree/master/Linux
CompTIA PenTest+ Voucher
Launch your pentesting career with a discounted CompTIA PenTest+ Voucher. Save up to 30% and earn your certification with an authorized CompTIA partner.
12. AutoLocalPrivilegeEscalation

AutoLocalPrivilegeEscalation is an automated Python script—launched via a shell script—which compares the current Linux system configurations and kernal with known privilege escalation vulnerabilities. This not only acts as a quick reference to potential exploits matching the target system, but can automatically download and compile the exploits to for you.
Why we like AutoLocalPrivilegeEscalation
- Downloads and compiles a list of exploits for the Linux kernel from Exploit-DB
- Saves you time in downloading and testing each exploit manually by automating the process
AutoLocalPrivilegeEscalation is not available within the standard Kali Linux repositories, but is available freely from Github: https://github.com/ngalongc/AutoLocalPrivilegeEscalation
Password Cracking Tools
Password cracking tools were one of the first types of hacking tools, and although they aren’t always as effective today as they once were (given the popularity in better authentication methods like multi-factor and zero-trust), password cracking tools are still an essential tool in a cyber security experts’ arsenal.
13. Patator

Patator is an access brute forcer, with a modular design. Apparently written by its author out of frustration, compared to tools such as Hydra, Medusa, Ncrack, Metasploit and NMAP NSE modules, Patator strives to “be more reliable and flexible” than these predecessors.
Why we like Patator
- Patator has 34 modules built-in, including brute-forcing for SSH, Telnet, SMTP, HTTP(S), RDP, SMB, VMware Authentication Daemon, MSSQL, Oracle, MySQL, PostgreSQL, VNC, DNS, SNMP, ZIP archive passwords, Java keystores and more.
- Multi-threaded for optimal speed
Patator is installed in the default Kali installation and can also be obtained from Github: https://github.com/lanjelot/patator
Poisoners
Poisoners are used to intercept, modify, or redirect communication between two parties without their knowledge. These can be used to grab and pass credentials, alter communication mid-stream, assume the identity of a legitimate service, or redirect users to malicious sources.
14. Responder

Responder is a popular open-source spoofing and credential harvesting tool for man-in-the-middle attacks. It impersonates legitimate Windows services and poisons the LLMNR, NBT-NS, and MDNS protocols.
When a Windows machine communicates with Responder, the tool spoofs the network traffic and hijacks login credentials. It uses these credentials to perform credential relaying and pass the hash attacks.
Why we like Responder:
- It is difficult to defend against if a Windows network uses the LLMNR and NBT-NS network protocols.
- Can automate pass the hash and credential relaying attacks when used with other tools, such as MitM6.
- It can capture traffic that uses common network protocols, such as DNS, HTTP, and SMB.
15. Scapy

Scapy is a network packet manipulation tool. It enables the user to send, sniff, dissect, and forge network packets. It is useful for tasks like network discovery, packet manipulation, and network testing.
Why we like Scapy
- From the GitHub page, Scapy claims to handle 85% of the tasks that tools such as nmap, arpspoof, arp-sk, arping, tcpdump, wireshark, p0f perform
- Allows for the creation of forged packets/man-in-the-middle attacks
- When you send a set of defined packets, scapy automatically receives answers, and matches requests with answers, effectively keeping track of the packet list
Scapy is available on GitHub at https://github.com/secdev/scapy.
Whilst scapy is not installed by default in Kali Linux, it can be easily installed by typing sudo apt install python3-scapy.
Pivoting Tools
Pivoting refers to the technique used by penetration testers and cyber attackers to move around inside a network after gaining initial access to a system. A pivoting tool is a software utility that facilitates this process, allowing the user to use the compromised system to target other systems within the same network, expanding the reach of their attack or assessment.
16. PivotSuite
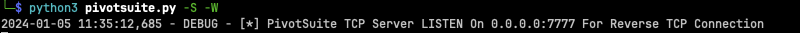
PivotSuite allows you to use a compromised system to move around inside a network, either as a client or a server.
Why we like PivotSuite
- Works without requiring admin/root access on compromised host
- Operates well when a compromised host is behind a Firewall / NAT, using a reverse tunnel
- Support for forward and reverse TCP tunneling is built-in, as is a SOCKS5 proxy.
- UDP over TCP supported for stealth
- NTLM proxy authentication support
PivotSuite is not installed by default in Kali, however is available freely from Github: https://github.com/RedTeamOperations/PivotSuite
Conclusion
Some of the finest ethical hacking tools are open-source and are generally free of charge. Furthermore, in many cases, Python is the programming language of choice for many of these tools because they are cross-platform and they are easily adapted because the code is easy to understand.
You can learn Python for cyber security with the StationX Master's Program. You will get exclusive certification advice, mentorship, and over 30,000 classes and labs to help you take your career to the next level.
You can also check out our Complete Python Course Bundle for Hacking and Cyber Security will teach you Python 2 and 3 through advanced hands-on and real-world projects. Click below to purchase lifetime access to six top courses.
This bundle includes:
- The Ultimate Python Hacking Course: Beginner To Expert
- Best Python Course for Beginners (Python 3)
- Advanced Python Course: Cyber Security and Web Applications
- Ethical Hacking Python Course: From Zero To Mastery
- Ethical Hacking With Python Course : A to Z
- Introduction to Python Data Science Course




