Google dorks can help you uncover leaked passwords and sensitive data, let you view neighborhoods from unsecured cameras, access files not meant for you, and more. They’re challenging to master because:
- Valid dorks change often;
- Misuse can lead to serious legal repercussions;
- The dangers of accidentally inappropriate Google dorking discourage explorers from achieving mastery.
This downloadable cheat sheet will cover Google dorking commands and operators, search parameters, their combinations, questionable dorks, and how to prevent others from Google dorking your online resources. But Google can trace your dorks back to you, so take care in handling the clickable examples in this Google dorking cheat sheet.
Google Dorks Cheat Sheet Search
Search our Google dorks cheat sheet to find the right cheat for the term you're looking for. Simply enter the term in the search bar and you'll receive the matching cheats available.
- Google Dorks Cheat Sheet Search
- What Is a Google Dork?
- Legal and Ethical Implications
- Quick Notes
- Google Dorks Search Parameters
- Google Dorking Commands
- Google Dork Generator
- Google Dorks Operators
- Examples of Complex Google Dorks
- Google Dorking Cheat Sheet: Quick Tips and Best Practices
- How to Prevent Google Dorks
- Google Dork Cheat Sheet Conclusion
- Frequently Asked Questions
What Is a Google Dork?
A “Google dork” is an advanced Google search technique. “Google dorking” (aka “Google hacking”) is the activity of performing advanced searches on Google. You can combine different Google dorks to comb data otherwise inaccessible to ordinary users of Google search.
Google Dorking is a powerful OSINT (Open Source Intelligence) technique. By using specific search queries, ethical hackers can locate exposed credentials, discover misconfigured directories, identify admin login panels, and even find unsecured cameras.
These search operators transform Google into an incredibly powerful and free reconnaissance tool, making it an essential skill for penetration testers and cyber security professionals.
Legal and Ethical Implications
It’s crucial to recognize that Google Dorking has a fine line between ethical and unethical use, as well as between legal and illegal activities.
Google Dorking can uncover a treasure trove of information, but searching and interacting are two different things. While on Google, everything you are doing should be fine from a legal standpoint. Once you click a link, however, you are now interacting with the information, and that’s where things get murky.
If you end up somewhere you aren’t supposed to be, you could be breaking a local or international law. Remember, some files are intended to be hidden, and many cameras are supposed to be isolated.
The fact that they’re exposed isn’t that different from finding a weak password - it may be the organization's security failure, but that doesn’t grant you permission to download or interact with it any more than you have the authority to use that password to access someone else’s account.
Keep this in mind when Google Dorking - anything that doesn’t directly interact with the target or its staff is passive. Clicking into their website, even the homepage, is active. If you go somewhere they did not intend visitors to go, you could find yourself in trouble, so always get permission.
Quick Notes
- On a browser, if you make too many Google searches in a short time, Google requires that you unscramble garbled letters in an image called a captcha before you can proceed. Captcha completion can frustrate end users like you, but Google servers must nip denial-of-service cyberattacks in the bud.
- Unlike most cheat sheets, we cannot guarantee that the commands below will remain unchanged in perpetuity. Google updates its dorks continually, so deprecated techniques don’t appear here, even if you can find them elsewhere on the Internet.
Before You Begin Google Dorking
Google dorking is not a playground where you can flood commands to your heart’s content:
- Google limits your Google search rate from a single device.
- It may ban your IP if you issue too many queries.
- Abuse of dorks may have legal repercussions.
If you know you can’t resist having fun with it (and you will), you could work from Pagodo, which automates Google searching for potentially vulnerable web pages and applications on the Internet. It also lets you automate the rate at which your device issues Google dorks.
Regardless of how you use Google dorks, respect Google’s Terms of Service. Be careful.
Examples of Creepy Dorks
These dorks reveal vulnerabilities in websites, and their contents may be newsworthy depending on the zeitgeist.
For details on how the following commands work, refer to Text dorks, Google Dorks Operators, and Scope-Restricting Dorks.
| Examples | Description |
|---|---|
| inurl:"view.shtml" "Network Camera", "Camera Live Image", inurl:"guestimage.html", intitle:"webcamXP 5’" | Get web applications showing live webcam (online camera) footage. |
| "Not for Public Release" + "Confidential" ext:pdf | ext:doc | ext:xlsx | Get links to documents meant to be classified. Some come from governmental websites. |
| site:.hk & inurl:wp-login | Get login pages of WordPress sites ending in the notoriously unsafe domain “.hk” |
| ”index of” inurl:ftp secret | Get FTP servers you want to access containing the keyword “secret” |
Critical dorks performed on .env files yielding results such as:![filetype:env [and a sensitive parameter] - Google Search - Google Search results on .env files containing a sensitive parameter.](https://www.stationx.net/wp-content/uploads/2022/11/Google-Search-results-on-.env-files-containing-a-sensitive-parameter.png) | Popular web development frameworks use .env files to declare general variables and configurations for local and online dev environments, often including passwords. The dork used to produce the screenshot exposes database passwords. Hence it’s vital to keep .env files from being publicly accessible. (If you’ve read this cheat sheet in its entirety, you will be able to guess the dork used here.) |
This often-updated exploit database contains other Google dorks that expose sensitive information. Proceed with caution.
Google Dorks Search Parameters
A search parameter in a Google dork is the text string payload affixed to or used with the Google dorking command or operator. Without a suitable search parameter, Google treats the dork keyword as an ordinary query keyword at best and returns zero results at worst.
For example, in the search site:www.stationx.net, the domain “www.stationx.net” is the parameter. In (psychology OR computer science) AND design, the three subjects of psychology, computer science, and design are the parameters. In 16 F to C (converting a temperature from degrees Fahrenheit to Celsius), 16 is the parameter.
Search parameters include web domains, file extensions, numbers, and character strings with or without quotes.
Google Dorking Commands
As Google’s internal documentation on dorks frequently changes, the following is not an exhaustive list but a list of commands known to return meaningful results. Some of the given commands may be obsolete because they return similar results as a dork-free search. Deprecated commands don’t appear below.
Scope-Restricting Dorks
These help specify your target range of websites or data types. For example, in hunting for e-books, the Google dork “filetype:pdf” is indispensable.
If a command listed below ends with a symbol, include no space between the command and the parameter. The correct way to use each command is in the “Example usage” column. Otherwise, Google will treat the command as an ordinary search keyword rather than a dork.
| Command | Description | Example usage |
|---|---|---|
site: | Restrict search to a particular website, top-level domain, or subdomain. Additional query items are optional. | site:google.com, site:maps.google.com, site:.org tax return |
filetype:, ext: | Restrict the returned web addresses to the designated file type. Unlike most other dorks, this requires additional keywords in the search bar or will return no results. Here is Google’s official list of common file types it can search. Google also supports the file extensions db, log, and html. Nonetheless, searches on mp3 and mp4 with and without additional search terms have yielded no results. | filetype:pdf car design, ext:log username Compare with filetype:pdf, ext:txt, etc.   |
@ | Restrict search to a particular social platform. It supports popular platforms such as Facebook, Twitter, YouTube, and Reddit. A downside is it’s not as precise as the “site:” dork. | @twitter pentest, @youtube google dorking |
define: | Return definitions of a word or phrase | Compare define:privacy and a plain search on privacy. |
stocks: | Check the financial activity of a particular stock | stocks:META (Meta), stocks:gm (General Motors), stocks:pfizer |
movie: | Return information about any movie with the given title | Compare movie:"phantom of the opera" and "phantom of the opera". |
source: | Find reports from a Google News source. | source:cnn |
Informational Dorks
These dorks appear to work best if used as standalone commands, i.e., without additional query items.
| Command | Description | Example usage |
|---|---|---|
$ | Search for prices in USD ($). This also works for Euro (€), but not GBP (£) or Yen (¥). | ipad $329, iphone €239 |
cache: | Get Google’s last saved version of a particular website. A website snapshot like this is called “cache”. | cache:news.yahoo.com |
link: | Find pages linking to the given domain | link:www.stationx.net |
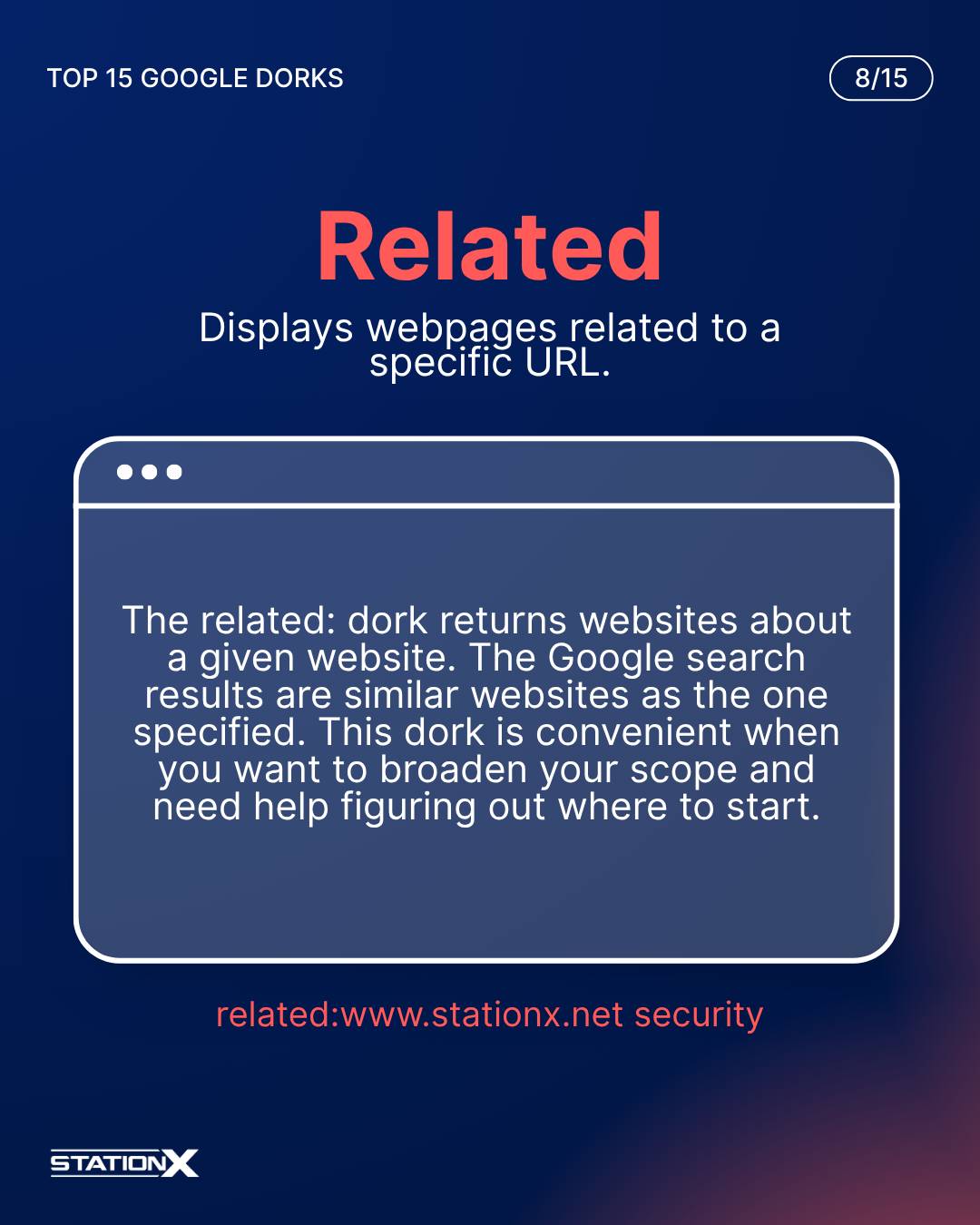
related: | Return websites related to the given website | related:harvard.edu, related:bbc.co.uk |
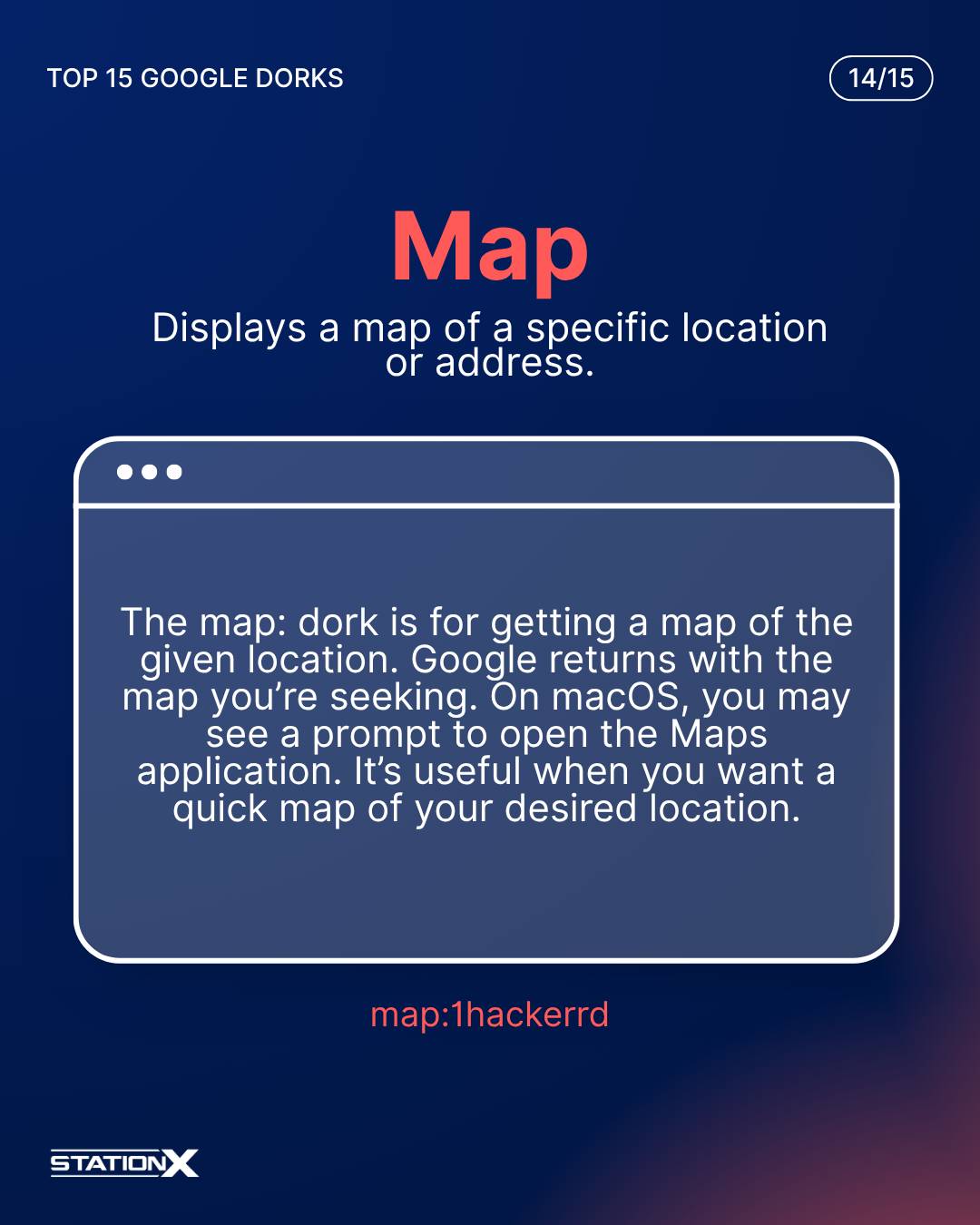
map: | Get a map of the given location | map:"new york" |
weather: | Get the weather of the given location | weather:london |
location: | Find information about a location. Results may be inconsistent. Google now treats “loc” (formerly an abbreviation of “location”) as a search term instead of a dork. | location:NY crime compared with NY crime. |
info:, id: | Return pages that convey information about the given website. Finding queries that gave different results with and without the “info:” / “id:” command was difficult. This command could still help you find the canonical, indexed version of a URL. Google now treats “id” (possibly shorthand for “info”) as a search term instead of a dork. | "babylon bee" vs info:"babylon bee": a politically conservative satire website in the US  Here’s how id:"babylon bee" treats “id” as a search parameter (bold text) in some results: ![An entry in [id:"babylon bee" - Google Search] - Example of Google Search treating "id" as another query keyword - Example of Google Search treating "id" as another query keyword](https://www.stationx.net/wp-content/uploads/2022/11/An-entry-in-idbabylon-bee-Google-Search-Example-of-Google-Search-treating-id-as-another-query-keyword-Example-of-Google-Search-treating-id-as-another-query-keyword.png) ![An entry in [id:"babylon bee" - Google Search] - Example of Google Search treating "id" as another query keyword](https://www.stationx.net/wp-content/uploads/2022/11/An-entry-in-idbabylon-bee-Google-Search-Example-of-Google-Search-treating-id-as-another-query-keyword.png) |
Google Dork Generator
Say goodbye to the hassle of trying to remember the exact syntax for your Google Dorks! With our Google Dork Generator, you can simply say what you need to do, and we will generate the Google Dork for you.
Text Dorks
These are helpful if you want to look for web pages containing certain text strings or follow particular patterns. For example, those familiar with the URLs of webcam apps, for example, use Google dorks similar to the first entry in this table to find camera footage to watch.
| Command | Description | Example usage |
|---|---|---|
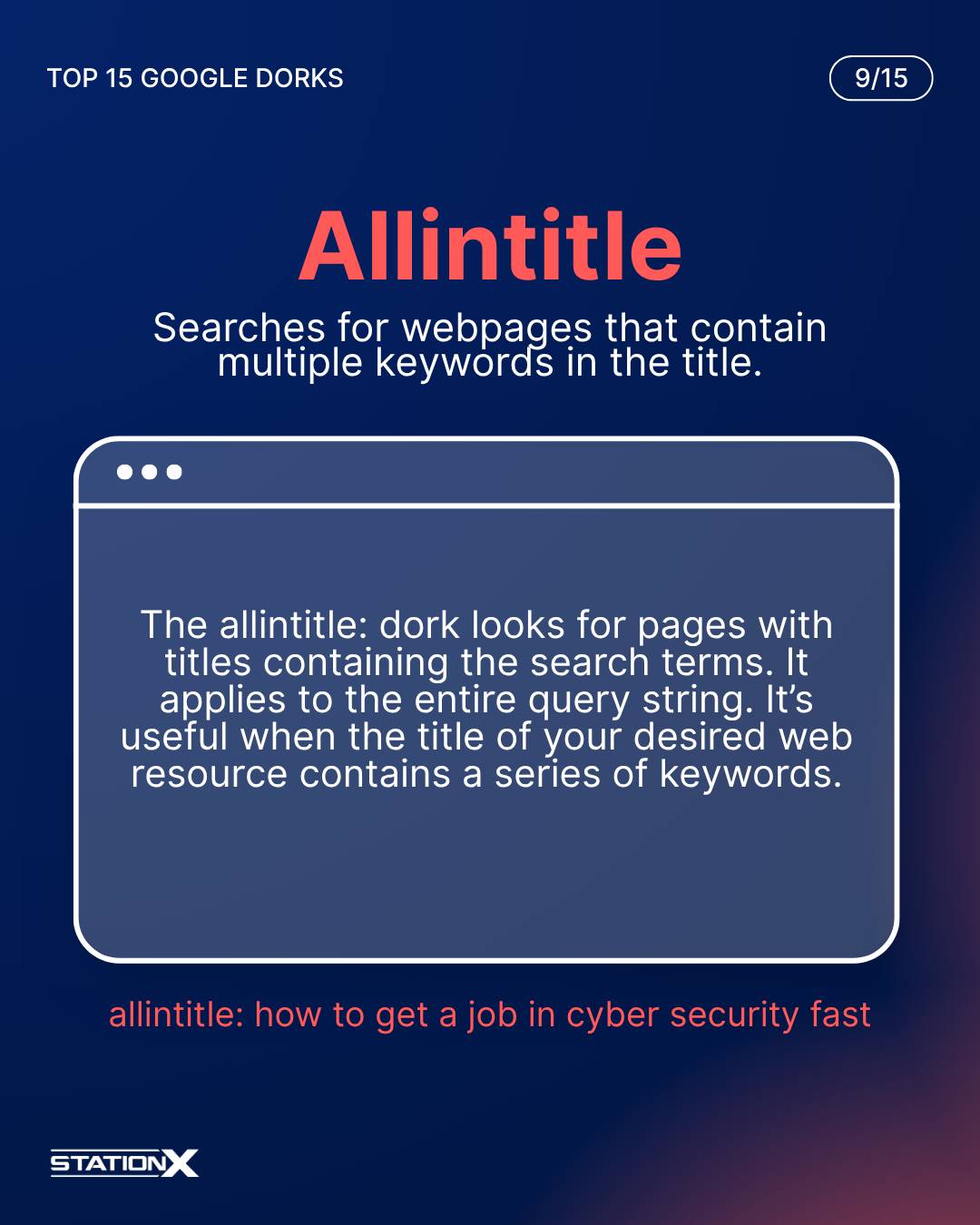
intitle:, allintitle: | Look for pages with titles containing the search terms. The dork “intitle:” applies to its search parameter only, while “allintitle:” applies to the entire query string. | intitle:toy story, intitle:"toy story", allintitle:"toy story", allintitle:toy story Compare the above with the number of search results of toy story and "toy story". |
inurl: | Find links containing the character string. | inurl:login.php |
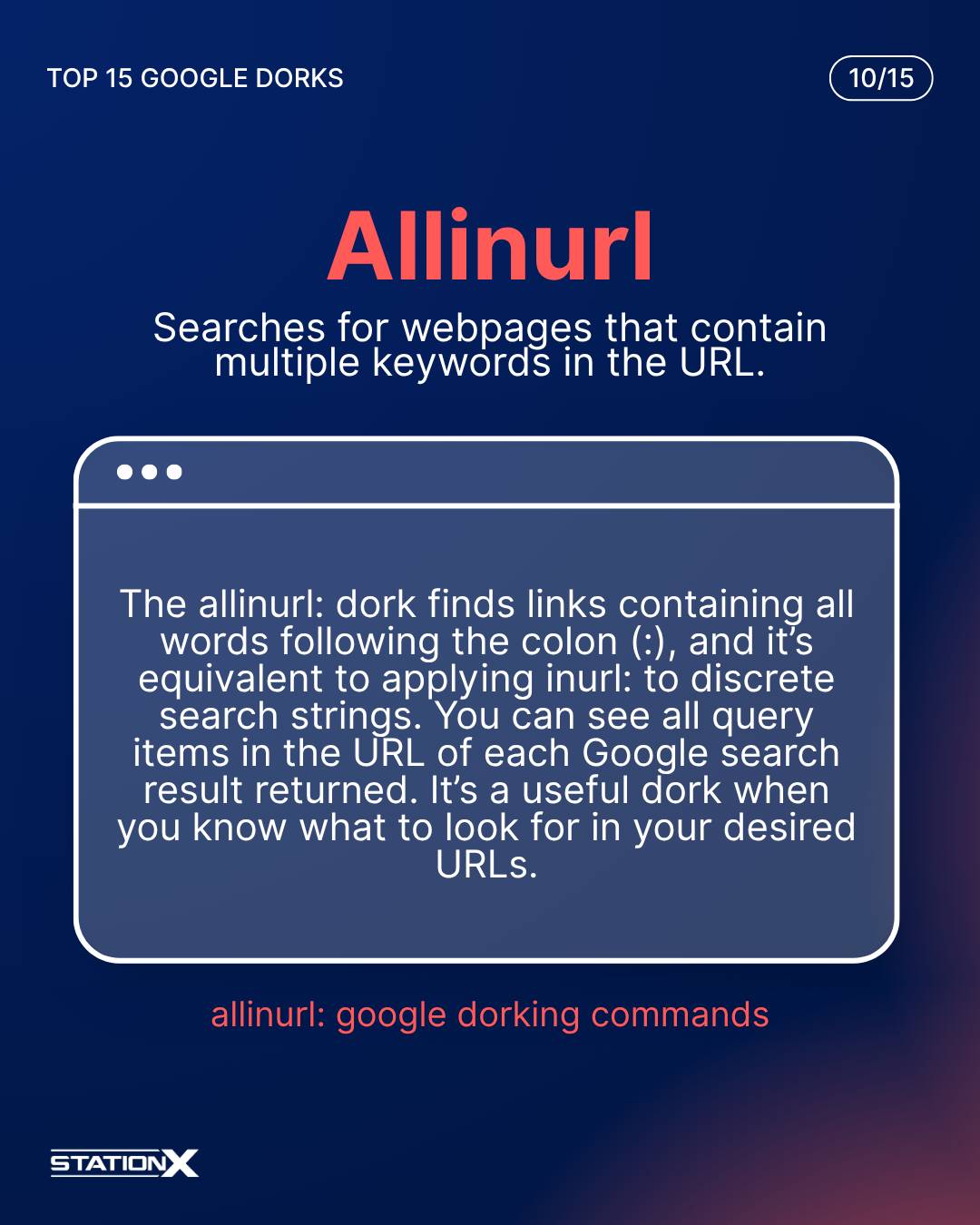
allinurl: | Find links containing all words following the colon (:). Equivalent to applying “inurl:” to discrete search strings. | Compare allinurl: healthy eating vs inurl:healthy inurl:eating:  |
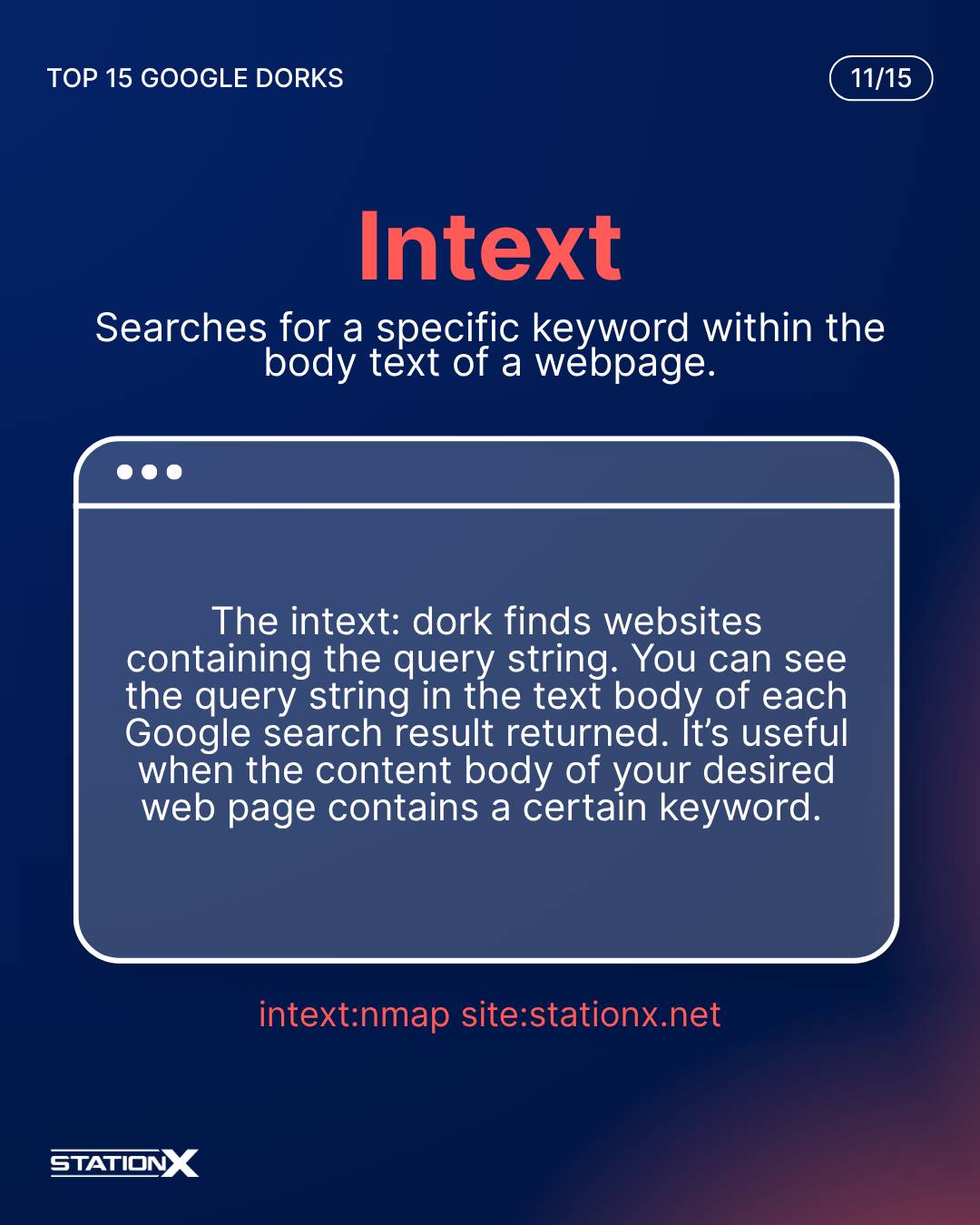
intext:, allintext: | Find websites containing the payload. The dork “intext:” applies to its search parameter only, while “allintext:” applies to the entire query string. The websites displayed in the results appear similar to a search without either command. | Compare intext:"Index of /" +.htaccess, allintext:"Index of /" +.htaccess, and "Index of /" +.htaccess. Look at intext:"Index of /" +.htaccess -intitle:"Index of /" (exclude titles containing the search query) too. |
Google Dorks Operators
Unlike certain Google Dorking commands, you may include spaces between Google dorking operators and your query items. You may combine as many different operators and commands as are necessary.
Search
These refine the search and constrain the results to follow the rules of logic. Most of the following are logical operators.
| Command | Description | Example usage |
|---|---|---|
" " | Return exact matches of a query string enclosed in the double quotes. Note that these are straight and not curly “” quotation marks. The curly quotes may or may not return similar results as straight quotes. Single quotes don’t work. | "Google dorking commands". Compare 'movie review' and "movie review":  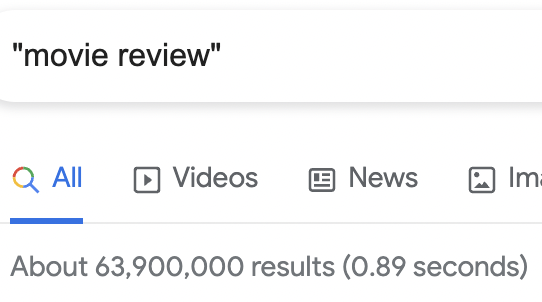 |
OR, | | Return sites containing either query item joined by OR or the pipe character |. This is an inclusive OR. | Amazon OR Google yields the same number of results as Amazon | Google.  |
( ) | Group multiple Google dork operators as a logical statement | (black OR white) hat hacker |
- | Hyphen; exclude search results containing the word or phrase after the hyphen. | Amazon -reviews, "sql injection" -"penetration testing" |
* | Wildcard or glob pattern as a placeholder for query item | "type * error" returns pages on Type I and II errors in statistics. Compare this with the search “type i OR ii error” which doesn’t use this wildcard:   |
#..# | Search a numerical range specified by the two endpoints # inclusive | 2006..2008 finds all pages that include 2006, 2007, or 2008 in them. |
AROUND(N) | Match pages containing the search terms separated by at most N other words | read AROUND(2) book, read AROUND(3) book |
Information Security Courses Bundles
Want lifetime access to expert-led cyber security training? Explore our Information Security Course Bundles — one-time purchase packages covering top topics like Ethical Hacking, Cloud, Linux, DevSecOps, and CompTIA certifications.
AND, &, + | Concatenation; return sites containing both query items joined by AND, the ampersand symbol & or the plus sign +. Google seems to assume you’re using this dork whenever you have multiple search items in one query. This is because the websites in the dorked search results are similar to queries without these dorks. Curiously, the estimated number of search results differs. | Amazon AND Google, Amazon & Google, Amazon + Google. Compare with Amazon Google (no quotes): 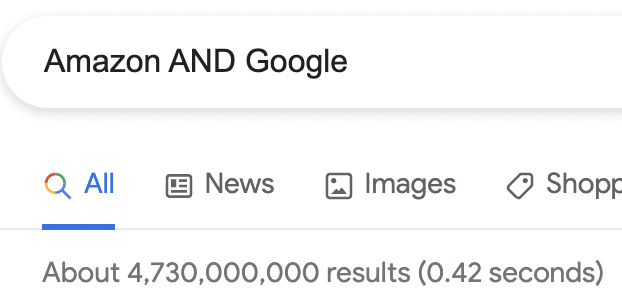    |
_ | Wildcard symbol for Google Autocomplete. Google appears to treat this symbol literally if it’s inside double quotes. | Suppose you can’t recall the name of the late singer Michael Jackson: Michael _ singer, "Michael _" singer.   Compare with Michael singer, "Michael *" singer. 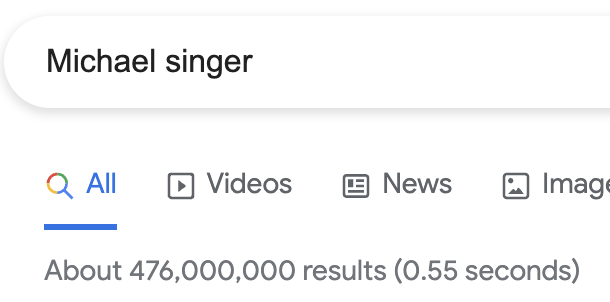  Only "Michael *" singer has a direct entry about Michael Jackson on the first page of the search results:  |
Math
The following are mathematical operations that you can perform on Google.
| Operators | Description | Example usage | Result |
|---|---|---|---|
| + | Addition | 3 + 20 | 23 |
| - | Subtraction | 3 - 20 | -17 |
| * | Multiplication | 3 * 20 | 60 |
| / | Division | 3 / 20 | 0.15 |
| % of | Percentage | 33% of 400 | 6.6 |
| X^Y, X**Y | Raise X to the power of Y. Both operators ^ and ** perform the same operation. | 3^2, 3**2 | 3^2 = 93**2 = 9 |
| in, to | Convert a quantity from a given unit to another. Translate words into another language. | 6 ft 2 inches in cm,140 lbs in kg,100 USD to bitcoin,8 am London time to California time,thank you in spanish | 6 ft 2 inches = 187.96 cm,140 lbs = 63.5029 kg,100 USD =   |
| sqrt | Square root | sqrt(3) | 1.73205080757 |
| i | Imaginary number. Use it with other mathematical operations to see it in action. | i^2 | -1 |
| N choose R | Find how many combinations are possible from N items taken R at a time, where N and R are integers. (Combinatorics) | 6 choose 4 | 15 |
| sin, cos, tan | Trigonometric functions. You may specify the formula using symbols and natural language. | sin(pi/6), sin 30 degrees | sin(pi/6) = 0.5, sin 30 degrees = 0.5 |
| timer | Timer | timer for 20 minutes |  |
| [This has no specific operator] | Generate a random number. Find more on the drop-down dialog box labeled “Tools” on the results page. | flip a coin, roll a dice, show random number from 10 to 40 |    |
| [graph] EXPRESSION [from A to B] | Graph a mathematical EXPRESSION with variables x and y on an (optional) numerical range from A to B. The “graph” keyword is only necessary if Google doesn’t understand your query. | sin(x)/x, graph log(x), sqrt(x^2+y^2) from -20 to 20 | ![Graph of y=sin(x)/x looks like a peak at x=0 and decreasing ripples towards both horizontal infinities. [sin(x)/x - Google Search]](https://www.stationx.net/wp-content/uploads/2022/11/Graph-of-y-sinx-x-looks-like-a-peak-at-x-0-and-decreasing-ripples-towards-both-horizontal-infinities-sinx-x-Google-Search.png) ![Graph of y=log(x) looks like a curved arm reaching from bottom left to top right. [graph log(x) - Google Search]](https://www.stationx.net/wp-content/uploads/2022/11/Graph-of-y-logx-looks-like-a-curved-arm-reaching-from-bottom-left-to-top-right-graph-logx-Google-Search.png) ![Graph of z=sqrt(x^2+y^2) looks like a paper cone with the tip at (x,y)=(0,0). [sqrt(x^2+y^2) from -20 to 20 - Google Search]](https://www.stationx.net/wp-content/uploads/2022/11/Graph-of-z-sqrtx2y2-looks-like-a-paper-cone-with-the-tip-at-xy00-sqrtx2y2-from-20-to-20-Google-Search.png) |
Google also supports other scientific calculator operations on its calculator. This website features additional examples of mathematical operations you can perform on Google.
Examples of Complex Google Dorks
You can combine Google dorking commands and operations for specific results.
| Command | Description |
|---|---|
| inurl:zoom.us/j intext:scheduled | Get links to publicly shared Zoom meetings you may want to access. |
| "index of" "database.sql.zip" | Get unsecured SQL dumps. Data from improperly configured SQL servers will show up on this page. |
| filetype:yaml inurl:cassandra | Get YAML configuration files specific to Apache Cassandra databases |
| @youtube trending shorts | Find short clips trending on YouTube |
| @reddit memes -dark | Find memes on Reddit that are not dark |
| site:cdn.cloudflare.net filetype:pdf | Find PDFs on the *.cdn.cloudflare.net domain |
| secret in spanish inurl:dict | Translate the word “secret” to Spanish and limit results to URLs containing “dict” |
| filetype:doc site:www.stationx.net nathan | StationX with the .doc extension. This looks for legacy Microsoft Word files containing the keyword “nathan” (founder’s name). |
Google Dorking Cheat Sheet: Quick Tips and Best Practices
Google Dorking is a powerful technique, but mastering it requires a clear understanding of best practices and use cases. This section offers quick, actionable tips to help you use Google Dorks effectively and ethically.
How to Use Google Dorks Effectively
- Use Quotation Marks for Exact Phrases: Enclose your search term in quotes (
"example phrase") to find exact matches, minimizing irrelevant results. - Stack Operators for Precision: Combine multiple operators to refine your search. For example,
site:example.com filetype:pdf "passwords"helps you locate specific PDF files containing sensitive terms on a targeted domain. - Target Specific Sites and File Types: Use
site:to restrict searches to a specific domain andfiletype:to limit results to certain file types, such as PDF, DOCX, LOG, ZIP, TAR.GZ, ENV, JS, PY, GIT, or TXT. - Experiment and Adjust: Google Dorks may become outdated or restricted over time. Regularly test and refine your queries for accuracy.
Popular Use Cases for Google Dorking
- Finding Exposed Cameras: Use queries like
inurl:/view/view.shtmlto locate unsecured cameras streaming online. - Locating Misconfigured WordPress Admin Pages: Try
intitle:"index of" "wp-admin"to discover exposed admin directories. - Discovering Login Panels: Use
inurl:loginorintitle:"login"to identify login pages on websites quickly. - Identifying Leaked Documents: Refine your search with
filetype:pdf intext:"confidential"to find documents that may contain sensitive information. Otherintext:terms to consider are- classified
- internal
- restricted
- release
- password
- proprietary
- private
- backup
- config
- db_dump
- sql
- admin
- backup
- export
- dump
- log
- archive
- credentials
- token
- secret
- key
- jwt
- login
- users
How to Prevent Google Dorks
With great power comes great responsibility, and even if you use Google Dorks with the utmost care, other entities may not. Here are some suggestions to avoid becoming the next victim of unwanted Google Dorking.
- Implement IP-based restrictions and password authentication to protect private areas. Securing your login portals discourages unauthorized access.
- Encrypt all sensitive information, like usernames, passwords, email addresses, phone numbers, and physical addresses. This way, in the event of data leakage, the original data remains unexposed.
- Run vulnerability scans to find and disable Google dorks. Examples of vulnerability scanners are nmap, Nessus, and Qualys.
- Run regular dork queries on your website to discover loopholes and sensitive information before attacks occur. Sqlmap is a helpful tool.
- If you find sensitive content exposed on your website and you’ve exhausted all other means of removing it (such as changing your passwords or renaming your login pages), request its removal through Google Search Console.
- Be judicious in the use of
robots.txt. Read the warning below.
A Word of Caution
Other websites mentioning Google Dorks typically recommend using robots.txt to conceal sensitive content or to stop Google from indexing specific parts of your website. On your website server, you can find robots.txt in the root-level directory, such as /public_html.
What seems like a simple, good-faith solution to eliminate complex reconnaissance via Google Dorks is, to an intelligent hacker, a treasure trove and a cash cow. Instead of backing off, they’ll attack your website by targeting the items listed in robots.txt.
Hence, it’s best to adopt this measure cautiously. The most prudent use of robots.txt is instructing Google to exclude one’s entire website, as follows:
| User-agent: * Disallow: / |
Such a robots.txt file compels visitors looking for information to use the search function inside the website. A well-built internal search function may have safeguards against Google dorking, SQL injection, and other hacking techniques. These safeguards protect the website better than allowing external search engines such as Google to index the website.
Google Dork Cheat Sheet Conclusion
Google Dork commands are such powerful tools for uncovering data and locating vulnerabilities that mastering them is paramount for ethical hackers, penetration testers, and cyber security professionals. Google is one of the most powerful free reconnaissance tools available if you know how to use it.
We hope this cheat sheet is helpful to you as a penetration tester, ethical hacker, or someone interested in the security position of your enterprise. You can read our full guide on Google dorking specific websites here.
If you’re interested in learning more, our Google Hacking Course Bundle will help you master Google Dorking and OSINT - see the banner below! To get a head start on a cyber security career, check out our free e-book, or join the StationX Master's Program.
This Google Dorking Course Bundle Includes:
- Learn OSINT Techniques From Scratch & OSINT Certification
- What Is Open Source Intelligence: OSINT Tools
- Top 5 Bug Bounty Tools and Tricks Course
Remember: with great power comes great responsibility. More important than enjoying Google dorking, stay safe.











I had no idea this was called “dorking” — I took a class on how to do advanced google searching 15 or 20 years ago and learned most of these. I develop websites so I’m going to play with some of the advanced methods to make sure I’m not leaving any doors open.
Google dorking was an unusually rewarding experience for me because I found something shocking whilst working on the companion article to this one: How to Google Dork a Specific Website for Hacking
Enter only his cameras
what
I’m new to all this but I was learning things on my vacation. I love to see the real potential for docking
Password
Banking
Please give me job im white Hecker
I think it is awesome that you are female in this male dominated field. Your content is easy to follow, too. I would suggest adding a few video examples of you using the syntax for visual and audio learners. Good job and good luck in your career!
Social