Are you looking for the top cyber security blogs, and do you want to stay up-to-date and informed on the latest threats? Do you want to find blogs that can help to elevate your career?
In a world where cyber threats are everywhere, security goes beyond firewalls and anti-viruses. Blogs are a great way to stay informed and can also help hone the skills needed in cyber security.
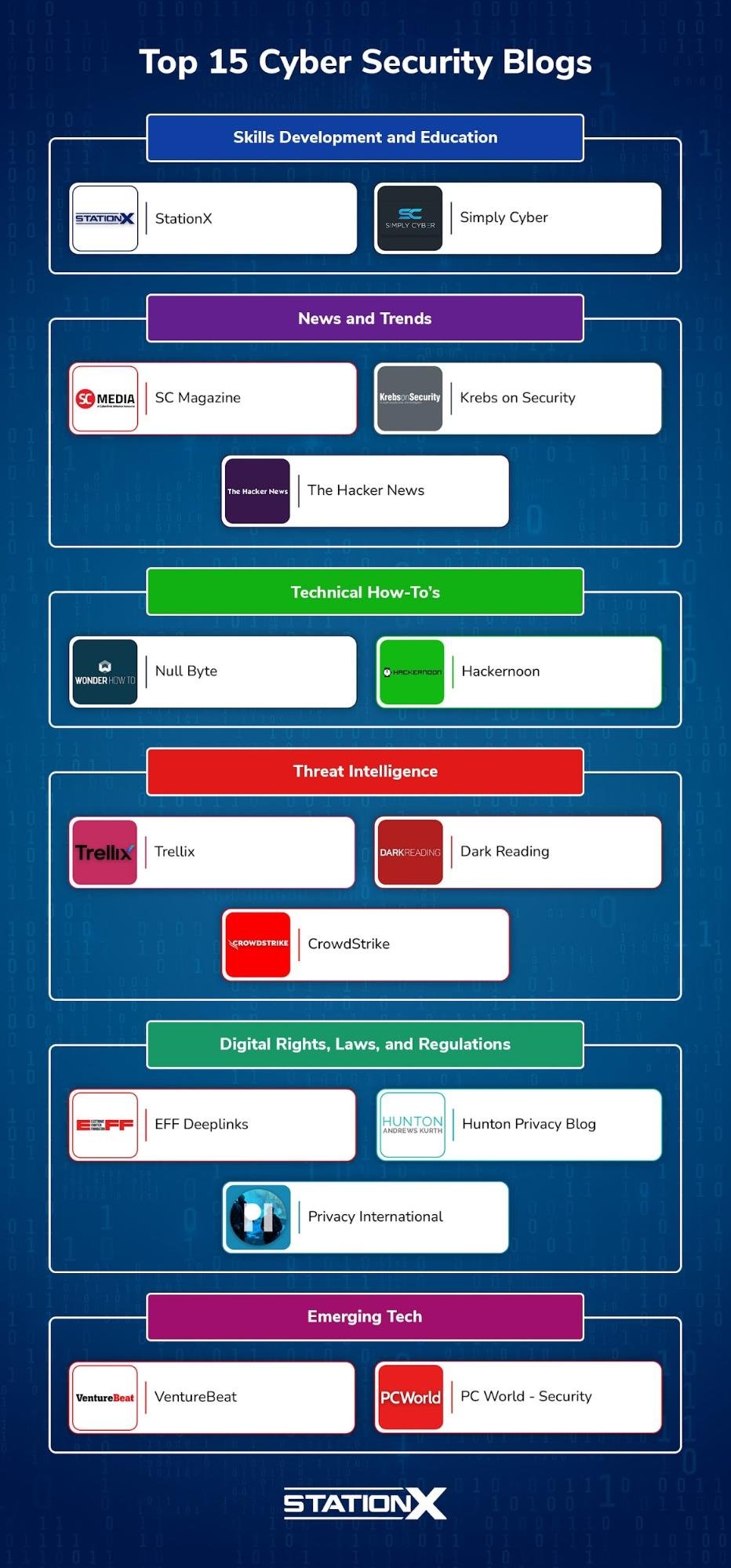
This article breaks down the best cyber security blogs into six categories, presenting you with options for skills development and education, news, how-to’s, threat intelligence, digital rights and regulations, and emerging tech.
Join us as we present you with the best cyber security blogs and arm yourself with the knowledge and skills necessary to confront the threats of tomorrow.
| Skills Development and Education | Threat Intelligence |
| StationX | Trellix |
| Simply Cyber | Dark Reading |
| News and Trends | CrowdStrike |
| SC Magazine | Digital Rights, Laws, and Regulations |
| Krebs on Security | EFF Deeplinks |
| The Hacker News | Hunton Privacy Blog |
| Technical How-To’s | Privacy International |
| Null Byte | Emerging Tech |
| Hackernoon | VentureBeat |
| PC World-Security |
Skills Development and Education
The development and education category contains blogs that will help you develop the skills needed to succeed in cyber security.
StationX Cyber Security Blog
The StationX blog is part of the StationX company, an online cyber security training and career development platform providing over 1,000 classes, virtual labs, and practice exams to help you master in-demand cyber security skills.
The blog offers a diverse range of articles for individuals interested in pursuing a career in cyber security. And offers a variety of tips, career guidance, and tutorials aimed at helping you expand your skills.
Articles span a range of categories, including Artificial Intelligence (AI), Careers and jobs, Certifications, Hacking, IT Fundamentals, Cheat Sheets, Networking Security, and Statistics, among others.
Featured Articles:
- How to Use Burp Suite: Discover & Master Powerful Features. Learn how to use the many features of this web application pentesting tool effectively.
- CISSP Cheat Sheet (Updated for Latest Exam). This cheat sheet summarizes key concepts to help you prepare for the CISSP exam.
We highly recommend exploring the StationX blog. Whether you've been in cyber for a while or are new to the field, you'll find valuable information to help you on your journey.
Simply Cyber
The Simply Cyber Blog is run by Dr. Gerry Auger, a professor, author, and speaker, who is a seasoned cyber security professional with nearly two decades of experience, holding a Ph.D. in Cyber Operations and multiple industry certifications.
The blog provides guidance and resources for individuals looking to start a career in cyber security. The content on the blog is primarily delivered through videos, each accompanied by a brief description that outlines the video's focus.
Simply Cyber covers various topics, including tips for landing a job in cyber security, guidance on setting up a home SOC analyst lab, insights on the role of a cyber security analyst, and discussions on different entry-level cyber jobs and what they entail.
Featured Articles:
- Overcoming Imposter Syndrome in Cybersecurity: Your Journey to Success. Learn strategies to help overcome imposter syndrome with expert advice and learn to embrace your strengths.
- Uncover the Secrets of a Home SOC Analyst Lab! [Step-by-Step Walkthrough]. Learn how to set up your own SOC lab at home.
We like Simply Cyber for its practical advice and insights to help you in your cyber security career journey.
News and Trends
The next blogs provide you with the latest news and trends happening in the world of cyber security.
SC Magazine
SC Magazine is a top source for infosec news. It’s a blog by SC Media, a cyber security news company that has been around for over 30 years. The blog provides current news on cyber security issues, trends, and incidents.
Topics covered include application security, asset management, cloud security, data security, and more, aiming to keep you informed on the latest advancements and challenges in cyber security.
Featured Articles:
- How to run a cybersecurity company during the current crisis in the Middle East. In times of crisis, business leaders must learn to lead compassionately and be vigilant of rising threats.
- Cybersecurity Awareness Month 2023: The shift to an identity-first world. What are the challenges and strategies as perimeter security shifts to a more identity-focused approach?
We like SC Magazine for its coverage of cyber security topics and focus on current events, making it a reliable source for staying updated.
Krebs on Security
The blog Krebs on Security, authored by Brian Krebs, is a well-regarded source of in-depth security news and investigations.
Krebs, a former Washington Post reporter, got into computer security by accident when his home network was hacked by a Chinese hacking group. This incident made him intensely interested in computer security, and he decided to learn as much as possible about the subject.
The blog is known for its investigative reporting on cyber security issues. Krebs dives into various topics, unraveling complex scams, frauds, and cyber-attacks.
Featured Article:
- The Fake Browser Update Scam Gets a Makeover. Krebs discusses a scam in which attackers trick users into updating their browsers only to infect their systems with malware, showcasing a detailed investigation into the mechanisms of the scam.
We like Krebs on Security for its deep investigative reports; it's a trusted source for uncovering newsworthy security issues.
The Hacker News
The Hacker News is a prominent resource for cyber security news, serving as a leading source for timely and pertinent updates from the world of cyber security, along with valuable insights into the latest threats and solutions.
The blog features articles on various issues, such as data breaches, cyber attacks, vulnerabilities, etc.
Featured Articles:
- Researchers Uncover Malware Posing as WordPress Caching Plugin. Cyber security researchers have uncovered a new malware disguised as a WordPress plugin to create admin accounts and control a site remotely.
- Europol Dismantles Ragnar Locker Ransomware Infrastructure, Nabs Key Developer. Law enforcement agencies across numerous countries coordinated to takedown ransomware group Ragna Locker’s infrastructure and arrest a “key” target.
We like The Hacker News as a comprehensive resource for anyone interested in staying updated with the ever-evolving cyber security landscape, offering you a blend of news, insights, and community engagement.
Technical How-To's
Our next recommendation of blogs will teach you specific hands-on techniques for tackling real-world cyber security challenges.
Null Byte
The Null Byte blog is on the WonderHowTo platform; WonderHowTo is a platform that hosts a variety of blogs focusing on different topics, including technology, food, gadgets, and more. It aims to provide "Fresh Hacks For a Changing World" as per its tagline, offering numerous tutorials, guides, and articles across a number of interests.
Null Byte is dedicated to fostering a learning environment for aspiring white-hat hackers and individuals interested in security awareness.
The blog covers a wide range of ethical hacking and cyber security topics. Some of the topics include password hacking, social engineering, and Wi-Fi hacking, among others.
Featured Articles:
- Write Your Own Subdomain Enumeration Script for Better Recon. A step-by-step guide to creating your very own subdomain enumeration script in bash.
- Crack Shadow Hashes After Getting Root on a Linux System. Learn how to crack the shadow hashes found inside of a Linux system once you’ve become root.
Null Byte is a great resource for individuals looking to jump into ethical hacking, offering a blend of tutorials and access to additional learning resources.
Hackernoon
The cyber security section of the Hacker Noon blog provides an array of technical "How-To" articles, insights, and guides related to security practices, tools, and trends.
Hacker Noon is a platform where articles on various topics, such as software development, blockchain, artificial intelligence, and cyber security, are shared.
The blog discusses security best practices and awareness topics, avoiding scams, practical guides, and technical hacking tutorials.
Featured Articles:
- 3 Flipper Zero Hacks to Wow Your Friends (and How They Work). Learn three hacks using the Flipper Zero, such as controlling TV’s.
- How to Make a Malicious USB Device and Have Some Harmless Fun. Learn how to create a BadUSB drive that will ultimately open a reverse shell.
We like Hackernoon for its emphasis on practical, hands-on tutorials. It’s a great resource for anyone looking to develop or expand their technical skills in areas like ethical hacking.
Threat Intelligence
The following blogs provide you with the latest in threat intelligence news, ensuring you're always updated on emerging cyber threats.
Trellix
The Trellix blog provides insightful articles on threat intelligence, security practices, and cyber security trends. Trellix is a security company that provides various solutions and services.
The blog provides technical analysis of new malware strains, vulnerabilities, and tactics, engaging in discussions on topics like endpoint security, network defense, threat intelligence, and data protection. It aims to keep CISOs, security analysts, and IT teams informed on emerging security issues.
Featured Article:
- CISOs: Cyber Criminals Don’t Want You to Know This One Weird Trick to Alleviate Insider Threat Nightmares. This article discusses the insider threat kill chain and offers detailed countermeasures to protect organizations from malicious insiders.
We like the Trellix blog's blend of thorough threat intelligence analyses, practical security insights, and diverse expert perspectives.
Dark Reading
Dark Reading is a prominent Threat Intelligence blog nested under the wing of Informa Tech. This blog aims to serve as a center for cyber security professionals, providing a wealth of resources to assist in managing the balance between data protection and user access.
Unlike generic security blogs, Dark Reading pivots towards providing real-time threat intelligence, sharing the dynamics of emerging threats, vulnerabilities, and activities in the cyber domain.
Featured Articles:
- Patch Now: APTs Continue to Pummel WinRAR Bug. The article spotlights the persistent exploitation of a WinRAR bug by state-sponsored cyber espionage actors.
- Iran-Linked 'MuddyWater' Spies on Mideast Gov’t for 8 Months. Shedding light on a prolonged espionage campaign orchestrated by state-sponsored threat actors.
We like Dark Reading as a top source for threat intelligence, offering a real-time look into the evolving landscape of cyber threats.
CrowdStrike Blog
CrowdStrike's blog is a collection of cyber security posts from the CrowdStrike company recognized for its cloud workload and endpoint security solutions. The blog is a resource for sharing real-time threat intelligence, discussing topics from endpoint and cloud security to adversary counter operations and beyond.
Featured Article:
- CrowdStrike vs. Microsoft Defender for Endpoint: A Cybersecurity Leader Compares EDR Tools. The article presents a comparative analysis between CrowdStrike's and Microsoft Defender's endpoint detection and response (EDR) tools, serving as a guide on the distinctive strengths and weaknesses of each tool.
We like the CrowdStrike Blog for its real-time analysis. The blog is an excellent resource for those needing immediate information on emerging threats.
Digital Rights, Laws, and Regulations
The following blogs deal with rights, laws, and regulations concerning the cyber security industry.
EFF Deeplinks
The Deeplinks Blog is orchestrated by the Electronic Frontier Foundation (EFF), a leading organization defending civil liberties in the digital world. This blog presents critical issues at the crossroads of technology and legality.
With issues like digital rights and privacy. The blog covers topics like surveillance, free speech, privacy, patent reform, fair use, net neutrality, and more.
Featured Articles:
- Adtech Surveillance and Government Surveillance are Often the Same Surveillance. Examining the intersection of advertising technology and government surveillance and its impact on privacy.
- Social Media Platforms Must Do Better When Handling Misinformation, Especially During Moments of Conflict. Analyzes the role of social media platforms in misinformation handling during political and social conflicts.
We like the Deeplinks blog as it provides news and actionable advice on preserving digital rights, making it essential reading for those interested in the legal aspects of cyber security.
Hunton Privacy Blog
The Hunton Privacy Blog is administered by the legal firm Hunton Andrews Kurth LLP, which is recognized globally for its profound expertise and exceptional client service in privacy and cyber security law.
The blog provides various posts addressing recent legal developments, rulings, and discussions related to privacy and cyber security.
If you want to understand the intersection of law, privacy, and cyber security. The blog helps to keep you updated on the evolving legal landscape surrounding data protection.
Featured Article:
CIPL Releases Paper on Ten Recommendations for Global AI Regulation. CIPL (Centre for Information Policy Leadership) released a paper outlining ten recommendations for AI regulation focused on flexible, risk-based rules building on existing laws, organizational accountability, and robust regulatory oversight.
We like the Hunton Privacy Blog as It provides a legal perspective in an easy-to-understand format, ideal for those wanting to understand the regulatory landscape.
Privacy International
The Privacy International blog on Privacy International's website is a collection of posts addressing critical privacy and digital rights issues. Since 1990, Privacy International has been promoting and defending the right to privacy across the globe, challenging the power abuses by governments and corporations exploiting technology for surveillance and control.
Their articles cover topics like digital device seizures at borders, global AI regulation, digital identity systems, and the implications of various cyber security laws and policies.
Featured Article:
- The 'Identity Crisis' around the world, discusses the challenges and risks associated with technology-driven ID systems being implemented globally.
We like Privacy International for its advocacy of privacy rights and resistance against the overreach by higher powers.
Emerging Tech
The blogs below are centered on emerging tech and how they may impact cyber security.
VentureBeat
The VentureBeat blog is a reputable source known for its coverage of technologies across different sectors. Started in 2006 by Matt Marshall, it covers various topics, from emerging tech in cyber security, AI, machine learning, and more.
The articles provide insight into how these technologies shape different sectors, including cyber security.
Featured Articles:
- Securing generative AI starts with sustainable data centers. The article discusses how cyber attacks aimed at stealing AI models and compromising infrastructure are increasing and provides strategies for securing data centers.
- How AI can help close IoT’s growing security gaps to contain ransomware. This examines how ransomware and cyber attacks targeting unsecured IoT devices and infrastructure are rising.
We like VentureBeat for Its well-researched articles on emerging technologies that provide you with insight into the future of cyber security.
PC World - Security
The Security section on PC World, a technology-oriented publication that provides reviews, news, tips, and feature articles on hardware, software, and other tech-related products, is a reputable source for understanding the link between emerging technologies and cyber security.
The blog discusses the advancements in security features, tools, and practices, shedding light on how these technologies shape the cyber security landscape.
Featured Articles:
- Best antivirus software in 2023: Keep your Windows PC safe from ransomware, malware, more. A breakdown of the best anti-virus solutions for Windows and one recommendation for Mac users.
- Best free VPN of 2023: It’s important to choose wisely. Don’t want to pay for a VPN service? A list of free recommendations.
We like PC World for Its timely articles on how emerging tech affects the security landscape.
Conclusion
We have provided you with recommendations for top cyber security blogs catering to different areas such as education, technical, threat intelligence, and more.
You should now have a great list of blogs to investigate and add to your daily reading list, creating a habit of continuous learning in the ever-changing world of cyber security. For more ways to learn and grow as a cyber security professional, join our StationX Master's Program today!







