A fiery debate in cyber security is red team vs blue team. Which is better and which is the right choice for you?
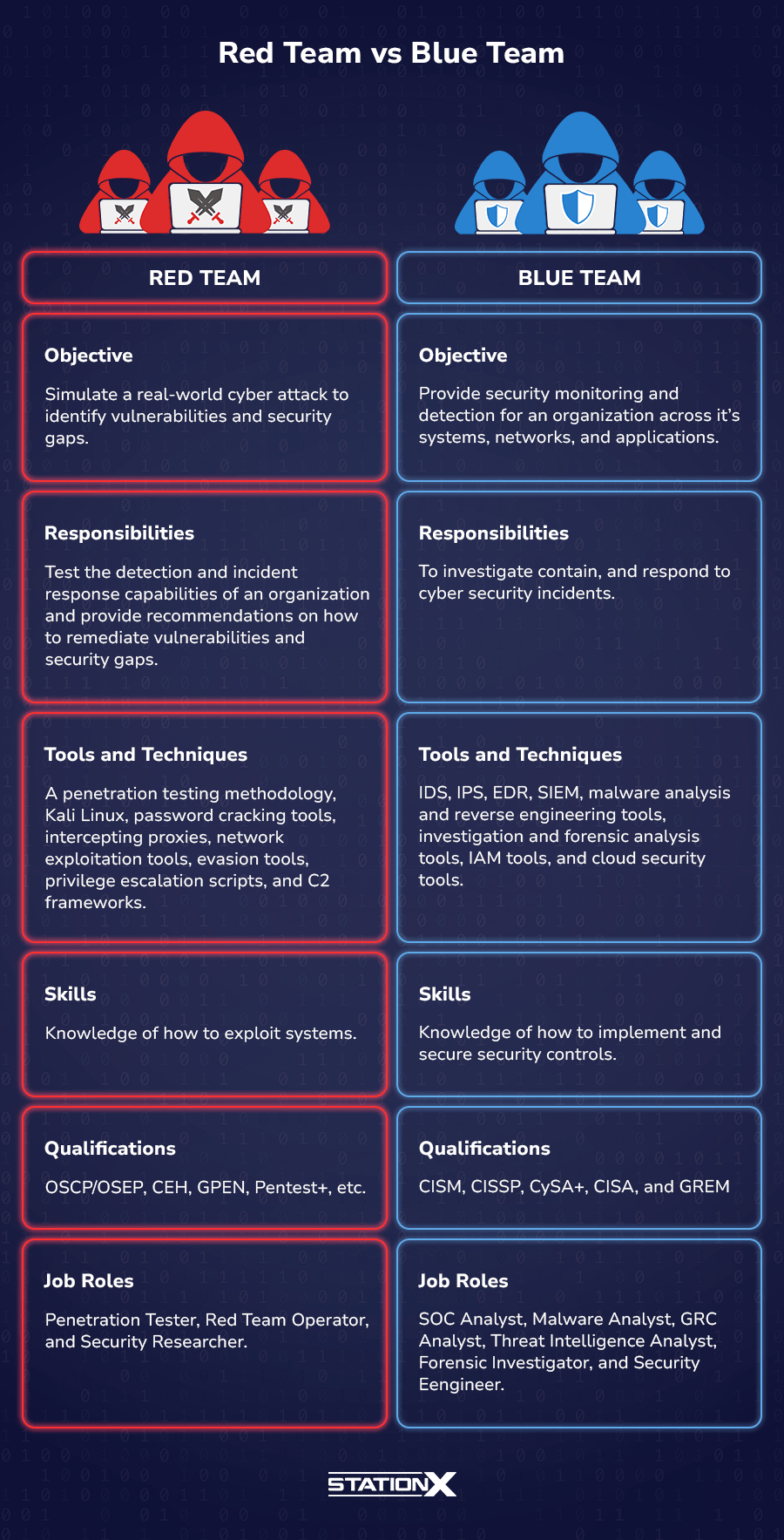
The red team focuses on assessing an organization's security by simulating real-world attacks. They attack organizations to uncover vulnerabilities and weak security controls. A blue team focuses on defending an organization against cyber attacks. They build security controls, patch vulnerabilities, detect threats, and respond to incidents.
The path you choose to go down is your choice. This article will compare and contrast the two teams, so you clearly understand what they do, the tools they use, and the skills and qualifications required to fulfill the roles that make up each team.
Let’s begin by defining what red and blue teams are responsible for and their key objectives.
What Are Red and Blue Teams?
Cyber security can be split into two teams. The red team performs offensive operations against an organization, and the blue team is responsible for protecting an organization’s systems.
Red Team
The red team is responsible for testing security controls and uncovering flaws by attacking IT systems. This could involve testing a specific web application for common vulnerabilities or simulating a real-world cyber-attack against a network. They try to uncover vulnerabilities by exploiting systems and then report these vulnerabilities so they can be fixed before black hat hackers exploit them.
The objectives and responsibilities of a red team are:
- Assess an organization's security effectiveness by identifying vulnerabilities that an attacker can exploit.
- Validate if security controls work as expected.
- Simulate a real-world cyber-attack.
- Test the detection and incident response capabilities of the client organization.
- Validate the ability of the people, processes, and technology to prevent a real-world cyber-attack.
- Provide recommendations on how to remediate vulnerabilities and security gaps.
- Collaborate with the blue team in security exercises as part of the purple team.
Blue Team
The blue team is responsible for protecting systems. They implement defensive measures to protect against cyber attacks, monitor these systems, and respond to emerging threats.
This team patches vulnerabilities, detects threats, and responds to incidents to keep an organization safe. They are the defenders who protect an organization's critical assets 24/7 and are the team that comes to mind for most people when they think of a cyber security team.
The objectives and responsibilities of a blue team are:
- Provide security monitoring and detection for an organization across its systems, networks, and applications.
- Investigate, contain, and respond to cyber security incidents.
- Manage the security infrastructure of an organization.
- Provide vulnerability management for an organization.
- Raise security awareness by educating and training employees.
- Collaborate with the red team in security exercises as part of the purple team.
Watch this video to find out more about how red teams and blue teams compare:
Tools and Techniques
Both teams will use various tools and techniques to aid them in their activities to be effective at their roles. Each team also shares some common tools with the other, which can be used to attack or defend systems.
Overview of Common Tools
Red and blue teams often use the same cyber security tools to attack and defend. These common tools are usually the ones that provide information about networks, systems, and applications. The red team uses this information to find vulnerabilities to exploit, whereas the blue team will use this information to identify security gaps that need patched.
Information Security Courses Bundles
Want lifetime access to expert-led cyber security training? Explore our Information Security Course Bundles — one-time purchase packages covering top topics like Ethical Hacking, Cloud, Linux, DevSecOps, and CompTIA certifications.
Tools used by the red team and blue team:
- Operating systems - Kali Purple
- Networking tools - Nmap, Wireshark, and Dig
- Information gathering and enumeration tools - Whois, Bloodhound, and PowerView
- Vulnerability assessment and management tools - GVM (formerly OpenVAS), Nessus, and Metasploit.
- Static Application Security Testing (SAST) tools - SonarQube and FindSecBugs
- Dynamic Applications Security Testing (DAST) tools - Burp Suite, OWASP ZAP, and Wapiti.
Although these teams have some tools in common, they also have their own sets of tools that they will utilize to attack and defend systems. Let’s take a look at those tools.
More details on the tools common to red teams and blue can be found in these articles:
Red Team
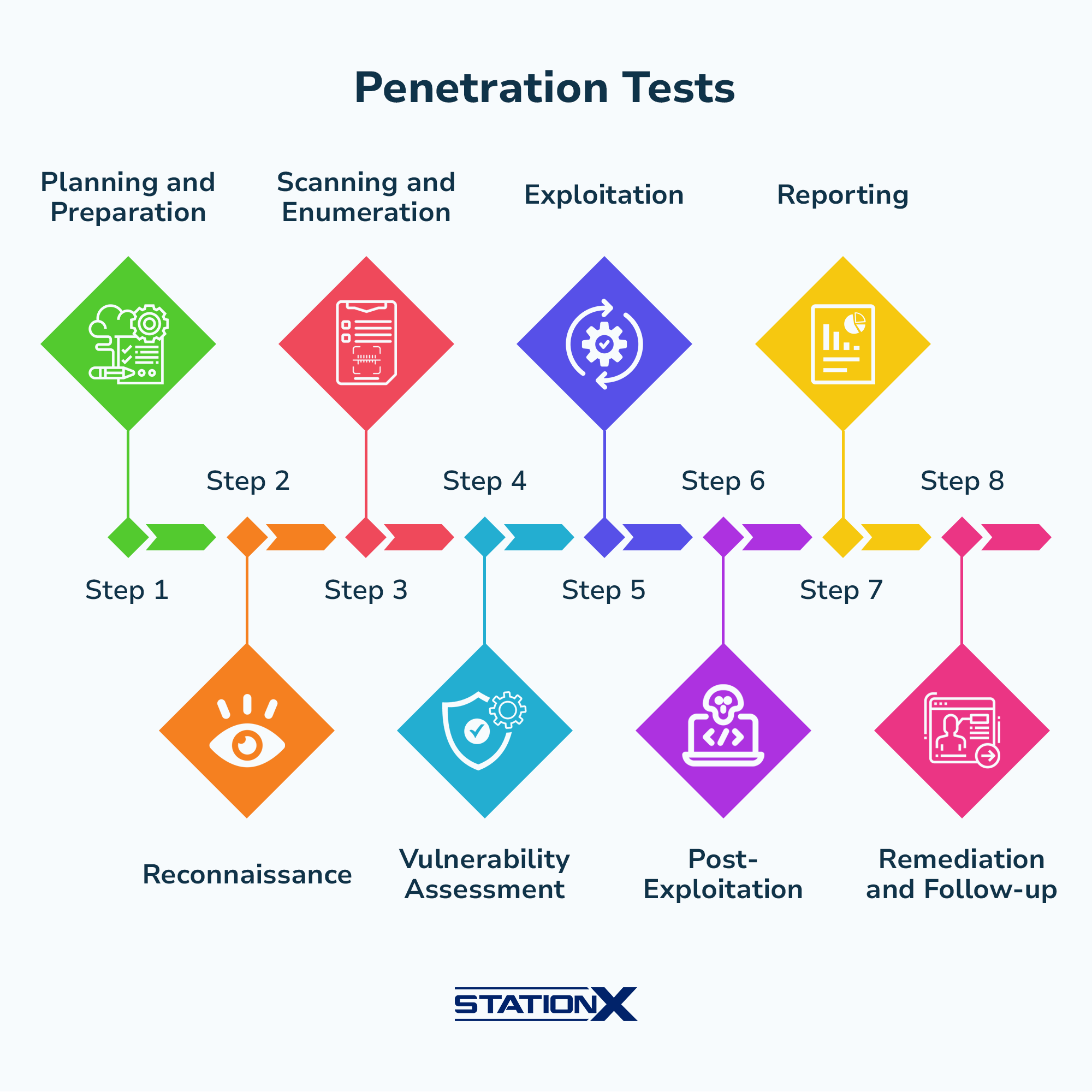
To provide a comprehensive security assessment, red teams will use a penetration testing methodology or framework to thoroughly test an organization's security.
A typical penetration test will follow eight phases during an engagement:
- Planning and Preparation
- Reconnaissance
- Scanning and Enumeration
- Vulnerability Assessment
- Exploitation
- Post-Exploitation
- Reporting
- Remediation and Follow-up
Along with a methodology, a red team will use tools to help them with their testing. These tools allow them to automate time-consuming tasks and perform offensive operations more efficiently.
Tools used by the red team:
- Hacking operating systems - Kali Linux and Parrot OS.
- Password cracking tools - John the Ripper and Hydra.
- Web application exploitation tools - Ffuff, Sqlmap, and Nikto.
- Intercepting proxies - Aircrack-ng, Responder, and bettercap.
- Privilege escalation tools - Seatbelt, PowerUp, and LinPEAS.
- Network exploitation tools - CrackMapExec, Mimikatz, and sshuttle.
- Pentesting and Command & Control (C2) frameworks - Cobalt Strike, Covenant, and Empire.
- Social engineering tools - Social Engineering Toolkit (SET), Beef, and EvilGinx2.
- Evasion tools - Veil and evilgrade.
More details on the tools used by red teams can be found in these articles:
Blue Team
A blue team is responsible for defending systems. To do this effectively, they require comprehensive logs from the systems they must protect. These logs allow blue team members to monitor their systems, trigger alerts if malicious activity is detected, and respond to incidents effectively. These logs are collected and pushed to a Security Incident and Event Management (SIEM) system, where they can be analyzed.
Additionally, a large part of a blue team's role is investigating the detected malicious activity. This requires tools to analyze computer forensics and malware, manage investigations, and perform reverse engineering when necessary.
Tools used by the blue team:
- Indecent Detection Systems (IDS) and Incident Prevention Systems (IPS) - Snort and Suricata
- SIEMs - Microsoft Sentinel, QRadar, Datadog, Elastic Security, and Splunk.
- Forensics tools - Autopsy, Volatility, Foremost, and GRR Rapid Response
- Reverse engineering tools - Radare2, Ghidra, and Binary Ninja
- Malware analysis tools - VirusTotal, REMnux, and YARA
- Endpoint security tools - OSSEC, ClamAV, SELinux (Security-Enhanced Linux), CrowdStrike Falcon, and Microsoft Defender for Endpoint.
- Investigation tools - CyberChef and Microsoft Security Copilot
- Infrastructure security testing tools - Cloudflare and Wazuh.
- Identity and Access Management (IAM) tools - Okta, Keycloak, and Microsoft IAM.
- Compliance and governance tools - OpenSCAP and InSpec by Chef.
- Cloud security tools - Zscalar, Qaulys, and Delinea (formerly Centrify).
More details on the tools used by blue teams can be found in these articles:
Skills and Qualifications
Now you have a firm understanding of what makes up a red team and a blue team, along with an idea about the tools each team uses, let’s look at the skills and qualifications required to become a member of each team.
Shared Skills and Qualifications
Both teams require fundamental skills that any cyber security professional needs. These include both technical skills and soft skills.
| Technical Skills | Soft Skills |
|---|---|
| Computer networking | Communication |
| Operating systems | Collaboration and teamwork |
| Hardware | Problem-solving and critical thinking |
| Troubleshooting and IT support | Adaptability |
| Software applications | Time management |
| Cloud computing | Leadership |
| Virtualization | Emotional intelligence |
| Securing basics | Social networking |
| Scripting and programming | Conflict resolution |
These fundamental skills provide a base for learning specialized skillsets and becoming a cyber security professional. To obtain these fundamental skills, there are two main approaches to take:
- You can choose the formal education route through University.
- You can choose to gain these skills through industry certifications or on-the-job experience.
If you are new to cyber, the CompTIA certification path is a common path to enter either the red or blue teams. This learning pathway first provides you with the core technical skills required to land a job in technology. From there, you can enter the world of cyber security with their Security+, PentTest+ (red team), or CySA+ (blue team) certifications. It’s a great way to learn the fundamental skills to excel in cyber security without having a University degree.
Once you have the fundamentals down, you can learn red or blue-specific skills.
Struggling to decide on what’s the right cyber certification for you? Read Top Entry-Level Cyber Security Certifications for You to find the best certification to complete now!
Red Team
Red team skills focus on simulating real-world cyber attacks. This involves effectively identifying vulnerabilities in systems and being able to exploit them. As such, you need to learn how various systems work and interact, the security mechanisms used to protect these systems, their flaws, and the common ways they are exploited.
The knowledge to perform these steps can be very low-level and technical. That said, there are a variety of tools and methodologies that you can use to abstract this low-level learning when you are starting out your career as a member of the red team.
It is advisable to obtain industry certifications to develop and prove your skillset.
Popular red team credentials and certifications:
For a comprehensive list of the hot ethical hacking certifications, read The Very Best Ethical Hacking Certifications for You. If you’re trying to determine if you should take the CEH or OSCP, look at CEH vs OSCP: Which One Should You Pursue?
Blue Team
Blue team members need various skills to effectively monitor and respond to security incidents. These skills involve investigating security incidents, building security controls, and mitigating potential vulnerabilities. This skill set requires technical knowledge of how systems work and connect to one another and an understanding of the common security controls used to protect these systems.
As your career progresses, you must specialize in a certain domain, such as malware analysis, compliance, or threat hunting. These domains require deeper technical knowledge or the ability to effectively manage a team. Often blue teams are more proficient in soft skills than red teams, as their roles require more collaboration and communication.
Popular blue team credentials and certifications:
- CompTIA Cybersecurity Analyst (CySA+)
- Certified Information Systems Security Professional (CISSP)
- Certified Information Security Manager (CISM)
- Certified Information Security Auditor (CISA)
- Certified Incident Handler (GCIH)
- Certified Network Defender (CND)
- GIAC Reverse Engineering Malware Certification (GREM)
CompTIA PenTest+ Voucher
Launch your pentesting career with a discounted CompTIA PenTest+ Voucher. Save up to 30% and earn your certification with an authorized CompTIA partner.
Job Opportunities
With an understanding of the skills and qualifications required to join the red and blue teams, let’s look at the job opportunities available to you.
If you are just entering cyber security, check out: A Newbie’s Guide to Finding a Cyber Security Job.
Red Team
Let’s take a look at the red team roles, the salary expectations at each career level, and the open positions that are available to you.
Red team roles:
- Penetration Tester: A cyber security professional who specializes in assessing an organization's security posture by attacking it. They identify vulnerabilities and weaknesses that could be exploited.
- Red Team Operator: These professionals emulate real-world cyber attacks using threat actors' tactics, techniques, and procedures (TTPs) to provide a holistic assessment of an organization’s people, processes, and technology.
- Red Team Lead: These professionals lead red team engagements and are responsible for a successful outcome. They typically have several years of experience as a red team operator.
- Security Researcher: This role focuses on discovering potential vulnerabilities and weaknesses in endpoints, networks, and applications by performing tests against systems to reveal flaws that can be exploited.
Average red team salaries
The average salary for a red team member will vary depending on experience, location, industry, and job responsibilities. However, the following is what you can expect to make through the course of your career:
Open positions
Red team roles can be difficult to find, particularly at the entry-level, where competition is fierce. However, as you move up to mid-level and senior-level positions, there tend to be more open positions because fewer people have the knowledge to qualify for these roles.
Both red teaming and penetration testing are possible red team roles. To discover the differences between red teaming and penetration testing, read Red Teaming vs Penetration Testing: What Is Best for Me?
If you are interested in pursuing a career in pentesting, read How to Become a Penetration Tester: The Ultimate Guide
Blue Team
Now let’s take a look at the blue team roles that exist, the salary expectations at each career level, and the open positions that are available to you.
Blue team roles:
- Security Operations Center (SOC) Analyst: These professionals are responsible for detecting, monitoring, investigating, and responding to security incidents to defend an organization from cyber attacks.
- Malware Analyst: This role involves identifying, dissecting, and analyzing malware to protect against it.
- Forensic Investigator (Digital Forensics Analyst): These professionals investigate and document digital evidence related to cybercrime and data breaches.
- Threat Intelligence Analyst: This role involves gathering, analyzing, and distributing intelligence related to new and emerging threats.
- Vulnerability Management Specialist: These professionals are responsible for identifying, assessing, and mitigating vulnerabilities that an organization is affected by.
- Governance Risk and Compliance (GRC) Analyst: This role involves ensuring an organization is compliant with regulatory requirements and follows governance frameworks to effectively manage risk.
- Security Engineer: These professionals design, implement, and maintain security controls that protect an organization from cyber attacks.
Average blue team salaries
The average salary for a red team member will vary depending on experience, location, industry, and job responsibilities. However, the following is what you can expect to make through the course of your career:
Open positions
Entry-level blue team roles are plentiful because of a lack of skilled defenders and the urgent need for organizations to defend themselves against cyber attacks. Because of this, most people entering cyber security get their start on the blue team. However, to progress in your career, you must develop more specialized skills to qualify for high-paying positions.
Conclusion
The red team focuses on attacking systems, and the blue team focuses on defending systems. Each team has its own set of objectives, tools, and skills required to perform their individual roles. However, members of both teams need the fundamental skills required to excel in cyber security.
To qualify for either team, you need to possess a certain set of skills and qualifications to effectively perform each role. This article highlighted the popular certifications recruiters look for, the job opportunities available to you, and the salary expectations for each team so you can make an informed decision about which team you want to join.
Although the red and blue teams have opposing roles, they share the goal of discovering and mitigating vulnerabilities before black hat hackers can exploit them. We are all on the same side.
If you are interested in learning the skills required to become a red team or blue team member, the StationX Master's Program is for you. With access to over 30,000 courses and labs, mentorship, career path roadmaps, and more, you can go from zero to a cyber security professional in six to 12 months.
Master red team tactics, including reconnaissance, Active Directory attacks, firewall evasion, scripting and API hacking, post-exploitation techniques, and enterprise phishing. Think, operate, and report like a professional red team operator in live environments and emulate real attackers
This Red Team Hacker Bundle includes:
- Red Teamer Hacking Course: Learn Ethical Hacking Volume 1
- Red Teamer Hacking Course: Learn Ethical Hacking Volume 2
- Red Teamer Hacking Course: Learn Ethical Hacking Volume 3
- Windows API Hacking Course With Python
- Breaching The Perimeter With Enterprise Phishing Training
- Get a Red Team & Penetration Tester Job Course
- The Complete Nmap Ethical Hacking Course