Through the manipulation of IP and MAC addresses, an ARP spoofing attack can alter the way devices on your network communicate with each other. This allows attackers to intercept traffic between your devices and potentially steal confidential information.
While ARP spoofing is useful for penetration testers in assessing a network's security posture, it poses a significant risk to blue teamers as it can be used as a stepping stone to carry out various other types of attacks, such as man-in-the-middle and denial-of-service attacks.
Being aware of the ARP protocol and its limitations is paramount to remaining safe from this attack and its potential threats. This article will provide you with more technical details about this attack, explore some commonly used tools and techniques, and address some frequently asked questions.
So If you are interested in learning more about what is ARP Spoofing, be sure to read the full article.
What Is ARP?
Before diving into the attack's technicalities, it is important to have a fundamental understanding of the ARP Protocol.
Typically, within a local area network (LAN), devices communicate with one another using two types of addresses; IP (Internet Protocol) for logical addressing and MAC (Media Access Control) for physical addressing.
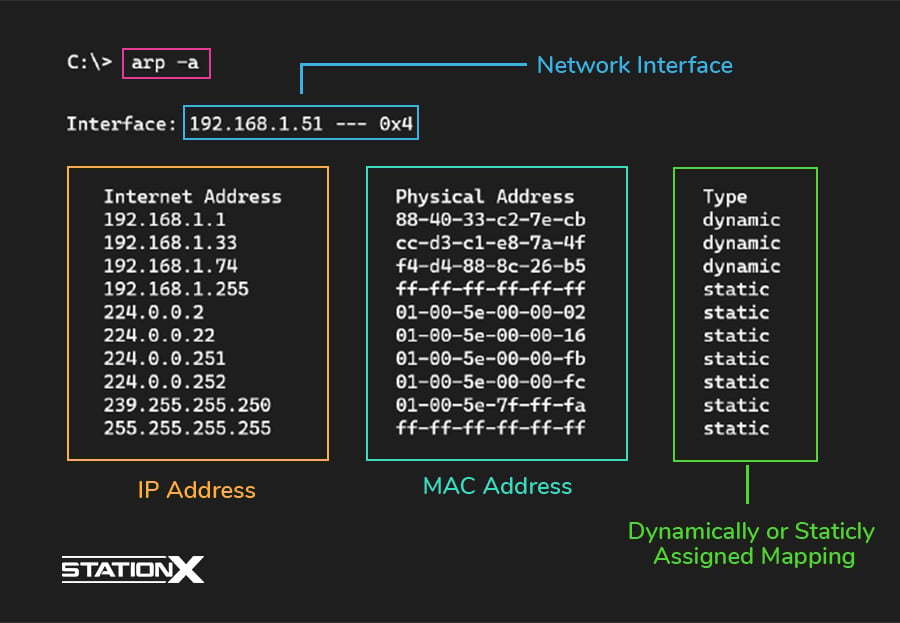
In order to facilitate communication through the physical network, the ARP (Address Resolution Protocol) was developed to map the layer three IP addresses of devices to their layer two corresponding MAC addresses.
In this way, the ARP protocol enables devices on a network to find and identify each other using their IP and MAC addresses.
The ARP protocol allows
- Hosts to communicate within the same network and to acquire the gateway address to other networks.
- Routers to communicate with hosts within the same LAN and to communicate with other routers.
The ARP protocol makes use of two distinct types of packets, referred to respectively as an ARP request and an ARP reply, in conjunction with the previously shown ARP table to store the mapping between the IP and MAC addresses.

ARP works by broadcasting an ARP request packet containing the IP address of the target device and then receiving an ARP reply packet containing the MAC address for that device.
Gratuitous ARP
There is another type of ARP packet that you should be aware of to understand certain spoofing attacks, called Gratuitous ARP. Two types can be distinguished
- Gratuitous ARP replies: These are ARP replies that are sent without any corresponding ARP request. Generally used by a host to announce its presence on the network.
- Gratuitous ARP requests: These are ARP requests that are sent without expecting any corresponding ARP reply. Typically used for detecting IP address conflicts and ensuring that nobody else in the same network uses the same IP address as the sender.
Within the gratuitous ARP packet, the source destination IP is the IP of the issuer (attacker), and the MAC Address is the LAN’s broadcast address (FF-FF-FF-FF-FF-FF).
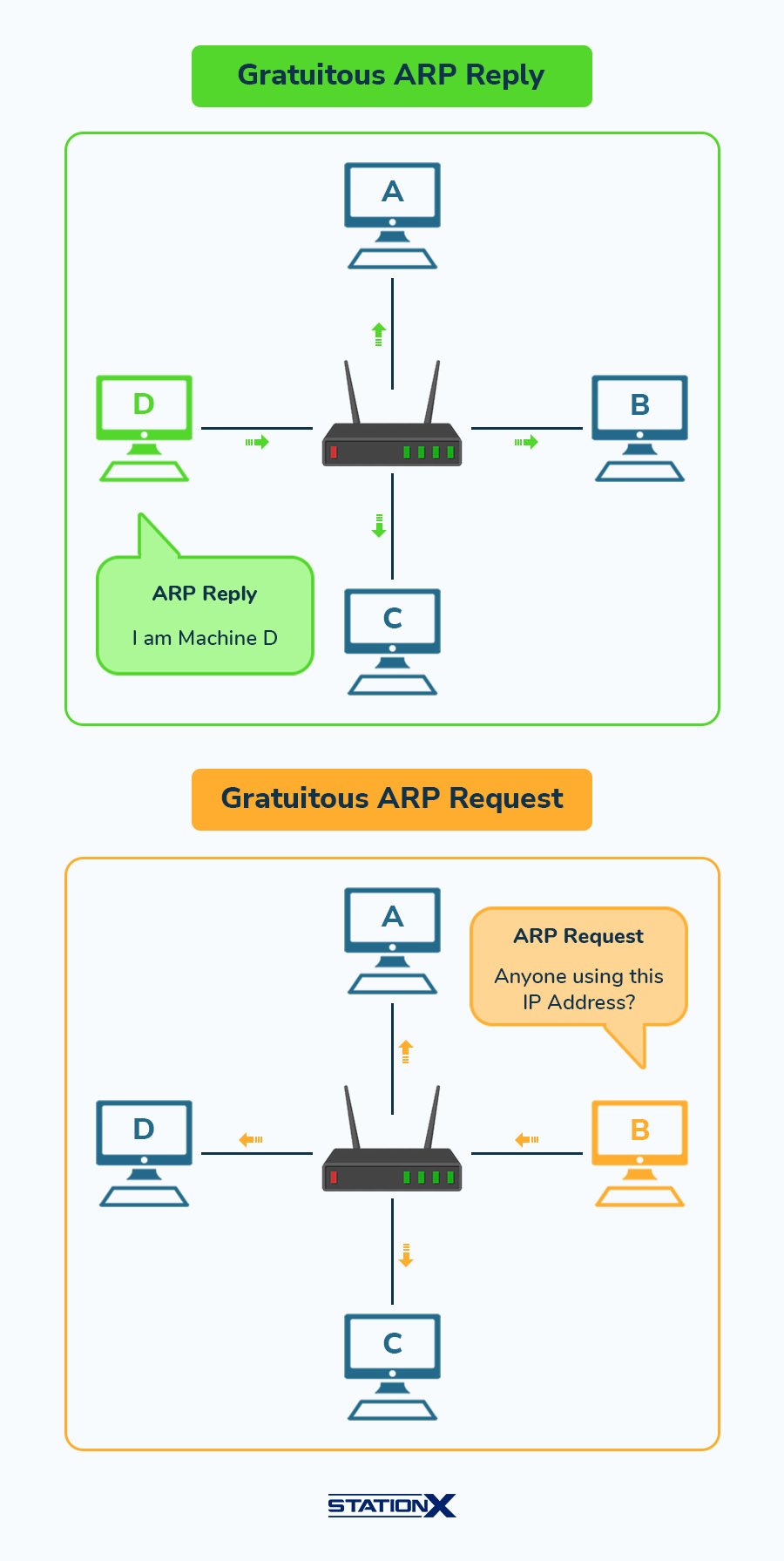
Gratuitous ARP can be useful for maintaining the consistency of the ARP cache on devices, reducing the amount of ARP requests, and enhancing network performance. However, they are usually exploited to initiate MiTM and spoofing attacks within a LAN.
CompTIA PenTest+ Courses Bundle
Ace your PenTest+ exam with our CompTIA PenTest+ Courses Bundle, containing a top-rated PenTest+ prep course, a beginners penetration testing course, 3 full length practice exams, and over 500 study flashcards!
What Is ARP Spoofing?
Now that we have gone through the basics of ARP, let us explore how it is exploited for ARP spoofing attacks.
ARP spoofing (also commonly referred to as ARP poisoning) is a form of attack in which an attacker sends falsified ARP messages over a local area network. This results in the linking of an attacker’s MAC address with the IP address of a legitimate computer or server on the network.
By doing so, the attacker would place himself in the middle of the communication between network nodes, which will allow him to gain access to the transmitted data, modify traffic, or even perform denial-of-service attacks.

ARP spoofing/poisoning alters the ARP cache of devices in order to redirect the traffic to their machine. This can usually be achieved in two ways, either by poisoning the hosts directly or the network’s gateway.
What Is the Aim of an ARP Spoofing Attack?
The main objective behind an ARP spoofing attack is to gain access to network communications and potentially mount to other attacks, including but not limited to
- Man-in-the-middle attacks: The attacker can intercept and alter network traffic intended for other devices on the network, effectively acting as a man-in-the-middle between the devices. This leads to several potential threats, including
- Eavesdropping: The attacker can use the spoofed IP address to listen in on network traffic and gather sensitive information intended for other devices.
- Credential sniffing: The attacker can intercept and capture login credentials, passwords, cookies, and other sensitive information transmitted over the network.
- Session hijacking: The attacker can intercept and steal or predict session cookies and IDs, effectively taking over an existing session between two parties.
- Data tampering: The attacker can alter or modify the redirected traffic, potentially causing damage or disruption to systems and applications.
- Identity theft: The attacker can use the spoofed IP to act as a particular authority or host within the network.
- Data exfiltration: The attacker can use the spoofed identity to steal sensitive data from the network and exfiltrate it to an external location.
- Pharming attacks: The attacker can use the spoofed IP address to launch a pharming attack, in which users are redirected to a fake website that appears legitimate, potentially leading to the theft of information.
- Denial of service (DoS): The attacker can flood the network with crafted ARP packets, disrupting or disabling the ability of other devices to communicate.
- Gain unauthorized access to resources: The attacker can use the spoofed host’s privileges to gain unauthorized access to resources on the network, such as servers, databases, restricted content, and applications.
- Malware injection: The attacker, with enough privileges, can inject malware or other malicious software into the network, potentially infecting other devices on the network.
- Network reconnaissance: The attacker can gather information about the devices and network infrastructure on the network, potentially as a precursor to a more targeted attack.
Depending on the security posture of the network, these attacks should not be straightforward by today's standards. In a regular scenario, it would be challenging to get access to certain resources, but with a combination of expertise and creativity, a lot can be compromised.
What Tools Are Used for ARP Spoofing?
Over the years, several tools have been developed for research purposes and to test the security posture of a network. Here are some tools that can facilitate an ARP Spoofing attack (Keep in mind that it is your responsibility to use these tools in a legal and responsible manner):
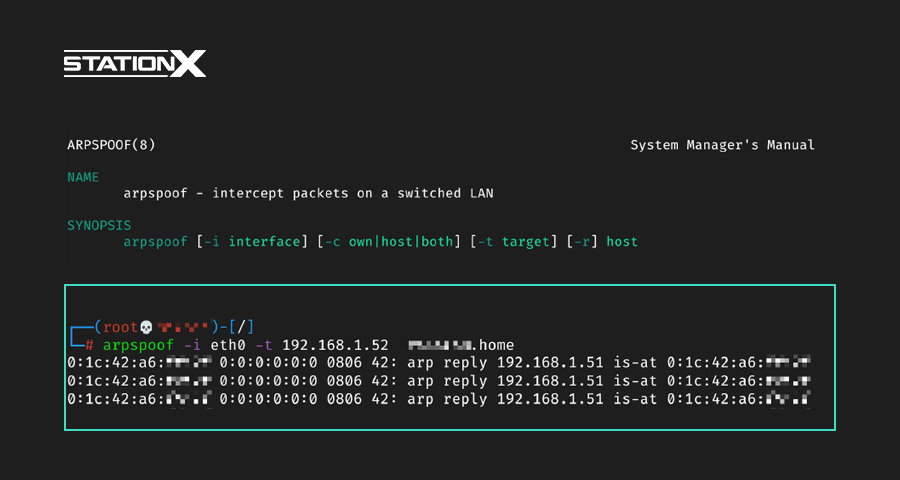
Arpspoof
A tool from the Dsniff package that can be used to send forged ARP messages on a LAN. It can be used to redirect traffic or to perform man-in-the-middle attacks. It is available in the Kali Linux distribution and can be obtained by installing the dsnif package.
Ettercap
Ettercap is a free and open-source network security tool that was originally developed for network sniffing but has since been expanded to include other man-in-the-middle (MitM) attacks, including ARP spoofing.
In addition to its core features, Ettercap now includes a range of useful tools such as packet filtering, password collection for various protocols, SSL/SSH support, and more. It also supports third-party plugins, providing virtually limitless capabilities.
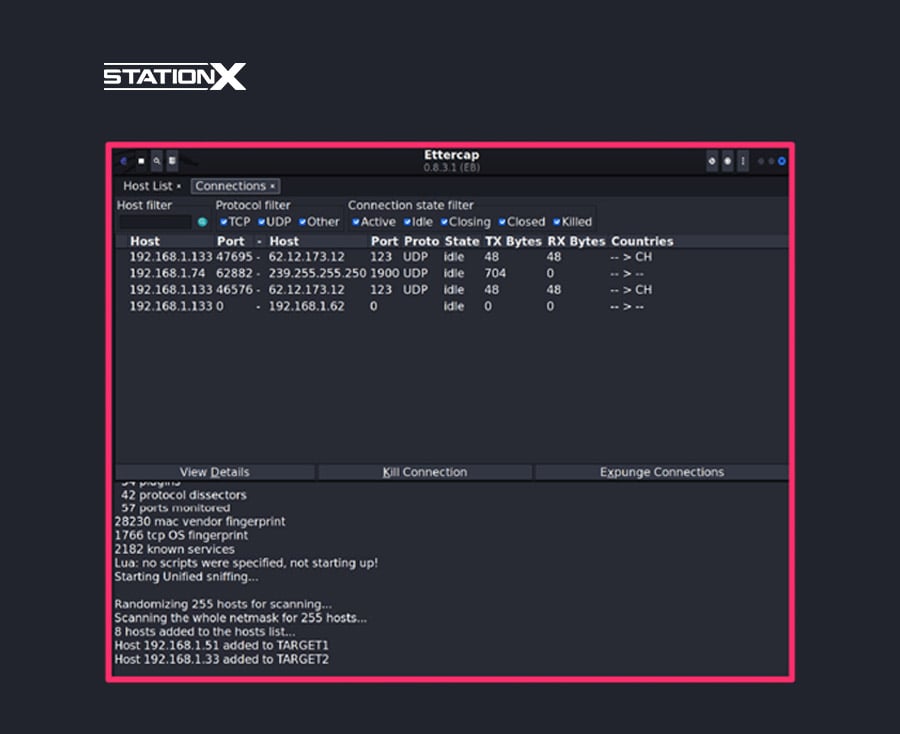
You can use Ettercap straight from the console, or you can use the GUI version. It is available for Linux, macOS, and Windows and can be downloaded from the official Ettercap homepage.
CompTIA PenTest+ Voucher
Launch your pentesting career with a discounted CompTIA PenTest+ Voucher. Save up to 30% and earn your certification with an authorized CompTIA partner.
Bettercap
Bettercap is an all-in-one networking hacking tool written in Go. The tool includes an extensible set of features for different types of targets, including WiFi networks, BLE devices, wireless HID devices, and support for ipv4 and Ipv6 networks.

Bettercap can be used from the CLI (Command Line Interface) in an interactive session and a javascript engine, as well as a web UI for an easier and more visual-based experience.
Wireshark
Although not necessarily used for performing the ARP spoofing. It is an essential tool for analyzing the network and sniffing the packets through the communication channel. See our Wireshark Cheat Sheet here.
Wireshark is A free and open-source network protocol analyzer that can be used to capture and analyze network traffic, including ARP packets.
It is available for Windows, macOS, and Linux and can be downloaded from the following link: https://www.wireshark.org/.
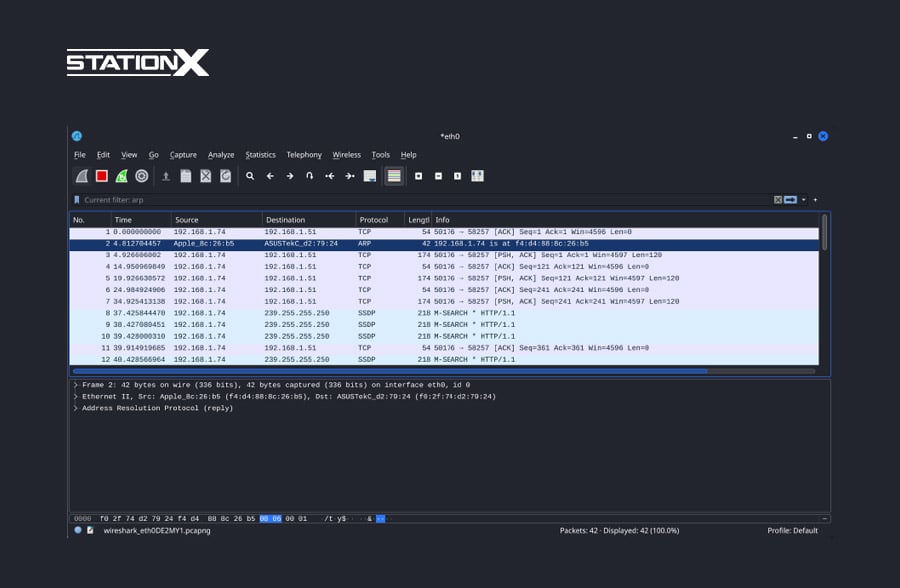
For a more lightweight and scripting-oriented workflow, Wireshark comes with another tool called Tshark, which you can access from the command line.
Whether you're a security researcher or just looking to learn more about network security, this is a powerful set of tools to have in your arsenal. If you are looking for more alternatives, however, keep in mind that several well-known tools have been retired or are no longer supported, so double-check before spending hours troubleshooting. We offer a Hacking Tools Cheat Sheet available for quick reference here.
Conclusion
ARP spoofing is a critical threat that allows attackers to gain access to network resources and sensitive information without the knowledge or consent of the target. It can also aid in launching other attacks, such as denial of service (DoS) and social engineering attacks.
As such, it is paramount for network and security engineers to be aware of the risks posed by ARP spoofing and to implement measures to counter and mitigate such attacks. This may involve implementing network security measures, such as firewalls and intrusion detection systems, and utilizing secure protocols, such as HTTPS.
If you wish to learn more about how to carry out this attack and secure your network from such threats, consider the StationX Master's Program, with over 30,000 courses and labs for both blue and red team students!
You can also dive deep into Kali Linux and Penetration Testing with our Ethical Hacking Course Bundle. Just click the banner below to start your hacking journey.




