Many cyber security professionals find digital forensics to be one of the most exciting fields to work in.
This is because working in digital or cyber forensics means not only letting your curiosity guide you in your search for and analysis of evidence but also having a significant real-world impact.
Often, digital forensic investigators identify home-run evidence to criminal legal cases or crack the source of a malware attack.
But what is digital forensics in cyber security? If you’re struggling to see the forest for the trees and want the low-down on what digital forensics professionals do and how they do it, read on.
Let’s start.
What Is Digital Forensics in Cyber Security?
Digital forensics is an area of cyber security that refers to the process of acquiring, examining, and analyzing digital data from a device, network, or system.
It also involves producing reports from these data analysis findings and following strict procedures to ensure data integrity and authenticity.
The National Institute of Standards and Technology (NIST) defines digital forensics as follows:
“In its strictest connotation, [digital forensics is] the application of computer science and investigative procedures involving the examination of digital evidence—following proper search authority, chain of custody, validation with mathematics, use of validated tools, repeatability, reporting, and possibly expert testimony.”
Meanwhile, Information Systems Audit and Control Association (ISACA), defines digital forensics as follows:
“In a nutshell, digital forensics tools and techniques can be used to trace and investigate what may have occurred or led to an incident, to retrieve lost data, and to gather evidence for use by an organization against a person or entity or to defend the organization.”
Working in cyber security forensics usually means working for law enforcement to extract and analyze data from the devices of those suspected of crimes.
The digital forensics professional will use specialist tools and techniques to accomplish this.
They’ll also follow strict and precise rules and regulations to ensure data integrity and authenticity. This is especially important because the digital evidence they secure, analyze, and report might be used in a legal trial, so establishing credibility is paramount.
While less common, digital forensics professionals can also work in the private sector. Such professionals might use digital forensic tools and techniques to audit a company’s digital components and discover if employees have been doing anything illegal, such as committing fraud.
More commonly, however, corporate digital forensics professionals will form part of a Security Operations Center (SOC) or be contracted by an organization’s SOC, to help investigate after a cyber security incident.
For example, they might analyze malware to discover who made it, who planted it, and how it breached company defenses.
Cyber Forensics Tools and Tasks
There are many different tools for different cyber forensics tasks, and which ones you use will probably depend on what type of cyber forensics you’re undertaking. Here are some of the most common types:
- Computer forensics
- Mobile device forensics
- Network forensics
- Live acquisition forensics
- Image/video/audio forensics
- Database forensics
Computer and mobile device forensics involve acquiring, analyzing, and reporting digital evidence found on computers such as desktops and laptops, or mobile devices such as smartphones or tablets.
Network forensics involves monitoring, acquiring, analyzing, and reporting activity over a given network.
Image, video, and audio forensics involves acquiring, analyzing, and reporting data evidence gleaned from images, videos, and audio recordings. This evidence should confirm the files' authenticity using metadata or specialist analysis tools.
Live acquisition forensics involves acquiring, analyzing, and reporting data evidence from computer memory (RAM).
RAM is volatile, meaning it only stores information while the system is powered on. So, forensics on RAM can only happen if the device was “live” (powered on) from the time of the event(s) you need to analyze.
Cyber Forensics Stages
Most types of digital forensics investigations follow the same six-part process.
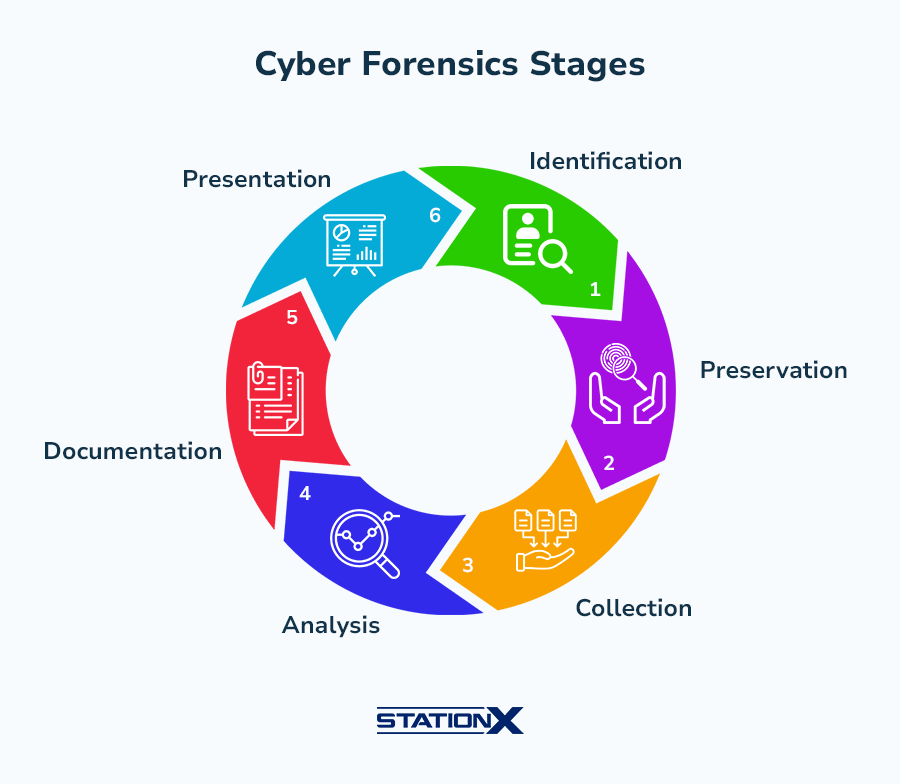
First, you find and note what evidence you need to analyze, such as a suspect’s digital devices or key evidence on one of them. Then, you secure and preserve this device or data and ensure it’s safe from tampering.
Following this, you collect all the digital evidence you might need for your investigation, often using specialist data retrieval and analysis tools. After this, you narrow down the data you’ve collected and analyze it to draw conclusions about the incident or crime.
Then, you put together your documentation and present it. You should’ve been carefully documenting the process throughout, but at the end of your investigation you should ensure your documentation is systematic, thorough, and replicable.
Finally, you can present a report that summarizes your conclusion.
FREE Cyber Security Career Guide
Thinking of a career in cyber security? Our Cyber Security Career Guide walks you through the industry landscape, skill-paths, certifications, and realistic timelines to become job-ready.
Cyber Forensics Tools
There are tons of cyber forensics tools for different jobs. Some are free and open-source (FOSS), and some are expensive and proprietary. Others, such as some of Cellebrite’s products, are physical devices only sold to law enforcement.
The digital forensics professional might want some of the following in their toolkit:
- File analysis tools
- Disk capture tools
- Registry analysis tools
- Network analysis tools
- Database analysis tools
More specifically, some of the most common digital forensics tools are:
- X-Ways Forensics: Data analysis and recovery software
- EnCase: Software for collecting and uncovering data from multiple sources
- Forensic Toolkit (FTK): Software that scans hard drives to find information
- WindowsSCOPE: Software for reverse engineering and memory forensics on Windows machines
- Universal Forensics Extraction Device (UFED): A series of products produced by Cellebrite for the use of law enforcement to extract and analyze data from mobile devices
- Radare2: Software for reverse engineering binaries, such as malware executables
What Does a Digital Forensic Investigator Do?
Digital Forensic Investigators most commonly work for or with law enforcement, using digital forensic science tools and techniques to extract, analyze, and report on data from a suspect’s device that’s relevant to an ongoing criminal investigation.
They might, for instance, be called upon to retrieve data from a suspect’s computer that shows they were planning to commit an illegal act.
The investigator will also assess and ensure the authenticity of such data and provide documentation of their findings that demonstrates clear data integrity so that the evidence can be used in court.
Digital Forensic Investigators working for or with law enforcement might:
- Disassemble devices to access internal components—such as hard drives—for analysis
- Use specialist hardware and software to collect data from digital devices
- Use specialist software to analyze data and find evidence for a criminal investigation
- Use techniques and tools to validate the authenticity of evidential data
- Carefully document everything they do with the devices and data
- Produce an official report on the evidential data once the analysis is complete
They can, of course, also work for private organizations.
In the corporate world, they might analyze malware or network data related to an intrusion to help an organization understand why, how, and by whom they were compromised.
They might work as part of the organization’s Security Operations Center (SOC), perhaps performing general blue team tasks until a breach occurs and they employ their digital forensics skills. Otherwise, they might be a contractor hired to work closely with the SOC after an incident.
Usually, corporate digital forensics professionals will form part of an incident response team.
A corporate Digital Forensic Investigator might spend time following the procedures described in the organization’s incident response plan, systematically analyzing data relevant to an intrusion or cyber security incident while documenting the process and eventually producing a report.
Depending on the incident response process, this analysis might involve reverse engineering malware.
Cyber Forensics Certifications and Skills
If you want a job in cyber forensics, the best thing you can do is get as much experience as possible. Thankfully, many cyber forensics certifications give you not only digital forensics skills but also hands-on experience.
Here are some of the most popular certifications for cyber forensics:
The first two of these, in particular, are of interest.
The CCE certification is not only awarded by the International Society of Forensic Computer Examiners (ISFCE), but it’s also the cheapest of the bunch at just $485 for the initial testing process.
The CFCE certification, on the other hand, is of interest because it’s a respected certification that demonstrates a lot of hands-on experience. Candidates solve practical problems and document their findings with a coach's help over 30 days, then solve a hard drive practical problem over 30 days, and finally take a knowledge-based practical exam.
Many other digital forensics certifications are valuable and well-respected, and all of them should help you toward gaining the knowledge and skills you’ll need for a real digital forensics role. The skills you might need include:
- Retrieving data from drives and systems
- Analyzing file systems
- Documenting your process and results
- Using specialist software such as FTK or UFED
- Writing official reports for legal teams
- Analyzing and reverse engineering software
- Scripting in languages like Python or PowerShell
Want to take your first steps into cyber security? Here’s how to get started: How to Get Into Cyber Security: A Quick Guide
Cyber Forensics Salary and Jobs
Law enforcement Cyber Forensics roles tend to pay less than private ones, often starting between $50,000 and $75,000 USD, according to Computer Forensics Recruiter.
However, more experienced digital forensics practitioners can earn north of $100,000 even in a state job, especially if they work as a government contractor. The most common job title for state roles like these is Digital Forensics Investigator.
CompTIA CySA+ Voucher
Prove your defense analyst skills with a discounted CompTIA CySA+ Voucher. Save up to 30% and earn your certification with an authorized CompTIA partner.
In the private sphere, digital forensics jobs are usually mid-to-late-career cyber security roles targeted at cyber security professionals who already have some on-the-job knowledge and experience, for example as a SOC analyst or incident response analyst. As such, they tend to pay more than an entry-level cyber security salary would.
Here are three of the main corporate cyber forensics job titles:
- Digital Forensics Analyst
- Cyber Threat Hunter
- Digital Forensics and Incident Response Specialist
Indeed shows over 1,000 jobs in the United States for “digital forensics.”
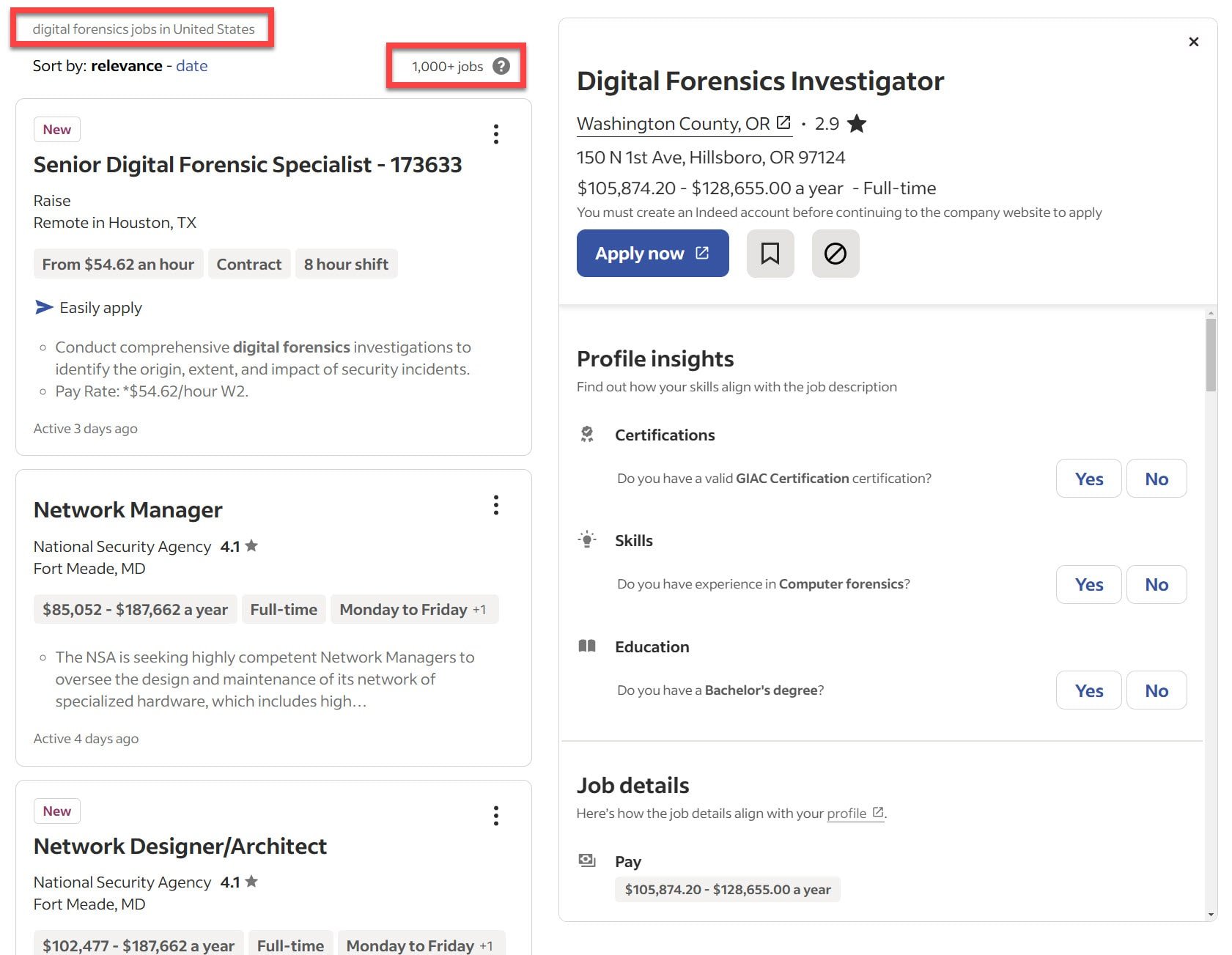
According to ZipRecruiter, a Digital Forensics Analyst—one of the most common digital forensics job titles—can expect an average salary of $74,125 USD.

Here are the job and salary data for three of the most common cyber forensics job titles in the private sector.
| Number of Jobs (Indeed) | Salary (ZipRecruiter) | |
| Digital Forensics Analyst | 300+ | $74,125 |
| Cyber Threat Hunter | 100+ | $112,871 |
| Digital Forensics and Incident Response Specialist | 50+ | $78,520 |
Curious about how this stacks up against the cyber security field in general? Read our guide:
Conclusion
Digital forensics is an exciting field in cyber security which appeals to many people’s fact-finding curiosity and desire to make an impact in the world.
Digital or cyber forensics professionals collect and analyze digital data from a device, network, or system, documenting and reporting their findings. Most digital forensics jobs are found working for law enforcement, working on finding and documenting evidentiary data for ongoing criminal cases.
Some, however, are found in the private sector, working for organizations to analyze malware or breached network data to discover the culprit and how they managed to bypass security measures.
If this sounds like the career for you, check out the courses below, which cover much of what you need to know to become proficient in digital forensics. And if you’re worried about keeping on track with your learning, try out the StationX Master's Program.
The Accelerator Program gives you access not just to 30,000+ courses, labs, and practice tests but also a community of like-minded prospective cyber security professionals. You can even access a mentorship program that lets you speak to real cyber security experts and get career advice.
You can get lifetime access to the CompTIA CySA+ Training Bundle, which includes a comprehensive study guide course, 8 full-length practice tests, 16 online quizzes, and flashcards to reinforce key concepts.
This CompTIA CySA+ Training Bundle (CS0-003) includes:




