This OSCP exam guide will teach you everything you need to know about the exam, what key areas to focus on, and how to get certified on your journey to becoming a professional penetration tester.
The OSCP is widely renowned as the golden standard of entry-level penetration testing certifications, and adding it to your resume will set you apart from the competition.
Passing this exam has become something of a legend. It’s notoriously difficult, tests your hands-on hacking skills to the extreme, and is filled with rabbit holes that could derail you.
Fear not. This comprehensive exam guide will teach you how to pass this and get certified.
Ready? Let’s go.
- What Is the (OffSec Certified Professional) OSCP Certification?
- OSCP Exam Cost
- The Penetration Testing With Kali Linux (PWK) OSCP Course
- What Is OSCP+?
- OSCP Exam Format
- OSCP Exam Guide: What Can I Expect?
- Should I Prepare Before Taking the PWK Course (OSCP Requirements)?
- The Difference Between Success and Failure
- Final OSCP Exam Advice
- Conclusion
- Frequently Asked Questions
What Is the (OffSec Certified Professional) OSCP Certification?
The OffSec Certified Professional (OSCP) certification is one of the most sought-after hacking certifications on the market.
It’s highly regarded by industry professionals and hiring managers as a practical certification demonstrating you have the skills and knowledge to be a junior penetration tester.
However, this exam is challenging to pass and is often considered the most difficult certification to acquire for those just starting in the field. It requires you to battle a real-world, scenario-based exam where you must hack multiple machines within 24 hours.
This certification is not for the faint of heart. But to the spoils go the victor, with certification holders making upwards of $75K USD.
So, let’s find out what you can expect to encounter when going for your OSCP.
In this article, learn how the OSCP compares to EC-Council’s Certified Ethical Hacker (CEH).
OSCP Exam Cost
To tackle the OSCP, purchase OffSec’s Penetration Testing With Kali Linux (PWK) Course, also called PEN-200. This course teaches you what you need to know to pass the exam and obtain the OSCP certification.
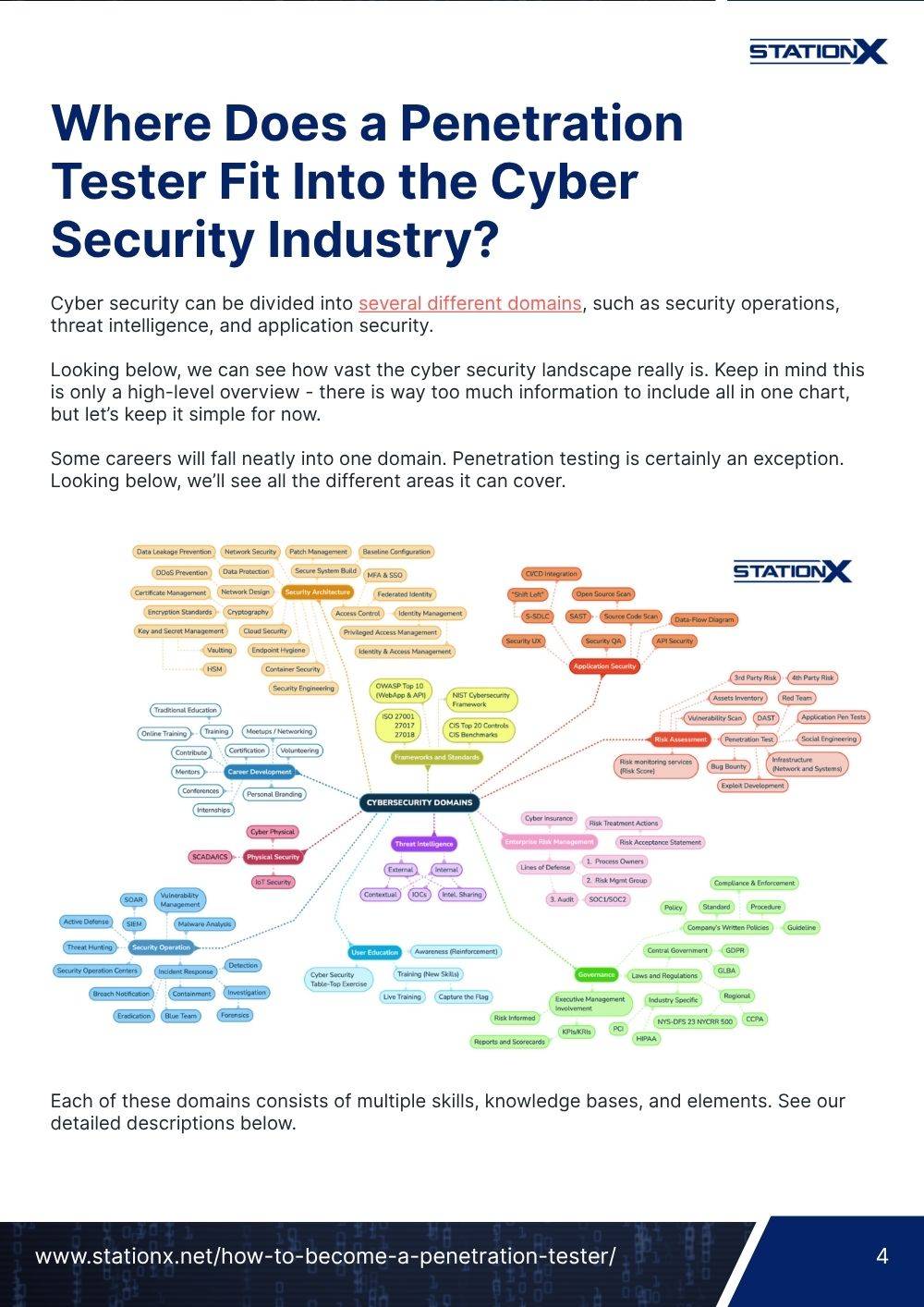
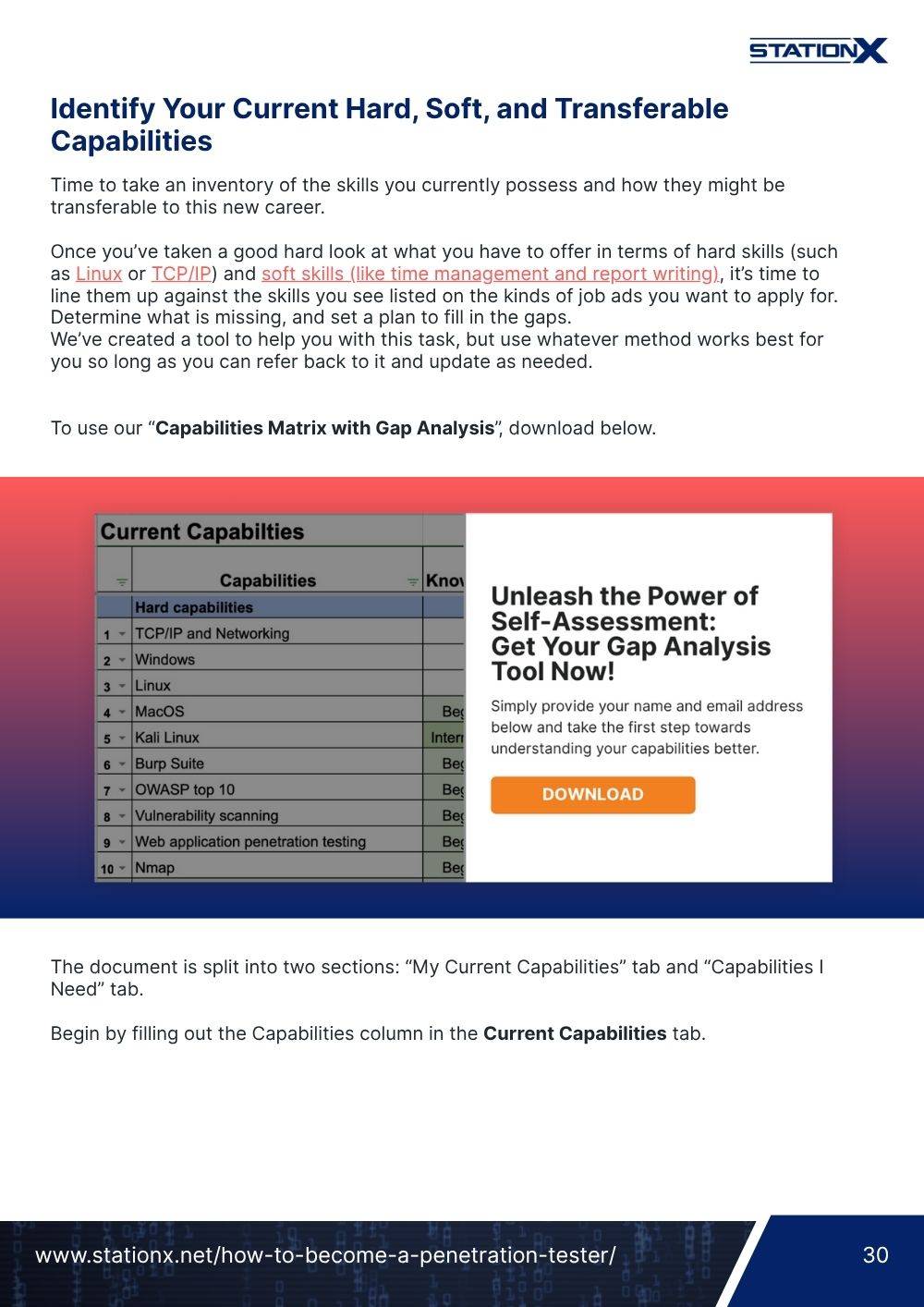
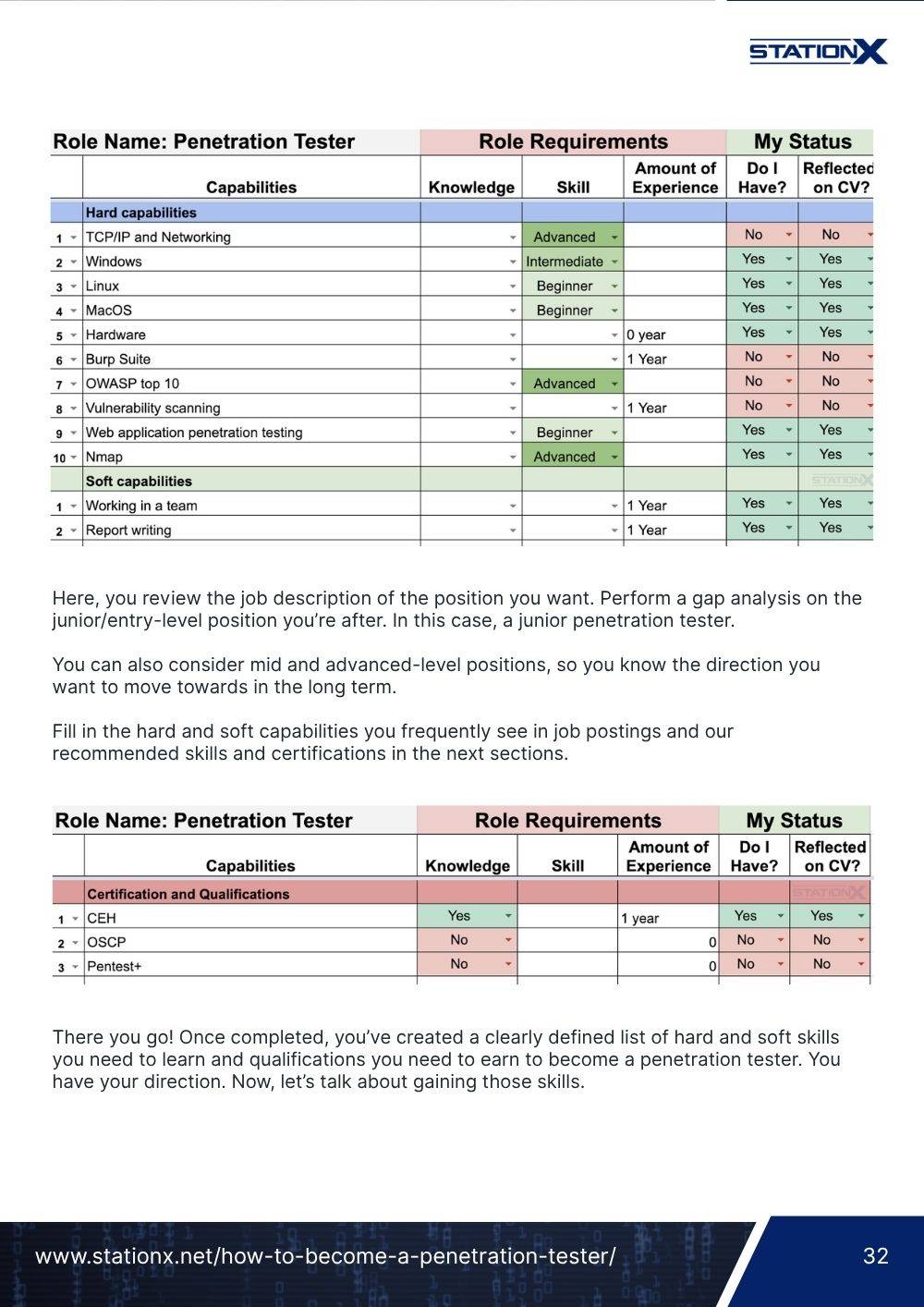
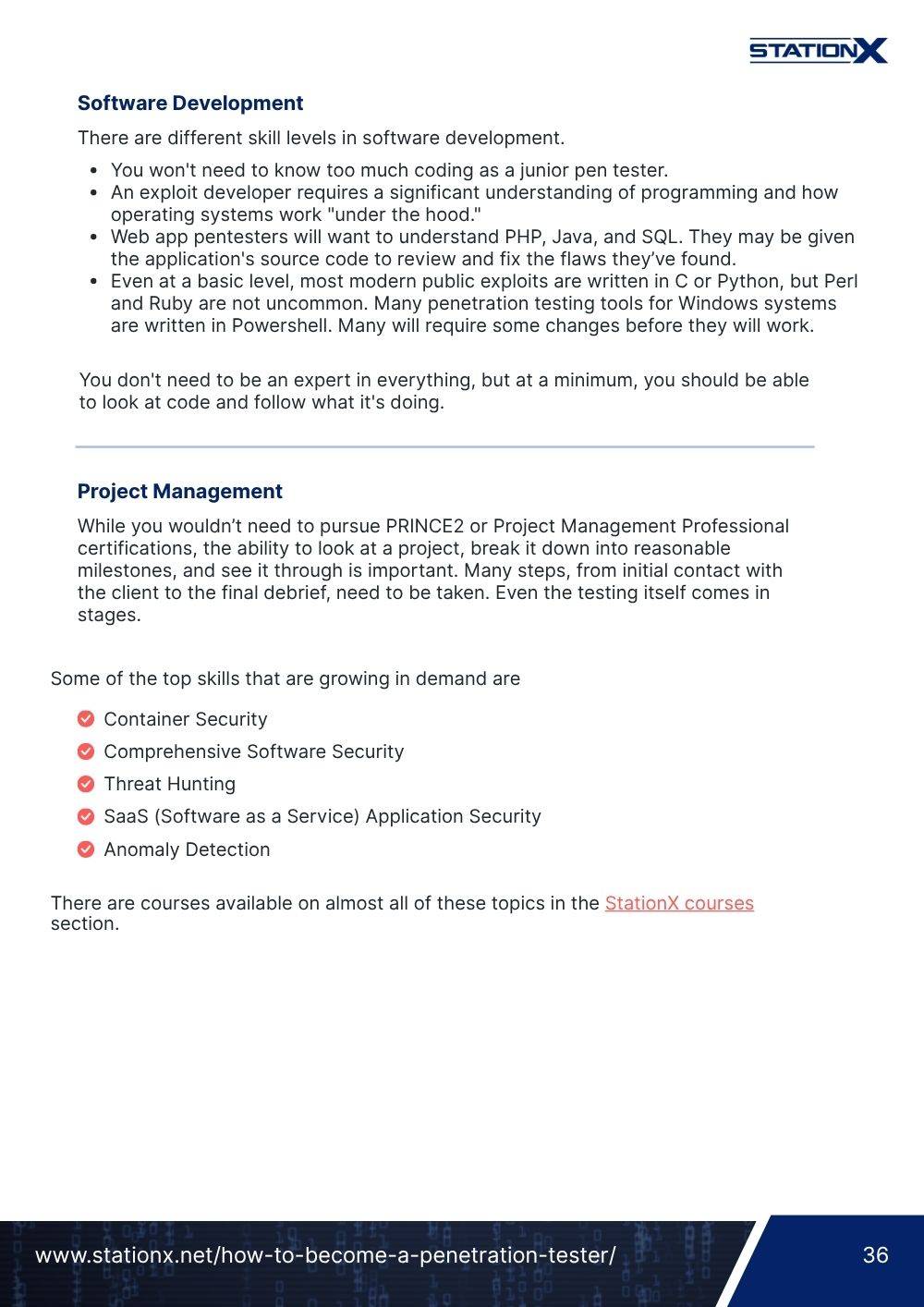
OffSec offers various pricing options, as shown below.
| Course & Cert Exam Bundle |
| $1,749 |
| Includes PWK course |
| 90 days lab access |
| One exam attempt |
| No additional contents |
| No access to PG Practice labs |
| Learn One |
| $2,749/year |
| Includes PWK course |
| 365 days of lab access |
| Two exam attempts |
| Includes additional content (PEN-103 and PEN-210) |
| Access to PG Practice labs |
| Learn Unlimited |
| $6,099/year |
| Includes all OffSec courses |
| 365 days of lab access |
| Unlimited exam attempts |
| Includes additional content |
| Access to PG Practice labs |
OffSec also offers discount programs if you have previous OffSec certifications, are a university student, or if your organization buys an enterprise plan. Individual exam retakes cost $249 each, and you can also extend your PWK lab access for 30 days by paying an additional $359.
The Penetration Testing With Kali Linux (PWK) OSCP Course
The PWK course is designed to introduce you to penetration testing and provide you with the knowledge and skills to become a junior penetration tester.
The PWK combines traditional course material with challenge labs that test your knowledge and skills through hands-on hacking exercises inside a virtual lab environment.
On purchasing the course, you’ll be given a massive 850+ page PDF document comprising various learning modules and access to training videos demonstrating the material taught in the modules.
OSCP Syllabus
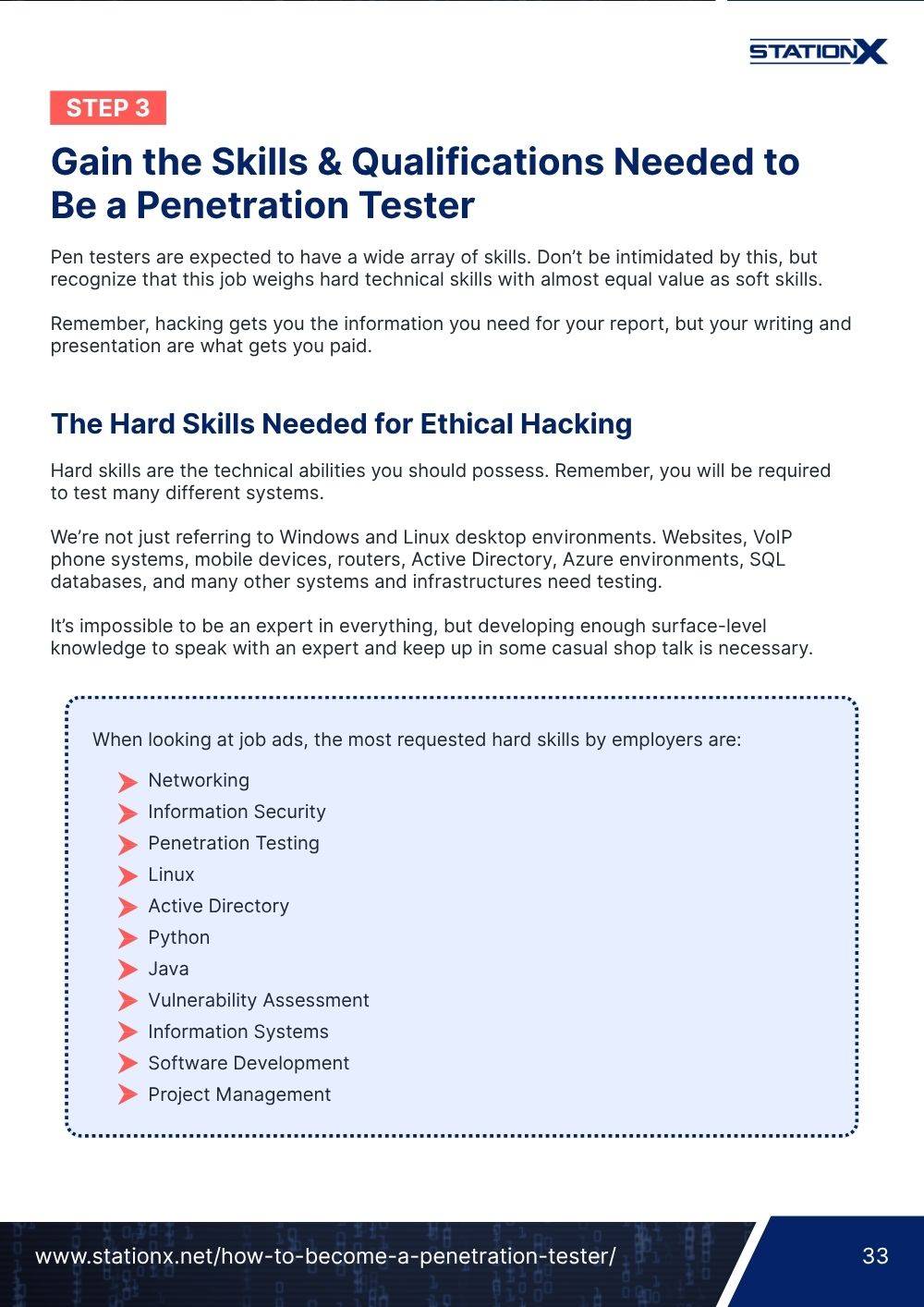
The course includes 23 learning modules, which include:
- Penetration Testing with Kali Linux: General Course Introduction
- Introduction to Cybersecurity
- Effective Learning Strategies
- Report Writing for Penetration Testers
- Information Gathering
- Vulnerability Scanning
- Introduction to Web Applications
- Common Web Application Attacks
- SQL Injection Attacks
- Client-Side Attacks
- Location Public Exploits
- Fixing Exploits
- Antivirus Evasion
- Password Attacks
- Windows Privilege Escalation
- Linux Privilege Escalation
- Port Redirection and SSH Tunneling
- Advanced Tunneling
- The Metasploit Framework
- Active Directory Introduction and Enumeration
- Attacking Active Directory Authentication
- Lateral Movement in Active Directory
- Assembling the Pieces
What Is OSCP+?
OSCP+ is the time-bound, current-knowledge version of OSCP. If you pass the updated OSCP exam, you receive two credentials:
- OSCP (lifetime, non-expiring)
- OSCP+ (valid for 3 years)
The only difference is expiration. If OSCP+ lapses, you still keep your OSCP forever.
Why Does OSCP+ Expire?
OffSec’s stated goal is to help employers and candidates signal that skills are recent and actively maintained, reflecting how fast offensive security changes. The “+” designation is meant to show up-to-date capability, while OSCP remains your permanent baseline credential.
How Do You Renew OSCP+?
Before the 3-year validity ends, you can keep the “+” active in one of these ways:
- Complete OffSec’s CPE program: Earn 120 CPE credits over 3 years and pay the $145 Annual Maintenance Fee to maintain the “+” status. Credits can come from OffSec training and approved external activities.
- Pass a recertification exam: Take and pass the OSCP+ recert exam within 6 months before expiration.
- Pass another qualifying OffSec certification: Getting a higher-level or parallel cert (OSEP, OSWA, OSED, OSEE) before expiry also renews your OSCP+
OSCP Exam Format
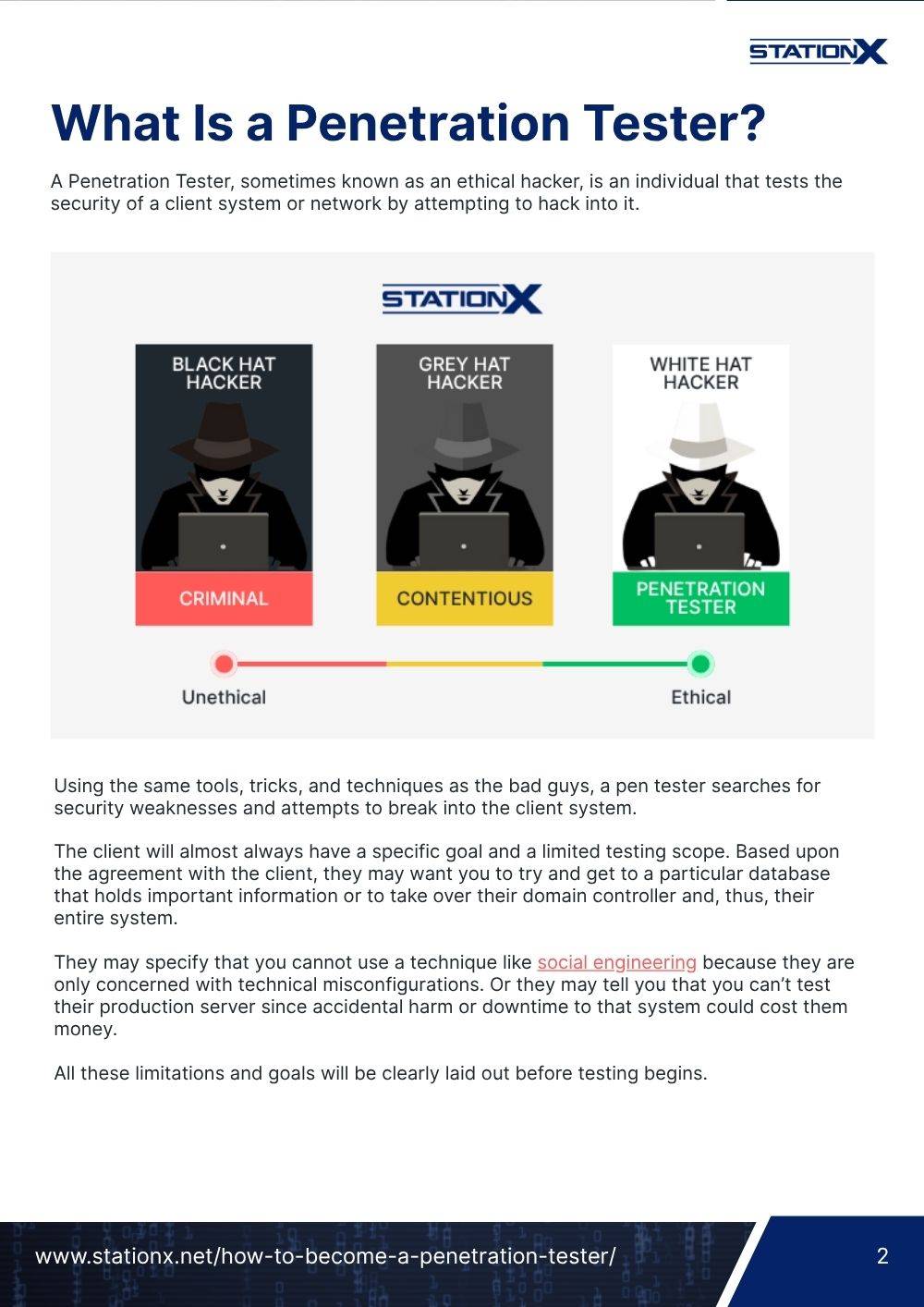
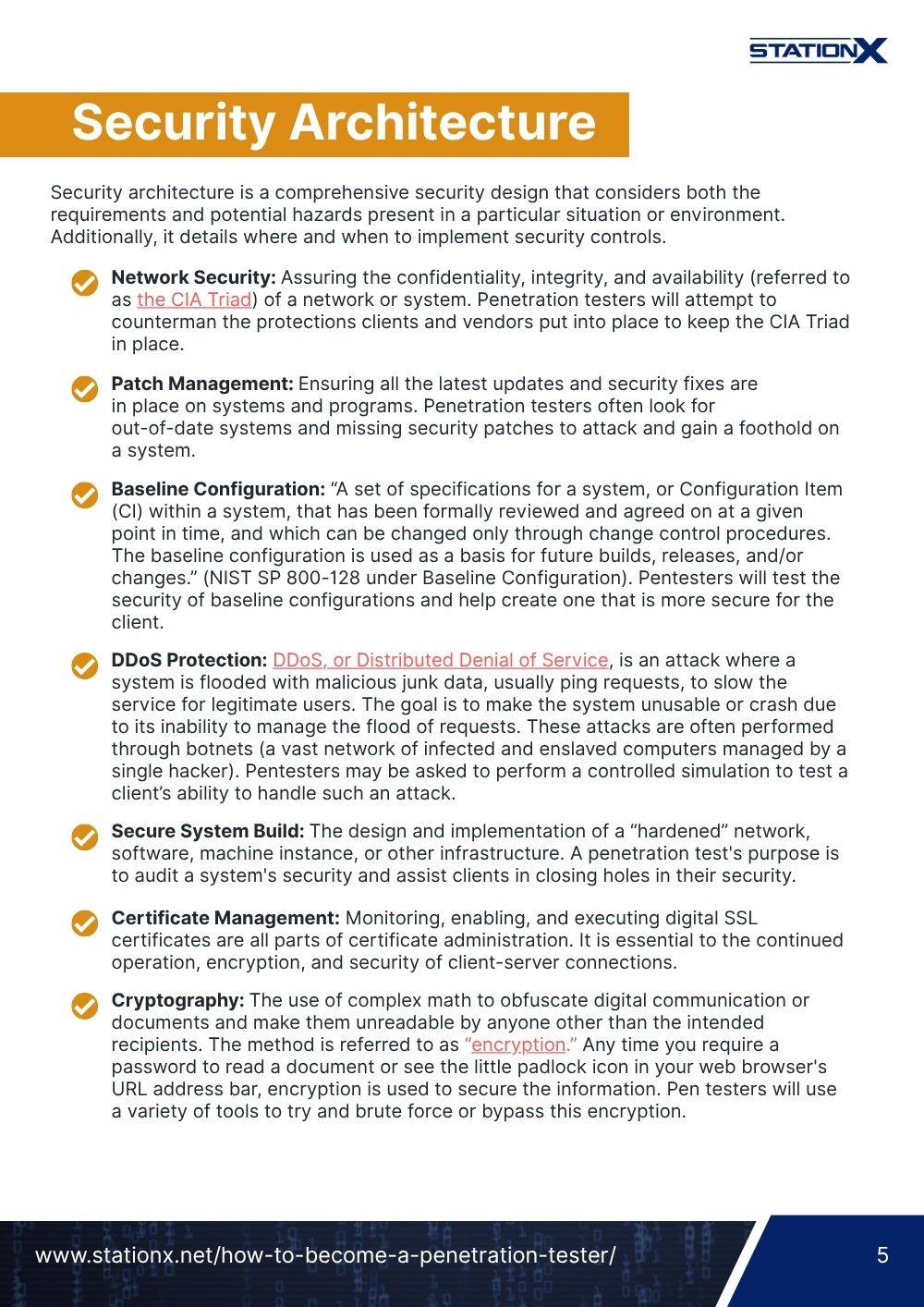
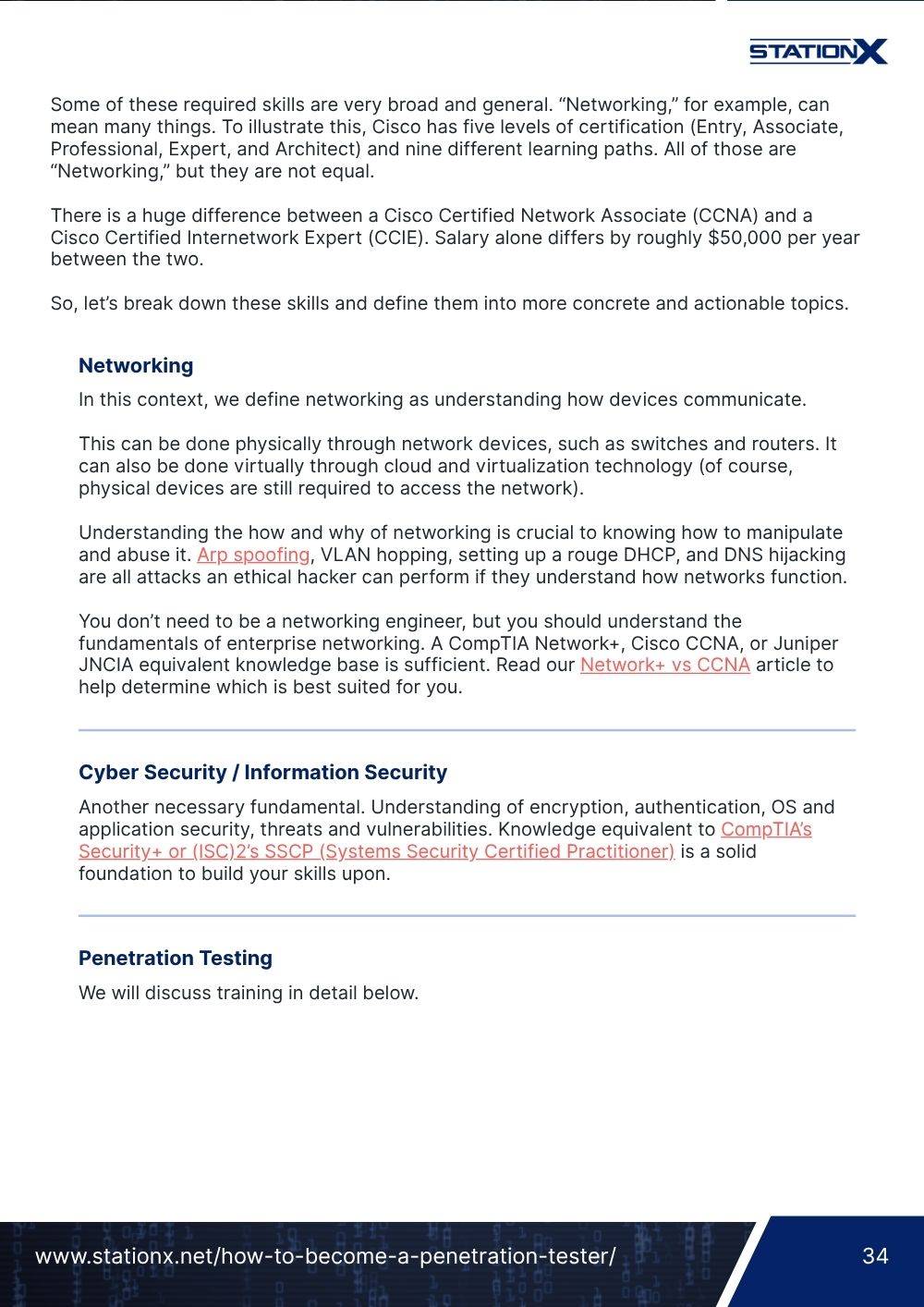
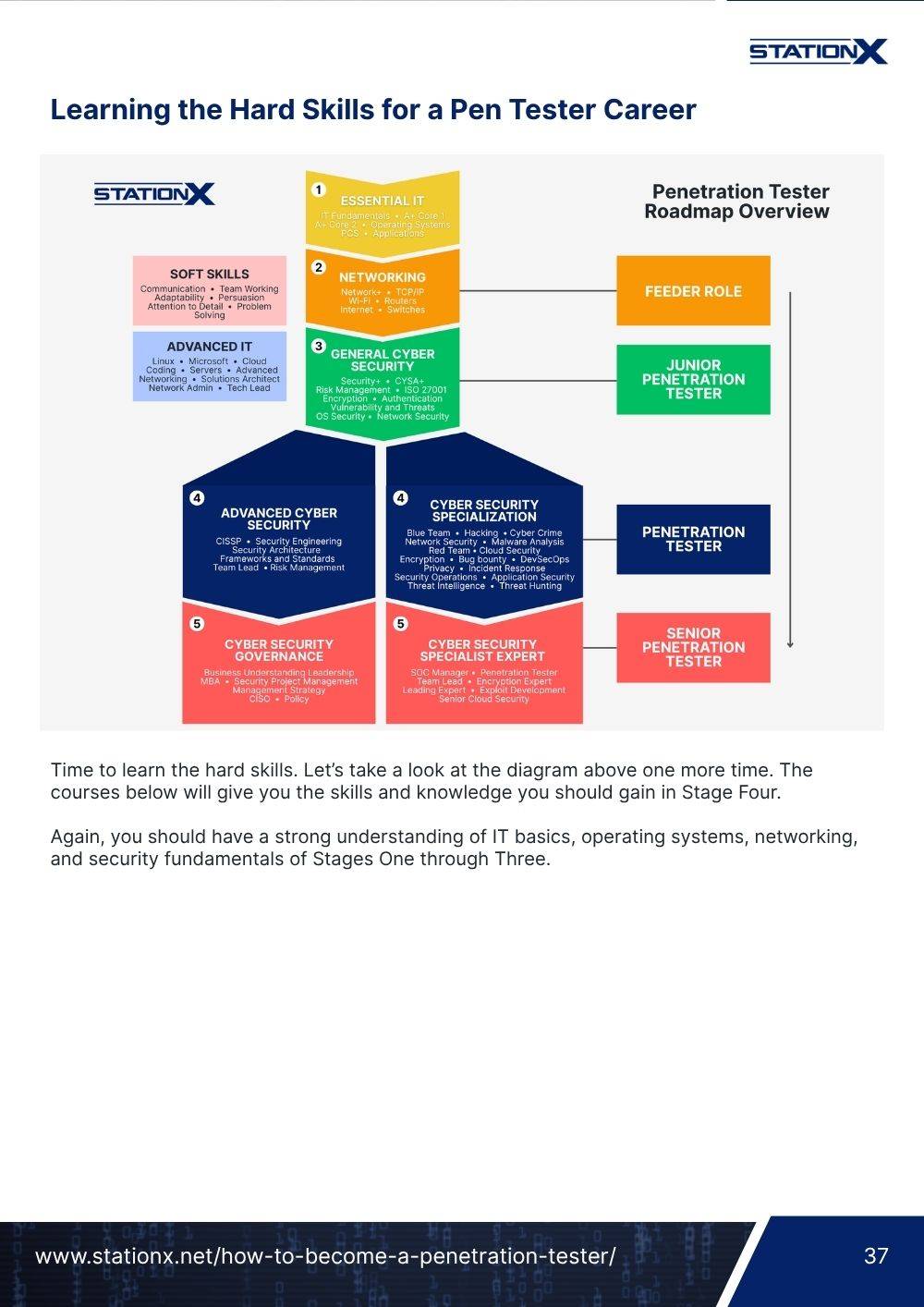
The PWK course prepares for the OSCP exam, a 24-hour exam which a member of OffSec proctors to ensure you follow exam requirements. The exam consists of two parts:
- Traditional penetration testing: This part consists of three independent targets that require two steps to compromise. You are awarded 20 points per successfully compromised machine, split into 10 points for low-privilege access and 10 points for privilege escalation, for a total of 60 points. You prove success by taking screenshots and submitting a proof file (
local.txtorproof.txt) to your control panel. - Active Directory testing: This part includes three machines worth 40 points total. You receive a username and password to simulate a breached-environment scenario, then work through the machines in sequence: 10 points for machine #1, 10 points for machine #2, and 20 points for Domain Controller #3.
As of November 1st, 2024, there are no more bonus points for completing course exercises.

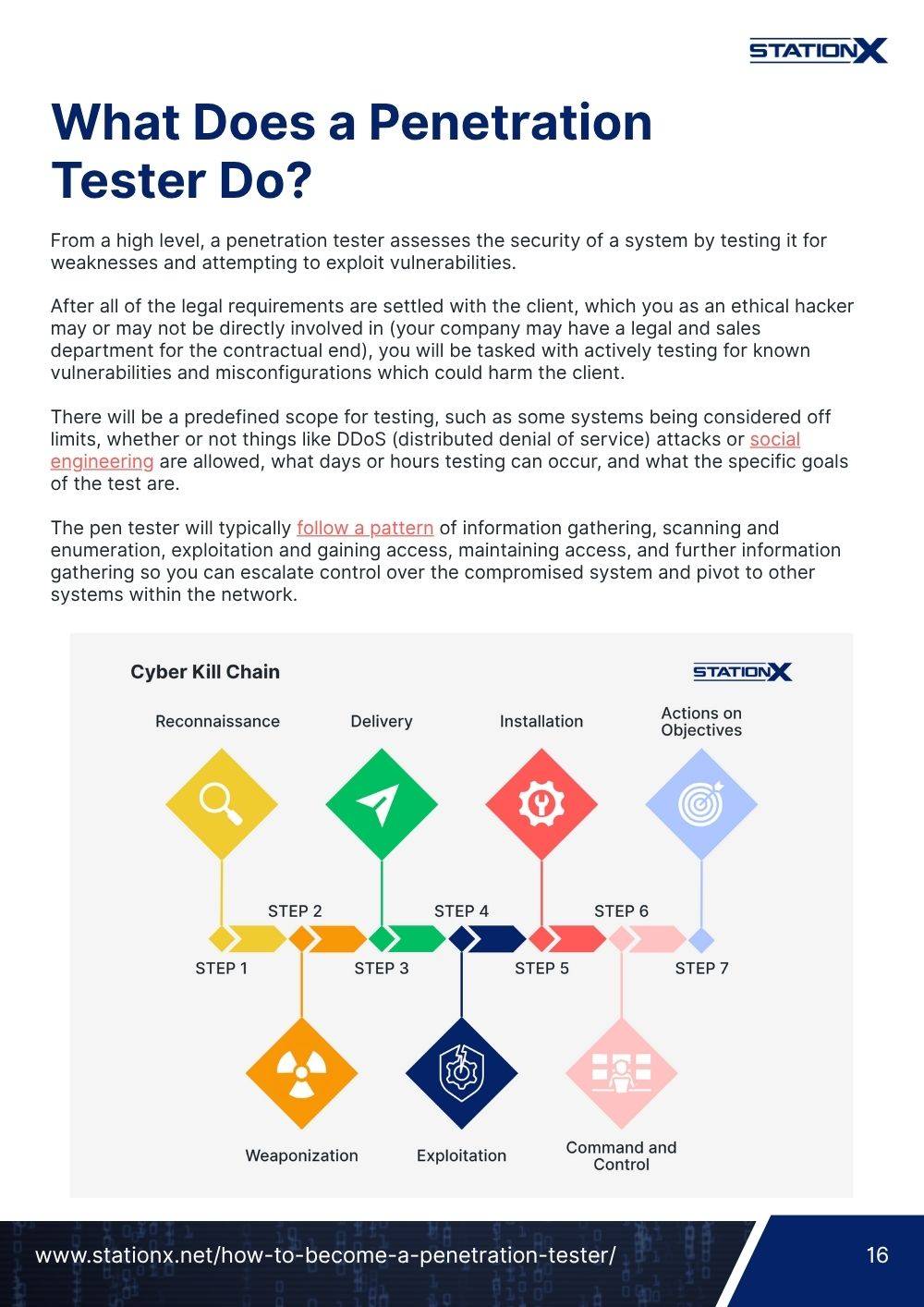
The diagram above shows one possible three-machine Active Directory layout you might face in a practice environment: an initial workstation where you start with low-privilege domain user credentials (assumed breach), a second workstation or member server reached via lateral movement and privilege escalation, and a Domain Controller as the final target.
Please note that this is not taken from the OSCP/OSCP+ exam. Treat the example as a learning aid showing a general Active Directory attack path, not a representation of any specific exam setup.
Pivoting may be required. In many reported cases, the AD set appears to sit on a single subnet with minimal segmentation. However, OffSec’s own guidance states that pivoting may still be necessary, so don’t assume a flat network. There may be multiple versions of the AD environment, and the structure you encounter could differ.
OffSec provides an official OSCP report template on their website, and it’s the safest way to structure your submission. Using it helps you stay aligned with what graders expect: a clear, step-by-step write-up for each target, including every command, output, and required proof screenshot in a format that can be replicated by a technical reader.

Important: No AI Assistance Allowed
OffSec prohibits any AI help during the OSCP exam. Using tools like ChatGPT, Copilot, or even AI-generated search summaries can result in an automatic fail. Before you start, make sure you disable AI answer features in your browser and rely only on permitted resources.
OSCP Exam Report
Upon completing the exam, you will have 24 hours to write a professional report describing your exploitation process for each target.
This report must document your attacks, including all steps, commands issued, and console output. It should be thorough enough that a third-party reader could replicate your attacks step-by-step.
To pass the exam, you must achieve a minimum score of 70 points, provide sufficient documentation, and follow OffSec’s strict exam requirements regarding exploit code, exam proofs, and exam restrictions.
Failing the OSCP exam will require you to pay for a retake. This costs $249 unless you are signed up for one of OffSec’s annual subscription plans (Learn One or Learn Unlimited).
Now you know the basics. Let’s jump into what you can expect on the OSCP exam.
OSCP Exam Guide: What Can I Expect?
The PWK course material is extensive. It includes everything from creating bash scripts to performing Active Directory and buffer overflows. However, much of this material is not tested during the OSCP exam.
Knowing what material from the PWK course you will be tested on is important before sitting your OSCP exam. This will allow you to dedicate your time to perfecting these skills, giving you the best chance of passing the exam.
Let’s look at what is and is not included in the exam.
What is NOT in the OSCP Exam
Here are topics taught in the PWK course that are not included in the OSCP exam.
Bash and Python Scripting
The PWK course includes sections on the basics of Bash and Python scripting. You’ll not be tested on this knowledge specifically, so don’t worry about memorizing syntax, listing language features, or creating scripts from scratch.
Open Source Intelligence (OSINT)
The PWK course has an entire section on information gathering. This is a vital phase during a real-world penetration test, but in the OSCP exam, you don’t need to gather public information about your targets. You only need to use tools like Nmap to find open ports, services, and vulnerabilities.
Buffer Overflows
The PWK teaches how to perform buffer overflow attacks against vulnerable Windows and Linux applications. This is valuable knowledge, but it’s no longer needed during your OSCP exam. The Active Directory portion of the OSCP exam has replaced this previous requirement.
Poisoning and Spoofing Attacks
The new PWK course is heavily focused on testing Active Directory environments. You’ll learn how to enumerate and attack Active Directory using various techniques, including how to use tools like Responder to perform poisoning and spoofing attacks. These attacks are common in real-world internal pen testing but are not tested on the OSCP exam. In fact, they are banned.
Anti-Virus Evasion and Persistence
During the PWK course, you’ll be exposed to material on anti-virus evasion and establishing persistence on compromised machines. These are great topics to know, but they are not tested on the OSCP exam. These topics often are more aligned with red teaming than penetration testing.
What IS in the OSCP Exam
Here’s the course material you should master to prepare for your OSCP exam.
Privilege Escalation
To earn all the points offered during your OSCP exam, you must perform privilege escalation on the machines you target. Escalating your privileges accounts for half the points available, so mastering Windows and Linux privilege escalation is critical for success.
Report Writing
Although not a traditional “hacker” skill, you must be able to structure and write a complete penetration test report. This is a skill you’ll need if you want to become a real penetration tester and one you must perform to pass the OSCP exam. Once you complete your exam, you must submit a detailed report that details your findings and allows a reasonably skilled third party to reproduce your testing step-by-step.
Web Attacks
Although not strictly a web app penetration test exam, you must often exploit at least one web exploit to gain access to a machine, though not always. This is typically a web application vulnerability like SQL injection, cross-site scripting, or broken access control. Ensure you know how to enumerate and exploit vulnerable web applications before your test.
Enumeration
A fundamental skill to master to pass the OSCP exam is enumeration. Everyone who has ever taken the OSCP will lecture you on the importance of performing enumeration to find all possible attack paths, vulnerabilities, and missing security controls. The main difference between passing or failing your OSCP is learning to perform thorough enumeration.
Key Active Directory Attack Skills
With the exam now heavily centered on Active Directory, your prep should focus on the core AD attack paths and the skills that unlock them. Prioritize the techniques that consistently show up in real-world domain compromises — and that give you multiple routes to privilege escalation.
Focus on building confidence in:
- BloodHound - map trust relationships, spot misconfigurations, and plan escalation paths.
- Kerberoasting - extract service tickets and crack them for higher-priv credentials.
- AS-REP Roasting - target users without pre-auth to recover hashes.
- Pass-the-Hash / Pass-the-Ticket - reuse NTLM/Kerberos material to move laterally without cracking.
- Mimikatz / credential dumping - pull creds, hashes, and tickets from memory when privileges allow.
- DCSync - simulate domain replication to dump high-value account hashes.
- Privilege escalation in AD - abuse ACLs, delegation, group memberships, and misconfigured GPOs.
- Lateral movement - pivot from initial foothold to member servers and onward to the DC.
- Pivoting & tunneling - be comfortable with tools like Ligolo-NG to reach segmented hosts.
If you’re unsure where to start, begin with these “big ones” first - they’re the most common and most valuable to master. We have dedicated guides for each technique, and together they cover the majority of AD scenarios you’re likely to face.
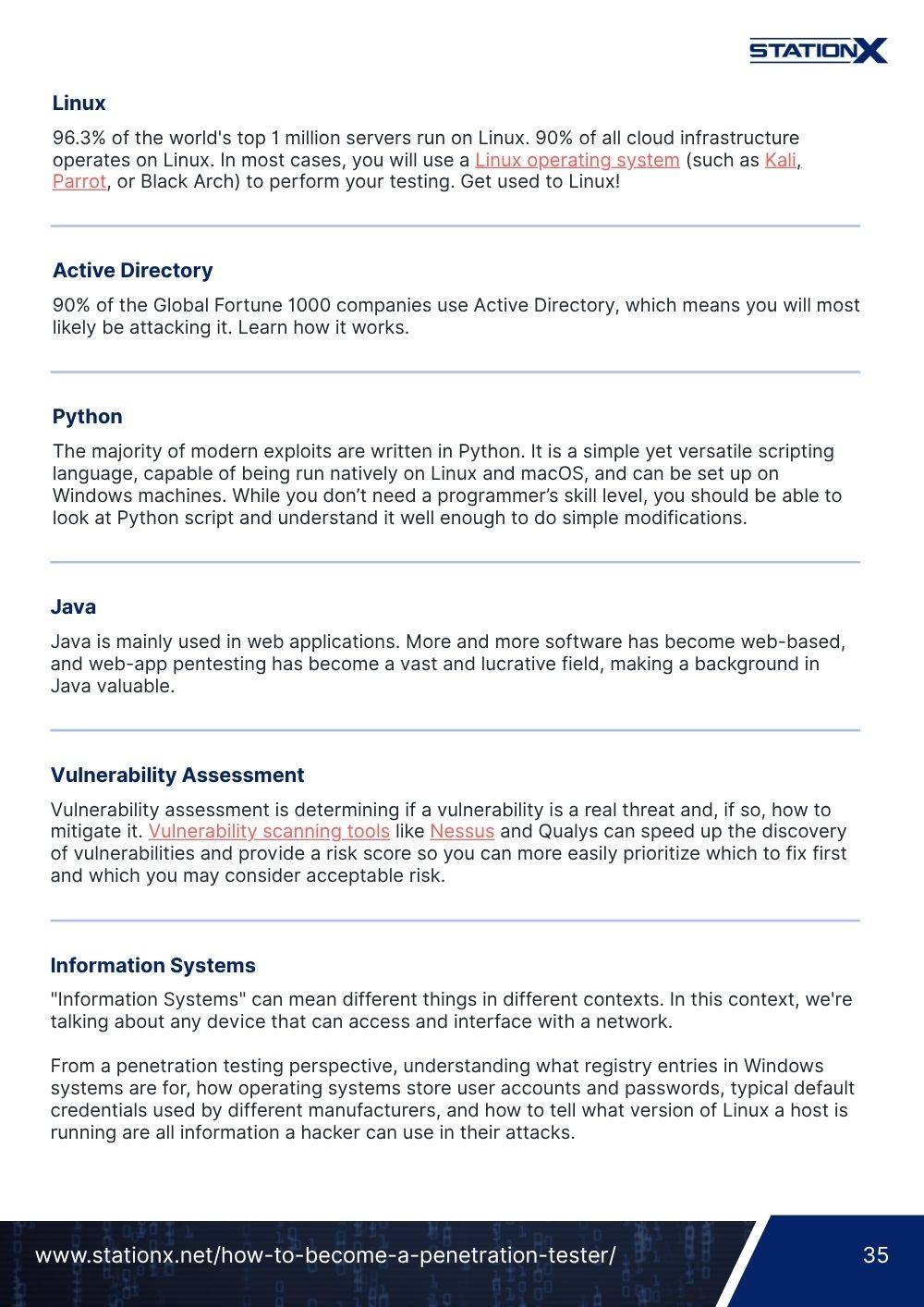
Should I Prepare Before Taking the PWK Course (OSCP Requirements)?
Preparing yourself before starting the PWK course is a good idea. At a minimum, OffSec recommends a solid understanding of networking, Windows and Linux administration skills, and familiarity with Bash or Python scripting.
However, most people who have passed the OSCP believe you should acquire more skills before tackling the course.
Cyber Security Foundational Knowledge
A strong foundation in IT, networking, and cyber security is essential. You should know how to troubleshoot IT issues, describe common network ports and protocols, and discuss common defenses used to protect against attacks.
You better have this knowledge locked down before starting the PWK course material.
Acquiring these foundational skills and knowledge is described in depth in our article, Best Way to Learn Cyber Security. The following courses also cover this material.
Additional IT Skills
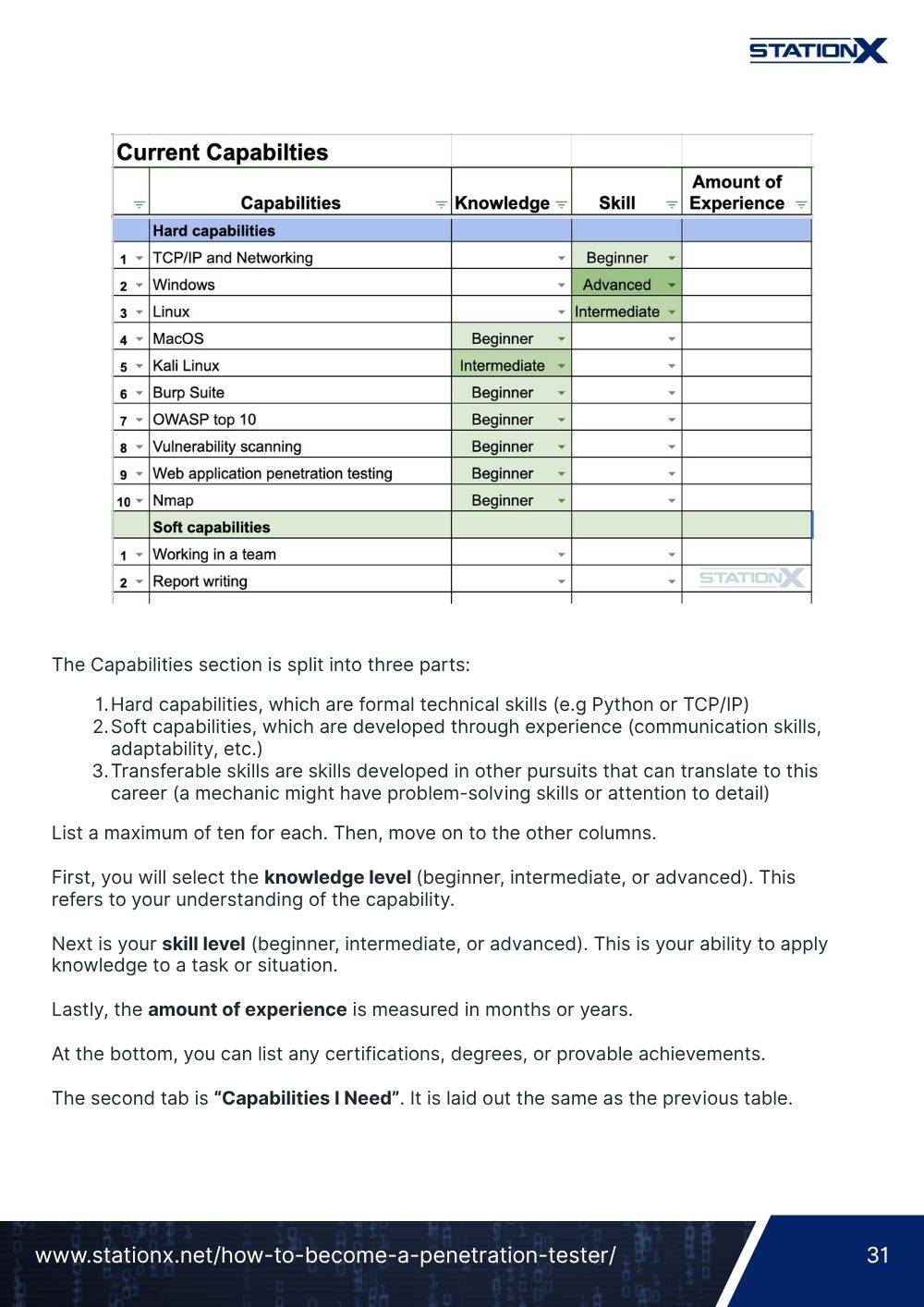
In addition to the basics, the OSCP exam will ask you to fix exploit code, enumerate Active Directory environments, and escalate your privileges on Windows and Linux machines.
Performing these tasks requires knowledge of Bash and Python, a comprehensive understanding of Active Directory, and advanced Windows and Linux skills.
You should try to learn these skills before tackling the course material, as they will significantly reduce the learning curve and help you get through the PWK material faster. To learn these skills, try one of the courses below.
Remote Cyber Security Jobs Database
Looking to work from anywhere? Tap into our Remote Cyber Security Jobs Database — over 360 remote-friendly companies, 70+ cyber employers hiring remotely, and 50+ niche job boards all organised into one curated resource.
Red Team Hacker Bundle: Learn Hacking Online Red Team Style
Train like a professional adversary with the Red Team Hacker Bundle. Learn offensive security tactics, privilege escalation, and post-exploitation techniques used by real red teams.
Additional OSCP Training
One of the key benefits of the PWK course is the virtual hands-on hacking labs that let you test your skills in a simulated environment. Unfortunately, your lab time is limited, and there is a lot of course material you need to work your way through.
This time restraint is often a reason many students go into the course with some background knowledge and experience they can get from much cheaper training options. With the fundamentals covered, these students can get to the hands-on hacking labs quicker and benefit from the PWK course.
Some of the key fundamentals to learn before starting the course include:
- How to use Nmap to scan targets
- The different types of shells you can use to connect to an exploited machine (reverse shell versus bind shell)
- How to effectively enumerate a target machine to discover potential vulnerability
- How to perform basic privilege escalation on Linux and Windows machines
- The basics of web application attacks, such as enumerating web apps with Burp Suite and common web vulnerabilities like the OWASP top 10
- How to use Kali Linux
Although the PWK course covers many skills and knowledge required to pass the OSCP exam, this is just one way of performing penetration testing.
Understanding different hacking perspectives, techniques, and tools can help you pass the OSCP the first time. Check out the courses below for a more well-rounded understanding of the penetration testing process.
The Difference Between Success and Failure
Your determination will be the biggest factor in your success in passing the OSCP.
OffSec is renowned for its “Try Harder” mantra that encourages individuals to push themselves beyond their comfort zones, embrace challenges as opportunities for growth, and remain persistent in their pursuit of knowledge.
At StationX, we believe that success in cyber security requires continuous effort, practice, and a readiness to tackle challenges head-on. Anyone can learn the skills, earn the certifications, and prepare for an interview. The biggest challenge is staying motivated, pushing forward when things get tough, and having a rugged determination that sets you apart from the competition.
In the video below, we break down what the OSCP journey really looks like and share practical strategies for approaching the exam with a clear method. We explain why persistence matters as much as technical ability, and offer a reality check on penetration testing as a career, including how it differs from red teaming.
Apple Podcasts | Spotify | Buzzsprout | RSS Feed
Whether you’re aiming for your first attempt or tightening your approach for a retake, you can be confident our OSCP exam guide will prove to be a trusted reference to keep you focused, efficient, and ready for exam day.
Final OSCP Exam Advice
The OSCP certification is a challenging exam to pass. Despite all the time and effort people dedicate to preparing for the exam, many fail and need multiple attempts to pass. With that in mind, here are some final pieces of advice:
- Spend time enumerating: Discovering exploitable vulnerabilities and identifying attack paths is the most crucial aspect of the OSCP exam. Don’t rush the enumeration step: be thorough and comprehensive.
- Practice Active Directory hacking: A large part of the new OSCP exam focuses on Active Directory, making up almost half the exam. Practice your Active Directory hacking while preparing and get all 40 points.
- Take breaks: People often get stuck during the OSCP exam and keep pushing onward, trying the same exploit or attack path. It’s usually more productive to take a little break, refresh your thinking, and approach the problem with a new perspective. Breaks help you form new ideas.
- Review the exam guide: OffSec regularly updates the OSCP exam guide. Ensure you are up-to-date on what is permitted and what OffSec expects you to provide to pass the exam.
- Don’t get caught up on one machine: The OSCP exam is notorious for rabbit holes. Limit how long you spend on any one machine so you don’t get caught in one. We recommend spending a couple of hours on a machine and then moving on. You can always come back to it with a fresh perspective.
Before the big day, be sure to review the official OSCP+ Exam Guide, which walks you through everything you need to know, from exam structure and requirements to key exam details, submission instructions, additional required information, and how results are delivered. Or, if you prefer, you can also watch this walkthrough video for a quick overview:
Conclusion
This comprehensive OSCP exam guide explored everything you need to know about the certification, from what to expect to the essential skills you need to master to be successful. It also showcased the best ways to prepare for the exam and bolster your chances of success.
Remember, the main difference between success and failure is your determination. The more time you spend mastering the fundamentals, learning the PWK course material, and practicing your skills, the more success you’ll have.
If you master the prerequisites, learn all the course material, and practice your hands-on hacking skills, you will pass the exam. The more time you spend on these three things, the higher your chances of passing the first time.
Remember to check out our StationX Master's Program. Inside, you’ll get access to 30,000+ training courses with comprehensive coverage across topics and levels, 40+ career paths with a personalized study roadmap based on your goals and situation, and 1:1 expert support with direct access to specialists and fast response times.
More than just content, the program keeps you consistent, supported, and motivated to pass the OSCP and any other exam on your radar.
You can also dive deep into Kali Linux and Penetration Testing with our Ethical Hacking Course Bundle. Just click the banner below to start your hacking journey.
The Ethical Hacking Courses Bundle: Learn Hacking for Beginners includes:
- Learn Hacking From Scratch: Ethical Hacking Course
- Pentesting and Website Hacking Course: Learn From Scratch
- How to Hack WiFi and Wired Networks: Beginner's Course
- Learn Social Engineering Testing From Scratch
- Cloud Hacking: How to Do Penetration Testing Using the Cloud



















Great article! The OSCP exam guide is a must-read for anyone aiming to pass the OSCP certification on their first try. The emphasis on “cyber investigation services” highlights the importance of practical skills in today’s evolving threat landscape. The OSCP exam’s focus on penetration testing and ethical hacking prepares candidates to become proficient cyber investigators. This comprehensive guide provides valuable insights and strategies, ensuring success in the exam and paving the way for a rewarding career in cyber investigation services.