Cyber security is a hot topic right now. There are huge data breaches every week, lucrative job opportunities, and a need for skilled professionals. With everyone trying to jump into the industry or move up the ladder, you need something to set yourself apart. Using Python for cyber security can be just that.
Python is a general-purpose programming language that you can use to build cyber security tools, automate repetitive tasks, and even create fully-fledged exploits! It can be used across many different areas of cyber security, from penetration testing to incident response. The best part is that the language is relatively easy to learn and use for beginners.
Let’s explore how you can use Python for cyber security and add a boost to your existing skillset.
What Is Python?
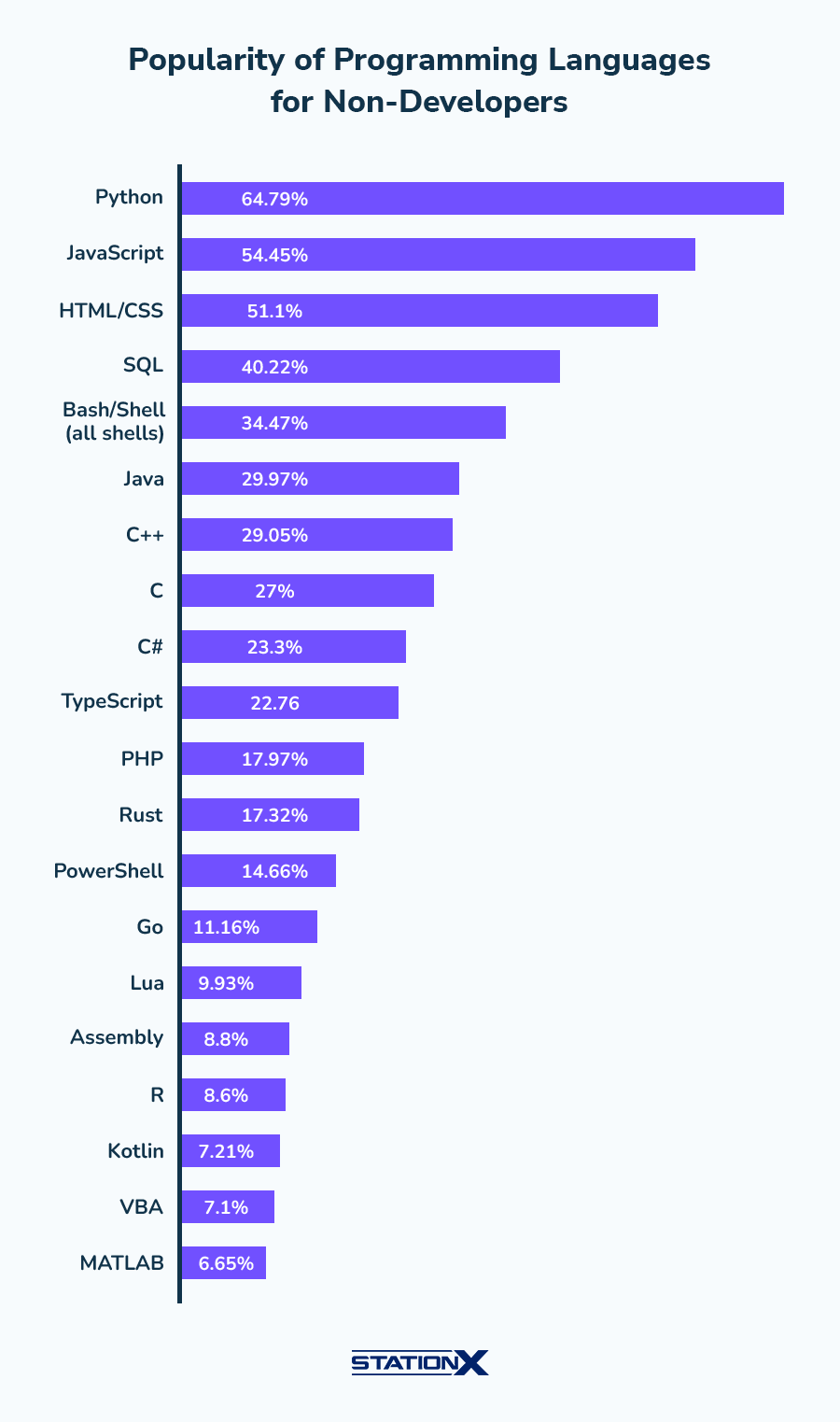
Python is a high-level, interpreted, and general-purpose programming language that has seen a steep rise in popularity due to its simple syntax and rich feature set. The language was created in 1991 by Guido van Rossum and is one of the most widely used programming languages today, with 49% of developers using it.
Only the web technologies JavaScript and HTML/CSS are more popular than Python with developers.
Python is the language taught to most people who are interested in learning programming due to its readability, simplicity, and feature set. The language supports many key components of object-oriented programming and can be used to create anything from basic scripts to commercial websites to AI algorithms.
Why Is Python Popular?
The Python programming language is simple, easy to use, and incredibly powerful. This has seen the programming language grow tremendously in popularity, with many modern programming projects and tools choosing to adopt the language.
That said, there are even more reasons to choose Python. Let’s take a look at those:
- Readability: Python code is very readable. The language uses indentation, whitespace, and clean syntax to make it easy for programmers to write complex functionality in very few lines of code.
- Interpreted: Python scripts are executed at runtime. This means you don’t need to compile your code, making development fast and flexible.
- Versatility: Python supports different types of programming paradigms, has an extensive collection of libraries and frameworks for various applications, and offers cross-platform support for Windows, Mac, and Linux.
- Large standard library: Python has a comprehensive standard library that comes with the language out of the box. This means you don’t need to spend time writing code for common functionality, you can focus on your particular use case.
- Dynamically typed: Variable types are determined at runtime in Python so you can write code faster.
- Supportive community and complete ecosystem: Python has a large community of contributors who regularly improve the language by updating the open-source backend, adding third-party python libraries and tools to enhance the language’s capabilities, or creating training materials.
- Garbage collection: Python has a built-in garbage collector that handles all your memory management needs. You don’t need to worry about memory allocation or complex memory management problems like you have to in other languages like C++ or Rust.
These reasons make Python a compelling choice for any developer and a great option for cyber security professionals.
You can learn more reasons why Python is so popular and why you should learn it in The World’s Most Popular Coding Language? Reasons to Get to Grips with Python…
Python for Cyber Security
Now you know the reasons to use Python. Let’s look at how Python is used in cyber security to help professionals automate tasks, streamline their workflows, and build awesome tools.
Ethical Hackers/Penetration Testers
A penetration tester is someone who simulates a cyber attack against a computer system, network, or application to uncover vulnerabilities or security gaps that need to be mitigated. They often use Python to create or modify exploits and automate their testing activities by scripting a tool’s execution or chaining multiple tools together.
Python has an extensive ecosystem of third-party libraries that are perfect for automating security testing, such as requests for testing APIs or Scapy for web scraping. The language can also be integrated with popular penetration testing tools like Nmap, Metasploit, and Burp Suite.
To learn more about how Python can be used for penetration testing, read Hacking With Python: Unlocking Python’s Potential.
Security Analysts
A security analyst is responsible for defending an organization’s computer systems and network from cyber attacks. This requires them to monitor security tools and parse through logs to investigate malicious activity. Python can help them do this by automating log parsing, using algorithms to detect network anomalies or suspicious user behavior, and automating response actions like isolating systems.
Python has extensive data analysis libraries like Pandas and machine learning libraries like PyTorch that security analysts can use to discover anomalies. They can also use Python to interact with API, such as the Endpoint Detection and Response (EDR) tool CrowdStrike Falcon’s FalconPy or VirusTotal’s vt-py library for quicker response and investigation.
New cyber security entry-level certs like Google’s Cybersecurity Certificate teach Python as part of their curriculum. This shows the importance of Python for cyber security and for security analysts in particular.
Incident Responders
Incident responders are professionals who you call in when a security incident happens. They are responsible for containing, eradicating, and recovering from a cyber attack or data breach. Much of their work involves collecting, processing, and analyzing forensic data from system and network log files. A scripting language like Python is incredibly useful for this.
Python’s ability to handle different data formats and third-party libraries that support log parsing allows incident responders to automate time-consuming portions of their workflow so they can focus on triaging and remediating incidents. The YARA library for detecting malware, the pySigma library for detecting malicious activity in log files, and the PyMISP library for querying threat intelligence are all useful for incident responders.
Cyber Security Researchers
Security researchers are dedicated to discovering vulnerabilities, threats, and risks in computer systems, applications, and networks. They identify weaknesses, develop solutions to exploit them, and then report what they find to security vendors so the issue can be remediated.
Python is a useful tool in the arsenal of a cyber security researcher. Third-party libraries like pwntools and Atheris allow them to automate the simulation of complex cyber attacks to find vulnerabilities. This process is known as fuzzing and is a popular method used to discover potential vulnerabilities.
Network Security Engineers
A network security engineer is responsible for designing, implementing, and maintaining a secure network infrastructure for an organization. They must continually ensure information confidentiality, integrity, and availability within an organization’s networked environment.
Python has become a must-learn language for network security engineers in the past several years. Infrastructure as Code (IaC) has become the standard for many organizations due to its high availability, rapid deployment speeds, and security. This means network security engineers must know how to programmatically deploy and roll out changes to network infrastructure using Python and other technologies like Terraform and Ansible.
Cryptographers
Cryptographers are cyber security professionals who secure communication and data using cryptographic algorithms. These algorithms are essential for the confidentiality, integrity, and availability of data across the network (in transit) and on computer systems (at rest).
Python is a great language for prototyping and testing cryptographic algorithms using libraries like PyCryptodome, Cryptography, and Fernet. Although you shouldn’t write your crypto algorithms in Python (you want a lower-level language like C or C++), Python’s mathematical libraries, simplicity in handling binary and hex data, and automation capabilities make it ideal for testing or simulating cryptographic attacks.
If you want to learn more about creating cryptographic algorithms, read Python Data Structures Cheat Sheet: The Essential Guide. You need to know data structures to write programming algorithms.
Vulnerability Assessors
Vulnerability assessors identify and assess vulnerabilities in computer systems, networks, applications, and infrastructures. Similar to penetration testers, they are responsible for finding weaknesses that could be exploited by malicious attackers (unlike penetration testers, they don’t try exploiting these vulnerabilities).
Vulnerability assessors must quickly identify and assess vulnerabilities in hundreds or thousands of systems. This is where Python is invaluable. Python allows vulnerability assessors to automate the scanning and analysis of systems for vulnerabilities by creating custom python scripts to check known weaknesses and integrating different vulnerability assessment tools like Nmap, Nessus, and Greenbone Vulnerability Manager (OpenVAS).
Forensics Specialists
Forensic specialists collect, analyze, and preserve digital evidence for cyber security and legal investigations. They play a crucial role in uncovering evidence related to cybercrimes and data breaches by working with other cyber security professionals to recover, examine, and document digital evidence present on computer systems and within network logs.
Python allows forensic specialists to automate many of the tedious and time-consuming processes that are part of their job. For instance, you can use Python to build tools that automate the gathering and processing of digital evidence, recover data from computer systems, and parse different file formats during investigations.
Malware Analyst
A malware analyst is a cyber security professional trained to study and analyze malicious software (malware). They are responsible for understanding, identifying, and providing information to security analysts that can be used to mitigate the impact of malware and protect the corporate environment.
The automation capabilities of Python make it an ideal tool for streamlining a malware analyst’s workflow. They can use it to automate routine tasks (e.g., setting up a malware analysis environment, file handling, and data extraction), for basic static malware analysis (e.g., checking file hashes, PE headers, etc.), and scripting tasks in specialists malware analysis tools together like Ghidra, IDA Pro, and x64dbg.
How Do I Start Learning Python?
Despite Python being one of the easiest languages to learn, it can be daunting for those new to programming. Here are some tips and advice to help you start your learning journey.
Things to do when learning Python
- Build projects: Building your own projects to fulfill your use case is the best way to learn about Python and what it can do. For instance, build a project to automate repetitive tasks at work (e.g., running multiple Linux commands, working with data in a spreadsheet, or finding out what the weather is like today).
- Share what you are learning: Write blog posts or social media updates about your learning and share this knowledge with others. Teaching someone else what you are learning helps you fully grasp complex concepts.
- Read other people’s code: It is useful to see how others with more experience write, structure, and organize their code. You will gain insight into improving your Python projects.
- Code every day: Consistent practice is key to learning any new topic. Doing a little bit of coding daily will develop the muscle memory and neurological synapses needed to master Python.
Mistakes to avoid when learning Python
- Trying to learn another language simultaneously: Stick to learning one language at a time. Additional language features, components, and syntax will only confuse you and slow your learning.
- Skipping the fundamentals: Trying to jump into a complex project without having a solid understanding of programming fundamentals will hamper development and leave you frustrated.
- Not practising what you are learning: You need to practise what you are learning in tutorials and courses so that you can begin creating your own projects, custom scripts, and tools.
- Not seeking help: Trying to solve everything by yourself can be incredibly frustrating and take a long time. Find a study buddy, community, or mentor who can help you out when you get stuck.
Conclusion
Python is a powerful programming language that will boost your skillset and make you very valuable in cyber security. It can be used to automate time-consuming tasks, augment your workflow with its versatile capabilities, and build complete cyber security tools.
Python’s popularity has surged over the past several years due to its easy-to-use nature, simple syntax, and rich feature set. You have discovered how Python can be used in many cyber security professions, from front-line defender roles like security analysts to heavily scientific and mathematical disciplines like cryptography.
You can learn Python for cyber security with the StationX Master's Program. You will get exclusive certification advice, mentorship, and over 30,000 classes and labs to help you take your career to the next level. Some of the courses included are listed below:







